12.28.14
Posted in Europe, Patents at 6:21 pm by Dr. Roy Schestowitz
Summary: Petition 2848/2013 — a petition which deals with the EPO scandals we have been covering for months — is dismissed in a fashion that leaves the Parliament arguably complicit and at best toothless
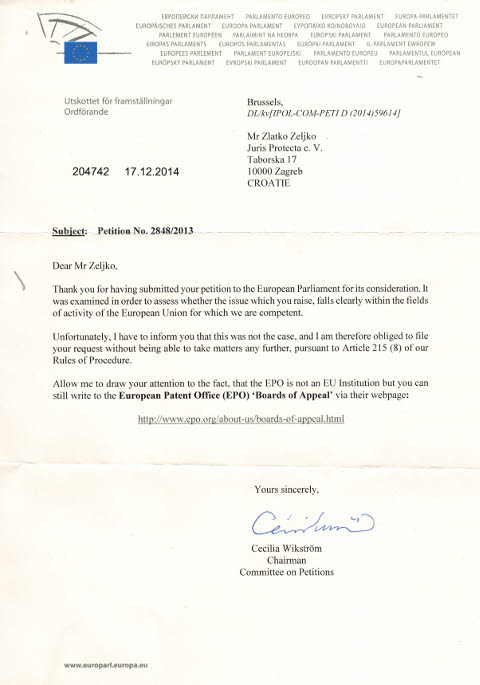
“We just got news from Zagreb,” said one of our numerous sources inside and outside the EPO. The “Petitions Committee of the European Parliament has recently decided not to admit Petition 2848/2013,” said our source, enclosing the image below (click the image for a larger version).
“In a rather bizarre twist,” explained the source, “the Chair of the Petitions Committee (Swedish MEP Cecilia Wikström) suggests that the petitioner should contact the EPO Boards of Appeal.
“However, the EPO Boards of Appeal deal exclusively with patent-related appeal cases and have no competence to investigate managerial appointments at the EPO. That is the responsibility of the Administrative Council which has already ignored a number of requests to submit Topic’s appointment to an independent investigation.”
Moreover, complaints from the EPO have already come from the Enlarged Board of Appeal to the capacity possible, directed at the Administrative Council which is very much complicit in Battistelli’s reign of terror (more on that in future articles of ours). This basically means that the European Parliament is unwilling to intervene and stop a scenario of very gross abuse. What does that say about the European Parliament?
“This basically means that the European Parliament is unwilling to intervene and stop a scenario of very gross abuse.”“So it seems the European Parliament has decided to wash its hands of the affair,” said our source. “This means that although they are apparently content to entrust the administration of the EU Unitary Patent to the EPO, they are not prepared to exercise any oversight with respect to the governance of the EPO.”
Given some of the ‘free’ ‘trade’ affairs as of late, the European Parliament has given citizens of the EU many reasons for distrust and suspicion, “Work that one out if you can,” summed up our source.
The scandals are far from over as we still have a pile of documents to organise, analyse and present. The EPO is a laughing stock, but for those affected by it (including EPO workers) it is not funny. █
Permalink
 Send this to a friend
Send this to a friend
Posted in News Roundup at 5:59 pm by Dr. Roy Schestowitz

Contents
-
Kernel Space
-
For those out of the loop, sdparm allows for setting and getting SCSI device parameters. The ddpt utility is yet another spin-off of dd but with extra features regarding storage control. Both ddpt and sdparm work on not only Linux but also BSDs, Solaris, and even Windows.
-
Applications
-
-
-
Popcorn Time, an application that lets users stream movies and TV shows directly from torrents without having to download them, has been upgraded to version 0.3.6 and is now available for download.
-
Calibre, a complete application to edit, view, and convert eBook files, has received its last update this year and the developer chose to add a number of fixes and other various improvements.
-
The phrase ‘terminal multiplexer’ sounds a bit of a mouthful and a large dollop of jargon. Multiplexing is a method of combining multiple data streams into one stream over a shared medium. This gives us a hint of the function of a terminal multiplexer. It is computer software that can be used to multiplex several video consoles. In English? Well, it allows you to make use of multiple separate terminal sessions inside a single terminal. So one terminal session can act like many sessions.
-
Instructionals/Technical
-
Games
-
Vendetta Online, a space MMORPG (massively multiplayer online role-playing game) developed and published by Guild Software Inc. that comes with Linux support, has received an update for the Holidays and the devs have made some very interesting improvements.
-
In honor of the occasion, we have a few things to announce, including a newsletter update, and some graphical improvements in the latest versions (Shadows in DX11!).
-
-
Q4OS, a Linux distribution built to offer a similar experience to Windows XP, is now featuring a couple of extra desktop environments that should provide some more options for users who want a different look.
-
Released this Sunday was OpenELEC 5.0 as one of the more popular XBMC (now known as Kodi) multimedia Linux distributions.
-
New Releases
-
KaOS, a Linux distribution built from scratch that uses a modified KDE desktop environment and that follows a rolling release model, has reached version 2014.12 and is now ready for download.
-
4MRecover 11.0 Beta, a new distribution based on 4MLinux that is designed to be used specifically for file recovery, is now available for download and testing.
-
Red Hat Family
-
Debian Family
-
Derivatives
-
When an important decision like this is taken, usually all the forks adopt the change, but this is not mandatory. Linux Mint’s Clement Lefebvre said that the decision to switch to systemd on their Linux Mint Debian Edition (LMDE) has not been taken yet.
-
Canonical/Ubuntu
-
Crouton is a script that lets you run Ubuntu or Debian on a Chromebook without uninstalling Chrome OS. Developed by David Schneider, the tool has been around for a few years, offering an easy way to run native desktop Linux apps such as GIMP, LibreOffice, and even Firefox on Chrome OS laptops and desktops.
-
The Ubuntu Manual Team announces that the second edition of the famous manual has been released and is now available for free download.
The Ubuntu Manual usually covers the LTS releases made by Canonical, so it only stands to reason that the current version is now focused on Ubuntu 14.04 LTS (Trusty Tahr) release made six months ago. Like any other book out there, especially in large ones, mistakes occur or maybe it was left out. In any case, this is a digital edition so it’s quite easy to fix and improve.
-
Flavours and Variants
-
The Linux Mint team has ended 2014 in force with a great Linux Mint 17.1 “Rebecca” release, for both the MATE and Cinnamon desktop, but it looks like the Debian edition is also going to be interesting.
-
-
Phones
-
Android
-
Google then rolled out its $35 Chromecast dongle, a streaming device, in mid-2013. Google’s new Android TV operating system is expected to make it easier for software developers to move apps from mobile devices to TVs.
-
-
-
Samsung has rolled out the Android 5.0 update starting with the new Galaxy S series flagship smartphone. Now it looks like the next device to get the Android dessert treatment is the third gen Galaxy Note, suggests a leak.
-
-
Our weekly round-ups of all the newest and best apps are as much a part of Giz UK’s furniture as Mr. T extolling the virtues of PlayStation 4s in comments. So after 52 weeks of investigation, here is a selection of the best Android apps from each month, spanning the crazy year that was 2014.
-
After watching profits tumble this year due to increased competition from other Android phone makers, Samsung sits at an odd inflection point. It can pump out pricey, generic Android phones and watch cheaper phone manufacturers continue to eat its lunch, or it can start innovating in software and services and find new ways to differentiate its devices from the competition.
-
Android 5.0 Lollipop is already available on a bunch of non-Nexus devices, but there are still many more devices waiting to get updated to the newest version of Google’s operating system. Samsung’s Galaxy Note 3 phablet is one of those device, we’ve seen the beta ROM leak for the Exynos version of this handset and also a video showing off the preview of Samsung’s Lollipop update on top of TouchWiz. The update should officially land on the Note 3 rather soon considering the build of it has leaked and it is now available, read on if you’re interested.
-
After Kodak nearly went bankrupt in 2012, the company went looking for ways to stay afloat. Today, the brand announced it is partnering with the Bullitt Group to unveil a new range of mobile devices, including smartphones and tablets, at a CES event in January.
-
The Moto 360, Samsung Gear Live or LG G Watch/G Watch R bring Android to your wrist thanks to Google’s Android Wear. These watches run a dumbed down form of Android, which recently received an update to Android 5.0 Lollipop.
-
The Nexus 7 Android 5.0.2 Lollipop update is finally rolling out to owners of the aging former flagship as it takes the device from Android 5.0 Lollipop to a newer version of the software that delivers bug fixers for several Android 5.0 Lollipop problems.
-
Android smartphone users have been waiting for the newest software to hit their devices. Google successfully rolled out Android 5.0 Lollipop to a handful of units including the LG G3. Interestingly, a newly-leaked photo suggests that its predecessor, the LG G2, will get the update next.
-
Google’s Nexus 7 Android 5.0.2 Lollipop update is currently rolling out to owners of the aging former flagship and it delivers several bug fixes meant to stabilize the software. With that in mind, we take a look at a few reasons why you might want to think about installing the Android 5.0.2 Lollipop update when it arrives on your device.
-
Funding
-
Openness/Sharing
-
After The Pirate Bay made its site available for anyone to host with “minimal web knowledge”, the project has become a hit on the popular developer site GitHub, and 372 copies of “The Open Bay” have been created.
The Pirate Bay was recently raided by police in Sweden, knocking its services offline. Its answer? Make it possible for anyone to create their own Pirate Bay, complete with all of its old torrents, and the ability to carry on the tradition.
-
Programming
-
The better part of four years since the release of PCC 1.0, the second official release of the modern Portable C Compiler is now available.
-
Douglas Carswell, one of Ukip’s most senior figures, has called on the party to stop making “the mistake of blaming outsiders” for Britain’s problems and described disliking foreigners as “not merely offensive, but absurd”.
The former Tory MP’s comments came as a damning new poll showed Ukip had failed to win the support of young voters ahead of the general election in May, who were found to be six times more likely to choose the Green Party.
Mr Carswell, whose by-election victory over his former party in October made him one of Ukip’s most influential faces and one of their two members in the Commons, said it was “interdependence that put the Great into Great Britain”.
His comments come after party leader Nigel Farage defended the language used by Ukip candidate Kerry Smith, who mocked gay party members as “p******s”, joked about shooting people from Chigwell in a “peasant hunt” and referred to someone as a “C****y bird”.
Mr Farage also made headlines last month when he blamed his lateness to a paid-for party event on “immigrants” causing greater traffic on the M4.
-
Flight QZ 8501 — an Airbus 320-200 — lost communication with Indonesia’s Surabaya Juanda International Airport at 7:24 Singapore time on Sunday morning, the airline said. The plane “was requesting deviation due to enroute weather before communication with the aircraft was lost,” AirAsia said in a statement.
“The weather was not good — it was bad — at the estimated location the plane lost contact,” Indonesian Transport Ministry official Hadi Mustafa said.
-
Health/Nutrition
-
Former Nestle CEO claims water is not a human right and should be privatized and controlled. He also states that GMOs have never caused illnesses despite hundreds of independent studies showing otherwise.
So, is water a free and basic human right, or should all the water on the planet belong to major corporations?
Should the poor who cannot afford to pay these said corporations suffer from starvation due to their lack of financial wealth?
-
Security
-
Security geeks reveal government disinformation
-
The FBI announcement last week that it had uncovered evidence in the Sony hack pointing to North Korea appears to have settled the issue for a lot of people—in Washington, DC.
“As a result of our investigation,” the FBI announced, “and in close collaboration with other U.S. government departments and agencies, the FBI now has enough information to conclude that the North Korean government is responsible for these actions.”
-
Everyone has a theory about who really hacked SONY PICTURES ENTERTAINMENT website, according to ASSOCIATED PRESS.
-
Truth can definitely be stranger than fiction, especially if you believe what actor/director Seth Rogen recently said about the production behind his latest film, The Interview.
-
Sony Pictures’ controversial movie “The Interview” collected more than $1m in a limited Christmas Day release, and is expected to make several millions of dollars over the holiday weekend.
-
Although Beijing is Pyongyang’s only significant ally on the world stage, many ordinary Chinese have mixed feelings about their government’s relationship with North Korea, which has been called as close as “lips and teeth.” Some have come to see a reflection of their own condition in North Korea’s poverty, repressiveness and over-the-top propaganda. Online, some commentators have begun to refer to the North Korean leader as “Fatty Kim the 3rd.”
-
The campaign of aggression against North Korea, from the hacking of Sony and the crescendo of noise over the film, The Interview, bears all the markings of a CIA false flag operation.
The hacking and alleged threats to moviegoers has been blamed entirely on North Korea, without a shred of credible evidence beyond unsubstantiated accusations by the FBI. Pyongyang’s responsibility has not been proven. But it has already been officially endorsed, and publicly embraced as fact.
The idea of “America under attack by North Korea” is a lie.
The actual individuals of the mysterious group responsible for the hacking remain conveniently unidentified. A multitude of possibilities—Sony insiders, hackers-for-hire, generic Internet vandalism—have not been explored in earnest. The more plausible involvement of US spying agencies—the CIA, the NSA, etc. , their overwhelming technological capability and their peerless hacking and surveillance powers—remains studiously ignored.
-
Defence/Police/Secrecy/Aggression
-
In December of 2001, the mightiest military force the world has ever known launched ‘Operation Enduring Freedom’ in Afghanistan. Today, the US and NATO military mission in that distant country officially comes to a close, but the foe remains unvanquished.
[...]
To sum up, the US and NATO mission in Afghanistan can rightfully be called disastrous. The America that once was aghast at the idea of torturing people wholesale, is today subdued and numbed to the so-called “black sites” in Afghanistan and around the globe, where torture became the norm. Compared to NSA spying on US citizens, the cover-up or misdirection used to conceal these activities are outright war crimes for most people. Names like Parwan Detention Facility, the Salt Pit, and detainees like Khaled el-Masri and other tortured detainees echo a dark reality of this war on terror. For the leaders who have helped perpetuate these wars, though, cheap talk still resonates. Barack Obama just spoke to US troops on Christmas day about this war’s effects. He said:
-
At least nine people suspected of being militants, including four foreigners, were killed in two separate drone strikes in northwestern Pakistan on Friday, a Pakistani security official said.
-
Two suspected U.S. drones fired missiles at militant hideouts in northwest Pakistan on Friday killing at least seven fighters, Pakistani intelligence officials said.
-
A US drone strike has killed at least three civilians in Afghanistan’s troubled southeastern province of Logar.
-
At least seven alleged Taliban fighters died in two separate US drone attacks in the northern-western Pakistani province of North Waziristan, where the Army is carrying out an air and ground operation against the insurgency.
-
A secretive group of U.S. Air Force intelligence specialists flying aboard American spy planes helped U.S. military commandos kill more than a thousand enemy combatants in just a single year back in 2012.
-
Robert Baer: Assassination doesn’t work, generally. I approached it from the premise that had we assassinated Hitler in 1933 we would have saved lives and destruction. Probably we would have, but in general assassination doesn’t turn out to be a way to avoid war. I take my own experience and other assassinations through history and get a lot into the drone program, which doesn’t work, as well. It’s clear to me, with the massacre at this Pakistani school [at Peshawar]; the CIA in a sense had a role in that, because the two predecessors of the man [Maulana Fazlullah, AKA “Mullah Radio”] who ordered that were both killed by drones. – See more at: http://www.progressive.org/news/2014/12/187945/torture-drones-and-hollywood-former-cia-operative-talks#sthash.jMxsX8Oy.dpuf
-
There were the new tidbits of information on the workings of the president’s “kill list” and the convening of “terror Tuesday” briefings to target specific individuals around the world. There were the insider discussions of ongoing decisions to target American citizens abroad for assassination by drone without due process of law and the revealing emails in which participants up to presidential advisers discussed how exactly to craft the exculpatory “legal” documents for those acts at the Department of Justice.
-
Law professor, writer and social critic Marjorie Cohn explores human rights and US foreign policy, and the frequent contradiction between the two in her monthly Truthout column, “Human Rights and Global Wrongs.” She agreed to an interview with Leslie Thatcher recently about her new book, Drones and Targeted Killing: Legal, Moral, and Geopolitical Issues.
-
Acts of ‘terror’ have been permeating through our televisions screens and newspapers in the West to the extent that we now seem to be surrounded by them. The ‘war on terror’ makes ‘us’ in the West feel safe, but what is almost never considered is how ‘our’ safety affects the lives of the ‘others’ we aim to destroy.
-
Over a lunch in Washington in 1976, James J. Angleton, for years the ruthless chief of counterintelligence at the C.I.A., likened the agency to a medieval city occupied by an invading army.
“Only, we have been occupied by Congress,” he told a young congressional investigator. “With our files rifled, our officials humiliated, and our agents exposed.”
The spymaster had cause for worry. He had endured a public grilling about his role in domestic spying operations by a select committee headed by Senator Frank Church, a Democrat from Idaho, that spent years looking into intelligence abuses. And the Central Intelligence Agency, used to doing what it wanted while keeping Congress mostly in the dark, was in the midst of convulsions that would fundamentally remake its mission.
-
The Obama administration insists that international humanitarian law (IHL) is the applicable law because it claims the US is involved in an armed conflict.
-
On November 24, two weeks before the Senate Intelligence Committee released its “torture report,” Reprieve, a UK-based human rights NGO, published the results of its latest investigation into President Obama’s drone strike program. While Obama was preparing for the inevitable release of the Senate’s report which provided the most extensive insight yet into the CIA’s use of torture during the Bush administration, Reprieve provided insights of its own into the Obama administration’s equally disturbing targeted drone assassination program.
-
On November 24, two weeks before the Senate Intelligence Committee released its “torture report,” Reprieve, a UK-based human rights NGO, published the results of its latest investigation into President Obama’s drone strike program. While Obama was preparing for the inevitable release of the Senate’s report which provided the most extensive insight yet into the CIA’s use of torture during the Bush administration, Reprieve provided insights of its own into the Obama administration’s equally disturbing targeted drone assassination program.
-
The Washington Post, ABC News, and other news outlets stress the report’s findings that targeted assassinations had limited impacts on Taliban targets. While this leaked report does criticize the effectiveness of some High-Value Target (HVT) assassination operations, such characterizations mistake the CIA’s argument that not all counterinsurgency problems can be solved with targeted assassinations as an argument against such operations. Far from dismissing HVT operations, the report advocates them in select conditions.
What the Post and others miss is the role this CIA report played in larger conversations about counterinsurgency strategies among members of the CIA, Pentagon, Congress, White House, and corporate military profiteers. In 2009, these conversations focused not only on the roles counterinsurgency should play in warzones, but whether this counterinsurgency should be based on soft power models (providing needed services, etc.) or hard power models (like Project Phoenix in Vietnam, or JSOC’s targeted assassination programs in Iraq). While this leaked document is only a single report, it provides a view into the types of intelligence analysis that informed President Obama’s rapid increased use of CIA HVT drone operations targeting individuals, including American citizens, in Yemen, Pakistan, Iraq, Somalia, and Afghanistan.
This 18-page CIA report reads like a Harvard International Relations dissertation proposal—an observation more about audience, than author–as it reviews data on past HVT programs, weighing the “positive and negative implications of targeted assassinations” in select insurgency campaigns around the world. High-Value Targeting refers to “focused operations against specific individuals or networks whose removal or marginalization should disproportionately degrade an insurgent group’s effectiveness. The criteria for designating high-value targets will vary according to factors such as the insurgent group’s capabilities, structure, and leadership dynamics and the government’s desired outcome.”
-
After a CIA memo explaining how to get through tighter EU border security checks was leaked to WikiLeaks, the question arose why are there covert agents in the countries the US is meant to share intelligence with, former MI5 agent Annie Machon told RT.
-
While the source isn’t named, Risen’s 2006 book “State of War” discusses a Russian nuclear scientist the CIA used as an intermediary to pass nuclear blueprints containing intentional flaws to Iran for use in their nuclear program. Risen’s account of what the CIA effort code-named “Operation Merlin” suggests that the Russian became concerned the flaws were too obvious and flagged them to the Iranians.
-
One case of many was the CIA’s involvement beginning in 1970 with the overthrow of the elected Chilean President Salvador Allende. They did this through instigating a coup that installed the military dictatorship of General Augusto Pinochet. His repression called the Caravan of Death resulted in the death of thousands and torturing tens of thousands. This account is a sordid story and approval went for it went all the way to the White House. Check out the details on Wikipedia. Unbelievable.
-
When created in 1947, the CIA was meant to coordinate objective intelligence and thus avert some future Pearl Harbor attack, but its secondary role – engaging in covert operations – came to corrupt its independence, a problem that must now be addressed, says ex-CIA analyst Melvin A. Goodman.
-
From its inception in 1947, the C.I.A. was designed with one overriding mission: preventing strategic surprise. Its controversial interrogation program is just the latest symptom of a larger disease, the tyranny of the current. Since 9/11, rather than assessing the threat landscape of the future, the C.I.A. has been mired in the terrorist threat of the here and now. Time and energy spent on targeted killings, black sites and interrogations with water boards and rectal hydration was time and energy that could have been spent better assessing and anticipating emerging challenges like the Arab Spring, Russian President Vladimir Putin’s intentions, or ISIS’s gathering strength. White House officials and warfighters naturally worry most about today. The C.I.A.’s job is to also worry about tomorrow.
-
Prominent JFK assassination researcher and author Lamar Waldron has posted on the White House website a petition calling for the release of all classified government files on the JFK assassination and a pardon for former Secret Service agent Abraham Bolden.
-
A 2010 email released by Wikileaks from a top-level CIA contractor asserts that CIA Director John Brennan, the subject of a story by deceased journalist Michael Hastings, was on a “witch hunt” against “investigative journalists” perceived as hostile.
[...]
The story on Brennan was never published.
Stratfor was once called “The Shadow CIA” by Barron’s. In 2012 WikiLeaks began publishing “The Global Intelligence Files,” over five million e-mails from the Texas-based company.
The email has never been disavowed by Stratfor. When San Diego 6 reporter Kim Dvorak asked the CIA for comment on the email in the context of the Hastings’ death, in an August, 2013 report, a CIA spokesman responded:
““Without commenting on information disseminated by WikiLeaks, any suggestion that Director Brennan has ever attempted to infringe on constitutionally-protected press freedoms is offensive and baseless.” ”
Michael Hasting was killed on June 18, 2013, when the new Mercedes C250 SUV he had just leased hit a tree after running numerous red lights at over 100 mph in Los Angeles. A surveillance video at a pizza shop captured a fiery, violent explosion, which is uncharacteristic of high-speed impacts. Generations of advances in safety design have made accidents exhibiting these characteristics unheard of.
-
Those of us who lived through the atrocities of World War II, the Nuremberg trials of Axis leadership for crimes against the peace and humanity, and the growth of the U.S. national security state are aware of CIA’s principal role. It’s to do things that the government wants done with plausible deniability. Harry Truman’s creation of the CIA was the worst mistake of his presidency.
-
In a December 19th interview in the Russian magazine Kommersant, George Friedman, who is the Founder and CEO of Stratfor, the ‘Shadow CIA’ firm, says of the overthrow of Ukraine’s President Viktor Yanukovych that occurred on February 22nd of 2014: “It really was the most blatant coup in history.” Perhaps he is saying this because of the videos that were uploaded to the Web which showed it to be so, but this statement by him contradicts the description that is asserted by the U.S. White House and the European Union, and the Western press, which description is that Yanukovych’s overthrow was instead just the result of the U.S. Government’s $5+ billion expense since 1991 to establish ‘democracy’ in Ukraine.
-
Wars against nations that haven’t harmed us in any way.
-
Finance
-
Spending by tourists visiting the UK is expected to reach record levels next year, the government has said.
Spending by overseas visitors will top £22bn for the first time, according to forecasts by tourism body VisitBritain.
-
PR/AstroTurf/Lobbying
-
Right-wing media websites continued to undermine their credibility in 2014 by peddling a number of false, ridiculous, and bigoted smears. Here are the top smears from conservative websites The Daily Caller, Breitbart.com, and The Washington Free Beacon.
-
Censorship
-
Censorship battles are usually a good thing, especially when powerful voices and interests are ranged on opposing sides. They illuminate the social and political landscape in a country – our own, as well as those we routinely regard as less enlightened. But the triangular controversy over Sony Pictures’ low-budget comedy The Interview, North Korea and the White House has not made my Christmas.
-
In an abundance of caution, Mr. Szulc’s article was shifted at the last moment from its position in the upper right corner as the lead story of the day. It was further demoted in importance when the revised layout for Page 1 specified a headline one column wide rather than four columns.
-
Iran is to expand what it calls “smart filtering” of the Internet, a policy of censoring undesirable content on websites without banning them completely, as it used to, the government said on Friday.
-
Iran is rolling out new “individual filters” that will let citizens receive access to different parts of the internet, depending on government clearance, and will allow censors to weed out specific website pages – not entire domains, as they currently do.
