High-Priority Opponents
This page presents patterns and companies that pose a risk to civil society.
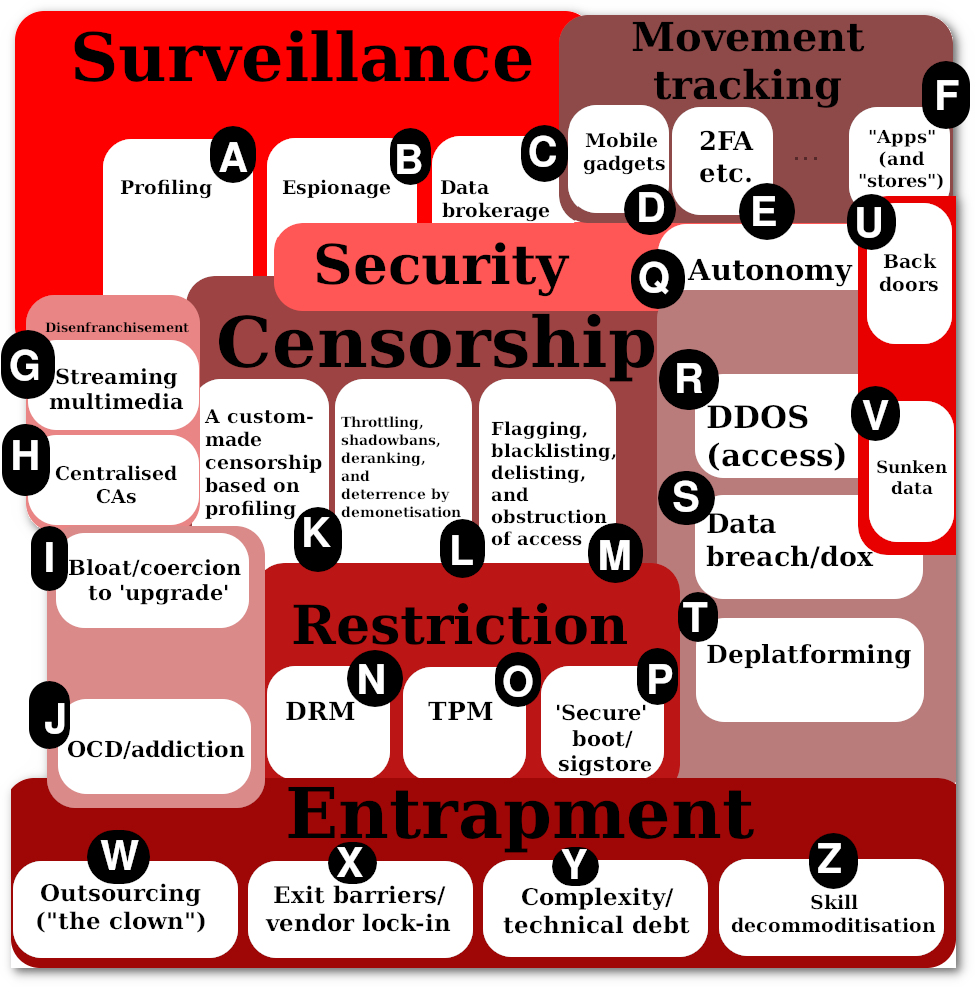
We've split the nature of threats to better classify the opponents' types of attacks. They come in different shapes and sizes, not all threats are equal. There are overlaps, too. Here is a quick legend, subjected to change over time (the accompanying text, shown below, will always be more up to date).
For inside threats or another perspective see Librethreat Database and Librethreat Forecast.
Examples: Twitter, Facebook, Microsoft (e.g. LinkedIn, GitHub)
Those certainly include patent lawsuits, submarine patents, as well as trademark and copyright enforcement actions (e.g. DMCA takedowns).
Additionally, administrivia 'DoS' and censorship/SLAPP-like attacks (e.g. via a Code of Conduct being selectively enforced) can demoralise projects and drive away much-needed talent (more rules and committees than actual contributors).
