Summary: With Aorato acquisition Microsoft helps protect the criminals (from whistleblowers) and with lies about .NET Microsoft distracts from a bug that has facilitated remote access into Windows (by those in the know) for nearly two decades
MICROSOFT IS A company of liars, centred around media manipulation. This is why not enough people know about the company's sheer levels of malice, crimes, and disregard for people.
Microsoft keeps
throwing money around for favourable publicity, so not enough criticism is published where it's
well overdue. Today we'll tackle several stories that deserve more attention from an appropriate angle, not a promotional (marketing) angle.
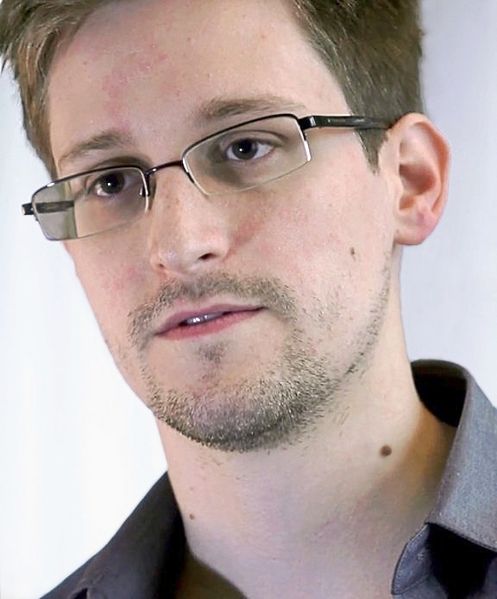
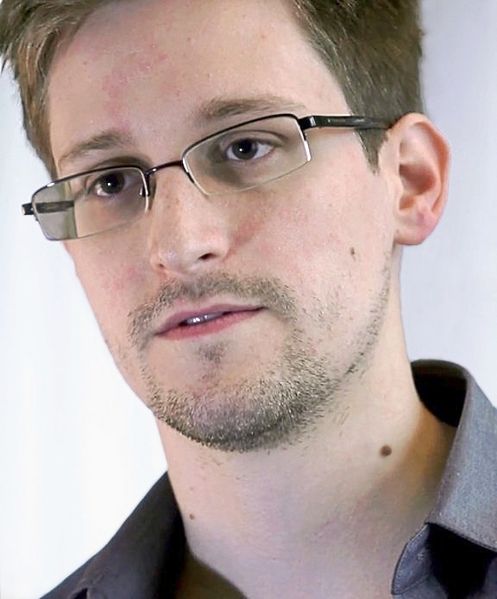
A few days ago
Microsoft decided to buy a military-connected (IDF/Israel) anti-whistleblowing 'software' company. What a lot of
shallow coverage failed to mention was the real purpose of the software (not often marketed as such). To quote one report: '“Snowden reportedly used colleagues’ passwords to access sensitive docs,” he told me. “Even if the user activity seems legitimate, the same account would actually present suspicious or abnormal behavior behind the scenes which Aorato would detect.”'
Actually, to keep the facts in tact, the NSA leaks were made possible by GNU WGet on the leakers' side (same as Bradley/Chelsea Manning) and that horrible Microsoft SharePoint on the leaked side (NSA). It means that Microsoft itself was the problem which it claims to be trying to solve. We
mentioned the role of SharePoint several times before. The acquisition by Microsoft seems to be geared towards stopping whistleblowing and hence defending corruption (so that Microsoft, for instance, can defend the NSA). How ethical a move, eh? So much for a 'champion' of privacy as it purports to be.
Anyway,
there is a 19-year bug door in Microsoft Windows (almost no version is exempted from remotely-invoked full capture), but the press hardly covers it. We
must give some credit to the BBC for covering it (for a change) and
"calling out Windows". Other British press covered other inherent issues in Windows (compromising Tor) [1] and it looks like Dan Goodin is finally covering some security problems in proprietary software [2] rather than always picking on FOSS, then hyping it up with ugly imagery and exaggeration.
A reader of ours suspects that the .NET announcement was designed to distract from horrible security-related news. The .NET announcement is nonsense because it's false (we
wrote two posts about
the .NET PR nonsense) and it also predicts future events like Visual Studio going cross-platform although the latest version of Visual Studio (proprietary) already
runs under GNU/Linux using Wine, i.e. the Windows build works under GNU/Linux as it's fully compatible anyway, for those foolish enough to want it. This is not news and the same goes for Office and other well-known Microsoft software.