-
Google, Facebook and Twitter are putting up resistance to orders received from the Russian government to block and remove information about the planned rally by the Russian opposition leader Alexei Navalny next month, which might result into a full scale showdown as Russia tried to censor online content.
-
Censorship is a part of daily life in China. News articles are erased from online search engines, social media sites such as Facebook and Twitter are banned, and CNN is routinely blacked out for Chinese viewers.
Instagram was a huge hit in China — until the government banned it during the Hong Kong protests.
-
Privacy
-
Mishandled data and unauthorized spying are among the allegations mentioned in recently released NSA documents through a records request.
-
The National Security Agency has quietly released more than a decade of reports detailing surveillance activities that potentially violated U.S. citizens’ privacy rights.
-
The heavily redacted reports detail many, many incidents where NSA agents pulled up the wrong information with the database. Each incident is followed by a statement that the data was either not accessed or the query and results were deleted.
Other reports cover agents being granted access to data without the proper training or using searches that were no longer meant to be in effect. Raw data was at times accidentally emailed or kept on an unsecured computer.
There is also at least one instance where an NSA employee purposefully sought out data that was both unnecessary and illegal. One document states a woman went through her husband’s phone contacts “without his knowledge to obtain names and phone numbers for targeting” over a period of 2-3 years.
-
One NSA analyst also looked up her husband’s personal telephone directory without informing him, to get names and contact information for “targeting.” The employee was advised to stop her activities.
-
Former NSA executive Thomas Drake stated that the information, released by the US NSA is Constitutional privacy violations of the 4th Amendment and statute involving process, procedure, unauthorized access and abuse, but the real scope of the agency’s actions still needs clarification.
-
The reports show “how the NSA has misused the information it collects [sic] over the past decade,” Toomey told the Wall Street Journal, and “… shows an urgent need for greater oversight by all three branches of government.”
-
-
Keith Alexander ordered a subordinate to unlawfully search the database on his behalf.
-
-
-
There are holiday document dumps and there are holiday document dumps. And then there is holiday document carpet-bombing from 30,000 feet.
-
The National Security Agency (NSA) is heading to court to defend its Internet data collection program. The Electronic Frontier Foundation (EFF) is arguing that the NSA’s information collection violates the Fourth Amendment, which prohibits unreasonable searches and seizures by the government.
-
Late Wednesday afternoon – yes, on Christmas Eve – the NSA dumped twelve years worth of documents detailing illegal surveillance and wiretapping. However, Sputnik was watching.
-
-
-
-
-
-
-
-
-
-
-
-
A former U.S. government official has filed a lawsuit against the makers of the Edward Snowden documentary Citizenfour, claiming they aided and abetted the former CIA agent in disseminating information related to U.S. National Security Agency leaks that originated with Snowden’s unauthorized release of thousands of classified documents last year.
The Hollywood Reporter says Horace Edwards – a retired U.S. naval officer, the former secretary of the Kansas Department of Transportation and a former pipeline company chief executive – filed the lawsuit in Kansas federal court Friday. Edwards seeks the creation of “a constructive trust” for profits from the film.
-
A recently released documentary about former government contractor Edward Snowden is being considered a potential candidate for the Academy Awards next year, but all isn’t well for the team behind the flick “Citizenfour.”
Attorneys representing a Kansas man filed a civil suit in District Court on Friday last week in which they allege that Snowden, movie director Laura Poitras and others involved in making “Citizenfour” intentionally violated federal law by profiting off of the disclosure of state secrets.
-
Retired National Security Agency official William Binney, who challenged decisions to ignore the Fourth Amendment in the government’s massive — and wasteful — collection of electronic data, faced career and legal repercussions. Because of his courage, he is being honored by former intelligence officials.
Sam Adams Associates for Integrity in Intelligence (SAAII) is pleased to announce that it has selected retired NSA Technical Director William “Bill” Binney to receive its 2015 award for integrity in intelligence. The public is invited to attend the award presentation scheduled to begin at 7 p.m. on Jan. 22at the Berlin Moscow venue, Unter den Linden 52, 10117, Berlin, Germany.
-
The malware known as Regin – linked to the National Security Agency as a tool for tapping mobile phone networks and infiltrating foreign computer systems – now appears to have been developed as early as 15 years ago, making it among the first major pieces of invasive computer software built to enable government espionage.
The program was revealed last month in reports from security companies Kaspersky Lab and Symantec Corp. Soon thereafter, The Intercept published new leaks from NSA whistleblower Edward Snowden that shed light on how programs such as Regin (pronounced Re-gen) were used to collect sensitive, technical information on more than 70 percent of the world’s cellular networks.
-
Both the TPP and TISA include provisions that allow personal information companies to freely move, store, and process their data anywhere in the world. The argument goes that such a measure is necessary to ‘knock down protectionist rules’. In a perfect world, this wouldn’t be a cause for concern, but given all of Snowden’s NSA leaks, the world now knows about the global surveillance state that the US has constructed, including how leading information companies like Google cooperate with Washington in order to perfect it.
-
In all the discussions of what is alleged to be North Korea’s horrible cyber-vandalism against Sony Pictures, I haven’t seen anyone bring up a key issue: The National Security Agency has been for two decades a powerful behind-the-scenes lobby for weak internet encryption and privacy protocols.
-
Earlier this month the Ninth Circuit Court of Appeals became the third federal appellate court this year to hear argument on the legality of the NSA’s bulk collection of telephone metadata.
-
Bottom line is the government is still collecting your data.
-
As curious journalists, tabloid writers, and Hollywood watchers pore over the massive trove of hacked Sony data, the public is being given a rare glimpse into the complicated world of Hollywood and politics. Tucked between bitchy emails about Angelina Jolie and snarky comments on Will Smith’s family are details of a chummy relationship between Sony executives and the CIA, as well as rare insight into how Hollywood views potential movies about NSA whistleblower Edward Snowden.
Sony’s plan to make a Snowden movie got rolling in January 2014, when Elizabeth Cantillon, then an executive producer at Sony, sent company Co-Chairman Amy Pascal an email saying she had successfully closed on the rights to the book, “No Place to Hide,” by The Intercept‘s founding editor, Glenn Greenwald. “[Y]ou will be my Oscar date,” Cantillon promised Pascal.
In March of 2014, Sony officially optioned the rights to Greenwald’s book, which chronicles how he broke the Snowden story, and moved forward with plans for a movie.
-
At what point did the wired world become so inextricably intertwined with everyday life, so much a part of, well, everything else that it started to seem absurd to separate out news about cyber-technology, the Internet and online life from news about, you know, life?
-
The Guy Fawkes-masked hackers of international activist group Anonymous are stepping in to stop Lizard Squad in its tracks — not in Lizard Squad’s attempts to bring down the gaming networks of Sony and Microsoft but in its plan to take down anonymous Internet browser Tor.
-
NSA reform died, as did copyright reform, and patent reform. Immigration reform? Kaput. And the recent election axed important politicians who were allied with the tech industry on certain issues. It was a dismal calendar cycle.
-
Last month David Laufman was named as the head of the Counter Espionage Section of the National Security Division United States Department of Justice.
-
Wow, what a shock to find out that Facebook had been scanning the private messages of its users. I for one am flabbergasted to discover this…not. It fits in with numerous other privacy issues with Facebook in the past and I tip my hat to the judge for making the company face the potential consequences of its actions. It will be very interesting to see what the financial fallout is for Facebook if it ultimately ends up losing this class action lawsuit.
-
Retiring Sen. Jay Rockefeller (D-W.Va.) said it is “unacceptable” that no CIA officials will reportedly be punished for breaching computers used by Senate staffers.
Rockefeller, a former Intelligence Committee chairman, said CIA Director John Brennan has continued to impede congressional oversight and will not answer basic questions about the incident.
The New York Times reported that the unauthorized search was, at some points, carried out with the support of Brennan. The White House must hold Brennan “accountable” if Brennan called for the search, Rockefeller said.
-
Civil Rights
-
Take it easy at the Christmas party if you plan to fly the next day. According to the CIA’s secret travel guide for spies, travellers with “shaking or trembling hands, rapid breathing for no apparent reason, cold sweats, pulsating carotid arteries, a flushed face, and avoidance of eye contact” will arouse suspicion.
-
-
Secret CIA documents advising undercover American spies on how to move through Europe on fake passports have been published online, revealing growing concern that tighter EU rules could blow the cover of US intelligence agents.
Two documents released by WikiLeaks show that CIA agents are currently able to freely enter and travel through the 26 countries of the Schengen Area with only a “minimal” risk that EU border guards will grow suspicious.
There is little chance of being detected when first entering the Schengen Area because European border guards are focused on “illegal immigration and criminal activities, not counterintelligence”, the CIA documents concluded.
-
-
The ACLU presented a letter to U.S. Attorney General Eric Holder Monday demanding an investigation into those responsible for the CIA’s torture tactics.
Recent revelations about CIA torture under former President George W. Bush and former Vice President Dick Cheney between 2001-2009 have put the two figures under increased scrutiny.
-
The ACLU and Human Rights Watch say the offences amount to ‘a vast criminal conspiracy’ and are ‘shocking and corrosive’ to US democracy and credibility
-
President Barack Obama should appoint a special prosecutor to determine if former Bush administration and CIA officials broke the law by having suspected terrorists abducted and tortured in secret prisons by waterboarding and other brutal interrogation methods, two leading human rights groups said Monday.
-
Bacteria to infect the enemy, poisons for assassinations, truth drugs for interrogations, germ warfare and brainwashing
-
For the United States, 2014 was a year of racial violence, rape, war, terrorism, drought and pestilence.
-
As a recent US Senate report showed, the CIA handed over up to USD 30 million to the secret services of an unnamed country that hosted the “black sites” where terrorist suspects captured in Afghanistan and Iraq were detained without warrant and subjected to “enhanced investigation techniques”, that is, torture, daily Rzeczpospolita reported. – See more at: http://www.thenews.pl/1/10/Artykul/191518,Polish-MPs-to-investigate-CIA-payment-for-torture-sites#sthash.uaNfAO9A.dpuf
-
Marek Biernacki, head of the Sejm Special Services Committee, stated that it is necessary to investigate where the money allocated for CIA “black sites” in Poland has gone.
-
This month’s acknowledgment by Poland’s former president that he allowed the CIA to operate a secret interrogation centre throws the Polish government’s appeal against a European court ruling on the jail into disarray.
-
Zimbabwe is one among a number of African countries that assisted the United States of America’s Central Intelligence Agency (CIA) in its notorious rendition programme. This emerged from a recent report that the USA Senate made public recently. – See more at: http://nehandaradio.com/2014/12/28/new-look-zimbabwe-usa-tortuous-relations-via-cia/#sthash.H0yxACxL.dpuf
-
This is the story of John Brennan’s CIA spying on Congress and getting away with it.
Last March, Senator Dianne Feinstein accused the CIA of spying on the Senate intelligence committee as it labored to finalize its report on the torture of prisoners. “I have grave concerns that the CIA’s search may well have violated the separation of powers principles embodied in the United States Constitution,” she said. “I have asked for an apology and a recognition that this CIA search of computers used by its oversight committee was inappropriate. I have received neither.”
-
The Senate report on the CIA’s interrogation program and the spy agency’s official response clash on almost every aspect of the long-secret operation, including the brutality and effectiveness of its methods and the agency’s secret dealings with the Bush White House, Congress and the media. Both reports largely agree on one major CIA failure: the agency’s mismanagement of the now-shuttered program.
-
The Senate’s recent report into the CIA’s interrogation methods has prompted new discussions on how the U.S. should be conducting intelligence gathering, and the level of Congress’ oversight. Glenn Hastedt writes that the report raises the prospect of a new era of intelligence politics characterized by a skeptical Congress that more tightly controls and challenges the intelligence community, as well as one of continued leaks. He also argues that concerns over short political time frames will continue to push the intelligence community to retroactively justify its actions.
-
David Cameron was last night under intense pressure to deliver on his promise to hold a judge-led inquiry into British complicity in torture.
-
The Obama administration won’t be able to throw the torture issue under the table, as the US Senate report on the CIA’s detention and interrogation program has sparked a global public outcry, the Russian Foreign Ministry’s human rights ombudsman told RT.
“It’s to be continued. If you wish, this report is to be continued against the will of those who would like to hush it down,” Konstantin Dolgov stressed.
The Senate Intelligence Committee report on CIA torture following 9/11 will be “discussed in the international forum, including, hopefully, in the UN Council of Human Rights and in some other international formats,” he added.
-
Two responses to the Senate report have stood out for me. The first was by Republican Senator John McCain. On the floor of the Senate, he described the use of torture as “shameful and unnecessary”.
He continued: “The use of torture compromises that which most distinguishes us from our enemies; our belief that all people, even captured enemies, possess basic human rights.”
The second response was that of the Conservative MP David Davis. Referring to “the barbarism of the secret CIA torture programme”, he went on to state that “our association with torture causes us to lose our moral strength and serves to galvanise those who oppose us”.
-
A panel appointed by Central Intelligence Agency (CIA) Director John Brennan to assess blame for the CIA’s intrusion into Senate Intelligence Committee computers has—no surprise—found that those who broke into the computers shouldn’t be punished.
The handpicked committee, composed of three CIA officers; Robert F. Bauer, who served as White House counsel during President Barack Obama’s first term; and chairman Evan Bayh, a former Democratic senator from Indiana who served on the Senate Intelligence Committee, said the three CIA technology officers and two lawyers who participated in the computer hacking should not be punished.
-
The United States Obama administration won’t be able to throw the torture issue under the table, as the US Senate report on the CIA’s detention and interrogation program has sparked a global public outcry
“It’s to be continued. If you wish, this report is to be continued against the will of those who would like to hush it down,” , the Russian Foreign Ministry’s human rights ombudsman Konstantin Dolgov told the media.
The Senate Intelligence Committee report on CIA torture following 9/11 will be “discussed in the international forum, including, hopefully, in the UN Council of Human Rights and in some other international formats,” he added.
-
The Bush administration and the CIA tortured al-Qaida suspects because they wanted evidence that linked Saddam Hussein to 9/11 and could be used to justify the 2003 invasion of Iraq, Middle East expert Patrick Cockburn writes at The Independent.
-
Johnston County leaders say they have no reason and no authority to probe a Smithfield-based company long linked to the CIA’s post-9/11 interrogation program.
A Raleigh-based anti-torture group says a recently released Senate Intelligence Committee report names 17 detainees transported by Aero Contractors, a company that leases space at the Johnston County Airport and at the Global TransPark in Kinston. Based on flight logs and other data, the group, North Carolina Stop Torture Now, says Aero Contractors transported another 14 detainees not named in the report.
Tony Braswell, chairman of the Johnston County Board of Commissioners, said he doesn’t know much about what Aero Contractors does. He said he does know, however, that the company has always been a “good corporate citizen.”
“That’s all we know, and we don’t know if they committed any crimes in Afghanistan or Pakistan,” Braswell said. “Our job is to deal with schools and provide clean drinking water and have a budget for the sheriff.”
But Christina Cowger, coordinator of North Carolina Stop Torture Now, said the Senate report confirms that Aero Contractors was vital to the CIA’s capture and interrogation of terror suspects using techniques that some consider torture. Now, she said, it’s time for elected officials to ask more questions.
-
Human experimentation was a core feature of the CIA’s torture program. The experimental nature of the interrogation and detention techniques is clearly evident in the Senate Intelligence Committee’s executive summary of its investigative report, despite redactions (insisted upon by the CIA) to obfuscate the locations of these laboratories of cruel science and the identities of perpetrators.
-
Buried amid details of “rectal rehydration” and waterboarding that dominated the headlines over last week’s Senate Intelligence Committee findings was an alarming detail: Both the committee’s summary report and its rebuttal by the CIA admit that a source whose claims were central to the July 2004 resumption of the torture program — and, almost certainly, to authorizing the Internet dragnet collecting massive amounts of Americans’ email metadata — fabricated claims about an election year plot.
-
Waterboarding: Yes or no? It’s OK to selectively violate the Geneva Convention, right? Spying on Americans is illegal, but aren’t rules made to be broken?
The world is a confusing place and it’s hard for young people to answer complicated questions like these on their own. Fortunately, students at George Mason University in Fairfax, Virginia, have Professor Robert Deitz to help them navigate the contemporary moral morass. “All of us are familiar with basic ethical notions,” he writes in the syllabus for his Spring 2015 course, Ethical Challenges in Public Policy. “We learn from childhood the idea that some conduct is right and other conduct is not right.”
How’d Deitz get so smart about ethics? He’s magna cum laude from Harvard (like President Obama) and then spent eights years as General Counsel at the National Security Agency, serving as the official Yes Man for General Michael Hayden, and after that three years as his Senior Councillor at the Central Intelligence Agency until 2009. At the former post Deitz rubber-stamped NSA surveillance. At the latter, he sought to derail an independent investigation by then-CIA Inspector General John Helgerson into the agency’s torture and rendition of terrorism suspects.
-
Alissa Starzak will have to wait until after the holidays to find out if accusations she stole and leaked classified Central Intelligence Agency (CIA) documents will scuttle her chances of becoming the U.S. Army’s top lawyer. And her chances could rely on whether Sen. John McCain (R-Ariz.) will back her.
-
The CIA torture report covers over 100 detainees but that’s so pale and insignificant compared with the actual number of detainees who experienced enhanced interrogation techniques, or EITs. That number would run into the thousands, during the period when EITs were deemed legal. Every interrogator was allowed to use them.
-
There’s still no official account of the hundreds, perhaps thousands, of other victims of torture that the CIA is responsible for.
-
Would the security needs of the United States be better served if the C.I.A. were dismantled?
-
Star Jeremy Renner and producer Scott Stuber talk about Kill the Messenger, their film about Gary Webb, the Pulitzer Prize-winning investigative reporter. Webb uncovered a CIA plot in the 1980s that funneled cocaine into the United States to finance arms purchases and other operations in Central America, then faced a campaign to undermine and deny his work.
-
An infamous South African, linked to some of the most shady scandals of this century, has emerged at the centre of a US transcontinental sting operation that netted an alleged drug cartel assassin.
Paul Calder le Roux shopped former American Special Forces-trained sniper Joseph Hunter, who was arrested in Thailand in an operation spearheaded by agents from the US Drug Enforcement Agency (DEA).
-
For South Africa to own up and come clean on its shameful role in assisting America’s immoral WOT is a matter we will continue to agitate for.
-
Human rights group Suaram urged Putrajaya to set up an independent commission of inquiry to unravel the authorities’ involvement in the United States’s torture programmes, following a US Senate report in which Malaysia was implicated.
-
In a recent piece here on The Monkey Cage, Michael Colaresi discussed the need for change in oversight of the CIA and by extension the entirety of the intelligence community. He suggests that in the wake of the Senate Select Intelligence Committee’s report on CIA torture issued Dec. 9, “current and former CIA officials, as well as President Obama, seem bent on missing the relevant lessons to improve governance of national security. The CIA needs more, not less, oversight” (my emphasis).
-
Beyond the drama created by the Report’s surviving multiple assassination attempts, what is there that should grab our attention? The CIA designed and conducted a program of systematic torture of those it suspected of being associated with terrorism. It did so at several of the notorious “black sites,” at Guantanamo and probably elsewhere in Iraq and Afghanistan. Torture was the official policy of the United States government as stipulated by President George W. Bush with the unanimous approval of his national security team – including Colin Powell. The torture program continued for years – carried out by the Army as well as the CIA. Several of those tortured were held on basis of no evidence whatsoever, something that did not shield them from abuse and imprisonment under brutal conditions.
-
Senator John McCain spoke the truth on the Senate floor this month, in response to the release of the Senate Intelligence Committee Report on Torture: “. . . this question isn’t about our enemies; it’s about us. It’s about who we were, who we are, and who we aspire to be.” Many voices insisted that the revelations contained in the report — savage, even murderous treatment of prisoners; illegal renditions; black sites — were not true to the American character. The CIA — having carried out torture; having lied about it at the time; and having lied about it this month in response to the report — was discussed as if it were “not who we are.” But is that true?
American officials, and the American people, know very well what the CIA is, and what it does. It was McCain who, when CIA waterboarding of terror suspects first surfaced as an issue some years ago, recalled that, after World War II, Japanese waterboarding of POW’s — what McCain calls “mock execution” — was one of the war crimes for which Japanese prisoners were hanged. But on the Sunday talk shows after the Senate report’s release, various CIA defenders, including Dick Cheney, talked of such tactics with stoic pride. President Obama decried torture and swore never again, but simultaneously defended the honor of the CIA, and declined to prosecute its war criminals. It comes as no surprise then, that in an NBC/Wall Street Journal poll released last week, a majority of Americans found that “the harsh interrogation practices” laid out in the report were “acceptable under the circumstances.” Really?
-
As details emerge from the CIA Torture Report, many Americans are finding themselves reeling. Yet we are still getting an incredibly sanitized version of the truth. This is because thousands of photos, taken at these CIA black sites, are being withheld by the government under the guise of ‘national security.’
The photos are currently locked in a court case that has been going on for some time, but last Friday the government was forced to submit reasoning for every photo they wanted to remain classified. NY State Judge Alvin Hellerstein is expected to make a ruling shortly regarding their release, but the United States may still attempt to withhold them.
-
Senior CIA officer Alfreda Frances Bikowsky has reportedly been described in several articles by large, credible sources as a linchpin figure in the CIA torture program. However, she was unidentified, but The Intercept has named her as being that instrumental figure in the CIA torture program.
After being called a “key apologist,” “The Unidentified Queen of Torture,” noted as “the model for the lead character in ‘Zero Dark Thirty,’” and identified in having a central role in lying to Congress about the CIA’s torture methods, Bikowsky appears to be the main liar. Last week, according to The Intercept, “NBC News reported that one senior CIA officer in particular was responsible for many . . . false claims.”
The report noted that Bikowsky, remaining unnamed, “also participated in ‘enhanced interrogations’ of self-professed 9/11 mastermind Khalid Sheikh Mohammed witnessed the waterboarding of terror suspect Abu Zubaydah and ordered the detention of a suspected terrorist who turned out to be unconnected to al Qaeda, according to the report.”
-
The CIA’s “enhanced interrogation techniques,” outlined in a controversial report released earlier this month from the Senate Intelligence Committee, was influenced by a Penn professor’s research.
Psychology professor Martin E. P. Seligman famously conducted studies at Penn in the 1960s that revealed a “learned helplessness” in dogs subjected to repeated eletric shocks. Instead of adjusting their behavior upon receiving multiple shocks, the dogs remained in place, providing valuable insight into the workings of depressed or abused persons. Now, his research is being used for torture rather than healing according the the Senate report.
-
Glenn Carle retired from the CIA after 23 years of service. He participated in the interrogation of top-level members of al-Qaida and refused orders to engage in torture.
-
For a clue into how out-of-control, un-American, and just plain wrong our CIA’s torture program was, note the frantic and furious reactions by the CIA establishment to reports about its torturous cruelty.
First were flat-out denials. George Tenet, CIA director during the most vigorous period of torturing al Qaeda suspects, almost blew a gasket in 2007, when a “60 Minutes” interviewer pressed him about the agency’s waterboarding of prisoners. “We don’t torture people.” Tenet practically hollered at the reporter – “Let me say that again to you, we don’t torture people. OK?”
-
Questions are being asked as to why local human rights groups and other non-governmental organisations that fight for people’s rights have remained silent over the US CIA Torture Report.
PAS official mouthpiece, Harakahdaily said there seems to be very little outcry from rights groups everywhere, adding that protest notes have yet to be sent to the US embassy over its treatment of detainees purportedly involved in terrorism.
-
It is very simple. If the CIA is insubordinate to the president, whom the country elected, then it is insubordinate to all of us.
-
The narrative is in place. James Mitchell and John “Bruce” Jessen made millions of dollars having convinced the CIA to construct a torture program via reverse-engineering brutal methods of interrogation used in their previous employment in a military program meant to prepare U.S. military and intelligence personnel for torture by a foreign power or terrorist group.
-
At times, waterboarding rendered al-Qaida terror suspect Abu Zubaydah hysterical. But later, a message to CIA headquarters described an interrogator merely lifting his eyebrow and snapping his fingers, and Zubaydah “slowly walked on his own to the water table” to lie down.
-
The Pew Research Center’s Forum on Religion & Public Life conducted polls in 2009. The surveys discovered that the religious Americans are more likely to believe that torture of suspected terrorists is justifiable.
Five years after the survey was conducted, a new poll was done and it was discovered not much has changed.
The new poll, conducted by the Washington Post and ABC News, found that more Christian Americans, compared to non-Christians, find that CIA “treatment of suspected terrorists” is acceptable.
-
Researchers and reporters had long counted the total number of prisoners who cycled through Guantanamo at 779, but the Senate intelligence committee’s report on CIA torture revealed that there was one more previously unknown detainee. Ibn al-Shaykh al-Libi, also known as prisoner 212, was held at a secret black site at Guantanamo Bay, according to the report, bringing the total number of detainees to 780.