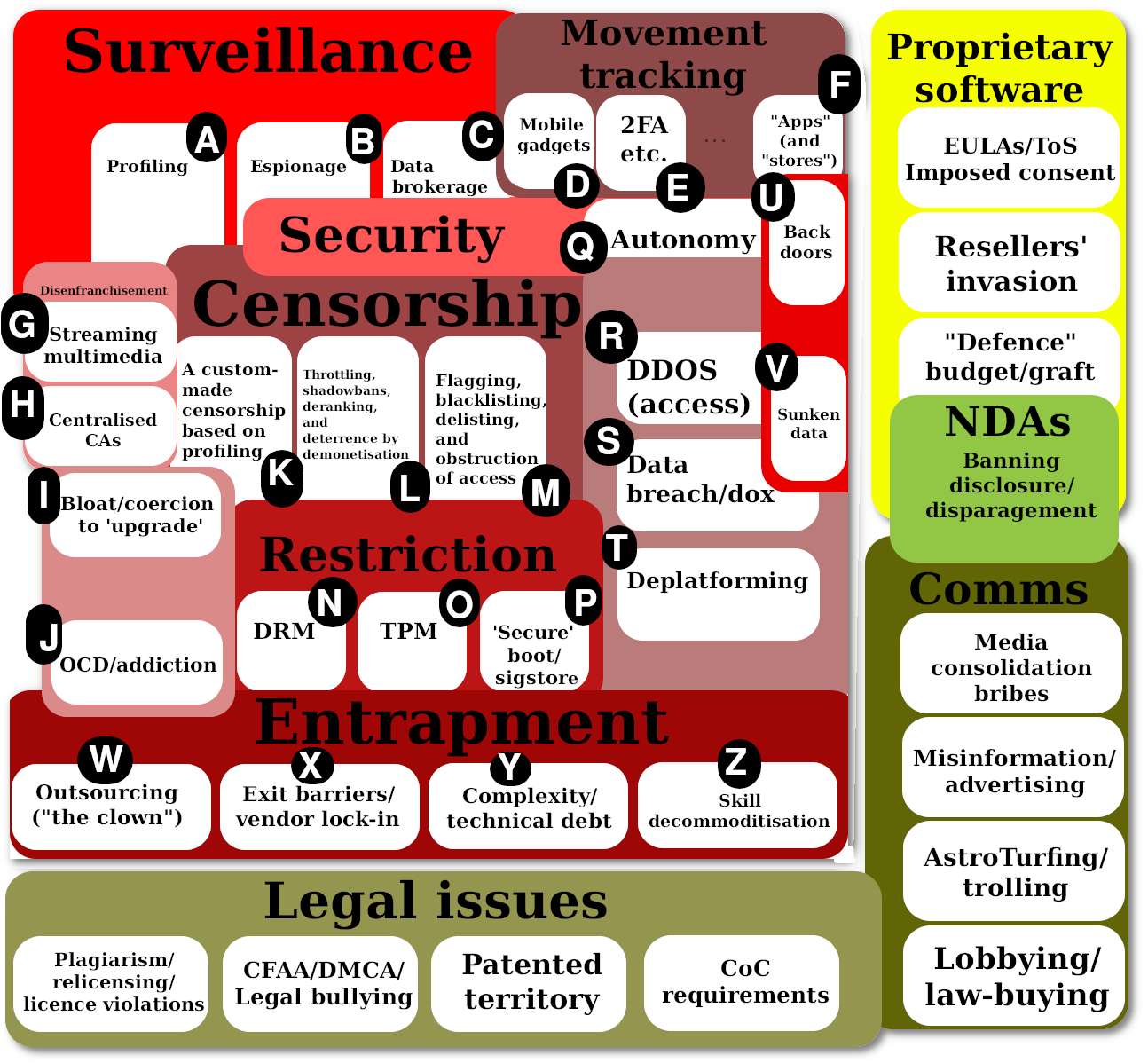
This one adds: Legal Issues, Comms, NDAs, and Proprietary Software
With the following 'bubbles'
Media consolidation/bribes
Misinformation/advertising
AstroTurfing/trolling
Lobbying/law-buying
EULAs/ToS/Imposed consent
Resellers' invasion
"Defence" budget/graft
Banning disclosure/disparagement
Plagiarism/relicensing/licence violations
CFAA/DMCA/Legal bullying
Patented territory
CoC requirements
To be continued...
