Reprinted with permission from Mitchel Lewis
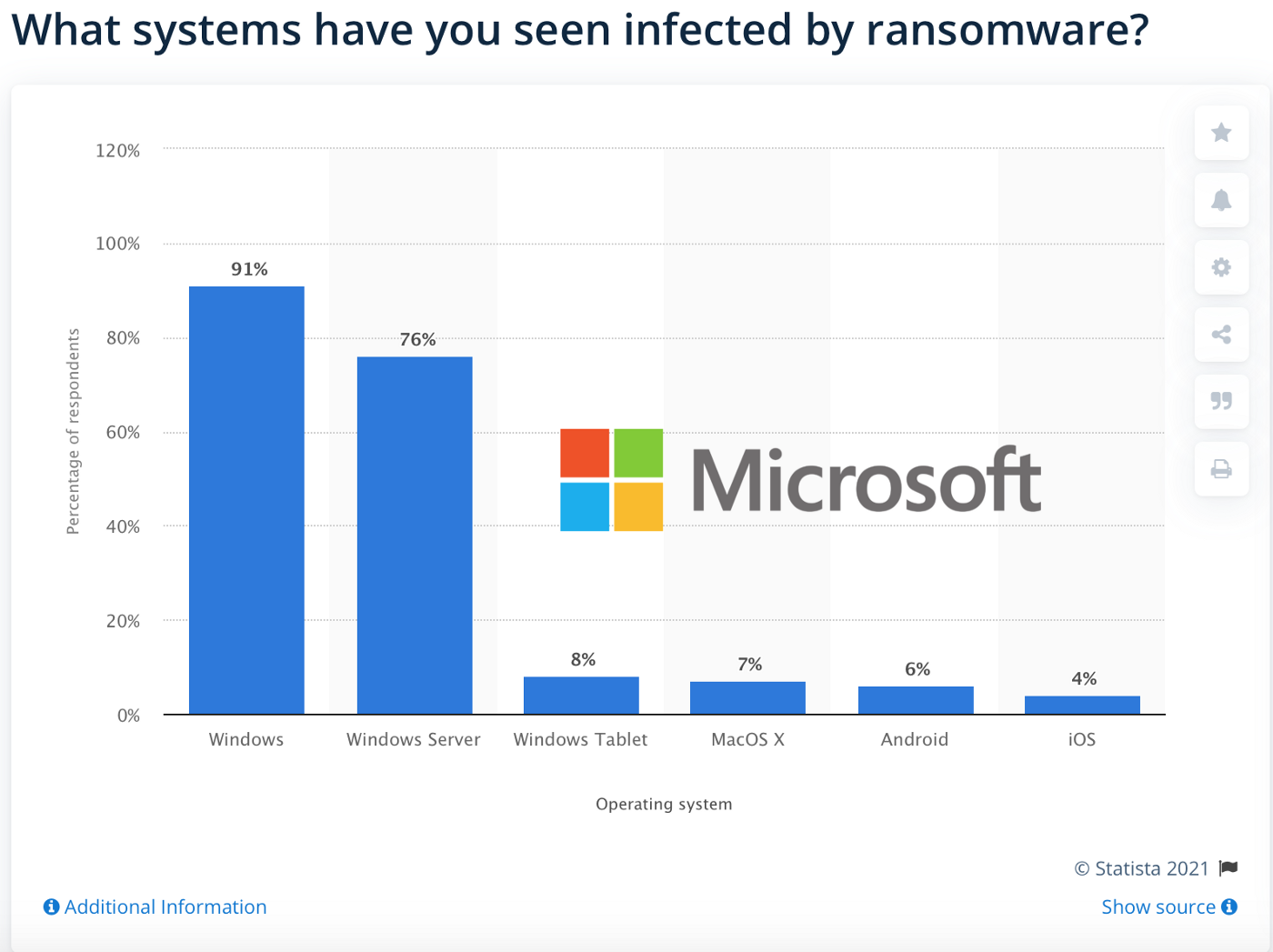
Despite entire industries and trade disciplines existing solely to manage Microsoft architecture and mitigate attacks against it, including a partner network consisting of 17 million+ IT professionals, 99% of all ransomware attacks still occur on Windows. Meanwhile, Microsoft architecture, including its cloud services, maintains a monopoly on botnet, brute-force, malware, phishing, virus, and zero-day attacks just the same. From individuals and small businesses to enterprises and government entities with unlimited IT budgets, everyone standardized on seemingly unsecurable Microsoft architecture are being phished, breached, exploited, and ransomed daily with no end to this in sight. Not even Microsoft is safe from this digital blitzkrieg, hence why they tell us to “assume breach”.
This isn’t to say that Linux OSs and macOS don’t see these attacks on their platforms though; they have and will again. Long-term savings and productivity advantages aside, they just don’t garner the same level of attack that Windows does, nor are they as likely to get exploited at the same rate as Windows when they are attacked. Put simply, Mac and Linux have a smaller
attack surface and get to treat Windows like an umbrella against attacks due to its prominence in the OS space. Both of which are the two primary reasons why I maintain that the best thing that organizations can do to mitigate these attacks, for now at least, is to migrate away to macOS or a Linux-based operating system such as RedHat, CentOS, Ubuntu, etc.