That al-Libi was held by the CIA is long established. After all, al-Libi’s name is notorious as the source of bad information used by the Bush administration to tie Saddam Hussein to Al-Qaeda to support the US invasion of Iraq — information he provided while being tortured in Egyptian custody, and later recanted.
Permalink
 Send this to a friend
Send this to a friend
12.27.14
Posted in News Roundup at 7:56 pm by Dr. Roy Schestowitz

Contents
-
It’s been a while since Mac OS X 10.10 “Yosemite” has been released into the wild, so we have a pretty good idea of how it performs. Mac OS X is also sometimes used as the poster child for a clean and elegant interface (most of the time, anyways). As a Linux writer, it’s my duty to make comparisons not only amongst Linux distros, but also against the competition.
-
As for */Linux taking over the world, I think it’s inevitable. Android/Linux seems to be working on it’s third billion users perhaps by the end of 2015. At some point there will be saturation but the diversity is amazing. I saw a young lady with a Christmas gift of a CyanogenMod Android/Linux smartphone. CyanogenMod is a customization of Android/Linux which gives users more features and some independence from Google. She’s leaving a feature-phone behind as soon as she can switch “sim” cards. Within hours she’s learned to use a bunch of features including speech-to-text (It was nearly perfect)… Strangely, at about the same time her regular notebook PC (GNU/Linux) melted down (hard drive suspected). It will be interesting to see whether she even needs to replace it. This smartphone is just so powerful. Maybe I will get one and leave Beast to serving/storing stuff.
-
Remember the netbooks with GNU/Linux at Walmart, years ago?
-
Canadians tend to lag USAians in some trends (GNU/Linux) and sprint ahead of them in others (Medicare).
-
Desktop
-
One of the oddest things I found about the crowd-funded Librem 15 laptop when writing about it last month was that it wanted to be open-source down to the component firmware/microcode yet they opted to ship with a NVIDIA GPU. In an updated earlier this month, at least they came to their senses and dropped the discrete NVIDIA GPU. While I have no problems recommending NVIDIA graphics for Linux gamers and those wanting the best performance, that’s only when using the proprietary drivers, and certainly wouldn’t recommend it for a fully open-source system — NVIDIA on the desktop side doesn’t do much for the open-source drivers, let alone down to the firmware/microcode level. Instead the Librem folks have opted to upgrade the design to using an Intel Core i7 4770HQ processor that features more powerful Intel Iris Pro 5200 Graphics, which isn’t as powerful as a discrete NVIDIA GPU but at least is more open-source friendly.
-
Setting up a new Chromebook is much easier than setting up a PC. Chromebooks don’t require major updates or antivirus software. You start simply by signing in with your Google Account (or creating that account, if you don’t already have one).
All that said, Chromebooks have some unique quirks—such as limited offline capabilities, and a wonky method for connecting a printer. Here’s everything you need to know to set up your new Chromebook up the right way—starting with the tools that let you replace the Windows software that just won’t work on a Googley laptop.
-
Kernel Space
-
The merge window is closed and 3.19-rc1 was released on Saturday, marking the end of new mainline Linux kernel features for 2014. Here’s a rundown of the exciting new features of the Linux 3.19 kernel for what will become the first major kernel release of 2015.
-
Since Russia has 10 days of holidays in January, I really don’t expect anything to be released until late January or more likely in February. One major change in the upcoming RHEL7-based Virtuozzo Core release is the move from the internal chkpoint code to CRIU. Although there are a lot more details and specifics to come, overall I see this as a very possitive move.
-
This year there’s been kGraft and Kpatch in development as new live kernel patching solutions to reduce downtime when applying maintenance/security updates to the kernel by avoiding system reboots, similar in nature to Ksplice. These solutions were devised independently by Red Hat and SUSE while more recently a unified infrastructure combining both kGraft and Kpatch was proposed. It looks like for Linux 3.20 is when that code will be merged.
-
Jerome Glisse remains hard at work on readying his Heterogeneous Memory Management (HMM) patch-set for eventual integration into the mainline Linux kernel. This HMM memory management will benefit HSA/OpenCL workloads on Linux.
-
Richard Hughes is looking to develop an open-source USB ambient light sensor as an OpenHardware initiative.
-
For the past month there’s been kernel developers investigating “a big unknown worry in a regression” that have left many key kernel developers — including Linus Torvalds — puzzled. It looks like that investigation is finally being close to being resolved.
-
Graphics Stack
-
With the year quickly coming to an end, it’s time to do our year-end driver recap benchmarks from the year for the proprietary AMD and NVIDIA graphics drivers as well as the open-source drivers. To get things started, here’s benchmarks done of the official AMD Catalyst Linux releases of 2014 and testing these drivers on three different graphics cards.
-
A NVIDIA engineer has sent out eleven new patches for the open-source Nouveau graphics driver just in time for Christmas.
-
The xf86-video-modesetting driver continues to be improved as now being built into the X.Org Server.
-
SPI, Software In The Public Interest, was supposed to vote earlier this month on accepting the X.Org Foundation as an associated project to its umbrella organization. That vote, however, has yet to occur.
-
With this week having delivered our 2014 Catalyst Linux Graphics Benchmarks Year-In-Review that looked at the evolution of the AMD Catalyst Linux driver performance over this year, now it’s time to see how the open-source Radeon driver performance has evolved.
-
Benchmarks
-
While on the AMD side there were just three official driver releases in 2014 (Catalyst 14.4, 14.9, and 14.12), on the NVIDIA side there were many more driver updates… NVIDIA continues to do a splendid job of maintaining multiple driver branches for their frequent and stable drivers, along with continuing to maintain multiple legacy driver branches for their older hardware that is still maintained for modern Linux kernel and X.Org Server releases along with important bug-fixes.
-
Applications
-
Shutter, a feature-rich screenshot program that allows users to capture nearly anything on their screen without losing control, has been upgraded and some minor changes have been made.
-
I’ve been hearing the litany of Dvorak enthusiasts for at least as long as I’ve been using Linux, and I can tell you with all honesty that I … have not converted.
-
-
Instructionals/Technical
-
Games
-
SteamOS, a Linux distribution based on Debian and developed by Valve that aims to provide the best gaming experience, has been updated by its makers and a new Beta version has been released.
-
Valve has a massive holiday sale and the Linux users can find quite a few interesting titles among them. We’ve put together a short list of must-have games that are also appreciated by the community.
-
The Humble Bundle website is now hosting a major sale and they have hundreds of discounted games available for purchase. A large number of those games are also available for Linux users and quite a few of them are actually very good. Here is a short list of Linux gems in that offer.
-
Chivalry: Medieval Warfare has today added Linux information to their Steam database, so get your “it’s happening” images ready.
-
Akalabeth: World Of Doom is one of the best games you will come across. This game was the birth of the role-playing game (RPG) genre and the best part of it is that it’s now available on Windows, Linux and Mac OS thanks to GOG.com. This is how the story unfolds:
-
-
Welcome to the future, where the people of Earth need a new home. It’s your job to clear all the undesirable life forms from the planet on which we just dropped you. Start shooting and don’t stop until you’re the only thing left moving.
-
The OpenMW team is proud to announce the release of version 0.34.0! Grab it from our Downloads Page for all operating systems. This release features many bug fixes, improvements to installation and the launcher, and exciting updates to OpenCS. Our “1.0” release remains excitingly close!
-
Making it out in time for some holiday open-source gaming is OpenMW, the open-source engine re-implementation of Elderscrolls III: Morrowind.
-
There’s been talk about Xonotic 1.0 plans going back years, but in reality, Xonotic 0.7 has been the current stable release for the past year and a half while Xonotic 0.8 is slowly coming together as the next version.
-
PlaneShift 0.6.3 has been released in time for Christmas for those pure open-source gamers wishing to engage with this community-based, open-source massively multi-player online role-playing game (MMORPG).
-
Choice of Robots is a new text-based interactive novel developed and published on Steam for Linux by Choice of Games. The game consists entirely of text, so you should really be sure you know what you’re buying before committing to it.
-
-
We’ve covered quite a bit on this topic in 2014. We started the year with OpenPandora, which further opened its hardware by releasing its designs. We looked at the Oculus VR, who acquired and open sourced their networking engine, and later in the year they released a software development kit. The Raspberry Pi is on the list, with emulating retro OSs. And we covered a few controllers, like the one from Steam, the Microduino-Joypad, and Gamebuino: an 8-bit ‘maker movement’ Arduino console.
-
This year was huge for Linux gamers with titles like Civilization: Beyond Earth, Metro Redux, and Counter-Strike: Global Offensive seeing native Linux game releases. There were also new milestones reached for SteamOS, Linux drivers for better handling OpenGL games, etc. Here’s a look at the most popular Linux gaming 2014 milestones along with a call for feedback for what you view as most significant to Linux gaming this year.
-
Minetest 0.4.11 was released today as the latest version of this popular open-source game alternative to the extremely popular Minecraft game.
-
Darwinia is one of the most unappreciated strategy games and now Linux users have the opportunity to get it with a huge 90% discount on Steam for Linux.
-
Desktop Environments/WMs
-
K Desktop Environment/KDE SC/Qt
-
Inspired by Aurélien Gâteau’s blogpost and the thread on KDE Forums, I decided to change my global KWin short-cuts as well to see how it fares.
-
For a project at university I recently needed a plotting widget to display some data. Naturally, Qwt came to my mind. I’ve already been using it in a number of other projects and it works great.
The one drawback, however: The project was intended to be run on the Raspberry Pi. Now the X-Server on the R-Pi doesn’t have any 3D acceleration yet, so the performance of Qwt was subpar.
-
Back in 2003 Krita had never been released and the application was only able to do some very crude painting. I think the main reason that I started contributing to Krita back then was that I was much more comfortable with the single window UI and the fact that it used Qt/KDE and C++. In the early days I would never have imagined that I would be still with the project after 10+ years and how big the project is now. Even that the project exists today is a miracle and result of many developers putting in effort without ever knowing how it would develop. For the first few years we had almost no users and the users that we had were die-hard KDE users. At the time that wasn’t a bad thing as it allowed us to do some radical changes and experiments. Many features that were developed during this time still provide the base for the current Krita.
-
-
GNOME Desktop/GTK
-
Libra is one of the best theme derived from flattastic theme suite. This theme is light with combination of blue color and it has menu colored buttons (minimize, maximize, close). It features a modern and clean look, with fully integrated and tested support for many of the popular desktops Including: Unity, Gnome Shell, Cinnamon, Mate, Gnome Classic & Fallback. It has been designed to be compatible with most GTK2/3 desktops out of the box. Rave-X-Colors and Ursa icons used in following screenshots. You can use Unity Tweak Tool, Gnome-tweak-tool or Ubuntu-Tweak to change themes.
-
GNOME developer Richard Hughes who is responsible for a lot of work on open-source software as well as being the engineer behind the open-source ColorHug color calibrating device is now looking at the possibility of making a USB ambient light sensor that’s open-source. A few days ago I wrote about Richard’s brainstorming over making a SD card based random number generator to provide fresh entropy to the system, but he’s received a lot of feedback with similar devices that have already been developed and are too Linux/open-source friendly.
-
-
Webconverger is a Linux distribution used for deployment in places like offices or Internet cafes, where only web applications are used. A new update has been released and the version number has advanced to 27.
-
Emmabuntüs 2 1.09, a distribution created for reconditioning old computers and relying on the robustness of Xubuntu 12.04.5 LTS, has been released and is now ready for download.
The Emmabuntüs developers only use LTS editions of Xubuntu, and that means they actually have two distros out right now that are maintained and improved. We had Emmabuntüs 3 1.0 released a few weeks ago, but that one was using Xubuntu 14.04 LTS as the base. Now, the old branch based on Xubuntu 12.04, Emmabuntüs 2, has been improved as well and the devs have made quite a few changes.
-
We would like to wish to all the Chakra community a happy and creative 2015!
-
New Releases
-
SparkyLinux 3.6, a lightweight, fast, and simple Linux distribution designed for both old and new computers featuring customized e19, JWM and Openbox desktops has been released and is now ready for download.
-
Black Lab Education Desktop 6.0 Beta 2, a Linux distribution built for an education environment and based on the Black Lab Professional Desktop series, is now ready for testing and download.
-
4MParted is a new Linux distribution based on the 4MLinux 11.0 OS and GParted. It has a simple goal, to provide users with the tools they need to make adjustments to the partition of their PC without having to actually go into the operating system.
-
OpenELEC, a powerful embedded operating system built specifically to run the Kodi media player hub and to run on most available hardware, has been updated once more and the developers are getting closer to the final version.
-
KaOS is very proud to announce the availability of the December release of a new stable ISO. This ISO marks two major milestones for this distribution. Since it’s inception almost two years ago, a need to be ready for UEFI installs has always been a priority. That was tied though to getting a modern Qt based installer that could handle such UEFI installs. With this ISO, both are implemented.
-
The Christmas release improves XDG standards compliance, brings more accurate GTK3 theme and fixes screen resolution detection weighty bug. Several internal improvements and bugfixes has been closed as usual.
-
PCLinuxOS/Mageia/Mandriva Family
-
PCLinuxOS 2014.12, a free Linux distribution aimed at desktop computers and laptops, has been made available and the devs have made a number of important upgrades.
-
Red Hat Family
-
For years, Red Hat executives fielded questions about its open source software from prospective customers: “Is open source safe? Is it secure? Is it reliable?”
But such inquiries have faded as open source software has gained momentum, CEO Jim Whitehurst wrote in a recent blog posted on the website of the Raleigh-based company. Red Hat is the leading open source software company.
“Today, it is almost impossible to name a major player in IT that has not embraced open source,” Whitehurst wrote. “Only a few short years ago, many would have argued we would never see that day.”
-
As open source advances, education is key for IT professionals to understand how their organizations can best take advantage of the technologies that are driving everything from cloud and mobile to big data and the Internet of Things.
-
It is confirmed: 2014 has been a great year for Red Hat. [On Dec. 18], we announced third quarter results of our fiscal year 2015 and, with that, celebrated our 51st consecutive quarter of revenue growth – more than 12 years of consecutive revenue growth. Thank you to the team of Red Hat customers, partners, open source contributors, and associates around the world, for helping us propel Red Hat to new heights. While 2014 has been a fantastic year for Red Hat, it has also been a banner year for open source.
-
Fedora
-
It was a fairly slow news day today in Linuxville. Nevertheless, Steven J. Vaughan-Nichols explains why 2014 “was the best of years, it was the worst of years.” Gary Newell asks if the Debian-fork Devuan is a good idea and Serdar Yegulalp looks at the competing live kernel patchers and Fedora 21 is reviewed again, twice.
-
Still a bit slow on the news front but yesterday, like a Christmas present, ROSA Fresh R5 was released. Simon Phipps offers his Open Source confessions and Phoronix.com reviews the year in Ubuntu. Also, William Moreno Reyes offers a few thoughts on his recent Fedora 21 Workstation install.
-
Also nearing release is Korora 21, the Fedora remix from down under, which should be ready sometime early in the new year, according to lead developer Chris Smart… As for the speakers for the Southern California Linux Expo SCALE 13x, the SCALE Team has chosen most of the speakers and they are setting the schedule for the four-day event in February. Keynoters have yet to be named, and I have it on the highest authority that SCALE 13x could be unique regarding the keynotes and many of the speakers this year.
-
Why did Fedora 21 have to be so buggy? Why? I wanted it to succeed, I wanted it to be cool and fun, just like the last release. There was so much potential, and then, something went wrong. Quite a few somethings, apparently. Installer partition selections, bootloader, login, codecs, printing, desktop effects. Damn. Fedora, where art thou?
Anyhow, Fedora 21 KDE is just not as good as it should be. Not as good as its predecessor, not as good as its rival, and most importantly, not as good as Fedora. There must be a baseline to quality, and it must never be crossed, downwards. This time, I did not get what I wanted, and I’m sad, because I know that Fedora can do it. We’ve all seen it happen. So more time is needed in the special oven for naughty distros. Perhaps I rushed testing just days after the official release, but it is how it is. 6/10. Done.
-
I am definitely going to recommend Fedora 21 to users fed up with Unity/Ubuntu and contemplating a change. Novice users may wait for Korora release. The 6 month release cycle of Fedora will ensure that you always have the latest packages. Many reviewers suggest to avoid Fedora for production purposes. Possibly in 2015, I’ll try to use Fedora for a year or so for all production purposes to understand if it is true or not.
-
On Sunday I wrote about how I found it surprising that Fedora didn’t enable F2FS support within its Linux kernel while it packaged the user-space F2FS tools and contains plenty of other experimental/early-adoption features. The discussion resulting from this article about F2FS for Fedora has been both good and bad.
-
-
Debian Family
-
Derivatives
-
Canonical/Ubuntu
-
Ubuntu, the latest LTS version 14.04 operating system (OS), is definitely worth trying. My statement is backed by the fact that Ubuntu won the operating system of the year award from W3tech not only once but three times consecutively, followed by admiration from major players in the market and an inclusion of major organisations such as Lenovo, Dell, HP, IBM, and Asus etcetera.
-
The Unity desktop environment has a simple and rather ineffective system notification mechanism and it looks like that’s not going to change, not even with the arrival of Unity 8.
-
Flavours and Variants
-
Remember Macbuntu? It’s a MAC OS X transformation pack for Ubuntu, which lets you tweak your Ubuntu desktop into looking like an Apple’s offering. I have tried it about four years ago, on Lucid, but haven’t played with the software since Unity replaced Gnome 2 as the desktop environment. I decided it was time for another attempt.
If you read online, you will find multiple references to Macbuntu, so it can be a little confusing. There’s the SourceForge hosted project, and there’s the initiative by Noobslab, who have packaged together a handful of PPA and scripts to help you refashion your Unity desktop in a modular and easily reversible way. We checked.
-
-
Erle Robotics launched a ROS-enabled, open source “Erle-brain” autopilot that runs APM directly on Linux. The device also powers an “Erle-copter” drone.
Over the last year, Spanish firm Erle Robotics S.L. has been working with 3DRobotics to develop an open source BeaglePilot autopilot for drones that can run Linux on 3DR’s popular, Arduino-based APM (ArduPilot Mega) platform. The APM Linux port was developed by both companies, as well as several academic institutions. The BeagleBone-based “Erle-brain” autopilot is built into the $490-and-up Erle-copter quadcopter.
-
The latest low-cost, Linux-friendly ARM single board computer is the Orange Pi that’s trying to ride off the success of the Raspberry Pi.
-
Phones
-
Tizen
-
Global smartphone leader Samsung Electronics Co Ltd is planning a new product launch next year based on its own Tizen operating system, the South Korean giant’s strategic push to free itself from Android and blaze its own software path.
But after years of development and a handful of Tizen-powered smartwatches and cameras, the only product confirmed for a 2015 launch so far is a TV set.
-
Android
-
Dell is about to begin selling an eye-poppingly beautiful slab of hardware. Will anyone notice?
Pricing and availability will be announced for the Venue 8 7000 at CES in January, a Dell spokeswoman said in response to an email query. (The tablet had initially been expected for release at the end of November.)
-
Last week, Google released an Android 5.0.2 Lollipop update for the Nexus 7 2012. The update does not appear to be rolling out OTA just yet but that should change in the future. While many users will likely want to rush into downloading the new Android 5.0 Lollipop update, we want to take a look at some reasons why Nexus owners might want to think about skipping Google’s brand new Android 5.0.2 update on the day it arrives.
-
The two-year-old Galaxy Note 2 has surprisingly been included in the list of devices that are slated to get the latest Android 5.0 Lollipop firmware update, according to Samsung’s official website in Finland. A section of the website shows a table, providing details about a number of handsets and tablets that are scheduled to get the latest update.
-
-
After launching its first Android tablet in November, the Nokia N1, the Finnish firm is now rumoured to be working on an Android 5.0 Lollipop-based smartphone called Nokia C1. If the rumour is true and smartphone is released as the Nokia C1, the firm would be breaching the Microsoft acquisition agreement.
-
Here we are at the end of 2014, a year that was full of smartphone launches. There’s a hard-fought battle on the high-end Android smartphone market and it’s getting harder and harder to choose a smartphone that fits your needs.
-
With applications able to run in the background and sync as they see fit, Android can rapidly eat through your cellular data allowance if you are not careful. While it’s fine to let the data run free on wi-fi, you’ll want to restrict your data usage when out and about.
-
-
A Samsung Galaxy Note 3 Android 4.4.4 KitKat update is hitting the United States ahead of the Galaxy Note 3 Android 5.0 Lollipop update that’s confirmed to arrive sometime next year.
-
If your children are getting to grips with a new Android tablet for Christmas, here’s our pick of the most educational and entertaining kids’ apps this year
-
It was an excellent year to be an Android gamer in 2014. More developers embraced the platform—which means not only more games, but also timelier releases. And the selection gets better and better by the week, with an array of excellent cheap titles and deeper-dive premium games that justify the added expense. Even the free-to-play market generated some serious winners this year.
-
Earlier this week, we told you about a massive sale Amazon was having that would let you download $220 worth of Android apps for free. Well that sale is now live and you can go right now to Amazon’s Appstore to get 40 Android apps that would normally cost a total of $220 for free right now.
-
-
Android Lollipop, while chock full of features and a fresh new UI, still doesn’t support Flash enabled videos online. A once killer Android feature, Adobe stopped supporting their Flash player for Android devices many moons ago, as websites too made the move to more mobile friendly format.
-
Have you ever heard the theory of winning a battle, but losing the war? A judge in India has lifted the sales ban on OnePlus One Android smartphones in India, but is it enough to ‘win the war?’
-
-
‘Tis the season of goodwill, apparently, and in an effort to spread a bit of festive cheer Amazon is offering up a bundle of paid apps and games for the princely sum of nothing.
The deal runs from December 24 through 26 and brings with it a not-to-be-scoffed-at saving of $220, with the Android apps ranging in price from 99 cents to a whopping $65.
-
Samsung is slowly starting to update its top Android handsets to Android 5.0 Lollipop, with the Galaxy S5 having already received Lollipop builds in certain regions, and the Galaxy Note 4, Galaxy Note 3 and Galaxy S4 also having been confirmed to be getting Lollipop updates in the near future. Now, GSM Arena discovered that even older Samsung devices will receive Google’s Material Design overhaul and other Lollipop features in the near future.
-
If you find an Android Wear device under your tree this year, the very first thing you’ll want to do is make sure you know how to control which apps are allowed to send you notifications. After all, if your wrist vibrated every time someone favorited one of your tweets, you’d get pretty annoyed very quickly.
-
For most people with a smartphone or tablet, their most-used apps weren’t released in 2014. Facebook, Twitter, Google Maps, Candy Crush Saga, Kindle, Spotify, Clash of Clans, YouTube… these apps have been out for years, albeit regularly updated since their original releases.
-
-
-
Many app developers choose to launch first on Apple’s iOS platform.
But one app developer — The Hunt‘s founder/CEO Tim Weingarten — told VentureBeat that he would take a different approach in the future.
While “the conventional wisdom is build first for iOS,” he said, “if we had to do it all over again, I would launch on Android first,” or at the same time as iOS. More than half of The Hunt’s downloads are to Android devices.
-
Today’s the Christmas Eve and below you can find some of the best Android Games that you can play in case you’re on your way home or to a friend’s house. All titles are listed randomly and you can find RPGs, puzzlers, action shooters and others that should offer you enough entertainment before the end of this year.
-
-
-
As it turns out, Boeing might actually be BlackBerry’s best friend right now. You see, the ultra-secure Boeing Black handset will come with support for BlackBerry’s BES 12 device management service. It’s not much of a stretch to assume the Boeing Black might also feature BlackBerry’s hallmark secure messaging system.
-
The automotive world is rapidly leaping into the next generation of infotainment systems. We already know that the CarPlay from Apple and Sync 3 from Ford are on the way. Even Microsoft has something up its sleeve. Google showed off its future concept for Android Auto earlier this year and promised that it would be available by the end of 2014. That didn’t happen, but the technology giant has put a tentative plan in place for its challenger in this crowded field.
-
-
-
Millions use their smartphone as their primary camera because it is always with them and sharing those photos is easy from your phone. Kodak announced they will be launching an Android-powered smartphone at CES in a couple weeks with a tablet and connected camera coming later in 2015.
-
I have also repeatedly evaluated GNU/Linux as a platform for my daily writing and administration. Each time, I’ve found it fairly easy to install (moreso every time I try) and easy to add applications. I’ve never had problems with malware, but at some point in the life of the system, a problem arises that at best causes an inconvenience (like the sleep mode failing) and at worst leaves the system impossible to boot.
-
Ho hum. Another year, another slew of open source announcements that prove the once-maligned development methodology is now so mainstream as to be tedious. Running most of the world’s most powerful supercomputers? Been there, done that. Giving retailers the ability to deliver highly customized paper coupons to consumers based on warehouse inventory nearby? So 2013!