This page is work in progress and is subjected to change as companies alter strategic focus, sometimes successfully and sometimes dooming themselves in the process. Regardless of profitability, large companies that control the digital lives of million if not billions of people have great and ever-growing potential for harm. Rarely has corporate power been leveraged for good; shareholders want returns at someone else's expense.
Amazon: This company isn't exactly old. Its cash cows include the online retail business (the original business model) and clown computing (governments, businesses and people outsourcing to Amazon's Web Disservices). In recent years Amazon has been relying more and more on military ("defence") contracts as well; it is hoarding a lot of data, including voice and video footage from people's homes. We can expect that to accelerate as disregard for privacy gets increasingly "normalised".
The nature of Amazon as a threat to GNU/Linux is grossly understated; AWS represents a new sort of issue which we'll need to come to grips with in years to come. As an associate explains, "Amazon uses, if I understand correctly, proprietary interfaces to manage what would have otherwise been commodity systems so they may rent access to commodity GNU/Linux but they have definitely found one way to decommodify it. Similar with Red Hat (IBM). IBM has followed Microsoft's outline from the Halloween Documents and been able to use systemd to decommodify GNU/Linux in such a way that it becomes so complex that their services must be hired in so decommodification appears to possibly be a recurring theme here."
We'll come to IBM later.
Apple: Apple is a brand that sells overpriced "luxury" (or perceived luxury) goods, which are precarious in a weak economy with supply/demand anomalies and sanction wars. Apple has been around for many years, it has had its ups and down, but it's mostly like a fashion industry for digital goods, which are typically made in sweatshops in the far east. Apple focuses on image, not technical merits. It also collects a lot of personal data and, contrary to the advertising, it passes on such data.
Netflix: Techrights has not written a great deal about Netflix. In a sense, Netflix is a lot weaker than people are led to assume and it has financial instability. It's a modern video rental disservice, selling temporary access to "content" (with DRM), making it akin to Spotify but for video, not audio. On the Internet, Netflix is responsible for a lot of traffic, but this can easily give a disproportionate sense of importance. Netflix is a bandwidth hose.
Clownflare: Speaking of bandwidth hoses, Clownflare has been a growing threat to the very nature of an Open Web. The company is unprofitable (at the time of writing), it is increasingly harmful to accessibility, and it offers a false solution to a real problem. Outsourcing does not beget security. Clownflare might not survive for very long for the same reasons Uber and other gig economy [sic] companies are, in general, a bit of a gamble.
Google, Facebook and Twitter: These companies depend a great deal on the Web. They engage in a lot of 'surveillance capitalism' with advertising and mental manipulation. Twitter is not even profitable and has rarely been profitable in its entire existence. But it represents a great dangerous, further elucidated by the rise of TikTok. They do not seem to rely on advertising as the business model but political force, corporate influence, perception management (YouTube does not seem to be profitable, either; it's increasingly censoring). Censorship is a serious problem when platform owners look to control other people's communications, centrally, in one fell swoop.
Microsoft: When Techrights was born we focused on Novell and Microsoft. A lot has changed since then, partly because Android rose, Windows fell, and Microsoft explored all sorts of contingency plans amid a state of emergency (no mobile platform caught on, not even after the abduction of Nokia). So Microsoft is a company in decline, trying to use de facto bailout funds ("defense" graft) to keep afloat. Like Google, Microsoft has a failing business in hosting (massive losses, layoffs etc.), with the same happening in GitHub and maybe LinkedIn (a failing competitor of Facebook). Like with Skype, it's hard to extract money when the competition costs nothing, so surveillance increasingly becomes the business model, even with Windows whose market share decreases and competition (e.g. ChromeOS) drives the prices down. While Microsoft remains the most potent threat to software freedom, we predict its influence will continue to wane in decades to come (of that company survives that long).
IBM (and Red Hat): Like HP and VMware, which are less relevant to us, there's a languishing hardware and software business, with several failed attempts at hosting as a subscription-based revenue stream/business model. IBM continues to shrink, but it's being helped by the US government while national debt expands. IBM has done various harmful things to GNU/Linux in recent years, wrongly believing it can grab more control by attacking the very community which supplies the code (Novell had made the same error).
Oracle: Like IBM, Oracle relies a great deal on branding, legacy systems, and government contracts. We expect Oracle's influence to ebb away.