With the above in mind though and when also accepting that there is no aspect of cyber, economic, environmental, homeland, human, and political security along with the security of our infrastructure and natural resources, national security if you will, that isn’t intricately dependent on Microsoft architecture, this reality alone is more than enough to warrant a discussion on whether or not Microsoft architecture is a consequent threat to national security. So, is Microsoft a threat to national security?
In order to answer this question, we first have to address why Windows and other Microsoft services are being breached so often in the first place. We have to see if they can be faulted for this present state, if there is another causal problem that’s beyond their control, or if anyone with their market share is destined to be a victim of their own success and dominance. And to be fair, not everyone will agree with my assessment above or below.
For one and in response to a previous article where I suggested migrating to macOS and Linux to mitigate these aforementioned attacks,
Michael Gillespie, and Marcus Hutchins (MalwareTech) seem to think that Microsoft architecture is exploited most frequently simply because it is the most prominent architecture and that migrating wouldn’t render you any less vulnerable. Put simply, they seem to think that differing attack surfaces are irrelevant to rates of exploitation and that macOS would be exploited at the same rate as Windows if the tables were turned with respect to market share.
Meanwhile, I’m not denying that that prominence is a factor, at all, I’m just saying that attack surface is on the same footing as prominence and that other solutions with smaller attack surfaces will be attacked and exploited at a lesser rate with the same market share which they disagreed with. However, it is also my stance that Microsoft’s
anti-competitive practices aimed at obtaining and maintaining their dominant market share with low-quality products has further exacerbated this issue into what we have before us today; more on this later.
Why this matters to the question of whether or not Microsoft is a national security threat is simple. By suggesting that Microsoft is merely a victim of its own success and that anyone with their market share would see the same rate of exploitation, they’re also absolving Microsoft of responsibility for the present state of threat. But by suggesting that Microsoft’s galactic attack surface is equally responsible with their dominance for their security woes and that Microsoft wouldn’t be in the position they are in now if they had quality products that didn’t have to rely on anti-competitive practices to maintain market share, I’m naturally shouldering Microsoft with their share of the blame in the threat posed to America’s IT infrastructure at present.
One immediate problem with the prominence argument though is that those relying on it seem to resort to it in response to the suggestion of migrating to macOS or RedHat in an effort to mitigate attacks. If you really think about it though, this is irrational and shouldn’t discourage anyone from making the switch. Based on their own logic, Mac and RedHat users would still be much better off than Windows users so long as Windows remains dominant and continues to take all of the flak and function as an attack umbrella.
That said, I’m failing to see how this argument is relevant to their stance, how it invalidates my suggestion, or how it could discourage anyone from migrating to Mac or Linux so long as Windows maintains a dominant market share. If anything, those leveraging this argument seem to be unwittingly reinforcing my suggestion of treating Windows like an umbrella; all of which I’m totally fine with.
Another odd aspect of the prominence argument is that I have yet to see an actual post-mortem or a root cause analysis faulting the dominant market share of Windows as a causal reason for <insert any breach/exploit/ransomware attack here>. In fact, Microsoft doesn’t even take the prominence stance. Instead, their root cause analyses focus on the attack surface, mistakes/oversights, mitigation steps, etc. The anatomy of a breach is never reduced to “They hate us because they ain’t us.” by people who are actually paid to do RCAs for a living as Hutchins and Gillespie suggest; if only it were that simple.
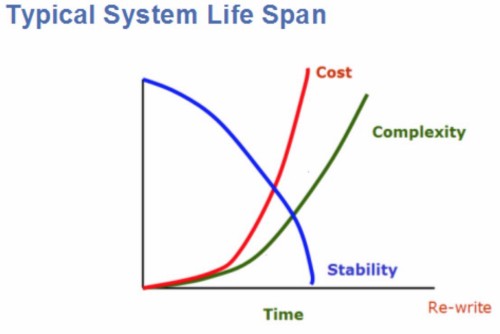
Another major flaw in the prominence fallacy is that those invoking it are unwittingly implying that attack surface has no bearing on rates of exploitation or that the attack surface of each of these platforms is equal; which is bold to say the least. For one and given that attack surface is a function of the overall complexity of their infrastructure, no differently than ownership costs and instability, they might as well be suggesting that all platforms are equally stable with no variance in ownership costs; none of which could be further from the truth.
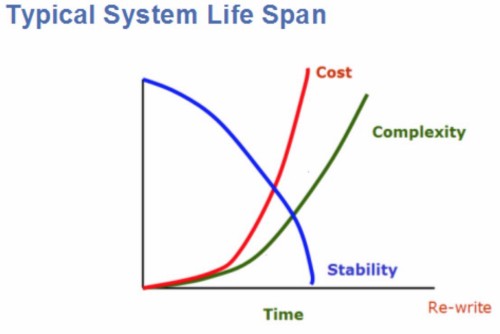
With Windows generating 3x+ the TCO that MacOS/Linux does, analysts can and do infer this is a reflection of disparity in relative complexity, attack surfaces, and stability because they all come hand in hand. Put simply, if one architecture generates significantly more ownership costs more to maintain over its lifespan than another, it’s rational to assume this is due to it being poorly engineered, consequently overly complex, and unstable; attack surface or otherwise. This is what software engineers refer to as
software entropy.