And yet in 2014 we had a few events in open source that managed to surprise us, and suggest an even brighter future.
-
On Christmas Eve, Marvell announced the release of a new open-source driver for one of its 802.11ac chips in cooperation with Linksys.
-
Web Browsers
-
Mozilla
-
2014 was both a phenomenal year for Mozilla while a wild ride for us as we waded through what seemed like hit after hit from the tech press but we fared well.
-
SaaS/Big Data
-
Cloud computing is no longer an issue of “if” for enterprises anymore, clearly all businesses will adopt or are adopting cloud in some shape or form as the basis for transforming their IT infrastructures into more agile and flexible organizations.
Whether from government, telecoms, retail or even the highly regulated financial sectors, companies across the board are jumping on the cloud bandwagon in efforts to create a new model for IT.
-
Hewlett-Packard is bullish on the future of the cloud and on network functions virtualization (NFV). Helping to lead HP’s NFV and cloud efforts is Senior Vice President Saar Gillai, who is also the general manager for NFV as well as the chief operating officer for HP Cloud.
-
Databases
-
A developer has modified the PostgreSQL database software so that it can exploit GPGPU computing for faster performance.
-
Healthcare
-
Healthcare is one of the most urgent socioeconomic issues of our time. This year, Opensource.com saw a variety of news and feature stories about applying the open source way and open source software (including tools) to alleviating the many problems faced by the healthcare industry. Here are this year’s best of the best from Opensource.com in open health.
-
FSF/FSFE/GNU/SFLC
-
Version 2.25 of Binutils is new this week. Binutils consists of the GNU linker and assembler along with other common binary tools to GNU/Linux environments.
-
Project Releases
-
Merry Christmas and happy holidays, everyone! We are proud to announce the release of Kodi 14.0, which comes with a new name, a new logo, and a wide variety of new features, but underneath the new coat of paint remains the same software we all love.
A detailed changelog for Kodi 14 can be found under milestones on our code repository, should you be interested. With that said, let’s take a look at some of the features that come with Kodi 14.0.
-
-
Kodi 14.0, the successor of the famous media hub XBMC, has been released. The developers have been working on this new version for some time and it’s finally here.\
-
The Subsurface development team proudly announces release 4.3 of Subsurface, an open source divelog and dive planning program for Windows, Mac and Linux.
-
BusyBox 1.23.0 is the new release and it brings a wide variety of changes across the table. There’s far too many changes to note but among the BusyBox 1.23.0 updates are a lot of fixes for ash, find improvements, ntpd improvements, etc.
-
Public Services/Government
-
Municipalities using open source are reaching out to other towns and cities, motivating them to switch to this type of software. The past four months, members of Finland’s Centre for Open Source Solutions (COSS) have been visiting towns around the country, talking about their use of free and open source.
The so-called ‘Open Knowledge Roadshow 2014’ involves six municipalities, Turku, Mikkeli, Pori, Oulu, Tampere and Rovaniemi. Apart from reaching out to their colleagues, the towns of Mikkeli, Oulu and Rovaniemi also organised a workshop, reports COSS on its website.
-
All of Romania’s public administrations are to use open source and open standards software. The government is making this a (minute) part of the 2014-2020 Digital Agenda, made public in November. The approach will increase interoperability of ICT systems.
-
sIn 2015, Cenatic, the open source software resource centre of the Spanish government, will campaign to get enterprises to implement, share and re-use open source solutions. The centre wants to help companies select the right free software solutions. It will also promote sharing and re-use, and reinforce the network of free software service providers.
-
Licensing
-
One of the most important updates in VVV 1.2 is the addition of a license. The project has adopted the open source MIT license after a six-month long discussion with participation from more than 50 contributors on the project.
-
Openness/Sharing
-
-
Goodwell toothbrushes, equipped with a medical grade aluminum handle have bristles made from Binchotan which is a biodegradable fiber that can repel negative ions, remove plaque and bad breath.
-
The OpenROV submersible is a low cost and open source kit designed for exploration and education. Originally launched on Kickstarter in 2012 it has now grown into a dedicated global community launching missions everywhere from Hawaii to the UK. The project raised $111,662 from 484 backers and has now reached version 2.7. Today the kit costs $899 with a fully assembled version coming in at $1,450 which you can purchase from the online store. Units weigh in at 2.6kg and normal battery life is expected to last between 2-3 hours depending on use.
-
Open Data
-
Not long ago, I was speaking at the National Association of Government Web Professionals. At the same conference, Mark Headd was speaking. We were speaking on different open data topics. My discussion was about the difference between open government and open data and his talk was about API [First].
-
Programming
-
We are pleased to announce the release of Ruby 2.2.0.
Ruby 2.2 includes many new features and improvements for the increasingly diverse and expanding demands for Ruby.
-
-
Science
-
Security
-
A vulnerability in the widely used Git open-source development tool has been revealed, but there is a patch.
-
Boies, along with three attorneys representing the States, brought Microsoft to it’s knees — or so it seemed at the time.
On November 5, 1999, Judge Thomas Penfield Jackson found that Windows dominance on the PC made the company a monopoly and that the company had taken illegal actions against Apple, Java, Netscape, Lotus Notes, RealNetworks, Linux, and others in order to maintain that monopoly. He ordered Microsoft broken in two, with one company producing Windows and another handling all other Microsoft software.
As we all know, Judge Jackson’s solution was never implemented.
Although an appeals court upheld the verdict against Redmond, the breakup of the company was overturned and sent back to the lower court for a review by a new judge. Two years later, in September, 2001, under the Bush Administration, the DOJ announced that it was no longer seeking the breakup of Microsoft, and in November reached a settlement which California, Connecticut, Iowa, Florida, Kansas, Minnesota, Utah, Virginia and Massachusetts opposed.
The settlement basically required Microsoft to share its APIs and appoint a three person panel that would have complete access to Microsoft’s systems, records, and source code for five years. The settlement didn’t require Microsoft to change any code or stop the company from tying additional software with Windows. Additionally, the DOJ did not require Microsoft to change any of its code.
-
-
-
-
-
Are hackers and malware purveyors targeting cloud and network service providers over the holidays? With the news of the Sony hack fresh in everyone’s minds, unusual hacking reports are flowing in.
-
Defence/Police/Secrecy/Aggression
-
There have been some rumblings from officials in Russia in recent days. I caught something like “the US needs to take another look at the real story behind the shooting down of Malaysian passenger jet over Ukraine last July.” The US-NATO were quick to blame Russia after the plane was shot down – the same kind of campaign we now see with North Korea over the Sony ‘comedy’ that I believe is truly aimed at creating more antipathy towards that nation. Today I stumbled upon this fascinating story about an eye witness who claims that it was a Ukrainian military jet that accidentally took down the Malaysian airliner.
-
The world is in turmoil. Like in the early 1940’s, something tremendous is gaining shape, something irreversible.
Almost all of us who have been analyzing the Empire fighting against the propaganda and nihilism it spreads, and its venomous tentacles extending to every corner of the globe, know that ‘appeasing’ Western imperialism is clearly impossible, as it is impractical, and even immoral.
Just as George W. Bush (clearly borrowing from fundamentalist Christian rhetoric), liked to say: “You are either with us or against us”. Countries are now evidently put on the spot: ‘they either accept the Western neo-colonialist doctrine’, or they get destroyed, one after another, as were Iraq, Afghanistan, Libya and Syria.
No logic can help, no negotiations, no international mediation from the United Nations. The willingness to compromise is mocked. Appeals for simple human compassion do not move the rulers of the Empire even an inch.
-
Environment/Energy/Wildlife
-
British driver Gavin Rigby told BBC News he had taken 11 hours to drive between Val d’Isere and Bourg Saint Maurice – a journey which would normally take 30 minutes.
-
Finance
-
With the federal government forecasting a $9 billion shortfall in revenue over the next two years as iron ore plunges to new five-year lows, the view of China from Australia is one of a country struggling to maintain the growth that turned it into a economic superpower.
Shadow banking, ghost cities, slumping property prices, a manufacturing slowdown and debt defaults are just some of the headwinds that threaten the world’s second-largest economy.
-
Censorship
-
Minnesotans protesting police violence and institutional racism could face “staggering” fees and criminal charges for a protest at Mall of America, with the City of Bloomington announcing plans to force organizers to pay for the mall’s lost revenue during the exercise of their free speech rights, highlighting important questions about free speech in an era of privatized public spaces.
-
My thanks to John B for giving me a heads up about this, I found his message to be quite fascinating. And if it’s found to be true that Facebook is blacklisting sites that criticize them, then I consider it a badge of honor to be on that list. There’s no way for me to know if Facebook actually is doing that, but I have wondered why I get so much more referral traffic from Twitter and Google+ than I do from Facebook. It seemed quite odd to me and I guess now I know why.
-
Rowan Atkinson defended the right of comedians to poke fun at other people’s religion last night as he joined the campaign against Government plans to create a new offence of incitement to religious hatred.
The star of the BBC’s Blackadder television series lined up with leading barristers, writers and politicians to oppose the proposed law.
-
Mauritanian court issues first death sentence against Mohamed Cheikh Ould Mohamed for writing something blasphemous against prophet.
-
Privacy
-
Australian telecommunications companies and internet service providers were given until January 9th, 2015 to offer an estimate of what it will cost them to comply with data retention laws, and some appear to have been told of that deadline on Christmas Eve.
-
The National Security Agency today released reports on intelligence collection that may have violated the law or U.S. policy over more than a decade, including unauthorized surveillance of Americans’ overseas communications.
The NSA, responding to a Freedom of Information Act lawsuit from the American Civil Liberties Union, released a series of required quarterly and annual reports to the President’s Intelligence Oversight Board that cover the period from the fourth quarter of 2001 to the second quarter of 2013.
-
-
-
-
-
-
-
-
-
-
-
Hundreds of pages of reports previously classified top-secret were released by the National Security Agency on Christmas Eve. They reveal dozens of instances of the NSA unlawfully spying on United States citizens over the last decade.
-
A US District Court in California has ruled that a suit that targets Facebook’s data-harvesting practices can go forward. The company had attempted to have the whole thing tossed out, but only succeeded in having two relatively minor allegations dismissed.
There are three plaintiffs to the suit, all of whom allege that various state and federal statutes were violated by Facebook’s practice of scanning private messages in order to target ads more precisely. They also are upset that the mention of any company in these messages ends up counting as a “like.” Their suit [PDF] alleges that Facebook’s messaging service is “designed to allow users to communicate privately with other users,” and the scanning therefore violates the federal Wiretap Act as well as California’s Invasion of Privacy Act.
Facebook, for its part, wants to see the whole thing thrown out. It claims that it must handle the content of the messages in order to ensure delivery, and therefore it is not possible for it to unlawfully intercept them. Failing that, it suggested that the scans were part of ordinary business practice, and therefore exempt from the law. And, in any case, it stopped the practice back in 2012. For all those reasons, its lawyers argued, the case should not proceed.
-
But Facebook’s size — it has five times as many users as Twitter — and mountains of user data mean that the site can do some really interesting things for a lot of people.
-
Perhaps the reason we are not horrified by the surveillance society is because our parents normalised that behaviour by teaching us about Santa.
-
My interview on RT about the recent disclosure to Wikileaks about how undeclared CIA officers can travel safely into the EU. The big question is — why would they? Especially when we know from the Edward Snowden disclosures how much the European intelligence agencies collude with their counterparts in the USA…
-
Security vulnerabilities in the SS7 phone-call routing protocol that allow mobile call and text message tracking will be revealed this weekend.
-
-
The National Security Agency, responding to a Freedom of Information Act lawsuit, has released heavily redacted reports detailing its employees’ violations of individual Americans’ privacy in the broad surveillance net cast after the Sept. 11, 2001, terror attacks.
The agency was required by executive order to file the reports with the President’s Intelligence Oversight Board. But the quarterly and annual reports covering NSA activities from 2001 to 2013 were publicly released Wednesday only after the American Civil Liberties Union filed suit.
-
-
More than a dozen Romanian non-governmental organizations are protesting new cybersecurity legislation passed by the parliament last week that would force businesses to provide the country’s national intelligence agencies with access to their data without a court warrant.
-
Civil Rights
-
Police are being accused of trying to muzzle protest movements as figures obtained by the Guardian reveal the widespread use of bail to ban hundreds of innocent people from attending lawful demonstrations.
The data shows that around 85% of those barred from protesting when bailed have not been subsequently charged with any crime. Civil liberties and protest groups accused police of dealing out their own justice and called for a change in the law.
The figures show that a least 732 people have been banned by police forces in England and Wales since 2008 but then never charged. They come as the government confirms it is considering overhauling the police bail rules.
-
It’s no secret that former Vice President Dick Cheney has never been one of my favorites. And I will admit that when I saw him rise again on the Sunday morning shows and other television outlets around this torture report a few weeks back, my first reaction was “Why are they talking to him? Shouldn’t he be on trial for violating international law?” So, of course he should have been there. We live in a democracy! And, as he sits square in the middle of this whole controversy I had to admit I was curious as to his reaction.
There he was in all his glory, in all his arrogance, defending torture, or rather enhanced interrogation techniques, such as waterboarding and rectal feeding — which he said he believed was done for medical reasons. Really? He defended it all. I couldn’t help but think that maybe it’s time Vice President Cheney move from defending his actions on Fox News and Meet the Press, and be asked to defend it in a court of law.
Let’s face it, turning this kind of microscope on our own actions brings with it a lot of controversy, calls that we are endangering or damaging the CIA, or opening a can of worms that is best left closed. The dilemmas of a free society are many, and this is one of them. And the dilemmas of a free society are messy. But we should never walk away from them because of that.
-
Internet/Net Neutrality
-
The media has been abuzz with stories recently about how the Marriott hotel has blocked Wi-Fi access in a desperate attempt to get its customers to pay the hotel for Internet access. Yes, the Marriott – a billion dollar corporation – has been attempting to gouge its customers by blocking private Wi-Fi connections, and now the company wants the FCC to give them its blessing. And to make the story even weirder,
-
Bharti Airtel Ltd, India’s largest telecommunications carrier by subscribers, will soon start charging users extra money for using services such as Skype as Indian operators look to boost their data network and revenues.
-
Intellectual Monopolies
-
Copyrights
-
Former Pirate Bay operator Fredrik Neij is currently jailed in Sweden after being captured in Thailand last month. However, according to leaked emails, the MPAA believes that the Swede could also face hacking related charges – and it doesn’t stop there.
-
isoHunt, the group now best known for launching The Old Pirate Bay, has shared an update a week after debuting The Open Bay. The Pirate Bay, the most popular file sharing website on the planet, still isn’t back following police raids on its data center in Sweden, but its “cause” is very much alive.
The Open Bay, which lets anyone with “minimal knowledge of how the Internet and websites work” deploy their own version of The Pirate Bay online, is becoming an open source engine of The Pirate Bay website, the group told VentureBeat in an email. “The fate of Open Bay is now in the hands of worldwide community.”
-
There can be few Internet-savvy people around who haven’t, on occasion, downloaded an MP3 or two. Among those people’s parents, find a person who has never listened to a copied CD or cassette-taped LP and i’ll show you the bar where Bigfoot buys the Loch Ness Monster a beer on Friday nights.
Permalink
 Send this to a friend
Send this to a friend
12.25.14
Posted in News Roundup at 7:36 pm by Dr. Roy Schestowitz

Contents
-
He sees the end of the old ways and the arrival of newer software with less baggage on ARM and the cloud giving us all a fresh start. GNU/Linux gives a fresh start too. Yes, refreshing. Why can’t the trolls be as forthcoming?
-
For Linux, 2014 could easily be labeled the year enterprise really and truly embraced Linux. It could just as easily be labeled the year that nearly forgot Linux on the desktop. If you weren’t Docker, containers, OpenStack, or big data ─ chances are the spotlight didn’t brighten your day much. If, however, you (or your product) fell into one of those categories, that spotlight shined so brightly, it was almost blinding.
Let’s glance back into our own wayback machine and see where Linux succeeded and where it did not. The conclusions should be fairly simple to draw and are incredibly significant to the state of Linux as a whole.
-
Forget the fancy graphics of Valve’s latest offering – the only computer game a Linux user needs this year is a good quiz on all things Linux-y. Here are eight rounds of fiendish questions on everything from the Kernel to hardware to see if you know your Tux from your Beastie.
-
There was great news and there was awful news in the world of Linux and open-source software during 2014.
-
Desktop
-
Today’s float on the parade of the PC-is-dead prognostications comes from The Register, which says, “At the very moment that Linux desktops seem to be reaching new levels of sophistication, polish and ‘just works’ ease-of-use, the entire future of the desktop computer (by which I also mean laptop) feels in doubt.”
The only thing that’s in doubt is whether that sentence is anywhere near remotely accurate. But let’s put that aside for a moment and assume we can see the future of how we deal with our digital lives.
-
I use Windows 8.1 and Linux Mint 17.1 a lot nowadays, to do things like write, surf the web, check twitter and other web-based things.
Sometimes I boot into Windows, sometimes Mint, but who cares which? I am just going to Chrome anyway. It’s all the same thing.
-
Struggling UNIX server makers are strengthening their Linux strategy in line with the open-source application environment. The move is aimed at maintaining remaining customers, since users are increasingly abandoning UNIX servers. However, it is receiving a lukewarm response from the market.
According to industry sources on Dec. 22, server vendors such as IBM and HP are concentrating on the development of products so that the Linux operating system and related applications can be used as UNIX servers.
-
Kernel Space
-
A new development cycle has been started for the Linux kernel, 3.19, but it looks like the 3.20 branch is about to receive a very interesting patch that should really shake things up if it’s going to get accepted, that is.
-
Life’s choices often amount to one of two options: Linux or Windows? Android or iOS? Kgraft or Kpatch?
That last pair consists of the two major contenders for the technology Linux could use for live kernel patches. Now a winner is in, and it amounts to all of the above.
According to a post on the official Linux kernel developer’s mailing list, a kernel patching system that works with both Kgraft and Kpatch and uses “core functionality abstracted out of [those] already existing implementations” has been proposed as an addition to the Linux 3.20 kernel.
-
One of the first tasks of this quite interesting challenge is to compile and boot your own kernel
-
kPatch and kGraph may soon enable live kernel updates on all Linux distributions, making it possible to apply security and other patches on the open source operating system without rebooting.
-
OPNFV, the open source software-defined networking and network-functions virtualization project, said development of both code and community will be its focus for 2015.
-
Linux has long been known as an operating system that would run well even on older hardware. But has Linux become bloated in recent releases and how does it compare to Windows 8 in terms of system requirements?
-
Applications
-
This cam is a solid thumbs-up in terms of graphics viewing for console environments, and unless you have something specific that you need from another converter tool, it might usurp others you already know.
-
-
-
Instructionals/Technical
-
Games
-
Valve has released a new Steam Beta client and the developers have made a number of small improvements, although there is nothing out of the ordinary. Nonetheless, if you need to upgrade, then now would be a good time.
-
BlazeRush had confirmed they were going to do a Linux version, and with no announcement it has landed. BlazeRush is a dynamic arcade racing survival game with no health, no levelling and no brakes!
-
Desktop Environments/WMs
-
K Desktop Environment/KDE SC/Qt
-
We also released a new version of KDE Frameworks 5.5.0. KDE Applications 14.12 are arriving in Vivid Vervet, with backports, as soon as we can. For now, we wish you a Happy New Year and recommend you to meet it with new Kubuntu on your PC.
-
-
-
Reviews
-
It’s been quite a while since I last looked at Linux Lite, the last version I reviewed being 1.0.6. Much has changed in Linux Lite since that release and now it’s reached version 2.2. If you aren’t familiar with it, you should know that Linux Lite is a distribution geared toward helping current Windows users transition to the Linux desktop.
-
PCLinuxOS/Mageia/Mandriva Family
-
PCLinuxOS has been updated to version 2014.12, and you can download it in a variety of flavors including the super-humongous 4.8 GB Full Monty version that comes with tons of additional software.
-
-
PCLinuxOS 2014.12 isos have been released for Full Monty, KDE, MATE and LXDE. Highlights include kernel 3.18.1, ffmpeg 2.5.1, mesa 10.4.0, SysVinit (no systemd) and all popular applications such as Firefox, Thunderbird, LibreOffice and VLC have been updated to their latest versions. Please note if you have been keeping up with your PCLinuxOS software updates then there is NO NEED to install fresh from a 2014.12 iso. These ISOS are final releases based on legacy technology. Future releases will default to grub2 and support uefi and gpt partition formats.
-
We planned initially to release Mageia 5 beta 2 around the 16th of December. We still have some work left to complete to release a proper beta 2 that would drive us through to the final release.
Releasing development ISOs is a good way to test all the functions of the installer with the largest possible scope of use cases and variety of hardware. We still have some issues left with EFI integration and some tricky bugs in the installer. So in order to allow some time to fix them and also to still enjoy the Christmas period with friends and family, it has been decided to delay beta 2 until the 6th of January 2015, the initial date of the RC, and then postpone the final release.
-
-
Today in Linux news the Mageia project announced another delay in version 5 Beta 2. The Linux Voice is running a Linux quiz for Christmas and Gary Newell offers up his list of the seven best alternative Linux distributions of the year. The Register says 2015 will be the year of Linux – on mobile. Three reviews need to be highlighted and, finally today, Matt Hartley says everyone should switch to Ubuntu MATE.
-
The ROSA company is happy to finally present ROSA Desktop Fresh R5, the number 5 in the “R” lineup of the free ROSA distros with the KDE desktop as a main graphical environment.
-
I had been thinking that a new PCLinuxOS release was due any time now, based on their quarterly release schedule. Sure enough, it has now arrived, just in time for Christmas – PCLinuxOS 2014.12.
-
Ballnux/SUSE
-
Red Hat Family
-
Red Hat Inc (RHT) is ending the year with a flourish, as the stock has hit a 52-week high of $70. This puts the market cap at nearly $13 billion. In the past year, RHT stock has gained about 23%.
-
Fedora
-
I think it is arguable the Fedora project has done just that, created a small “core” base that products (such as Workstation, Server and Cloud) can be built on. And I applaud Mr Miller for working successfully toward his vision. Still, I am disappointed the result appears to be a smaller, less interesting Fedora. It is a more, to borrow Mr Miller’s term, “boring” foundation distribution, rather than a powerful desktop or server distribution. It is not a solution that brings more functionality to the table, something that would approach Mint’s level of “just works”, Ubuntu’s task oriented work flow or openSUSE’s level of integration. As a core platform we can use as a base to install Docker containers and run services, Fedora 21 can be considered a success. As a workstation operating system I would use to develop code or a desktop distribution I would install for friends & family, I do not think Fedora is a good match for those roles.
-
Debian Family
-
Devuan, the Debian spin-off that will not include systemd has posted its first progress report.
The missive says things are going well, as the project now has a GitLab repository and has built the first devuan-baseconf package.
-
-
This is an update on the progress of the Devuan.org project, born out of the Debianfork.org declaration to defend our growing community from the systemd avalanche.
-
I was idly looking through the press releases and news stories when I came across this article which talks about the new Debian fork called Devuan.
Devuan is a complete fork of the Debian system minus systemd.
I know that there are lots of people who aren’t happy with the inclusion of systemd as part of the next release of Debian but to make such a radical decision to clone the entire thing and start your own project could be deemed overkill.
I can understand a single developer or a handful of developers taking a Debian or Ubuntu base and then creating a new distribution with a specific purpose in mind. I actually think smaller distributions are a good thing because they come up with and implement ideas that might not reach the light of day in one of the base distributions.
Many people are of the opinion however that it is better to pool resources and have just a few distributions where everybody works together to make those distributions as good as they can possibly be.
-
The Devuan fork of Debian is progressing as Debian GNU/Linux without systemd present on the system.
-
And not just Debian this time, since I have one or two here that elude me and are from the Arch corpus only. By and large the relevant theme here is a consistent lack of required hardware, although I’m throwing in an oddball application or two that I just can’t seem to get working, for more traditional reasons. Like extensive or esoteric setups. Or my own thick-headedness.
-
Derivatives
-
Canonical/Ubuntu
-
Canonical has announced that a number of NTP vulnerabilities have been corrected for Ubuntu 14.10, Ubuntu 14.04 LTS, Ubuntu 12.04 LTS, and Ubuntu 10.04 LTS operating systems.
-
Flavours and Variants
-
I am very happy with Linux Mint 17.1 Cinnamon. It looks great with very polished interface, hundreds of attractive wallpapers, easy customization options and awesome collection of themes. The distro offers really good performance and excellent battery life. If you are looking for a functional distro which offers attractive looks and impressive performance, I definitely feel you should try out Linux Mint 17.1 Cinnamon.