AMD/Intel/Nvidia: Putting aside Qualcomm and some other important players, the "big three" for graphics-intensive chipsets are trying do sell overpriced hardware that exceeds in capacity what most PC users or portable devices need (also too energy-intensive, unlike competitors from Europe and east Asia).
Lenovo, Huawei, Xiaomi etc.: Speaking of east Asia, China has a growing number of hardware giants, increasingly competitive on price and quality. The Western nations have increasingly resorted to blockades and bans, mostly for inability to compete.
LG and Samsung: South Korean "premium" goods, more widespread than Japanese brands in particularly lucrative markets such as phones (where Samsung continues to dominate). The threats posed by Samsung are inherently different. We used to call for a boycott of LG and Samsung because of their relationship with Microsoft. Their stance on software patent is problematic.
ASUS, Acer, HTC and other Taiwanese brands: Those are typically beholden to Android and Windows, but that might change in the future.
In this list, which is partly grouped by region, the national identity matters because of cultural differences and domestic expertise. Europe does a lot of mechanics, India focuses on programming, China does manufacturing, Japan is still excelling at cars, and the US seems hellbent on controlling people's digital lives (platforms and data). This makes the US exceptionally difficult and harsh towards Free software. We must remember that more "tech giants" (with more "share") does not mean more income, as some operate at a loss and many are a yoke on the economy (they receive "life support" from the taxpayers) while they have endless potential for abuse. It's hardly a secret that the US wasted around 1.1 trillion dollars a year on "defence" around 2015 (it must be a lot more now, but the complete numbers are harder to find than what Congress signs out in the open; the public sees only about 60% of the real budget). The issue associated with graft, which always was prevalent in other sectors (subsidies for oil and food to name two), is under-explored. It seems highly probably that the US "tech bubble" (and techno-babble) lives on borrowed times and borrowings with the general public as 'collateral'. We therefore expect Free software's persistence to pay off in the long run. As an associate put it, "one essential factor to consider is that ICT is a pawn in major war efforts" and as the US strives to maintain its post-WW2 status (political domination and military might) it'll throw resources at some of the companies above in order to sustain them. Even when their business models aren't economically viable.
We've split the nature of threats to better classify the opponents' types of attacks. They come in different shapes and sizes, not all threats are equal. There are overlaps, too. Here is a quick legend, subjected to change over time (the accompanying text, shown below, will always be more up to date).
