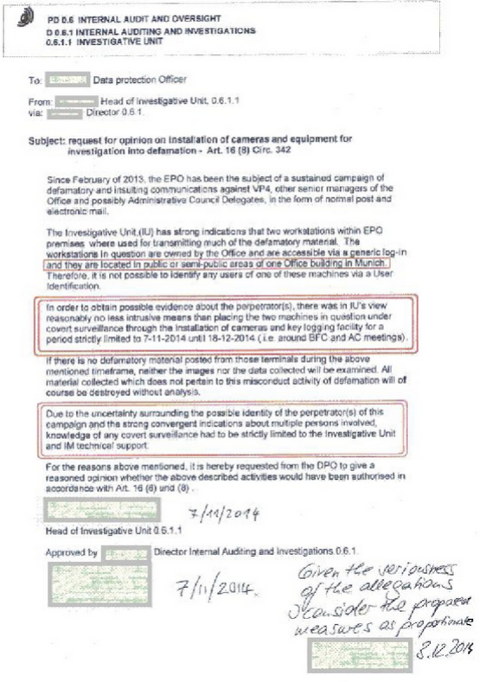
THE EPO spying scandal is merely the latest among many scandals (we were among the first to report these). It's the result of the EPO's desperate attempts to muzzle critics. According to newly-leaked documents from Germany, "the so-called data protection officer of the EPO signed off on keylogging, hidden cameras" (blatant violations of European privacy laws), which means that he is very much like Microsoft's so-called (bogus) privacy chiefs, not the ones Microsoft fired for actually trying to ensure privacy (i.e. doing their job).
"It's the result of the EPO's desperate attempts to muzzle critics."For an institution that goes as far as keyloggers, with approval from high-level officials, it may not seem radical to hire Control Risks, mercenaries of the British government (with special spy connections). "Control Risks" is of course a very nice euphemism, which one of our readers initially described as the "private security company hired by EPO" (that was before much was known about it).
Control Risks is of course unlikely to find out much of use by reading this site. What they are after must be identities of sources and at no point will they succeed, unless they think that the reporters and sources are very dumb (the same poor assumption police often makes about felons). We know that they even spy on our IRC channels, which is rather pathetic use of their time (and European taxpayers' money). As counter-intuitive as it may first seem, the transparency of the channels is what makes them useless for blackmail or exploitation by spies. In other words, knowing that everything there is visible (not just to moles/intruders and leakers) discourages bad behaviour or self-incriminating communication therein. There are no secrets there and people in the channels don't have an illusion of privacy. Now, compare that to what Wikileaks had done before an FBI mole from Iceland leaked the logs. We advise Control Risks to step back and we wish to tell EPO (in the Netherlands) that we are seeing (and banning) its IP addresses that have been hammering on this site. We know what you are up to.
In order to secure future reference of the leaked material we are adding it below as JPEG (just large enough to be legible). It is possible that the Sepp Blatter equivalent at the EPO is actually Željko Topić, not King Battistelli. What the EPO needs is a sacrificial lamb, not more coverup. The longer it goes on for, the more embarrassing it will become. Keyloggers and hidden cameras should be installed on (or pointed at) Topić's PC, not everyone who works at the EPO. ⬆