-
-
“Orange Pi,” a new hacker SBC and RPi clone, is available in two models using Allwinner’s dual-core A20 SoC, and a third model that’s based on the quad-core A31.
Just in time for our upcoming year-end hacker SBC roundup, Shenzhen Xunlong Software unveiled an Orange Pi board that shares a number of characteristics with the Raspberry Pi Model B+, and many more with the $50 Banana Pi RPi clone.
-
SinoVoip is prepping an “Banana Pi M2″ update built with a quad-core Allwinner A31 SoC, while LeMaker has begun shipping a competing A20-based “Banana Pro.”
It appears that the Banana Pi project has forked into two rival groups that are now pushing their own Banana Pi updates: SinoVoip’s “Banana Pi M2,” which is announced but not yet shipping, and LeMaker’s recently released “Banana Pro.”
-
Phones
-
Top Smartphone OS by Installed Base end of 2014 in millions and market share (and year 2013 number)
Android . . . . . . 1,600 million . . . . 75% (64%)
iOS . . . . . . . . . . 395 million . . . . 18% (19%)
Windows . . . . . . . 55 million . . . . . 3% ( 3%)
Blackberry . . . . . . 45 million . . . . . 2% ( 5%)
Symbian . . . . . . . .25 million . . . . . 1% ( 7%)
Other . . . . . . . . . . 20 million . . . . . 1% ( 2%)
TOTAL . . . . . . 2,200 million
-
Tizen
-
Android
-
-
Samsung’s Galaxy Alpha made headlines when it launched earlier this year because it was the first Samsung smartphone to feature some metal in its design. Now Samsung is taking things a step further with the Galaxy Alpha by throwing in some leather as well.
-
-
Open source was initially adopted for low cost and lack of vendor lock-in, but customers have found that it also results in better innovation and more flexibility. Now it is pervasive, and it is challenging proprietary incumbents across technology categories. It is not only mainstream, open source is truly leading innovation in areas like cloud, mobile, big data, the Internet of Things, and beyond.
As we embark on a new year, I cannot help but reflect on the speed with which technology is changing. Rapidly delivering technology is about much more than just the technology – it is about people and culture. More than ever, this is why executives are looking at key technology companies – including Red Hat – as their partner instead of as a vendor.
-
Torrent site ISOhunt has created a roll-your-own, open source, version of infamous file-sharing site The Pirate Bay.
IsoHunt’s motive for the release seems to be a belief that big targets like The Pirate Bay will inevitably be picked off by law enforcement agencies. Lots of sites, however, present a tougher target. Open-sourcing what it’s calling “OpenBay” means there’ll be more targets for law enforcers to consider.
“History of torrent sites such as Isohunt and The Pirate Bay gives us a lesson that would be a crime not to learn,” says the new OpenBay site. “The era of individual torrent sites is over.”
-
-
-
-
-
Wikipedia is one of the most frequently visited websites in the world. The vast online encyclopedia, editable by anyone, has become the go-to source for general information on any subject. However, the “crowdsourcing” used by Wikipedia opens their doors to spin and whitewashing–edits that may be less than factual in nature. To help journalists, citizens, and activists track these edits, TWG (The Working Group) partnered with Metro News and the Center for Investigative Reporting to build WikiWash.
-
In January 2014, Github removed the rug in its office’s waiting room in response to criticism of its slogan, “United Meritocracy of Github.” Since then, the criticism of the idea of meritocracy has spread in free software circles. “Meritocracy is a joke,” has become a slogan seen on T-shirts and constantly proclaimed, especially by feminists.
Such commentary is true — so far as it goes, but it ignores the potential benefits of meritocracy as an ethos.
Anyone who bothers to look can see that meritocracy is more of an ideal than a standard practice in free software. The idea that people should be valued for their contributions may seem to be a way to promote fairness, but the practice is frequently more complicated.
-
Luis Ibanez is a senior software developer at Google. In this short talk he explains what he means by “unmanagement” and “unleadership” and how they can change the course of a project.
-
So you’ve worked on an open-source project, and you want to place that experience on your resume in order to move your career forward. Fantastic! In theory, there’s no reason an employer should shun your experience, just because you did the project from home on your own time. But how can you actually leverage that project work to obtain a full-time job?
-
Events
-
Sumana writes, “Open Source Bridge is already a leader among tech conferences in diversity-friendliness — OSB featured a strong code of conduct, accessibility, well-labelled food for all needs, and cheap & free admissions before they became de rigeur, and in 2014 boasted a gender-balanced slate of speakers.”
-
SaaS/Big Data
-
If you ask many enterprises considering doing an OpenStack deployment why they aren’t pulling the trigger, lots of them will cite security concerns as the primary obstruction. As I covered recently, IDG Enterprise came out with results from a new survey it did involving 1,672 IT decision-makers who report that they are very focused on cloud computing, including open cloud platforms such as OpenStack. The survey clearly showed that security and protection from disaster were among IT managers’ chief concerns in implementing cloud deployments.
-
Now that many enterprises are actually moving forward with OpenStack deployments, they are also wrestling with the complexities of putting applications and appropriate services on their cloud platforms. The last days of 2014 have brought news of some interesting choices becoming available for OpenStack deployments.
-
Tesora and Mirantis have partnered to certify the interoperability of their respective OpenStack open source cloud computing distributions and tools.
-
BSD
-
In this issue, you’ll get a summary of all the FreeBSD development work we’ve supported; highlights of all the conferences that we sponsored and attended; plans for the FreeBSD Journal in 2015; another great testimonial from a commercial user; and our Q1-Q3 financial reports. I’d be remiss if I didn’t mention my favorite part of our semi-annual newsletter, the insightful and always inspirational letter from our president and founder, Justin Gibbs.
-
FSF/FSFE/GNU/SFLC
-
This is the announcement of a new release of GNU gettext.
-
Openness/Sharing
-
In 2011 I — Ben Goertzel – interviewed physicist and futurist Giulio Prisco on his notion of Technological Transcendence. Since that time Giulio has been very active in developing these ideas further – and quite recently he has taken the initiative to start a “Turing Church” with an open-source spirit. So it seemed time to have another conversation with Giulio on his Turing Church concept and plans, and what it may mean for the future of humanity, transhumanism and spirituality.
-
If you are like me, you can’t help but see dollar signs every time you run your 3D printer. “How much filament is this using?” “What if the printer screws up just as the project is nearing completion?” Those are thoughts that run through my head as I watch the spool of filament slowly unravel and my finances follow right behind.
-
Sifteo, a system of intelligent gaming cubes launched with significant fanfare in 2011, has gone open-source.
-
As of December 19, the European Space Agency (ESA) is now sharing all of its images and videos from the Mars Express mission under CC BY-SA. ESA is using the intergovernmental organization (IGO) port of CC BY-SA 3.0. ESA is one of several intergovernmental organizations to use the IGO port since we introduced it last year.
-
Open Data
-
It was another year full of encouraging news on the open data front in states and municipalities across the country. New open data policies were approved in municipalities of all sizes from coast to coast, existing open data programs matured and sparked new innovations, and there were numerous other open government wins as a result of advocacy efforts.
-
Programming
-
Google has launched an open source Cloud Dataflow SDK for Java, with the intention of making it easier for developers to integrate with Google’s managed service. Here are the details.
-
Science
-
women cisco networks girl tablet server © wavebreakmedia ShutterstockWomen are far less well-represented than men in IT recruitment, with more than half of IT employers saying one in twenty, or five percent, of IT job applicants are women, a new study has found.
-
Security
-
The CSO of VeriSign discusses his concerns about domain collisions and the risks they entail.
-
More than 12 million devices running an embedded webserver called RomPager are vulnerable to a simple attack that could give a hacker man-in-the-middle position on traffic going to and from home routers from just about every leading manufacturer.
-
Apple Inc has pushed out its first-ever automated security update to Macintosh computers to help defend against newly identified bugs that security researchers have warned could enable hackers to gain remote control of machines.
The company pushed out the software on Monday to fix critical security vulnerabilities in a component of its OS X operating system called the network time protocol, or NTP, according to Apple spokesman Bill Evans.NTP is used for synchronizing clocks on computer systems.
-
Attackers can infect MacBook computers with highly persistent boot rootkits by connecting malicious devices to them over the Thunderbolt interface.
The attack, dubbed Thunderstrike, installs malicious code in a MacBook’s boot ROM (read-only memory), which is stored in a chip on the motherboard. It was devised by a security researcher named Trammell Hudson based on a two-year old vulnerability and will be demonstrated next week at the 31st Chaos Communication Congress in Hamburg.
-
The problem was discovered by the Google Security Team which seems to be responsible recently for more than its fair share of vulnerabilities detected. Some of the vulnerabilities are in older versions of the NTP code and have been fixed. So as long as you have been keeping up-to-date there is nothing to worry about.
-
Now public via the ICS-CERT after the discoveries were made by the Google Security Team are multiple vulnerabilities with the widely-used NTP. These vulnerabilities could lead to arbitrary code execution with the same privileges as the NTP daemon. These vulnerabilities can be exploited remotely and the ICS-CERT characterizes them as requiring low skills to exploit.
-
Everyone seems to be eager to pin the blame for the Sony hack on North Korea. However, I think it’s unlikely. Here’s why:1. The broken English looks deliberately bad and doesn’t exhibit any of the classic comprehension mistakes you actually expect to see in “Konglish”. i.e it reads to me like an English speaker pretending to be bad at writing English.
-
The hackers who took down Sony Pictures’ computer systems yesterday say that they are working for “equality” and suggest that their attack was assisted or carried out by Sony employees. In an email responding to inquiries from The Verge, a person identifying as one of the hackers writes, “We Want equality [sic]. Sony doesn’t. It’s an upward battle.” The hackers’ goals remain unclear, but they used the attack yesterday to specifically call out Sony Entertainment CEO Michael Lynton, referring to him as a “criminal” in a tweet.
-
Defence/Police/Secrecy/Aggression
-
The FBI and New York police held a news conference to discuss the latest on an airline security breach involving a Delta employee facing federal charges.
Police say more than 150 guns were illegally smuggled from Atlanta to New York on more than a dozen trips. Channel 2′s Rachel Stockman broke the news Monday that a former Delta employee at Hartsfield-Jackson is accused of using his clearance to help smuggle the guns.
-
Wikileaks has released two classified documents instructing CIA operatives how best to circumvent global security systems in international airports, including those of the EU, while on undercover missions.
The first of the documents, dated September 2011, advises undercover operatives how to act during a secondary airport screening. Secondary screenings pose a risk to an agent’s cover by focusing “significant scrutiny” on an operative via thorough searches and detailed questioning.
-
Transparency Reporting
-
An open-source component used to display PDF files on WikiLeaks.org and other websites contains vulnerabilities that could be exploited to launch cross-site scripting (XSS) and content spoofing attacks against visitors.
The vulnerable component is called FlexPaper and is developed by a company called Devaldi, based in New Zealand. The company confirmed the issues, which were first reported Thursday on the WikiLeaks supporters forum, and released FlexPaper 2.3.0 to address them.
-
Finance
-
The cost of US war-making in the 13 years since the September 11 terrorist attacks reached a whopping $1.6 trillion in 2014, according to a recent report by the Congressional Research Service (CRS).
-
Sheeta Leung Hui-kwan, a spokeswoman for G4S Hong Kong, said an internal investigation was underway, but initial findings suggest a broken door sparked the incident.
Armed police were quick to arrive at the scene, and closed off two lanes of the road.
According to reports, witnesses to the accident were seen running onto Gloucester Road and grabbing HK$500 notes. One person allegedly filled their arms with wrapped bundles of cash, a witness told the SCMP.
-
Illustrating that nothing rattles corporate media like progressive populism, the Washington Post’s David Ignatius (12/24/14) is the latest establishment journalist to launch a salvo against Sen. Elizabeth Warren (D-Mass.) and “her jihad against Wall Street.”
Echoing the New York Times’ Andrew Ross Sorkin (FAIR Blog, 11/26/14), Ignatius goes after Warren for opposing the nomination of Antonio Weiss to be the Treasury Department’s undersecretary for domestic finance. He makes the same extraneous points Sorkin did about Weiss (He’s a Democrat! He publishes the Paris Review!) and similarly misrepresents Warren’s primary reason for opposing him, which is, as she wrote in the Huffington Post (11/19/14), that “Weiss has spent most of his career working on international transactions,” so “neither his background nor his professional experience makes him qualified to oversee consumer protection and domestic regulatory functions at the Treasury.”
Ignatius also criticizes Warren for including on her “enemies list” Timothy Geithner and Lawrence Summers, despite the fact that they “had never worked as private bankers.” Summers may not have been a private banker, but he was a managing director of the hedge fund D.E. Shaw, which paid him $5.2 million; he also got $2.7 million in “speaking fees” from financial firms, including major banks like Citigroup and JP Morgan Chase (Salon, 4/4/09). But he wasn’t a private banker!
-
Censorship
-
Amy Adams says she is still “really confused” about having her live interview on The Today Show dramatically pulled minutes before it was due to take place Monday morning.
Adams told USA TODAY on Tuesday night that she was “surprised” that the segment was unceremoniously canceled after she expressed misgivings over discussing aspects of the Sony hacking scandal on live television.
-
Privacy
-
Horace Edwards, who identifies himself as a retired naval officer and the former secretary of the Kansas Department of Transportation, has filed a lawsuit in Kansas federal court that seeks a constructive trust over monies derived from the distribution of Citizenfour. Edwards, who says he has “Q” security clearance and was the chief executive of the ARCO Pipeline Company, seeks to hold Snowden, director Laura Poitras, The Weinstein Co., Participant Media and others responsible for “obligations owed to the American people” and “misuse purloined information disclosed to foreign enemies.”
It’s an unusual lawsuit, one that the plaintiff likens to “a derivative action on behalf of the American Public,” and is primarily based upon Snowden’s agreement with the United States to keep confidentiality.
-
Free software isn’t free. Someone’s got to shell out for the expensive development, maintenance, bug fixes and updates for programs that so many of us who live online have come to see as almost natural resources. And increasingly, those taken-for-granted tools have become vital for the privacy and security of millions of people.
-
In the world of online anonymity, the Tor network is a silent king. Millions of users depend on Tor to keep their tracks untraceable online, and not just individual users. Banks and other institutions leverage the Tor network as a security layer. In the U.S. last year, when NSA snooping was in the news, usage of the Tor network doubled within a matter of days.
-
The Western media has attempted to portray Mark Zuckerberg’s ambitious plan to get every human being online as altruistic at first, but later revealed as simply what could be called “profitable empathy.” In reality however, the truth is much more sinister, with Facebook already revealed to be much more than a mere corporation run by Zuckerberg and his “ideas”
-
Civil Rights
-
The New York Times has a blistering editorial calling on President Obama to prosecute those who committed torture…
-
Torture, including rape and other forms of sexual violence, suffered by women and girls from Iraq’s Yezidi minority who were abducted by the armed group calling itself the Islamic State (IS), highlights the savagery of IS rule, said Amnesty International in a new briefing today.
-
A body camera system is nothing without solid policies backing them up. Anyone can instruct an officer to wear a camera, but only a department solidly behind the program will hold them accountable if they fail to do so. According to public records obtained by Ars Technica, the Oakland PD is making a genuine effort to ensure devices are on and recording.
-
A review of the trial later revealed that police coerced and coached key witnesses
-
But still, mainstream politicians still don’t think that issues like civil liberties, mass surveillance, digital rights and freedom of speech will move people’s votes at a general election. That is why so many MPs simply ignored their constituents when it came to crackdowns like the DRIP vote. They count that once election will be run in exactly the same way as previous decades.
-
The DNI, USDI, and CIA went over the cliff when they confused technology with thinking, secrets with intelligence, and spending money with progress. Nothing could be further from the truth. In the world of intelligence as decision-support, Big Data is noise. The best intelligence — precision intelligence — is from a human source with direct access, and that is not something we can do today despite millions of such sources being available. We have no penetrations of ISIS, the clandestine service refuses to deal with “overt” human experts, while the diplomats and attaches have no money for commercial sourcing and modest performance fees. In consequence we have no human assets of any import across the Middle East, Central Asia, Africa, or the Americas at the same time that our analysts are children lacking in real-world experience — who in addition rarely speak the target language and have no grasp of the culture or history of the target population.
-
As officials continue to investigate Saturday’s tragic killing of two NYPD officers, Wenjian Liu and Rafael Ramos, details have surfaced about the suspect, 28 year old Ismaaiyl Brinsley, who allegedly shot a woman in Baltimore before traveling to New York. Anti-police posts he appears to have published on social media sites prior to the killings have lead many to connect his crime to protests that occurred in previous weeks, and some commenters have cast blame on officials including New York Mayor Bill de Blasio, Attorney General Eric Holder, and President Obama, all of whom have condemned the violence.
-
Internet/Net Neutrality
-
If you’ve been watching the issue of net neutrality this year, you know it’s been quite a ride. The year started with the D.C. Circuit overturning the majority of the FCC’s 2010 Open Internet rules, explaining that the FCC can’t impose “common carrier”-type rules on ISPs without actually classifying them as “common carriers.” Having chosen to classify them instead as “information services” back in 2004, the ruling meant the FCC had to go back to the drawing board. That led to a new proposal in May by FCC Chairman Tom Wheeler that many believed would actively undermine the open Internet in the name of protecting it.
-
Offices everywhere are emptying as people head home for a few days of light dining and constructive political conversations with relatives. But is the Internet as much of a ghost town as your workplace over the holiday season? Nope. Internet usage is likely to be higher than usual for the rest of the week, according to Sandvine, a firm that tracks Internet traffic. The only exception: a few hours on Christmas Eve, when people have no choice but to put away devices and talk to one another.
-
Intellectual Monopolies
-
Copyrights
-
Last December the MPAA announced one of its biggest victories to date. The Hollywood group won its case against file-hosting site Hotfile, who agreed to a $80 million settlement. However, this figure mostly served to impress and scare the public, as we can now reveal that Hotfile agreed to pay ‘only’ $4 million.
-
A high-profile police raid carried out on Kim Dotcom’s New Zealand mansion has been declared legal by the country’s Supreme Court. The Court acknowledged that the search warrants used against Dotcom were ‘deficient’ in detail, but this did not result in a miscarriage of justice.
-
A group of 12-year-old girls had the police called on them after they decided to bring their iPhones and iPads to a showing of The Hunger Games at a local cinema. The police officers who rushed to the scene were unable to find any recorded footage, but by then the children were too distressed to watch the rest of the film.
Permalink
 Send this to a friend
Send this to a friend
12.23.14
Posted in News Roundup at 4:37 pm by Dr. Roy Schestowitz

Contents
-
It’s nearly impossible to sum up an entire year of developments in something as large and nebulous as the world of desktop Linux, especially in a year like this one which has seen some the best releases that projects like Mint, Fedora and openSUSE have put out to date.
At the same time the distro that’s closest to being a household name, Ubuntu, has been nearly silent since 14.04 arrived in April.
To paraphrase author Charles Dickens, the past year of Linux releases has been both the best of times and the worst of times.
At the very moment that Linux desktops seem to be reaching new levels of sophistication, polish and “just works” ease-of-use, the entire future of the desktop computer (by which I also mean laptop) feels in doubt.
-
HP has recently been facing some serious difficulties and has opted to betting all its resources on the new PC called ‘The Machine’. Probably the most intriguing thing about the machine is that it will rewrite basic computing on a very fundamental level. While the topic has been covered extensively, I realized we haven’t actually touched it here and thought it was about time.
-
It seems that even the somewhat “traditional” North Korean tech aesthetics is getting an update. Thanks to a former lecturer at Pyongyang, we are getting a glimpse of what the officially sanctioned operating system of North Korea, Red Star Linux, now looks like, almost half a decade since the OS was first leaked outside the secretive regime. Apparently, like the rest of the tech world, the Linux-based OS has moved away from a Windows 7, nay Window XP even, look towards a more stylish OS X.
-
If imitation is the sincerest form of flattery, then Microsoft has nothing but good things to say about Linux. Windows 10 is abandoning many of the more jarring changes of Windows 8—while simultaneously copying features from Linux.
Windows 10 includes virtual desktops, a centralized notification center, and a vision of apps that can run in windows when you’re using a proper PC, or full-screen when you’re using a mobile device. It’s a smattering of ideas from 15-year-old Linux desktops, GNOME Shell, and Ubuntu’s vision of convergence.
-
Regulators in China recently seeked anti-trust probes against Western companies such as Microsoft and Qualcomm Inc.
-
Two Thousand and Fourteen was an exciting, tumultuous and rather funky year for Linux.
Great consumer news, forks, death threats, hardware delays and… something truly unthinkable just a few years ago. Truth be told I’m still trying to wrap my head around, what feels like, the zaniest year of Linux shenanigans I have ever seen.
Here are the 5 stories that, I feel, best sum up what happened with Linux (and the related Open Source world) in 2014.
-
There’s a reason for that lock-in. For decades, M$ was allowed to use strong anti-competitive practices all over the world. It takes a lot of time money and effort to undo that. e.g. Munich took 10 years to throw open the doors to the jail in which it found itself after decades of using M$’s products while folks like Largo, FL, who never took the bait are laughing all the way to the bank, year after year. Smaller organizations like the ones for which I worked could free themselves in weeks but it requires good knowledge of GNU/Linux which is often lacking. That too can be overcome. When the dust settles, folks who switch are better off and have lower costs of IT forever. It pays to switch.
-
Like most governments, China’s has long been concerned about the security vulnerabilities that may come with using software developed in other countries. The biggest problem: PC operating systems in government buildings are almost universally run on Windows. For years, China has been trying to create a domestic alternative. Yesterday, the latest alpha build of its decade-in-the-making Kylin operating system went up for download.
According to Techweb, this latest version of Ubuntu Kylin – the version of Kylin that’s being designed for use by the public – still contains serious bugs, and important parts of the OS have not been translated into Chinese.
In fact, whether Kylin is even a Chinese operating system at all is debatable, although the Chinese media continues to describe the project as “home-grown.”
-
Red Star OS is a Linux distribution developed in North Korea. Not only is it North Korea’s official Linux distribution, it’s their country’s official operating system period.
Microsoft’s Windows operating system is written and developed in the USA, so it’s no surprise North Korea doesn’t really trust it given the tense relations between the two countries. Until 2002, when Red Star OS began to be developed in the DPRK, the few available computers in North Korea generally ran Windows. (Interestingly enough, the North Korean hackers which seem to be behind the hack of Sony Pictures appear to have been using Windows PCs instead.)
-
Desktop
-
When Razvan Rughinis began teaching the introductory operating systems course at University Politehnica of Bucharest in Romania 10 years ago, he was challenged to get students interested in Linux and keep them interested for the entire three-month course.
Many first-year computer science students have no experience with Linux, and they have no interest in learning it, said Rughinis a professor in the Computer Science and Engineering Department. And those students who do know Linux are regarded as unusual and treated as social outcasts, he said.
“They wouldn’t pay attention to the first experience to see what Linux has to offer; not just the desktop, but how the services work and the depth of the system,” he said. “It’s a steep learning curve for students coming from high school. Their first encounter was too difficult.”
-
Librem 15 aims to be the only laptop coming with completely free software and its makers are looking to get some funding through a crowdfunding campaign.
You might think that if a laptop ships with any Linux distribution, then it would stand to reason that it would be loaded with free and open source software, but the truth is that it’s not that simple or even intuitive. For example, it’s true that the Linux kernel is an open source project and that it’s freely distributable, but there are some people in the community that say it’s not enough.
-
Did I tell him it was Linux? Did I give him the party line on freedom-as-in-beer-and-code? No. I didn’t tell him anything except I was going to fix his computer.
When the install was done, I imported his IE bookmarks into Firefox and loaded his music and pictures into the appropriate directories. I did not set him up with multiple desktops, nor did I blingify his desktop. He wanted to play his online games with his friends, he wanted to check his bank account from time to time and he wanted to access his Yahoo email account. That’s all. Oh…and he wanted to play World of Goo. It’s his new and favorite obsession.
It took me all of one and a half hours to get him fixed and out the door.
In the years I’ve been doing this, it’s only been recently that I’ve learned an extremely important lesson. Not everyone needs to be saved from one entity and changed to another. Not everyone wants or needs to know the important philosophical truths about free open source software. Sometimes, people just want their computers to do what they tell them to do and in the shortest and most simple way possible. The end result was a happy friend and a neighborhood computer I will not have to fix for a long time.
-
Chromebooks are killing iPads and Wintel PCs in USAian education. Even PhotoShop ships for them. Every major OEM of PCs is shipping ChromeOS which is Chrome browser embedded on GNU/Linux. There are moves to integrate the rampant Android/Linux, too, with ChromeOS. We’ve won, beyond our wildest dreams and rather quickly too. It was only 7 years ago that Android was a gleam in Google’s eyes but they sold a billion copies last year.