For inside threats or another perspective see Librethreat Database and Librethreat Forecast.
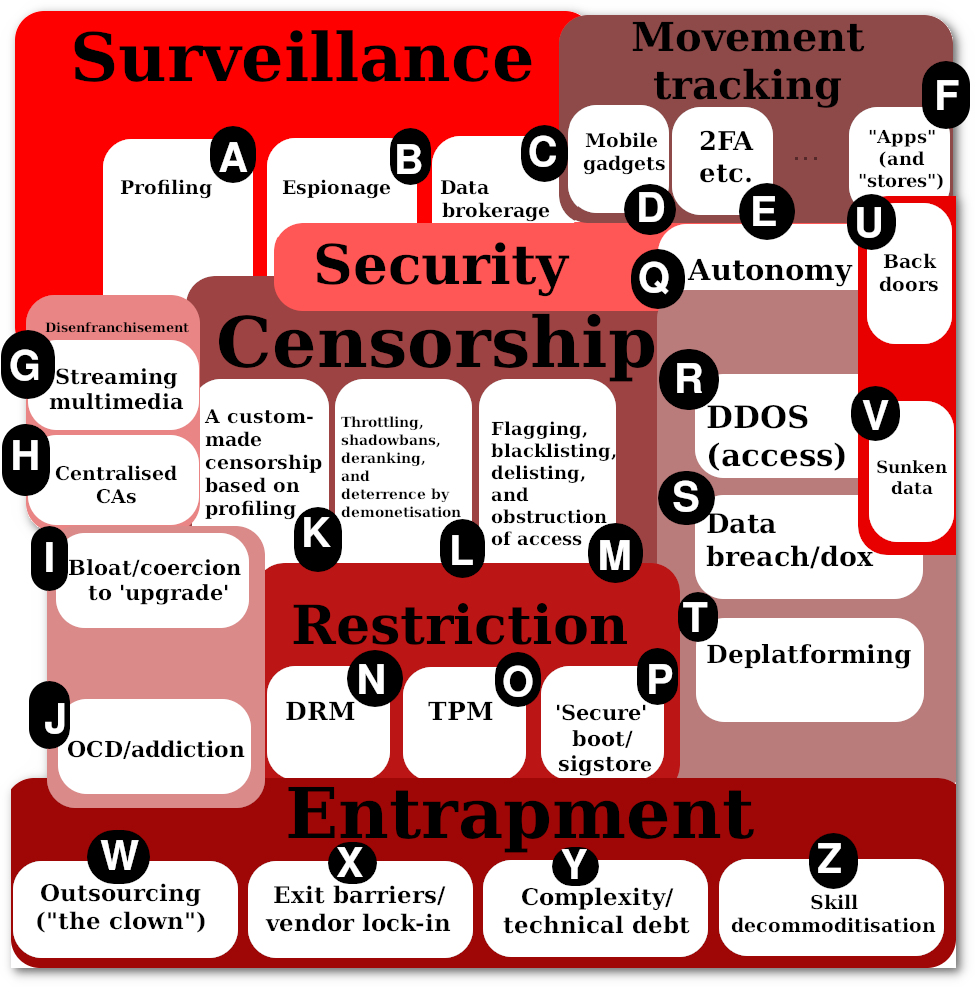
Surveillance
Spying is a very broad subject, which is hard to generalise. In the absence of privacy there is erosion of personal dignity, so persons stand to lose a lot by giving intimate details (and a discreet lifestyle) away.A. Profiling
Examples: Amazon, Apple, Microsoft, Facebook, Google, ClownflareB. Espionage
Examples: Oracle, IBM, Microsoft, Facebook, Google, Twitter, Samsung, DuckDuckGoC. Data brokerage
Examples: Microsoft, Facebook, Twitter, DuckDuckGo, StartpageMovement tracking
This is a branch of surveillance, pertaining mostly to an all-seeing, always-seeing eye (sometimes with gyroscope, microphone etc.) that studies a person's behaviour even whilst "away from keyboard"; devices that are inside people's pockets, worn on the wrists and so on may offer some temporary convenience, often to be vastly outweighed by the risks, which can manifest themselves in the long run. Even perfectly law-abiding citizens can be subjected to false accusations, based on a misinterpretation, or be harshly scrutinised some time in the future when laws and administrations change (e.g. bans on abortion).D. Mobile gadgets
Examples: Amazon, Apple, Microsoft, Facebook, GoogleE. 2FA etc.
Examples: Twitter, Apple, Facebook, GoogleF. "Apps" (and "stores")
Examples: Apple, GoogleDisenfranchisement
Personal ownership and a sense of belonging, unlike the lack of a responsible employer in the so-called 'gig economy', will be recognised as more people are convinced if not compelled to rent instead of own, to be used instead of become empowered. There are many angles to this conundrum, which is multi-faceted and partly covered by categories other than this one.G. Streaming multimedia
Examples: Netflix, Spotify, Amazon, GoogleH. Centralised CAs
Examples: Linux Foundation, Google, ClownflareI. Bloat/coercion to 'upgrade'
Examples: Apple, Microsoft, GoogleJ. OCD/addiction
Capturing users (captives) is an experimental business model. Proprietary interfaces that are made more "addictive" for so-called 'engagement' have been optimised to the point where many people cannot imagine living without these.Examples: Twitter, Facebook, Microsoft (e.g. LinkedIn, GitHub)
Censorship
A growing trend in a connected world (via the Internet or other means) is exclusion and isolation, based on the desires of leaders and the business objectives of corporations. A hands-off approach is framed as "extreme", hence or thereby 'normalising' a censorious climate, uncaring and intolerant of dissent.K. A custom-made censorship based on profiling