Xamarin staff
keeps trying hard to infect GNU/Linux with .NET (that's what they do) and as
this very stupid article about .NET shows, the .NET nonsense did indeed help bury the news about the bug door. This disgusting article even gives credit to Microsoft for having fixed massive 19-year-old bug (only after IBM had found it). When bash or openssl have a bug, then FOSS is all bad, apparently. When Microsoft has a bug door for 19 years, the media says well done to Microsoft (for fixing it after another company forced it to). One has to wonder if this flaw (voluntary or involuntary) is
part of Microsoft's collaboration with the NSA, which made
Stuxnet and has made
yet another piece of Windows malware together with Israel. Here is a new article from
The Intercept:
The Digital Hunt for Duqu, a Dangerous and Cunning U.S.-Israeli Spy Virus
Boldizsár Bencsáth took a bite from his sandwich and stared at his computer screen. The software he was trying to install on his machine was taking forever to load, and he still had a dozen things to do before the Fall 2011 semester began at the Budapest University of Technology and Economics, where he taught computer science. Despite the long to-do list, however, he was feeling happy and relaxed. It was the first day of September and was one of those perfect, late-summer afternoons when the warm air and clear skies made you forget that cold autumn weather was lurking around the corner.
Bencsáth, known to his friends as Boldi, was sitting at his desk in the university’s Laboratory of Cryptography and System Security, a.k.a. CrySyS Lab, when the telephone interrupted his lunch. It was Jóska Bartos, CEO of a company for which the lab sometimes did consulting work (“Jóska Bartos” is a pseudonym).
“Boldi, do you have time to do something for us?” Bartos asked.
“Is this related to what we talked about before?” Bencsáth said, referring to a previous discussion they’d had about testing new services the company planned to offer customers.
“No, something else,” Bartos said. “Can you come now? It’s important. But don’t tell anyone where you’re going.”
Bencsáth wolfed down the rest of his lunch and told his colleagues in the lab that he had a “red alert” and had to go. “Don’t ask,” he said as he ran out the door.
A while later, he was at Bartos’ office, where a triage team had been assembled to address the problem they wanted to discuss. “We think we’ve been hacked,” Bartos said.
They found a suspicious file on a developer’s machine that had been created late at night when no one was working. The file was encrypted and compressed so they had no idea what was inside, but they suspected it was data the attackers had copied from the machine and planned to retrieve later. A search of the company’s network found a few more machines that had been infected as well. The triage team felt confident they had contained the attack but wanted Bencsáth’s help determining how the intruders had broken in and what they were after. The company had all the right protections in place—firewalls, antivirus, intrusion-detection and -prevention systems—and still the attackers got in.
The ability to keep people's rights away and keep the population down depends on passivity and conformity, including the use of Windows. Avoiding Microsoft Windows is imperative for those not wishing to be controlled remotely. As Microsoft's collaborations with the NSA serve to show, mass surveillance on the whole world is practically contingent upon not just innovation but sabotage and social engineering with corporate buddies. Eradication of Microsoft software isn't about competition only; it's about justice.
⬆
Related/contextual items from the news:
-
There are suggestions that the malware code has been around for a while, and has predecessors, and F-Secure warned internet users, anonymous or otherwise, to tread carefully when they download.
"However, it would seem that the OnionDuke family is much older, based on older compilation timestamps and on the fact that some of the embedded configuration data makes reference to an apparent version number of four, suggesting that at least three earlier versions of the family exist," the firm added.
"In any case, although much is still shrouded in mystery and speculation, one thing is certain: while using Tor may help you stay anonymous, it does at the same time paint a huge target on your back.
"It's never a good idea to download binaries via Tor (or anything else) without encryption."
-
Three weeks ago, a security researcher uncovered a Tor exit node that added malware to uncompressed Windows executables passing through it. Officials with the privacy service promptly shut down the Russia-based node, but according to new research, the group behind the node had likely been infecting files for more than a year by that time, causing careless users to install a backdoor that gave attackers full control of their systems.