-
When I first started using Linux, back in the mid-late nineties, a typical Linux installation was roughly four to five CDs and wound up installing applications geared toward scientists, programmers, HAM radio operators, and more. The kernel was built for a small sub-section of hardware it actually had support for (which included a lot of hardware most people didn’t have). The typical resources needed to run Linux were quite small. The first machine I ran Linux on was a Pentium II 75 Mhz processor with 56 MB of RAM and an unsupported WinModem (which was eventually swapped out for a US Robotics 36.6 external modem).
-
Server
-
For all for all of the hype containers have received, they are still dependent on the underlying operating system to run. Containers are awesome, but they’re still new, and the technology is still growing. In this talk, Brian Proffitt talks about how changes in the IT sector still require a trusted operating system sitting underneath containers, hypervisors, and all virtualization solutions.
-
Kernel Space
-
This was released by the Linux Foundation yesterday and I thought I’d share.
-
The Ceph file-system in Linux 3.19 will support inline data to offer performance improvements for some operations.
Ceph, the distributed file-system that prides itself as having no single point of failure and being very scalable, is adding in new functionality for Linux 3.19. First up, CephFS for Linux 3.19 adds support for inline data. Inline data makes the file-system quicker for accessing small files and is a feature already supported by Btrfs, EXT4, and other file-systems. Inline data support for Ceph has been a long time coming and is outlined further on this Ceph Wiki page.
-
Nearly one month ago back during the Linux 3.18 release candidates there was a worrisome regression uncovered by kernel developers, but now with the Linux 3.19 merge window nearly over, that issue still has yet to be firmly addressed.
-
-
Graphics Stack
-
Beyond the VC4 Gallium3D work yesterday landing in Mesa that led to this Raspberry Pi graphics driver potentially running much faster, DMA-BUF support was also added.
-
The NIR Mesa IR was envisioned and originally developed by Connor Abbott, who was interning at Intel this summer after being a fresh graduate of high school and having already contributed to Lima and other Linux graphics projects.
-
Before going on holiday break, Aaron Plattner at NVIDIA released version 0.9 of the VDPAU library (libvdpau) and of the VDPAU information utility (vdpauinfo).
-
The Freedreno Gallium3D driver’s support for the Adreno A4xx hardware is taking shape and beginning to work for GL rendering on this latest-generation Qualcomm graphics hardware.
-
Given the recent X.Org Server security vulnerabilities that were aplenty and many dated back 10 to 20 years or more, Jeremy Sharp is trying to get developers into finally materializing server-side XCB.
-
The Intel X.Org driver (xf86-video-intel 3.0) driver has been in pre-release form since September 2013 and now after having gone through many development revisions, xf86-video-intel 3.0 might be on final approach.
-
Benchmarks
-
Applications
-
Well, after a day or two of completely scrambling my scheduled posts — and even revisiting an application that I had already mentioned a year ago  — I have some catching up to do.
— I have some catching up to do.
Please accept this as a double post, and hopefully make up for a little lost ground. Here’s lddot and dothost, respectively, both from Jakub Wilk and both in AUR (but not in Debian).
-
-
-
Instructionals/Technical
-
Wine or Emulation
-
Games
-
The game was funded on Kickstarter two years ago, and was released for PlayStation 3 and 4 in May. This week it was released for PCs, but due to Bluetooth driver issues one of the four games in the compilation is missing in the Windows version.
-
Desktop Environments/WMs
-
K Desktop Environment/KDE SC/Qt
-
Since 2007 there has been KO GmbH as a support and software service company built around KOffice/Calligra in their belief that the software was “getting ready for the big time”, but seven years later the situation is not so good and KO GmbH is no longer handling Krita.
-
I haven’t worked for FOSS projects yet, but what a great idea for a New Year’s resolution. I’ve worked as part of teams that generated open source tools and upstream patches for existing drivers/kernel, but nothing directly.
-
KDE e.V. has been successfully supporting the KDE community for over 17 years. For many of them we had the tremendous help of a business manager, several interns, an event manager and countless volunteers to be able to do this. In the coming years we want to be able to support the KDE community even better. In order to do this we need strong support from an Executive Director. The Board of Directors has decided to hire someone for this position in the coming months. We are looking for a passionate individual who understands our community and can drive our business interaction. Do you want to be a part of bringing great software to millions of users? Do you want to really make a difference for a Free Software non-profit? Then this is the job for you! If you would like to know more about the position please read the job ad.
-
For my job, I need to take care of the support of old Linux distributions for our products, therefore I experimented in building Qt 5.x for Red Hat Enterprise 5 (or CentOS 5 or other clones).
Whereas Red Hat Enterprise 6 works more or less out of the box, to build Qt (even without WebKit and Co.) on Red Hat Enterprise 5, more work is needed. Even the xcb library is not yet existent there.
-
I got a copy of the Application Development with Qt Creator, 2nd ed. for review, so I decided to post the review here – KDE is still the greatest Qt community in the world, and we have more than a few students and teachers in it which might benefit from a book like this one.
-
The Subsurface development team proudly announces release 4.3 of Subsurface, an open source divelog and dive planning program for Windows, Mac and Linux.
-
On 3rd December, I have released Bluedevil 2.0. It was a first stable release that supported Bluez 5 and it contained mainly crash fixes over 2.0-rc1. Unfortunately, there was also a big regression.
-
GNOME Desktop/GTK
-
Since this summer Christian Hergert has been hard at work on building “Builder”, a new integrated development environment designed for GNOME developers. The GNOME Builder isn’t expected to compete with Eclipse, Qt Creator, and the likes, but is focused solely around the GNOME development workflow and the needs of GNOME developers. Builder is focused on C, Vala, JavaScript, and Python language support. Builder also has plans for GObject Introspection integration, PerfKit integration, GDB support, Clang integration, etc. Hergert is so committed to builder that he had quit his day job at MongoDB to focus on Builder for one year.
-
-
Puppy Linux is a lightweight Linux distribution designed to run from removable devices such as DVDs and USB drives.
There are a number of Puppy Linux variants including Puppy Slacko, which utilises the Slackware repositories, and Puppy Tahr which utilises the Ubuntu repositories.
Other versions of Puppy Linux include Simplicity and MacPUP.
It is possible to use UNetbootin to create a bootable Puppy Linux USB drive but it isn’t the method that is recommended.
Puppy Linux works great on older laptops, netbooks and computers without hard drives. It isn’t designed to be installed on a hard drive but you can run it that way if you want to.
-
Well the holidays are pretty much upon us at last here in the Linux blogosphere, and there’s nowhere left to hide. The next two weeks or so promise little more than a blur of forced social occasions and too-large meals, punctuated only — for the luckier ones among us — by occasional respite down at the Broken Windows Lounge.
Perhaps that’s why Linux bloggers seized with such glee upon the good old-fashioned mystery that came up recently — delivered in the nick of time, as if on cue.
-
-
Reviews
-
Deepin, a Linux distribution that tries to provide users with a unique, stable, fast, safe, and user-friendly desktop experience based on the latest HTML5 technologies, has been upgraded to version 2014.2 RC and is ready for testing.
-
Screenshots
-
Slackware Family
-
For a long time I have been keeping copies of the full source directories for every KDE 4 release I have made for Slackware. That is amounting to a lot of megabytes, since I am also keeping the source tarballs, not just the scripts and patches. Traditionally, I have kept one KDE version publicly available for all recent Slackware releases, in my ‘ktown’ package repository at http://alien.slackbook.org/ktown/ . This repository is also available through rsync, not just http (using my primary mirror at rsync://taper.alienbase.nl/mirrors/alien-kde/).
-
Red Hat Family
-
Although differentiation is tough in Linux distributions today, CentOS 7 has carved out a niche as the free and open alter ego to Red Hat Enterprise Linux (RHEL). We found that CentOS, which is mandated to be binary-compatible with Red Hat 7, shares about 95% of the features of its commercial enterprise-class sibling.
There’s no IBM System z port, and special variants for cloud and virtualization are more limited than with Red Hat 7. But for many common and generic applications, it’s a drop-in replacement.
-
Linux vendor Red Hat is continuing to grow its business beyond just providing Linux for servers. Red Hat reported its third quarter fiscal 2015 earning on December 18, showing just how important the company’s broad product offering has become to its continued financial success.
-
-
-
-
Fedora
-
While F2FS is a promising open-source file-system looking to live up to its name as being the Flash-Friendly File-System, one major distribution not yet willing to enable it within its kernel is (surprisingly) Fedora.
I continue to be running Fedora 21 on a number of systems and continue to enjoy the release. Fedora 21 is easily my favorite and arguably best release since probably Fedora Core 3, or ever for this Red Hat sponsored Linux distribution. While Fedora is often referred to as being a distribution living on the “bleeding edge” of upstream Linux and often shipping with experimental / next-generation open-source components, surprisingly it’s still not shipping a kernel with F2FS support.
-
Debian Family
-
Derivatives
-
Canonical/Ubuntu
-
It seems that Samsung isn’t the only one experiencing delays in getting a new player in the mobile market out of the woodwork. Canonical, the commercial company behind the open source Linux-based Ubuntu OS has been quoted to have said that its much-hyped Ubuntu Phone won’t be announced until early 2015. And that’s just the announcement of the availability and not the availability itself, which can, of course, be delayed repeatedly, as Samsung’s dance with its own Tizen OS has proven.
-
-
-
Canonical has just promoted a new Ubuntu Touch RTM version of its operating system and it’s moving even closer to the final build that should be ready in time for the February 2015 release.
-
-
Flavours and Variants
-
When I first came to Linux, I gravitated to KDE and then later on, early GNOME. Back then, these desktop environments were designed mostly to provide a usable X environment from which to use Linux compatible applications. Today, however, our need for a desktop environment is more varied. Some individuals prefer to have a desktop experience that is rich, full of nice effects and looks great. Others still, prefer a desktop experience that provides a simple, hassle free interface.
My own desktop needs, reflecting on the ideas above, have also evolved. I went from wanting a fancy, slick GUI desktop over to leaning with a lighter weight desktop. XFCE started off as my go-to lightweight desktop preference, while keeping Gnome 3 around on another machine because it was fun to use.
After a lot of recent thought and reflection, I have decided to commit full time to a “no frills” desktop environment. My desktop of choice: MATE on Ubuntu.
-
-
Erle Robotics launched a ROS-enabled, open source “Erie-brain” autopilot that runs APM directly on Linux. The device also powers an “Erle-copter” drone.
Over the last year, Spanish firm Erle Robotics S.L. has been working with 3DRobotics to develop an open source BeaglePilot autopilot for drones that can run Linux on 3DR’s popular, Arduino-based APM (ArduPilot Mega) platform. The APM Linux port was developed by both companies, as well as several academic institutions. The BeagleBone-based “Erle-brain” autopilot is built into the $490-and-up Erle-copter quadcopter.
-
Phones
-
The tenth update to Jolla’s Sailfish mobile operating system is now available. This update is version 1.1.1.26 and is codenamed Vaarainjärvi.
-
Tizen
-
We have been waiting for the Samsung Z1 launch event, and it looks like its finally happening at a secret Samsung Z1 launch event in India. Its exciting to see that we have final specifications of the Z1 which runs Tizen 2.3, 4.0 inch 800 x 480 PLS TFT display, 768MB RAM, 1.2GHz Dual-core processor, 3MP primary camera with a LED flash, VGA Front Facing Camera, 4GB internal storage, microSD card slot, with a 1,500 mAh battery.
-
Android
-
Google is planning a big push into in-car infotainment systems with an upcoming version of Android, sources claim.
“Android M” – the version to come after the current Android 5.0 “Lollipop” – will be available in a formulation designed specifically to run cars’ built-in screens, Reuters reports, citing anonymous insiders with knowledge of the plan.
Google made its first advances toward the automotive world at its I/O developer conference earlier this year, when it unveiled its Android Auto software. The first Android Auto–compatible cars are expected to arrive early next year.
-
After rolling out the first fixes for Android Lollipop on Nexus phones and tablets, Google has tied up some loose ends with a separate update just for the 2012 Nexus 7.
-
The company is working on a new Android version that will power a car’s entertainment and navigation systems, connect it to the Internet, and integrate with the vehicle’s sensors, a Reuters report says.
Sometime in the not-too-distant future, cars from many automakers could feature a version of Google’s Android operating system built directly into the vehicles.
-
Monument Valley, The Room Two, Clumsy Ninja and much, much more in our pick of games released this year through the Google Play store.
-
Databricks, a company founded by the creators of the popular open-source Big Data processing engine Apache Spark, is a firm that you may not have heard much from in 2014, but you will throughout 2015. The company has healthy venture funding of $47 million, and Andreesen Horowitz is one of the investors, with Ben Horowitz on board.
-
Events
-
Open-Xchange CEO Rafael Laguna has hit out at the closed nature of services offered by Silicon Valley giants like Google and Facebook.
Speaking in Paris earlier this month, Laguna said many of Silicon Valley’s largest companies, and others like them, need to open up their proprietary systems to comply with laws around the world and uphold many of the citizen’s rights that people have fought for over the last several hundred years.
-
Such is the case with the Ponemon Institute’s survey of 1,400 technology professionals, which according to some outlets found big companies “cautious” and “slow” to embrace open source. Others, looking at the exact same data, found respondents “generally positive” to open source. (The survey was sponsored by Zimbra, which provide of open-source messaging and collaboration software.)
-
Web Browsers
-
Mozilla
-
Mozilla, the mission-based organization dedicated to promoting openness, innovation and opportunity on the Web, is excited to announce that KDDI will release the first Firefox OS smartphone in Japan, just in time for the holidays.
KDDI announced at a press conference in Tokyo today that the newest Firefox OS smartphone, Fx0, goes on sale in Japan on Dec. 25. Fx0 is the first high-spec Firefox OS smartphone with the latest Firefox OS update inside.
-
Announced at a KDDI press event in Tokyo today, the Fx0 is a striking 4.7-inch smartphone with a transparent shell and a home button decorated with the golden Firefox logo embracing the Earth. It runs the latest version of Mozilla’s web-centric mobile OS and was designed by noted Japanese designer Tokujin Yoshioka, whose previous collaboration with KDDI produced a phone worthy of making it into the Museum of Modern Art’s collection. With the Fx0, Yoshioka has worked around the familiar outlines of LG’s G3 design (LG is the silent partner producing the device) and adapted them to a smaller size while producing a delightful aesthetic in the process. Like a watch with a window showing its internal mechanism, this phone’s exposed electronics are a subtle reminder of its technical sophistication — plus, that Firefox home button is just plain cool.
-
SaaS/Big Data
-
Interested in keeping track of what’s happening in the open source cloud? Opensource.com is your source for what’s happening right now in OpenStack, the open source cloud infrastructure project.
-
Marking the clearest evidence yet that OpenStack player Mirantis is working more closely with VMware on open cloud initiatives, the companies have published a Mirantis OpenStack reference architecture for VMware vCenter Server and VMware NSX. Now available for download, Mirantis OpenStack allows customers to deploy and control workloads that run on VMware vSphere in their VMware vCenter Server clusters within Mirantis OpenStack.
-
Saar Gillai, SVP and general manager of NFV at HP, discusses the opportunities and the challenges of cloud deployment.
Hewlett-Packard is bullish on the future of the cloud and on network functions virtualization (NFV). Helping to lead HP’s NFV and cloud efforts is Senior Vice President Saar Gillai, who is also the general manager for NFV as well as the chief operating officer for HP Cloud.
-
Oracle/Java/LibreOffice
-
Most of us are not coders. I’m a coder but don’t do C… That is a barrier to giving back to FLOSS in the form of code but there are opportunities.
-
Funding
-
Wikipedia co-founder Jimmy Wales says he’ll “start a foundation” to process a large amount of money he has received from the United Arab Emirates’ regime.
Christmas came early for Wales, and Tim Berners-Lee, earlier this month when they shared a $1m cash award from the Gulf state. The “Sheikh Mohammed bin Rashid Al Maktoum Knowledge Award” is named after the veep of the UAE.
-
BSD
-
Those of us who work in the depths of high technology are not immune to the age-old adage of the shoemaker’s children having no shoes. We probably have the most technologically advanced homes of anyone we know, but we also tend to leave various items alone if they’re not causing problems. After all, that’s what we deal with at work. Who needs to saddle themselves with network upgrade projects at home when nothing’s broken?
-
FSF/FSFE/GNU/SFLC
-
Gnu Privacy Guard (GPG, the free/open version of PGP) relies on donations to pay developers to keep the project alive and viable; as one of its millions of users, I am grateful and indebted to the people who keep it alive and that’s why I’ve just donated to the project.
-
Project Releases
-
The UDisks 2.1.4 release for managing/manipulating storage devices adds the Intel Fast Flash Standby partition GPT type, supports building against the libsystemd library, adds a man page for umount.udisks2, and has numerous other fixes and improvements.
-
We’re starting to hear details about the LLVM 3.6 release plans.
-
Updated as part of XZ’s liblzma library for LZMA compression is multi-threaded compression support, speed optimizations, support for symbol versioning, and updated Windows MSVC build support.
-
Version 0.15.1 of LDC was released this past week, a D compiler written to use the LLVM compiler infrastructure.
-
Public Services/Government
-
Might also think about encrypting stuff. Maybe. You know… next year, perhaps?
-
The European Parliament is funding a security audit of the free and open source solutions used by the Parliament and the European Commission. Last Wednesday, the EP allocated EUR 1 million for the audit project, to be carried out by the EC Directorate General for Informatics (DIGIT). The project should also come up with best practices for code review and quality assessments of free software and open standards funded by the EU.
-
When a politican talks about security technology, they’re usually coming for your civil rights. Suspicionless mass surveillance, secret internet blocklists, arduous security theatre at airports: Safety and freedom are presented as trade-offs — and many politicians are all too willing to sacrifice more and more the latter for the short-term sugar high of feeling like they’re Doing Something to Keep The World Safe.
-
Licensing
-
The most-read articles this year on Opensource.com demonstrated a strong interest in the changing aspects of complicated issues. For example, the top two stories this year both relate to a complex series of cases involving a dispute between Versata and Aperiprise surrounding alleged violations of the GNU General Public License (GPL).
In addition to cutting-edge legal issues, readers remain very interested in more practical questions such as which open source license they should use.
And readers were also interested in the biggest software patent case from the Supreme Court in recent memory, Alice Corp. v. CLS Bank.
But it’s not just developments in the court that had readers’ interest: the FTC’s patent-assertion study represents a potentially important step to combat the harmful effects of Patent Assertion Entities.
Looking ahead to 2015, open source legal issues will likely remain in the news, with a possible new push to revive patent litigation reform in the United States under the new Congress.
-
Openness/Sharing
-
We have had quite a year of open science at Opensource.com in 2014! I couldn’t hope to cover every article we published over the year, but I will highlight some of my favorites. The tide is turning in science. More funding is going to open science projects, more publications are making their data available to everyone (especially other researchers), and all of this is hopefully beginning to impact hiring decisions.
-
Open Data
-
It feels that these days we live our whole digital lives according mysterious algorithms that predict what we’ll want from apps and websites. A new open-source product could help those building the products we use worry less about writing those algorithms in the first place.
-
Open Hardware
-
In 2015 we might see an open hardware random number generator that would connect to the system via an SD card slot.
-
Open hardware is the physical foundation of the open movement. It is through understanding, designing, manufacturing, commercializing, and adopting open hardware, that we built the basis for a healthy and self-reliant community of open. And the year of 2014 had plenty of activities in the open hardware front.
-
Health/Nutrition
-
As families across the country carry out the final preparations ahead of Christmas Day, many minds will be switching to turkey.
No, not the country, but the main ingredient of tens of thousands of festive dinners that will be enjoyed on December 25.
According to the Food Standards Agency, millions of people have been defrosting their turkey incorrectly and, due to that, have launched National Defrost Your Turkey Day.
And that day is today, December 22.
-
Security
-
-
At first, U.S. authorities said that the North Koreans didn’t do it. Then they said they did. The North Koreans countered with a “no-way-Jose” and offered to help in the hunt to find the real culprit, which elicited an adamant “no-way-back-atcha” from the U.S.
-
“The hack sounds similar to attacks involving the Stuxnet worm” http://www.itworld.com/article/2861675/cyberattack-on-german-steel-factory-causes-massive-damage.html dump #microsoft #windows http://techrights.org/wiki/index.php/Stuxnet
-
-
President Obama has done his best to tamp down fury at North Korea for hacking Sony–”I don’t think it was an act of war,” he said Sunday on CNN, but “cybervandalism”–but to find true skepticism about North Korea’s role in the attack, you have to turn to the professional hacking and anti-hacking community.
-
Even after the Federal Bureau of Investigation’s official statement that North Korea was behind the Sony attack, many cybersecurity experts are still skeptical the hermit nation is truly the culprit, citing a lack of new and more convincing evidence.
-
-
According to a report in Techcrunch, one particular employee, who wished to remain anonymous, told the online publication “We are stuck in 1992 more than here.” She was referring to how they dragged out old printers to cut cheques and dusted off fax machines to send messages. They had been even speaking to each other rather than sending emails or immediate messages.
-
Defence/Police/Secrecy/Aggression
-
Renowned commentator Noam Chomsky says that the US-Soviet war is taking the world on the brink of a Cold War that threatens to wipe out the world.
The threat of a nuclear war is hanging over the world again, ominously, adds the scholar, to RT’s Sophie&Co. It looks like both the US and Russia seem to be on the track of another Cold War.
-
The Russian economy is overly dependent on crude oil exports, and this ongoing crisis proves that it is not easy for Russia to be an extra-large Saudi Arabia. Some people suggest that Russia should learn from Canada and Australia, which have managed to transform huge reserves of natural resources into fortunes. However, due to Russia’s large population of 140 million people, its modernity and strong currency cannot be solely supported by oil, gas and timber.
-
But of course, the “war on terror” is very much about boosting the standing of politicians who are “fighting terror” on behalf of their citizens, and about boosting the ever-inflating powers – and budgets – of the security services. SO counterproductive measures are, paradoxically, the most attractive to those whose aim is not to obtain peace, but rather to maintain the concentration of power and finance consequent upon an eternal state of phoney war.
-
“Ambush Recharges Debate,” declares the front page of USA Today (12/22/14), a headline over a story about the killing of New York police officers Rafael Ramos and Wenjian Liu. The “debate” being recharged is presumably linked to the national protests against police brutality–protests that are in no way connected to this brutal murder.
-
Transparency Reporting
-
Let’s get one thing clear: The two secret CIA documents published today by Wikileaks will not make you a clandestine officer.
Both reports are aimed at teaching CIA agents traveling undercover to avoid unnecessary scrutiny at airports. The first, “Surviving Secondary,” dated September 2011, explains how not to be singled out for secondary screening by passport officers, and how to handle it if you are, while the second, “Schengen Overview,” from January 2012, summarizes the information systems used by the 26 European countries that have open borders with each other as part of the Schengen agreement.
-
It advises that “smart phones, iPods, and MP3 players, can pose a vulnerability to alias travel because of their requirement for subscriptions. If border control officials can establish a link between the device and the traveler’s true name,this could present a difficulty for someone traveling in alias,” which is a classic concern of those critical of the global security state.
-
PR/AstroTurf/Lobbying
-
In a digital world the media often struggles to maintain the attention of its audience. Between horrific mass killings, viral outbreaks, violent authority figures, terrorists, and tantalizing political melodrama, the focus of our media shifts constantly.
The following six topics from 2014 were once a major focus of the fleeting attention of the media. Each of them at one point has received overwhelming media attention to become a fixture of American dialogue before fading into obscurity.
-
Truthiness has replaced truth. Now that we all have our own facts, we may rue the day we personalized the news
-
As I’ve written before (FAIR Blog, 12/2/09), reading the Washington Post opinion pages can be like reading dispatches from a parallel universe. You get that sense of alternative history from Post deputy editorial editor Jackson Diehl’s latest piece (12/21/14), teeing off on Barack Obama’s statement that “we know from hard-earned experience that countries are more likely to enjoy lasting transformation if their people are not subjected to chaos.”
-
It’s that time of year again, when FAIR looks back at the year and recalls some of the stinkiest media moments. There were, of course, many contenders– but only a select few can make the list.
-
Privacy
-
Congress last week quietly passed a bill to reauthorize funding for intelligence agencies, over objections that it gives the government “virtually unlimited access to the communications of every American”, without warrant, and allows for indefinite storage of some intercepted material, including anything that’s “enciphered”.
-
The spy agency has suffered “significant” damage in its ability to monitor and capture serious organised criminals following the exposes by the former CIA contractor.
-
-
Thomas White (@CthulhuSec) warned users to steer clear of his Tor servers after he lost control following what he’s called “unusual activity.” In a post on Tor mailing list Thomas said,”I have now lost control of all servers under the ISP and my account has been suspended.”