Examples: Apple, Microsoft, GoogleL. Throttling, shadowbans, deranking, and deterrence by demonetisation
Examples: Twitter, Facebook, MicrosoftM. Flagging, blacklisting, delisting, and obstruction of access
Examples: Apple, Google, ClownflareRestriction
The assault on general-purpose computing (or computers one can modify, hack on, customise) is an ongoing assault. It may culminate in the narrowing of "permissible" computing, locked down and restricted not by the operator but companies that control them remotely.N. DRM
Examples: Apple, Microsoft, Google, Amazon, Netflix, IntelO. TPM
Examples: Apple, Microsoft, IBM, IntelP. 'Secure' boot/sigstore
Examples: Google, Microsoft, IBM, IntelSecurity
Q. Autonomy
Think along the lines of self-determination or self-hosting. Centralisation poses a threat.R. DDOS (access)
S. Data breach/dox
T. Deplatforming
Examples: Twitter, Facebook, MicrosoftU. Sunken data
Examples: Google, FacebookV. Back doors
Examples: Google, MicrosoftEntrapment
There has been a proliferation through hype of platforms designed to increase complexity and capture people/governments/businesses whilst at the same time violating commitments to data protection and sovereignty. Some of these efforts have been subsidised at a loss for gains through long-term control.W. Outsourcing ("the clown")
Examples: Amazon, Google, Microsoft, Oracle, IBMX. Exit barriers/vendor lock-in
Examples: Apple, Microsoft, Oracle, IBMY. Complexity/technical debt
Examples: Microsoft, Oracle, IBMZ. Skill decommoditisation
Examples: Microsoft, IBM, AmazonOther Threats (Peripheral)
Legal attacks
There are many ways to deter and discourage competitors, including non-profit, community-run projects.Those certainly include patent lawsuits, submarine patents, as well as trademark and copyright enforcement actions (e.g. DMCA takedowns).
Additionally, administrivia 'DoS' and censorship/SLAPP-like attacks (e.g. via a Code of Conduct being selectively enforced) can demoralise projects and drive away much-needed talent (more rules and committees than actual contributors).
Antitrust violations
Sometimes the competition gets bought, e.g. GitHub and Skype is Spy Campaign|Skype.Media manipulation
This is sometimes done by Microsoft directly and sometimes via proxies and shells like Gates Foundation Critique|the Gates Foundation. There are many examples of AstroTurfing|Microsoft AstroTurfing.Work in Progress/Under Review
We're tentatively publishing revised charts. Here is the June 2020 version: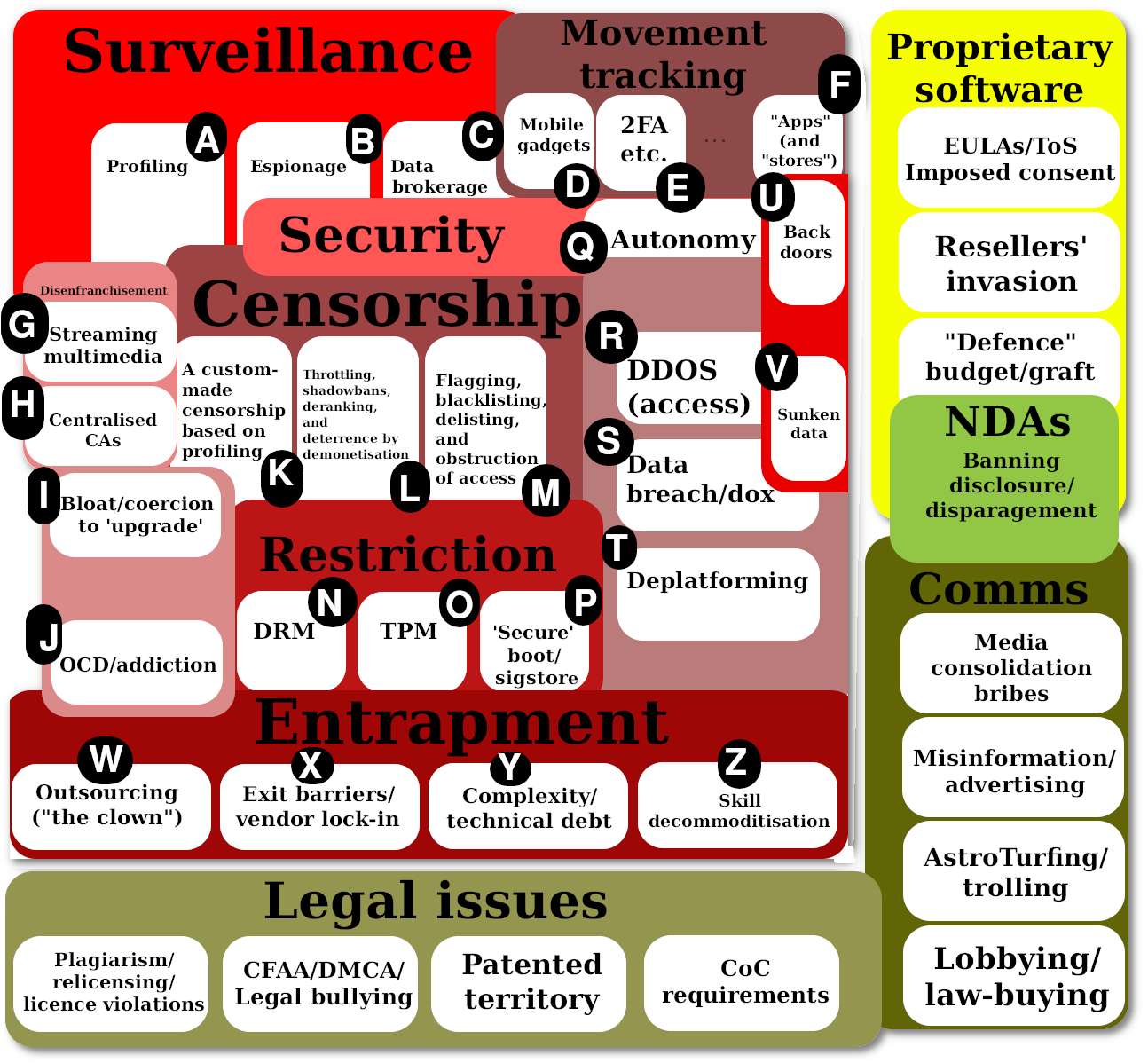
This one adds: Legal Issues, Comms, NDAs, and Proprietary Software
With the following 'bubbles'
To be continued...
2012 Outline