And if they’re going to imply that attack surface doesn’t influence rates of exploitation then the onus is on them to support this stance with data and research. Just as complexity driving cost, instability, and attack surface is fundamental to engineers, so is a ballooning attack surface driving rates of exploitation. This is why engineers treat simplicity like their North Star. That said, great claims that run contrary to fundamentals and conventional wisdom tend to require great amounts of evidence; none of which has been furnished.
On top of lacking a fundamental precedent, yet another oddity of the prominence fallacy is that it lacks historical precedent. It’s important to remember that we’ve only lived in an Information Age with Microsoft at the top. We’ve never lived in a connected world with another OS dominating the market, it’s always been Windows. As such, to say that this would be the case for anyone at the top is a conjecture on its best day.
It’s almost scraping the barrel at this point, but yet another problem with the prominence fallacy is that it ignores how Microsoft obtained its dominant share of the market and why they had to resort to these tactics in the first place. Not only is it Microsoft’s modus operandi to rely on
anti-competitive tactics to obtain and maintain a dominant market share, a monopoly if you will, they only have to rely on said tactics because their products couldn’t garner this market share on merit alone.
Natural selection applies to free markets in that the fittest products will naturally dominate a free market. That said, the best architecture would dominate a market naturally and wouldn’t need to resort to anti-competitive practices. And if Microsoft were the best in class, then they wouldn’t need to be optimizing their architecture for
lock-in while bullying or buying out their competition at every avenue as they are today. They wouldn’t need to implore their partners to
“create stickiness” by entrenching their products to further inflate switching costs.
All said, it’s safe to say that Microsoft is by no means a victim of their own success here so much as they’re a karmatic victim of their own anti-competitive practices and low-rent approach to software engineering; a digital
Icarus complex if you will. There is much that Microsoft can do but doesn’t to simplify their products, shrink their attack surface, reduce ownership costs, reduce their rate of infection, and reduce the consequent threat that they present to America and the world. And to say that they aren’t complicit in the security threat that their architecture poses to America borders on the insane. But does the current level of threat that Microsoft poses constitute them as being a national security threat?
Although I’m not an expert in this regard, those that are have a few qualifying questions in order to really answer this question. IE, in order to classify Microsoft as a threat to national security, threat analysts would have to ask if Microsoft’s undue vulnerability and inorganic prominence mentioned above is a critical threat to our cyber, economic, environmental, homeland, human, and political security along with our infrastructure and natural resources.
Even Microsoft would claim that their architecture is detrimental to all of the aforementioned aspects of national security though. And given the extent of Microsoft architecture throughout personal, industrial, and governmental sectors and its rate of exploitation, it’s hard to see how Microsoft doesn’t expose all of these aforementioned categories to undue risk; a threat if you will.
Further, there is nothing to suggest that a platform with a smaller attack surface won’t have a lower rate of exploitation with the same market share while fundamentals and conventional wisdom suggest smaller attack surfaces lead to lower rates of exploitation. And as a consequence of this, it’s probably safe to say that Microsoft and its architecture is indeed a national security threat in comparison to less prominent Linux and Mac alternatives.
And given that ransomware and anti-trust has already been deemed a threat to national security, it’s not much of a stretch, at least in my opinion, to extend this classification to Microsoft when considering their history with anti-trust and monopoly on exploitation. Nor is it a stretch to suggest migrating onto modern platforms rather than crying about it to the competition exploiting weaknesses; no differently than we do with other critical infrastructure. This is why we rely on nuclear subs now instead of wooden ships.
It’s not a coincidence that the same countries exploiting the US as a whole, China and Russia, are the same countries moving to Linux as I’m typing this. It’s not just about cost-savings and productivity for justifying this move though. And mitigating the risk that Microsoft architecture poses to their national security also happens to be a primary motivating force behind their migrations. Maybe they understand something about Microsoft architecture that America is still slow to realize?
I digress, but even if my assessment above is wrong, prominence is all that matters, and Microsoft isn’t a national security threat, individuals and organizations alike are still better off abandoning the Microsoft ecosystem on any scale in favor of more modern alternatives for the foreseeable future. Although Microsoft gets a lot of criticism for the low quality of their products, hence the persistent updates (552 in 2021 thus far) and a revolving door of CVEs, few seem to see the genius behind them. Microsoft doesn’t need to maximize quality or even compete on that field of play when they can render entire organizations dependent on products of less quality.
Because of this, organizations relying on Windows will have a hell of a time migrating away from Windows and the rest of the Microsoft ecosystem which means that they’re naturally going to drag their toes in doing so; the bigger they are, the slower any attempt at a migration will go. In turn, this means that there is plenty of time for those that can easily migrate away from the madness and insecurity of the Microsoft ecosystem as a means of sheltering themselves from a barrage of attacks safely in the shadow of Microsoft for the time being.
⬆