-
We have yet another story on the intelligence sharing regarding the 26/11 attack and it has almost become a habit for the Americans and the British to let out such information in bits and pieces year after year. The US has time and again said that intelligence was shared with India on the 26/11 attack and this fact has been repeatedly denied by India. For India the attacks were not specific enough to collate and act upon.
-
There were a series of “missed signals” about Pakistani-American David Headley’s involvement in the 26/11 Mumbai attacks even though he had exchanged “highly suspicious” emails with his LeT and ISI handlers before and after the assault, an investigative report said.
-
Three spy agencies collected intelligence that could have thwarted the lethal terror attack in Mumbai in 2008 but failed to put the pieces together, according to a report published late Sunday evening by The New York Times and Propublica, an online news source.
-
Indian and British intelligence agencies monitored the online activities of a key plotter but couldn’t connect the dots.
-
Hundreds of protesters took to the streets of Brussels on Friday to express anger about secret trade talks between the EU, US and others that they believe would damage the 28-member-state bloc’s data protection rights.
More than 1,000 people marched in the centre of the EU quarter to protest about the Transatlantic Trade and Investment Partnership (TTIP) and the Trade in Services Agreement (TiSA). The latter has provoked outrage following a leak of the US position from April 2014 that was published on Wednesday by Netzpolitik.org and Associated Whistleblowing Press. It focuses on e-commerce, technology transfer, cross-border data flows and net neutrality.
-
The US is gearing up for a major power play among its ‘allies’ through the Trans-Pacific Partnership Agreement (TPP) and the Trade In Services Agreement (TISA). Chief among its many controversies is what amounts to the US spying on its partners, all in the name of ‘anti-protectionist’ measures.
-
The thing that perplexes me is why so many people still use Facebook these days. I can understand wanting to stay in touch with friends and family, but there are plenty of other ways to do that. Video chat, instant messaging, and email all work well and do not expose private information to Facebook’s algorithms and advertising systems. Yet some people behave as though Facebook is the only way to maintain contact over vast geographic distances and time zones.
-
Civil Rights
-
The recent Senate Intelligence Committee’s report on CIA interrogations is a parade of horribles. Detainees by the dozen arrested wrongfully and later released, including innocent nobodies and even men with mental disabilities. Poorly vetted interrogators with disciplinary problems and financial conflicts of interest. Relatives held as hostages to gain leverage over targets. Incredibly shoddy intelligence analysis.
-
For the past eight months, there has been a furious battle raging behind closed doors at the White House, the C.I.A., and in Congress. The question has been whether the Senate Select Committee on Intelligence would be allowed to use pseudonyms as a means of identifying characters in the devastating report it released last week on the C.I.A.’s abusive interrogation and detention program. Ultimately, the committee was not allowed to, and now we know one reason why.
-
NBC News yesterday called her a “key apologist” for the CIA’s torture program. A follow-up New Yorker article dubbed her “The Unidentified Queen of Torture” and in part “the model for the lead character in ‘Zero Dark Thirty.’” Yet in both articles she was anonymous.
The person described by both NBC and The New Yorker is senior CIA officer Alfreda Frances Bikowsky. Multiple news outlets have reported that as the result of a long string of significant errors and malfeasance, her competence and integrity are doubted — even by some within the agency.
The Intercept is naming Bikowsky over CIA objections because of her key role in misleading Congress about the agency’s use of torture, and her active participation in the torture program (including playing a direct part in the torture of at least one innocent detainee). Moreover, Bikowsky has already been publicly identified by news organizations as the CIA officer responsible for many of these acts.
-
Since the day President Obama took office, he has failed to bring to justice anyone responsible for the torture of terrorism suspects — an official government program conceived and carried out in the years after the attacks of Sept. 11, 2001.
He did allow his Justice Department to investigate the C.I.A.’s destruction of videotapes of torture sessions and those who may have gone beyond the torture techniques authorized by President George W. Bush. But the investigation did not lead to any charges being filed, or even any accounting of why they were not filed.
-
From a maximum-security prison in Texas, former United States military analyst Ana Montes has been offering up bumper-sticker justifications for why she betrayed her country and spied on behalf of the Cuban government over the course of 17 years. “I believe that the morality of espionage is relative,” Montes wrote in a private letter to a friend last year. “The activity always betrays someone, and some observers will think that it is justified and others not, in every case.”
-
Tabling the draft, Director of the Commission for Legislative Affairs of the NPC Standing Committee, Li Shishi, told lawmakers, “It was necessary to make a fundamental law on national security in accordance with the new contemporary environment.”
-
One popular device, the LRAD-100X, was used in Ferguson, and on two days last week, it was used to warn off demonstrators in New York City protesting the death of Eric Garner. According to its manufacturer, the LRAD offers police “near instantaneous escalation across the force protection spectrum” to “shape the behavior of potential threats.”
-
DRM
-
Rockstar’s Max Payne 3 is 70% off right now as part of the 2014 Steam Holiday Sale, but would-be neo-noir crime story aficionados were denied entry into the cynical world of the drug-dependent detective yesterday by a failure in the game’s third-party authentication and matchmaking system. Starting early on Friday, December 19, the Rockstar Social Club component of the game would respond only with “Error contacting activation server” when players tried to start up the game for the first time.
-
Intellectual Monopolies
-
Copyrights
-
A group of 12-year-old girls were left in tears after being hauled out of a cinema by police when staff falsely accused them of recording The Hunger Games on their mobiles and iPads.
The seven children, who attend one of the country’s leading independent girls’ schools, were quizzed after staff dialled 999 and reported the allegation as an ‘emergency’.
-
Pressure for EU reform is now greater than ever. The UK earlier this year passed a law that legalized private copying by individuals without any requirement for additional compensation to artists. Two years ago Spain replaced levies with a government compensation fund similar to the one adopted in Finland this week.
Although it’s true that progress has been made, it’s also worth noting that the usual copyright dinosaurs are fighting back, and that the final outcome is by no means clear. In the UK, the music industry has said that it may try to challenge the private copying exception in the courts. In Spain, legal action by collecting societies has resulted in two key questions about copyright levies being sent to the European Union Court of Justice, and its judgment on the case is likely to have important implications for such levies throughout the EU.
Permalink
 Send this to a friend
Send this to a friend
12.21.14
Posted in News Roundup at 9:53 pm by Dr. Roy Schestowitz

Contents
-
Linux is a platform ready for everyone. If you have a niche, Linux is ready to meet or exceed the needs of said niche. One such niche is education. If you are a teacher or a student, Linux is ready to help you navigate the waters of nearly any level of the educational system. From study aids, to writing papers, to managing classes, to running an entire institution, Linux has you covered.
If you’re unsure how, let me introduce you to a few tools Linux has at the ready. Some of these tools require little to no learning curve, whereas others require a full blown system administrator to install, setup, and manage. We’ll start with the simple and make our way to the complex.
-
There is a reason why China and others are trying to move away from Windows to Linux and other alternatives, and it is not to avoid sending its hard earned dollars to Cayman Islands (or whatever tax haven Microsoft is using these days to collect the majority of its income. 
-
Welcome to this week’s edition of About Linux Weekly News. Some of you will probably have noticed that this bulletin is going out later than normal and there is a very good reason for that.
-
Server
-
Infoxchange is one of the few places I’m aware of that runs Docker in prod. If you’re looking at using Docker to do web development, it’s worth checking out what we’ve been doing over on the Infoxchange devops blog.
-
Nick Hardiman argues that the problem with Linux is that multi-purpose distros, which are great for cloud computing jobs, are making the server OS fat.
-
Hewlett Packard High-performance computing (HPC) markets are powered by the adoption of Linux clusters. High-performance computing (HPC) markets are powered by the adoption of Linux clusters. Cluster complexity is rampant hardware parallelism: systems averaging thousands of processors, each of them a multi-core chip whose core count doubles every 18.24 months.
-
But before Docker co-founder and CTO Solomon Hykes got a chance to board the plane, he got word that operating-system provider CoreOS announced its own Rocket container technology, which caught the Docker team off guard, according to Docker CEO Ben Golub in this week’s Structure Show.
-
Kernel Space
-
Merged already for Linux 3.19 were significant power management and ACPI changes while a second serving of ACPI+PM updates have been requested for pulling just prior to the end of the 3.19 merge window.
-
With the Kernel-based Virtual Machine in Linux 3.19, the code for the IA64 architecture has been dropped. Hardware-assisted virtualization for the PowerPC 970 was also dropped as part of some “spring cleaning” of KVM.
-
The Linux Foundation has announced via it’s blog that those who sign up for the $99 individual membership will be entitled to a $100 discount from certification courses that the Linux Foundation offers, in addition to this they have said that if you become a member by January 16th 2015 they will donate $25 to Free Geek, a non-profit which refurbishes old computers and donates them back to schools, community organisations and sells them on it’s online store.
-
The first Linux kernel Release Candidate has been made available in the 3.19 branch and it looks like it’s one of the biggest ones so far. Linux Torvalds surprised everyone with an early launch, but it’s easy to understand why.
-
-
In the past I’ve written a number of favorable entries about systemd. In the interests of balance, among other things, I now feel that I should rake it over the coals for today’s bad experiences that I ran into in the course of trying to do a yum upgrade of one system from Fedora 20 to Fedora 21, which did not go well.
-
-
Hewlett Packard is going to introduce their “revolutionary” new operating system next summer that’s dubbed Linux++.
-
Graphics Stack
-
I’m sure you’ve seen a 4k monitor on a friends desk running Mac OS X or Windows and are all ready to go get one so that you can use it under Linux.
-
Benchmarks
-
The performance of Civilization: Beyond Earth on Linux is quite demanding. The OpenBenchmarking.org test profile of Civilization Beyond Earth uses roughly the high image quality settings and for this article the tests were done at 1920 x 1080. As the results are about to show, even with modern graphics cards, it’s quite a chore putting out a decent frame-rate at 1080p for this strategy game.
-
Applications
-
-
-
-
Proprietary
-
I almost missed one of the most important Dropbox updates, thanks to Arch Linux. The package was updated a few days ago when I ran a system update, I did see a Dropbox update with version 3.something but didn’t pay attention until I booted my system and had to unlink it to move the folder. That’s when I spotted the Qt based UI we reported a few months ago.
-
There are stable, beta, and developer updates out this week for the Linux / OS X / Windows versions of the Opera web-browser.
-
Instructionals/Technical
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
Revision control is a practice that tracks and provides control over changes to source code. It is a critical tool in the developer’s tool chain. Git is a distributed revision control system initially designed and developed by Linux Torvalds for Linux kernel development. It is used on many kernel-related projects besides the Linux kernel such as OpenVZ, KVM, ALSA, and udev. Git is also frequently used for source code management for non-kernel projects.
-
Games
-
“Furthermore, it also means that the toolset is going to be improved for a long time to come and so eventually we’ll get more and better mods. We’ll even have a Linux version.”
-
Sid Meier’s Civilization: Beyond Earth, the latest title in the Civilization franchise, is finally coming to the Linux platform and the released date is tomorrow, December 18.
-
Divinity: Original Sin is a complex RPG developed by Larian Studios that managed to get a lot of praise from the community. It’s been out on Windows for quite some time and the developers are also planning a Linux version.
-
Run or Die, a new 2D endless runner developed and published by Team Flow on Steam has been released for all the supported platforms, including Linux.
-
Desktop Environments/WMs
-
K Desktop Environment/KDE SC/Qt
-
-
To generate this changelog we diff from previous release to the released one and use the commit message with a few annotations for stuff like REVIEW: BUG: etc.
-
The KDE Community just announced that Plasma, the desktop for the KDE project, is now at version 5.1.2 and it comes with a large array of changes, improvements, and various fixes.
-
I always have been a huge fan of astronomy, stars, cosmos etc. I must admit that I find it absolutely breathtaking, especially, looking at particular constellations, the way they combine into jewelry shapes that have lots of similarities with known objects. Interesting, somewhere in space there could be a guy like me, looking at sky and finding other objects…
-
Plasma 5 pushes QtQuick to the limits. It sounds like a cheesy marketing line, but it’s true. Unfortunately this isn’t a good thing. Although Plasma 5.1 is somewhat stable we have had some crashers, and whilst we’ve worked hard to fix the ones that are ours a sizeable number of these were caused by problems deep inside Qt.
-
digiKam Software Collection is digital photo management application for the KDE desktop that includes an image editor for photo corrections and manipulation. The application was just updated to version 4.6.0.
-
The digiKam Software Collection 4.6 release offers many bug fixes to the image editor and batch queue manager. There’s also many other bug-fixes found with today’s update. The next bug-fix release for digiKam 4.x is planned in 2015.
-
Trinity, a desktop environment for Unix-like operating systems with a primary goal of retaining the overall KDE 3.5 computing style, has finally reached version R14.0.0 and is now ready for download.
-
Kubuntu 15.04 Alpha 1 (Vivid Vervet), a Linux distribution based on Ubuntu that uses the KDE desktop environment, has been released and is now ready for testing.
-
Well, Marley might be dead, but Krita ain’t! So, here’s what’ll be the last beta build of Krita before the festive season really breaks lose. Apart from building, the Krita hackers have had a pretty good week, with lots of deep discussions on animation and coding safety, too.
-
After adding the first theme, I was working on a theme on nature. That theme represents the basic elements in the nature such as trees, flowers and etc. Since KDE Pairs is developed for pre school children the objects represented in the themes should be familiar and educational to them. Following are some screen shots after adding the theme nature to the game. These screenshots represents the different game modes such as logic, pairs, relations and words.
-
GNOME Desktop/GTK
-
Appart from porting Yelp, I submit a patch to WebKit2Gtk+. I expose some part of the API to could check if the clicked element corresponds to a selected area or not. Working with the WebKit code has been a really challenging and cool experience that I want to repeat. When I have time I would end my work on this patch to enable improve plugin support at WebKit.
-
At the GUADEC I spoke with Allan Day about a new design for gnome clocks. He was very fast in putting it into an image. It will fix some issues, among them we will get multiple and labelled timers so we can stresslessly roast potatoes while baking a cake and making a tea – repeatedly without having to redefine the timers. Strange meal though.
-
Various GNOME packages are being checked in this week for GNOME 3.15.3, another development release toward GNOME 3.16.
-
-
Looking back at my 2013 summary, I just realized I’m a bloody prophet. I wanted openSUSE to make a nice comeback, and it did. And I wanted Fedora to shine, and it did, and it’s version 20 no less. The utter and total dominance of the Ubuntu family has been shattered, and this is a very good thing. Competition is always good.
What about Mint, you ask? Well, Linux Mint behaved splendidly, but this year, the few spins I tried weren’t as sharp and spectacular as what we saw in 2013. Not necessarily a bad thing, but the best-of is more than just a list of grades. It also packs an emotional element, a surprise element, as well as the overall combination of what the selected distributions have achieved with their given parameters. For instance, CentOS is not supposed to be a desktop system, so when it does that well, it’s more interesting than similar results with the stock Ubuntu family members and cousins. Hence, this list and its players.
Of course, this is entirely my private, subjective observation, but I think it fits the global shift in the Linux field. With the Mir vs Wayland game, a big delay in Ubuntu Edge, and a general cooling off in the distro space, seeing more effort from outside the Ubuntu range is only natural. And welcome. That said, the big winner is still Trusty, and it shows that even though some years may be rougher than others, Ubuntu has its merit and cannot be easily disregarded, no matter how we feel, or want to feel, even if purely on a reactionary basis. And to prove us all wrong, Canonical has baked a phenomenal LTS release, which should bring much joy and fun to Linux users worldwide for years to come. I hope you’ve liked this compilation. See you next year.
-
As the year draws to a close it is a good time to reflect on the good and bad of 2014.
In this article I am going to list my favourite alternative Linux distributions of the year.
What constitutes as an alternative Linux distro? To define the alternative, we need to look at the mainstream distributions first.
-
Reviews
-
Debian is the great-granddaddy of many Linux distributions, and Parsix is definitely one of its grandchildren. Parsix uses Debian as its base, but builds on it to provide a very desktop-oriented distribution. Parsix has reached version 7.0 and this release ships with GNOME 3.12 as the default desktop, and Linux kernel 3.14.23.
-
Tanglu GNU/Linux is a distribution based on Debian Testing. When I wrote recently about the future of Linux Mint Debian Edition and other distributions based on Debian Testing, what I was concerned about was the fact that they will be changing their base to Debian Stable in the near future. Tanglu has not given any indication that they intend to change, so this could be a good alternative for the future.
-
New Releases
-
Devil-Linux 1.6.7 has been released! This release brings lots of software updates. Please see the change log for details.
-
SuperX 3.0 Beta, an operating system that is highly modular, flexible, and that comes with a customized KDE desktop aimed at all user categories, is now available for download and testing.
-
Slackware Family
-
There was an announcement a few days ago by The Document Foundation about their latest release. LibreOffice 4.3.5 is now available for download. When browsing the download directories, I noticed that sources for 4.4.0 are already present there, but since there is no public announcement yet, I chose to ignore those sources for now. The 4.3.5 release targets “individual and enterprise users” and fixes 70 bugs compared to the previous version – which is perfect for a Slackware 14.1 user.
-
Red Hat Family
-
Red Hat Enterprise Linux for SAP Hana will help organisations make smarter, faster decisions; accelerate business processes; and enable consistency of operations across the business through standardisation on the Red Hat platform, which powers mission-critical systems in more than 90 per cent of the global Fortune 500.
-
-
Customers around the world are changing their perceptions about open-source technology, making it more mainstream, and open source is driving innovation at enterprise and cloud services giant Red Hat (RHT) , according to its president and chief executive Jim Whitehurst.
Red Hat, the world’s largest provider of open-source solutions, reported fiscal third-quarter results Thursday that topped Wall Street’s revenue and profit estimates, sending its shares up more than 9% in after-hours trading. In an interview after earnings were released, Whitehurst discussed Red Hat’s performance and outlined how the company plans to stay ahead of the competition in its core markets.
-
With the recent hack on Sony, one major issue on the minds of businesses in the U.S. is cybersecurity. Jim Cramer has had his eye on Red Hat, as it is the largest provider of open sourced software in the world.
Not only is the company is up 28 percent since June, and is right in the epicenter of the cloud software security debacle.
When Red Hat refers to open source, its goal is to create collaboration with technology that allows the users to see the code, learn from it, ask questions and offer improvements. The company offers the software for free and then sets up its customers as subscribers who pay regular fees for maintenance and customer service.
Cramer spoke with Red Hat CEO James Whitehurst to find out his take on the issue of cybersecurity and where the stock could be headed.
“I’m not surprised that it happened, and we are obviously involved with a lot of agencies that look at security, and it’s a major, major problem in general,” Whitehurst said.
He stated that the root of the problem is not just about the technology. The issue stems from people and access to passwords with every company at risk. He described it as a “multifaceted, layered and complex problem.”
So with Red Hat promoting an open software platform, does that make them vulnerable to cybersecurity risks?
“I think open source itself is proving to be very safe. The simple analogy here is; are you safer in a crowded shopping mall or down a dark alley? Having the wisdom of the crowd is actually a powerful thing,” the CEO said.
-
Red Hat Inc. ( RHT ) reported third quarter adjusted EPS of $0.42 after the bell Thursday, which was flat with the prior year result. The consensus estimate was for EPS of $0.40.
-
-
In an announcement on Monday, Red Hat have said that their Red Hat Enterprise Linux (RHEL) for SAP HANA can be deployed on public clouds as well as that Hitachi Data Systems (HDS) have joining the RHEL for SAP HANA ecosystem as a certified hardware partner and will begin offering RHEL for SAP HANA on SAP-certified hardware.
-
Red Hat’s strategy of sacrificing service revenues to increase subscription revenues over the long run is expected to hurt top-line growth in the next couple of quarters.
-
After more than ten years of development, Dan Williams of Red Hat has announced the release of NetworkManager 1.0. The NetworkManager 1.0 release is more than just bumping the version after waiting long enough, but there’s many improvements too over NetworkManager 0.9!
-
The news never stops and Sky News must ensure its systems are always available and adaptable for changes to service provision.
To ensure the scalability and resiliency of operations, the news organisation has deployed Red Hat Enterprise Virtualisation and Red Hat Satellite in two datacentres. The upgrade to IT infrastructure allows the firm to deliver flexible broadcasting and publishing.
-
-
-
The Raleigh, N.C.-based company reported third-quarter GAAP net income of $48 million, or 26 cents a share, compared with $52 million, or 27 cents a share, in the year-earlier quarter. Adjusted earnings per share of 42 cents came in higher than analysts’ expectations of 40 cents. Revenue jumped 15% to $456 million.
-
Red Hat (NYSE:RHT) earned at least 10 price target hikes from investment banks Friday, after the Linux leader late Thursday posted Q3 earnings that soundly beat estimates, and its stock rose to 14-year highs.
-
After eleven and a half years, today is my final day at Red Hat.
-
Fedora
-
-
For the moment next 6 months, i will stick with fedora 21 only, Lets see what UBuntu 15.04 will come up with an answer to Fedora 21.
-
So if you think of yourself as the adventurous type, someone who likes everything to be pretty new all the time but doesn’t really want to deal with a lot of breakage and is curious about Wayland in the real world, give Fedora 21 a try.
-
-
-
OpenStack can now be installed using Fedora 21 or Rawhide, on aarch64 hardware.
-
Debian Family
-
Derivatives
-
Elive, a Linux distribution that uses Debian as a base and Enlightenment as the default desktop environment, has been upgraded to version 2.5.0 Beta. The devs are still making some important changes and this latest release is proof of that.
-
Canonical/Ubuntu
-
First alpha of Ubuntu flavors of 15.04 cycle is available for download and testing. Since Ubuntu Unity doesn’t participate in the alphas there will be only on beta of Ubuntu Unity in March, 2015.
-
The first alpha releases in the Ubuntu 15.04 development cycle are now available to download for testing.
Four flavors participate in this milestone, including Ubuntu GNOME and Kubuntu. Ubuntu ‘proper’ will once again only participate in the final beta release due March 2015.
-
There isn’t much time left in 2014 so we suppose it comes as no surprise that Canonical, the parent company behind Ubuntu, recently confirmed that the first Ubuntu-powered smartphones have been delayed until “early” next year. The first Ubuntu-powered devices were originally scheduled to launch sometime in 2014.
-
Canonical’s stripped down “Snappy” edition of Ubuntu Core is now available on Amazon’s AWS cloud computing platform.
If you’ve followed along over the last few weeks, that’s not a major surprise. Snappy first launched on Microsoft Azure at the beginning of this month and then arrived on Google’s Compute Engine platform earlier this week. It was pretty obvious that AWS’s EC2 would be next.
-
-
In the first week of February BQ will be launching a version of it’s Aquaris e4.5 device loaded with Ubuntu software, the release will be limited to Europe for now however it will still have the low price of €159. The launch will see Ubuntu Phone’s debut launch of a commercial device, unless Meizu surprise up and release their device before then.
-
The contest is an extension of national carrier China Mobile’s ‘”AND Your Dream Come True” Million Youth Entrepreneurship and Employment Programme’ . Launched in 2010 with support from the Communist Youth League Central Committee, ‘AND’ aims to give young people employment opportunities and foster a sense of “can do”.
-
It looks like the Ubuntu team made a very good decision in creating the new, stripped down and fast performing “snappy” version of Ubuntu Core. This minimalist take on Ubuntu is targeted at those doing cloud deployments, and is already integrated with Microsoft’s Azure cloud platform and Google Cloud. Snappy is optimized for Docker deployments and platform-as-a-service environments, as I covered here.
-
Canonical has issued fixes for a number of Linux kernel vulnerabilities that have been identified and resolved by the developer for Ubuntu 14.10 (Utopic Unicorn).
-
Flavours and Variants
-
The Linux Mint developers have just outed the first and probably only RC for the Linux Mint 17.1 “Rebecca” Xfce edition. Users can now download the images and test the new release.
-
Linux Mint 17.1 “Rebecca” KDE RC uses KDE 4.14 as the default desktop environment and it looks like users will have to keep employing this old version for a while. KDE SC 4.14.3 was made available a couple of weeks ago, but it’s the last one in the series.
-
Ubuntu Kylin, a Chinese Linux distribution based on Ubuntu and developed in collaboration with Canonical, has been promoted to version 15.04 and the first Alpha in the series is now ready for download and testing.
-
-
Phones
-
Lenovo early next year will announce two new smartphones , with both using not only a low-power 64-bit Atom processor but also a cellular modem chip from Intel, according to a report in The Wall Street Journal. One of the smartphones will be sold in China, a growing market that Intel officials have tagged as being key to the company’s mobile ambitions.
-
Tizen
-
Samsung has had a busy year with Tizen and not only in with Smart watches. Following the release of the first Tizen Smart Camera, the Samsung NX-300M, we have had the NX Mini, NX 30 and recently the NX1.
-
Android
-
This year kicked off with OnePlus and Cyanogen Inc announcing the OnePlus One invitation only device which created a buzz in the tech community, since then, relations have taken a downward turn and now the two companies are in a legal debacle over the Indian market.