At the time of writing (2022), many potent threats to digital sovereignty, both online and offline, come from from American companies. This may change in the future. We've attempted to identify the nature of the threat/s, with the aim of classifying or grouping brands (companies come and go; the underlying nature of problems remains the same), ultimately clustering brands based on common criteria or categories.This page is work in progress and is subjected to change as companies alter strategic focus, sometimes successfully and sometimes dooming themselves in the process. Regardless of profitability, large companies that control the digital lives of million if not billions of people have great and ever-growing potential for harm. Rarely has corporate power been leveraged for good; shareholders want returns at someone else's expense.
Amazon: This company isn't exactly old. Its cash cows include the online retail business (the original business model) and clown computing (governments, businesses and people outsourcing to Amazon's Web Disservices). In recent years Amazon has been relying more and more on military ("defence") contracts as well; it is hoarding a lot of data, including voice and video footage from people's homes. We can expect that to accelerate as disregard for privacy gets increasingly "normalised".
The nature of Amazon as a threat to GNU/Linux is grossly understated; AWS represents a new sort of issue which we'll need to come to grips with in years to come. As an associate explains, "Amazon uses, if I understand correctly, proprietary interfaces to manage what would have otherwise been commodity systems so they may rent access to commodity GNU/Linux but they have definitely found one way to decommodify it. Similar with Red Hat (IBM). IBM has followed Microsoft's outline from the Halloween Documents and been able to use systemd to decommodify GNU/Linux in such a way that it becomes so complex that their services must be hired in so decommodification appears to possibly be a recurring theme here."
We'll come to IBM later.
Apple: Apple is a brand that sells overpriced "luxury" (or perceived luxury) goods, which are precarious in a weak economy with supply/demand anomalies and sanction wars. Apple has been around for many years, it has had its ups and down, but it's mostly like a fashion industry for digital goods, which are typically made in sweatshops in the far east. Apple focuses on image, not technical merits. It also collects a lot of personal data and, contrary to the advertising, it passes on such data.
Netflix: Techrights has not written a great deal about Netflix. In a sense, Netflix is a lot weaker than people are led to assume and it has financial instability. It's a modern video rental disservice, selling temporary access to "content" (with DRM), making it akin to Spotify but for video, not audio. On the Internet, Netflix is responsible for a lot of traffic, but this can easily give a disproportionate sense of importance. Netflix is a bandwidth hose.
Clownflare: Speaking of bandwidth hoses, Clownflare has been a growing threat to the very nature of an Open Web. The company is unprofitable (at the time of writing), it is increasingly harmful to accessibility, and it offers a false solution to a real problem. Outsourcing does not beget security. Clownflare might not survive for very long for the same reasons Uber and other gig economy [sic] companies are, in general, a bit of a gamble.
Google, Facebook and Twitter: These companies depend a great deal on the Web. They engage in a lot of 'surveillance capitalism' with advertising and mental manipulation. Twitter is not even profitable and has rarely been profitable in its entire existence. But it represents a great dangerous, further elucidated by the rise of TikTok. They do not seem to rely on advertising as the business model but political force, corporate influence, perception management (YouTube does not seem to be profitable, either; it's increasingly censoring). Censorship is a serious problem when platform owners look to control other people's communications, centrally, in one fell swoop.
Microsoft: When Techrights was born we focused on Novell and Microsoft. A lot has changed since then, partly because Android rose, Windows fell, and Microsoft explored all sorts of contingency plans amid a state of emergency (no mobile platform caught on, not even after the abduction of Nokia). So Microsoft is a company in decline, trying to use de facto bailout funds ("defense" graft) to keep afloat. Like Google, Microsoft has a failing business in hosting (massive losses, layoffs etc.), with the same happening in GitHub and maybe LinkedIn (a failing competitor of Facebook). Like with Skype, it's hard to extract money when the competition costs nothing, so surveillance increasingly becomes the business model, even with Windows whose market share decreases and competition (e.g. ChromeOS) drives the prices down. While Microsoft remains the most potent threat to software freedom, we predict its influence will continue to wane in decades to come (of that company survives that long).
IBM (and Red Hat): Like HP and VMware, which are less relevant to us, there's a languishing hardware and software business, with several failed attempts at hosting as a subscription-based revenue stream/business model. IBM continues to shrink, but it's being helped by the US government while national debt expands. IBM has done various harmful things to GNU/Linux in recent years, wrongly believing it can grab more control by attacking the very community which supplies the code (Novell had made the same error).
Oracle: Like IBM, Oracle relies a great deal on branding, legacy systems, and government contracts. We expect Oracle's influence to ebb away.
AMD/Intel/Nvidia: Putting aside Qualcomm and some other important players, the "big three" for graphics-intensive chipsets are trying do sell overpriced hardware that exceeds in capacity what most PC users or portable devices need (also too energy-intensive, unlike competitors from Europe and east Asia).
Lenovo, Huawei, Xiaomi etc.: Speaking of east Asia, China has a growing number of hardware giants, increasingly competitive on price and quality. The Western nations have increasingly resorted to blockades and bans, mostly for inability to compete.
LG and Samsung: South Korean "premium" goods, more widespread than Japanese brands in particularly lucrative markets such as phones (where Samsung continues to dominate). The threats posed by Samsung are inherently different. We used to call for a boycott of LG and Samsung because of their relationship with Microsoft. Their stance on software patent is problematic.
ASUS, Acer, HTC and other Taiwanese brands: Those are typically beholden to Android and Windows, but that might change in the future.
In this list, which is partly grouped by region, the national identity matters because of cultural differences and domestic expertise. Europe does a lot of mechanics, India focuses on programming, China does manufacturing, Japan is still excelling at cars, and the US seems hellbent on controlling people's digital lives (platforms and data). This makes the US exceptionally difficult and harsh towards Free software. We must remember that more "tech giants" (with more "share") does not mean more income, as some operate at a loss and many are a yoke on the economy (they receive "life support" from the taxpayers) while they have endless potential for abuse. It's hardly a secret that the US wasted around 1.1 trillion dollars a year on "defence" around 2015 (it must be a lot more now, but the complete numbers are harder to find than what Congress signs out in the open; the public sees only about 60% of the real budget). The issue associated with graft, which always was prevalent in other sectors (subsidies for oil and food to name two), is under-explored. It seems highly probably that the US "tech bubble" (and techno-babble) lives on borrowed times and borrowings with the general public as 'collateral'. We therefore expect Free software's persistence to pay off in the long run. As an associate put it, "one essential factor to consider is that ICT is a pawn in major war efforts" and as the US strives to maintain its post-WW2 status (political domination and military might) it'll throw resources at some of the companies above in order to sustain them. Even when their business models aren't economically viable.