Back in February on the 28th, OnePlus and Cyanogen both signed a collaboration agreement and earlier on that month, on the 1st, they signed a trademark license agreement which is valid until 31st January 2016. These agreements meant that OnePlus was allowed a non-exclusive license to use Cyanogen trademarks and software worldwide except mainland China. Everything is OK up until September 2014.
-
This hands-on review takes a first look at SolidRun’s tiny CuBoxTV set-top box, running both its default OpenELEC/XBMC OS, as well as an Android 4.4.4 beta.
The CuBoxTV is one of several CuBox-i models currently available from Israel-based SolidRun. Whereas the full-up “CuBox-i Pro” model comes with 2GB RAM, WiFi, and Ethernet, the CuBoxTV hits a $110 price target though the reduction of RAM to 1GB and the elimination of the WiFi/Bluetooth radio module, though it still possesses the power of a Freescale i.MX6 Quad SoC clocked at around 1GHz.
-
I pay for a premium membership, and to be honest, I don’t think I even use the premium features. I just love Evernote so much, I want to support the company. But in the spirit of fair comparison, I forced myself to try Google Keep.
-
Android fans rejoice, for today Blizzard’s super-addictive digital card game, Hearthstone, is available for Android tablets. Sure, it’s been out on PC and iOS for a while, but it’s a newcomer amongst the Android ranks — and since it’s a game that’s really designed for the touchscreen experience, that’s definitely a tough fact for Android owners to cope with.
-
Blizzard’s free-to-play card game Hearthstone: Heroes of Warcraft is now available to Android tablets in Australia, New Zealand, and Canada. The game can be downloaded for free from the Google Play store and Amazon Appstore. Blizzard has announced that a worldwide release will roll out “in the days ahead.”
-
There are must have Android apps that everyone has – the big apps that get all the buzz. There are also apps that win popularity contests in specific groups of people.
But there are also Android apps worthy of download that aren’t that well known. Think of them as the “must have” underdog list.
To avoid missing out on what may prove to be your most helpful app ever, take a look at these lesser known contenders:
-
We pride ourselves at The Apache Software Foundation on our principles of “community over code” and “don’t be a jerk”. But, alas, we’ve been slow to codify some of these things in public. Part of this, I’m sure, is that it’s easy to think we all just know how we’re supposed to treat people, and so you shouldn’t have to say, right?
-
In a recent post on the organization’s blog, Chris Price, chairman of the technical steering committee (TSC) for the Open Platform for NFV Project (OPNFV), said the panel is reviewing a broad array of project ideas to see what ones will be pursued by the committee. In addition, the wider OPNFV community will focus on establishing an integration and baseline platform while also creating several NFV-related projects that will find their way into the OPNFV’s second release of 2015.
-
-
OpenDaylight accepted seven student interns for the summer of 2014 to work in the community and receive hands-on development experience in SDN. Each intern worked closely with an active OpenDaylight developer as their mentor on a project that suited interest and community need.
-
Cloud Dataflow, which it describes as “a platform to democratize large-scale data processing by enabling easier and more scalable access to data,” was just unveiled in June. It’s still an alpha release, but used internally in the company, Google says.
-
All the way back in June, at Google I/O, Google pronounced that the venerable MapReduce data crunching scheme was “tired” and launched a service dubbed Cloud Dataflow that analyzes pipelines with “arbitrarily large datasets.” Dataflow was a much talked about star in a set of cloud services discussed at Google I/O and Google officials even confirmed that Dataflow had replaced MapReduce at Google. MapReduce, of course, is built for processing and generating large data sets with a parallel, distributed algorithm on clusters.
-
Events
-
The GNOME Asia Committee is pleased to announce that the upcoming GNOME.Asia Summit 2015 will be hosted in Depok Indonesia May 7-9 2015. It will be a great place to celebrate and explore the many new features and enhancements to GNOME 3.
-
We are thrilled to report that GNOME.Asia is a founding member of KAIYUANSHE(开源社) launched Oct 16, 2014. KAIYUANSHE roughly translated as “open source alliance,” is a group of enterprises, communities, and individuals in China supporting and promoting free and open source software (FOSS).
-
Web Browsers
-
Chrome
-
Dell is now dishing out full-fledged USB Chrome keyboards on its online store in the US, and it is expected to start selling it outside the US soon.
-
Google’s media streaming stick Chromecast now has a guest mode. That means you no longer have to share your Wi-Fi password with your guests if they want to stream a video from their smartphones to your television.
-
Mozilla
-
The Mozilla project is dedicated to tackling these challenges. Our community makes Firefox products that are loved and used the world over, all in service of our mission to protect the Web. We are also hard at work teaching thousands more people how to help build the Web, developing innovative open source technologies for others to leverage, protecting individual privacy and establishing technical standards.
-
It looks like the effort to bring Mozilla Firefox to Apple IOS iPhone/iPad devices is getting real. Some very preliminary code for the effort is now available on Github.
-
Databases
-
The open source cross-platform document-oriented database company MongoDB has acquired WiredTiger for its database storage engine technology.
-
PostgreSQL 9.4 is out in time for Christmas with numerous changes for users of this open-source database solution.
-
Oracle/Java/LibreOffice
-
The Document Foundation announces LibreOffice 4.3.5, the fifth minor release of LibreOffice 4.3 “fresh” family, which is a stable release of the more advanced version of the software, targeted to individual and enterprise users. LibreOffice 4.3.5 contains over 70 bug fixes.
-
…importance of working with upstream projects and initiatives for a government like the UK Government.
[...]
Public interest and software freedom are not always aligned, in the sense that software freedom grant rights to users of Free Software but does not imply users will get what they want; in this case however, these two notions could become very much aligned. The same holds true for Open Standards: if major chunks of the UK’s public sector’s pool of documents is migrated to ODF, there is something close to a liability – and an opportunity- for this Government to ensure the format continues to thrive and be improved.
-
CMS
-
The popular open-source CMS and blogging system gets a major milestone update that includes an enhanced distraction-free writing mode.
-
-
FSF/FSFE/GNU/SFLC
-
-
For those sticking to the GCC 4.8 compiler series rather than the newer GCC 4.9 stable series, the GCC 4.8.4 release is now available.
-
With OpenACC, NVIDIA’s NVPTX back-end, and other improvements finally materializing within mainline GCC and its related code-bases, users are beginning to wonder how to actually use these new GCC features and experience GPU offloading with this free software compiler.
-
Public Services/Government
-
The European Parliament has approved funding for several projects related to Free Software and privacy. In the EU budget for 2015, which the European Parliament adopted on December 17, the Parliamentarians have allocated up to one million Euro for a project to audit Free Software programs in use at the Commission and the Parliament in order to identify and fix security vulnerabilities.
-
Public administrations in the EU are hindering competition by asking for specific brands and products when procuring software solutions, says OpenForum Europe, an organisation campaigning for an open, competitive ICT market. “No progress has been made in recent years. In fact the practice of referring to brand names in public procurement has become more widespread”, OFE says.
-
EU software procurement breaches rules more than ever before – OFE PDF – Because they really do prefer to feed what they perceive as corporate power brokers rather than work to create European value with European money.
EU allocates half million euros for testing open source – FSFE – It’s a rounding error on the budget, but at least it’s something. Let’s see who gets it.
-
Openness/Sharing
-
If cars are indeed set to become “smartphones on wheels”, able to connect to the internet and each other, there are a few things we need to settle first. What kind of operating system will they run on, for example, and will they use proprietary or open source applications? Will upgrades to the car’s underlying system happen as seamlessly as mobile OS updates do today, or will you have to call out a mechanic?
-
It looks like our Linux friend Tux enjoys racing karts! The SuperTuxKart team is wishing its gamers a Merry Christmas by releasing SuperTaxKart 0.8.2 beta. SuperTuxKart is a 3D kart racing game licensed under GPLV3 and available on many platforms, including Linux. This new beta release includes a new graphical engine, Antartica. You should really check out the release post and the screenshots of the improved graphics. Another new feature is online accounts in preparation of networked multiplayer gaming—which is still to come.
-
Why do we share? What makes it different from giving? And what does it have to do with strategy and impulse control? Mike talks to the scientist Nikolaus
-
“We just wanted to play video games in real life,” said Ibrahim Pasha, the youthful CEO of Skirmos — an ambitious open-source laser tag gun started by a handful of former high school pals.
-
The holiday season is in full swing and you may still have a few people to check off your gift-giving list. If you’re at a loss for what to buy the open-source-focused engineer or maker in your life, take a gander at these 8 open-source gifts.
-
-
Open Data
-
U.S. intelligence agencies and the military are increasingly leveraging analytics platforms based on machine learning to sift through data sources like social media. In the vernacular of the Pentagon, these efforts are generally referred to as open source intelligence initiatives.
-
Security
-
-
In the meantime, you can use this extension to turn off SSLv3 in your copy of Firefox. When you install the add-on, it will set the minimum TLS version to TLS 1.0 (disabling SSLv3). If you want to change that setting later, like if you really need to access an SSLv3 site, just go to Tools / Add-ons and click the “Preferences” button next to the add-on. That will give you a drop-down menu to select the minimum TLS version you want to allow.
-
Several severe vulnerabilities have been found in the time setting software NTP. The Network Time Protocol is not secure anyway due to the lack of a secure authentication mechanism. Better use tlsdate.
-
Alert Logic admits it has NOT seen any exploits that harness this vulnerability. Other security firms believe Alert Logic is overstating the risk, which Trend Micro characterises as “limited”.
[...]
An independent researcher first posted about the vulnerability – which he called PackageKit Privilege Escalation – almost a month ago before Alert Logic picked up on the threat and publicised it.
-
-
“Linux clients are not affected if they run in a case-sensitive filesystem,” the service’s warning reads, but are nonetheless encouraged to upgrade. Windows and Mac OS users have no excuse not to upgrade, as “Git clients running on OS X (HFS+) or any version of Microsoft Windows (NTFS, FAT) are exploitable through this vulnerability.”
-
Defence/Police/Secrecy/Aggression
-
Some politicians seem to act as if “terrorism” means a terrible crime committed by someone who doesn’t fit the speaker’s own racial & religious profile. Just because something induces terror in some or many people, that doesn’t make it terrorism. That diminishes the concept as well as grouping routine crime – for which society has millennia of experience and solutions – into the same bucket as a more subtle and serious phenomenon that preys on the meshed society.
-
Environment/Energy/Wildlife
-
The first thing you notice about the Mirai, Toyota’s new $62,000, four-door family sedan, is that it’s no Camry, an international symbol of bland conformity. First there are the in-your-face, angular grilles on the car’s front end. These deliver air to (and cool) a polymer fuel-cell stack under the hood. Then there’s the wavy, layered sides, meant to evoke a droplet of water. It looks like it was driven off the set of the Blade Runner sequel.
-
Finance
-
The Times might offer in its defense that this piece is labeled as one of Sullivan’s “Wealth Matters” columns, a feature specifically set up to give advice to the 1 percent (or the 0.01 percent) on how to “manage not only their money and fortune, but their overall well-being.” To which one can only note that it’s not a coincidence that the Times does not have a “Poverty Matters” column.
-
Censorship
-
BT, Sky, and Virgin Media are hijacking people’s web connections to force customers to make a decision about family-friendly web filters. The move comes as the December deadline imposed by prime minister David Cameron looms, with ISPs struggling to get customers to say yes or no to the controversial adult content blocks.
[...]
The hijacking works by intercepting requests for unencrypted websites and rerouting a user to a different page. ISPs are using the technique to communicate with all undecided customers. Attempting to visit WIRED.co.uk, for example, could result in a user being redirected to a page asking them about web filtering. ISPs cannot intercept requests for encrypted websites in the same way.
BT is blocking people’s browsers until they make a decision, making it impossible for customers to visit any websites once the in-browser notification has appeared. A spokesperson for the UK’s biggest ISP said: “If customers do not make a decision, they are unable to continue browsing. The message will remain until the customer makes a decision.”
-
Privacy
-
A federal judge in New Jersey has signed off on the practice of law enforcement using a fake Instagram account in order to become “friends” with a suspect—thus obtaining photos and other information that a person posts to their account.
-
The Tor Project has learned that there may be an attempt to incapacitate our network in the next few days through the seizure of specialized servers in the network called directory authorities. (Directory authorities help Tor clients learn the list of relays that make up the Tor network.) We are taking steps now to ensure the safety of our users, and our system is already built to be redundant so that users maintain anonymity even if the network is attacked. Tor remains safe to use.
-
Many of you by now are probably aware than I run a large exit node
cluster for the Tor network and run a collection of mirrors (also ones
available over hidden services).
Tonight there has been some unusual activity taking place and I have
now lost control of all servers under the ISP and my account has been
suspended. Having reviewed the last available information of the
sensors, the chassis of the servers was opened and an unknown USB
device was plugged in only 30-60 seconds before the connection was
broken. From experience I know this trend of activity is similar to
the protocol of sophisticated law enforcement who carry out a search
and seizure of running servers.
Until I have had the time and information available to review the
situation, I am strongly recommending my mirrors are not used under
any circumstances. If they come back online without a PGP signed
message from myself to further explain the situation, exercise extreme
caution and treat even any items delivered over TLS to be potentially
hostile.
-
Civil Rights
-
Today, 21 December 2014, WikiLeaks releases two classified documents by a previously undisclosed CIA office detailing how to maintain cover while travelling through airports using false ID – including during operations to infiltrate the European Union and the Schengen passport control system. This is the second release within WikiLeaks’ CIA Series, which will continue in the new year.
-
Intellectual Monopolies
-
Copyrights
-
In 2011, police in two countries coordinated to take down a private torrent site that had largely flown under the radar. This week, 3.5 years after the raid, two alleged operators of the site faced a criminal trial in Sweden. Having uploaded no content themselves, will they be held liable for the actions of their users?
Permalink
 Send this to a friend
Send this to a friend
Posted in IRC Logs at 8:42 pm by Dr. Roy Schestowitz
IRC Proceedings: November 30th – December 6th, 2014
IRC Proceedings: December 7th – December 13th, 2014
IRC Proceedings: December 14th – December 20th, 2014
Enter the IRC channels now
Permalink
 Send this to a friend
Send this to a friend
Posted in News Roundup, Site News at 12:30 pm by Dr. Roy Schestowitz

Contents
-
We all know that Hollywood movies are the worst place to see some accurate depiction of anything from real life and that includes computer terminals. Well, there is a solution for that now and we can only hope that some misguided producer will see the new “hollywood” package made for this exact purpose.
Hollywood movie producers invest a lot of time and money in custom interfaces and GUIs that don’t really do anything, but they think they’re nice and interesting on film. Most of the time, someone is hacking away by typing frenetically while windows with crazy stuff open and close. This is why this kind of image is now seared into the public’s consciousness and hacking looks more exciting than in real life. It isn’t.
-
The orders from Chinese banking and military commissions coincided with the trial of domestic computer systems in Siping, a city of 3.4 million people in Jilin province. Other cities and agencies in Jilin will now begin testing whether NeoKylin, a Linux-based operating system from China Standard Software Co., can substitute for Windows and servers made by Inspur can replace IBM’s, the two people familiar with the plan said. The trial will then expand across the country, they said.
-
-
Server
-
The announcement of Rocket by CoreOS was perceived by many to be a direct challenge to Docker, particularly as it came on the eve of DockerCon Europe and threatened to overshadow news coming out at the event. Docker, Inc. CEO Ben Golub was quick to fire back with his ‘initial thoughts on the Rocket announcement’. This piece isn’t about the politics of ecosystems and VC funded startups, which I’ll leave to Colin Humphreys (and note an excellent response from Docker Founder and CTO Solomon Hykes). It also isn’t about managing open source community, which I’ll leave to Matt Asay. Here I want to look at systemd, which lies at the heart of the technical arguments.
-
Kernel Space
-
The x86 platform driver changes for the Linux 3.19 kernel have been submitted and they include some noteworthy improvements for many Linux laptop owners.
-
Intel’s next-generation Skylake processors are starting to take shape with the Linux 3.19 kernel.
Linux 3.19 lands initial Skylake graphics support within the Intel DRM drivers (there’s already initial support on the user-space side too within Mesa) and there’s Skylake MPX support among other Skylake related work that’s been merged for 3.19.
-
Linus announced on Friday night that he’s closing the merge window early for 3.19. Torvalds said that he’s pulling the last of the pull requests on Saturday — related to KBuild and the READ_ONCE split-up — but is planning to then close the merge window.
-
Graphics Stack
-
Julien Cristau of Debian announced the X.Org Server 1.16.3 release on Saturday morning. The primary focus of this release is on correcting the security issues within the GLX, DIX, XV, DRI3, RENDER, and other areas of the xorg-server code-base affected by outstanding security problems.
-
Applications
-
-
-
Instructionals/Technical
-
Games
-
With now having the automated testing capabilities in place for the Linux build of Civilization: Beyond Earth, next week I should have out a large Linux GPU/driver comparison for this popular game.
-
Desktop Environments/WMs
-
K Desktop Environment/KDE SC/Qt
-
As you saw I continue to work on 4.14 branch, in parallel I work on KF5 porting.
-
Each application has a “domain” it was created for. KOrganizer has for instance the calendar domain, and kmail the email domain, and each of those domains can be described with domain objects, which make up the domain model. The domain model of an application is essential, because it is what defines how we can represent the problems of that domain. If Korganizer didn’t have a domain model with attendees to events, we wouldn’t have any way to represent attendees internally, and thus couldn’t develop a feature based on that.
-
nOS Infinity is a Linux distribution based on Ubuntu that uses the KDE desktop environment. It’s built for old and new computers and it’s quite different from what you might expect.
-
GNOME Desktop/GTK
-
-
New Releases
-
SparkyLinux 3.6 Enlightenment19, JWM, Openbox and CLI is out.
ISO images of Sparky 3.6 e19, JWM and Openbox belong to the Base Edition.
-
Arch Family
-
Manjaro 0.8.11 is a Linux distribution based on Arch Linux, which is also 100% compatible with the repositories of the base system. It’s been out for a short time, but developers have already pushed a second major update for it.
-
Red Hat Family
-
The official reply noted that “this report incorrectly classifies expected behavior as a security issue,” through a Red Hat Bulletin released on Wednesday just one day after the report being made public. This was in response to Alert Logic claiming that this Grinch issue may be as large as the previously seen Heartbleed bug, noting that they believe it is a serious design flaw in how Linux handles user permissions.
-
Red Hat, which just reported a profit of $47.9 million (or 26 cents a share) on revenue of $456 million for its third quarter, has managed to pull off a tricky feat: It’s been able to make money off of free, well, open-source, software. (It’s profit for the year-ago quarter was $52 million.)
-
Fedora
-
Fedora is an open source Linux based operating system. As Fedora is free so end users can use it , modify it as per their requirements and distribute it. Fedora Operating system is available for Desktops, Servers and cloud. Fedora project is supported by RedHat. Most of the new softwares and technologies are developed and tested by Redhat in Fedora and then later on these softwares are used in Redhat Stable Versions.
In this post we will discuss Fedora 21 Desktop or workstation (64 bit) Installation Steps with Screenshots. Below are the minimum requirements to install Fedora 21.
-
Debian Family
-
Derivatives
-
The Elive Team is proud to announce the release of the beta version 2.5.0
-
Canonical/Ubuntu
-
Earlier this year, I reported on the forthcoming release of Ubuntu phones. Ubuntu for phones had just hit “release to manufacturer” status and phones were supposed to launch before the end of 2014.
Bad news: The phones clearly won’t be here this year. But good news! Canonical told me they’ll be out in early 2015, after a slight delay to clean up some lingering interface and manufacturing snags.
-
Linux is a dominant player in almost every industry segment, minus one: desktop. We heard Linus Torvalds’ pain when he uttered these words at LinuxCon North America this year, “I still want the desktop”.
-
Marco’s work involves adding an option to always show the Unity menus (in Unity, the menus are currently displayed on mouse over). Furthermore, this option will work with both the regular Appmenu / global menu, displayed on the top Unity panel, as well as LIM (locally integrated menus), displayed in the application titlebar:
-
Just when you thought you couldn’t get anymore Red Hat news, it once again was the talk of the techtown. An interest blog post from Hanno Böck today says quit using NTP if you care about security. Jack M. Germain discusses the work of Open Invention Network and Jamie Watson reviews Debian-derivative Tanglu 2. Dedoimedio.com shares their best distro of 2014 and Ubuntu 15.04 Alpha 1 was released.
-
The first two companies that have been confirmed to release phones with Ubuntu Touch are Meizu and Bq. Until now, only Meizu showed any kind of involvement with Ubuntu Touch and they were the first to announce a launch window. On the other hand, Bq has been silent, but it seems to have been very busy and to be the first one out the door.
-
A Linux kernel regression for Ubuntu 14.10 (Utopic Unicorn) has been identified by Canonical and the developers have issued a patch that should be available through regular channels.
-
Flavours and Variants
-
Lubuntu 15.04 Alpha 1 (Vivid Vervet) has been officially released and it follows its Kubuntu and Ubuntu GNOME brethren. Users can now download and test this latest installment.
-
The Ubuntu GNOME developers have released the first version of the 15.04 branch for their Linux distribution and it looks like this operating system is also going through some interesting changes, just like Ubuntu, although not on the same scale.
-
-
If Android M is for real, the technology would go far beyond its Android Auto initiative announced earlier this year. Android Auto offers Apple CarPlay-like extensions to existing Android apps for customized interactions with a wide variety of IVI navigation and multimedia systems. IVI systems that support Android Auto should begin to appear in cars sometime in 2015.
-
Phones
-
Tizen
-
It’s not news that open source is rolling through many industries like a well-oiled machine, so of course automotive is no exception. Organizations like GENIVI are helping to move this along, by creating specifications for open source platforms that provide a consistent foundation for the use of open source for In-Vehicle Infotainment systems.
-
Android
-
The best thing about Android is that there are lots of choices. The worst thing about Android is that there are lots of choices. There are just too many damn phones to choose from!
-
While there’s no question that the iPhone 6 and iPhone 6 Plus are beautiful smartphones, some might argue that Apple’s 2012 iPhone 5 and last year’s iPhone 5s feature an overall look that is more sleek and sophisticated. Now, imagine that sophisticated design was given harder lines, darker tones and a 5-inch full HD display, and it was built out of titanium and 18k gold instead of aluminum.
-
In 2014, we have seen continued growth for both use and adoption of open source software in the enterprise software market. Cloud takes a big part of that obviously, with project likes Docker and OpenStack who have been in the news frequently. But growth wasn’t limited to increased use and adoption. We also noticed a lot of big names open sourcing their own solutions. Facebook announced a new branch of MySQL built for scalability, NASA released source code for many software projects, GitHub released the Atom text editor under a MIT license, and Google open sourced an email encryption tool and it’s Chrome PDF engine. The biggest news this year when it comes to open sourcing software has been Microsoft with .Net. This list of new open source releases goes on, with companies like LinkedIn, organizations such as DARPA, and more. If this trend continues, we can expect a lot more to be released under an open source license in 2015.
-
CMS
-
Release 4.1 of WordPress came out on Friday so after some work to fit in with the Debian standards, the Debian package 4.1-1 of WordPress will be uploaded shortly. WordPress have also updated their themes with a 14-day early theme called twentyfifteen. This is the default theme for WordPress 4.1 on-wards.
-
BSD
-
FSF/FSFE/GNU/SFLC
-
The Free Software Foundation has now built up a committee to review their “High Priority Projects” list and they’re looking for more feedback from the community.
Nearly ten years ago is when the Free Software Foundation began listing what they viewed as the High Priority Free Software Projects in a list. This list has over time contained some definite high-priority projects related to freeing Java and Adobe PDF support and open graphics drivers to some more obscure projects of high priority like a free version of Oracle Forms, a replacement to OpenDWG libraries for CAD files, automatic transcription software, etc. I’ve personally called out many of the FSF HPP for what they’re worth with my thoughts over the years.
-
-
Project Releases
-
The Calibre eBook reader, editor, and library management software has just reached version 2.13 and the developer has added an important driver and made quite a few fixes and improvements.
-
Public Services/Government
-
The population in Uganda has been growing rapidly. The country now has 35 million people. In order to provide quality services to its citizens and to improve the national competitiveness through administration innovation, the government has adopted free and open source software as the preferred mode of operation for electronic government (e-government) services and platforms.
-
Licensing
-
Almost three years ago, millions of Internet users joined together to defeat the Stop Online Piracy Act (SOPA), a disastrous bill that would have balkanized the Internet in the name of copyright and trademark enforcement. Over the past week, we’ve been tracking a host of revelations about an insidious campaign to accomplish the goals of SOPA by other means. The latest development: Google has filed a federal lawsuit seeking to block enforcement of an overbroad and punitive subpoena seeking an extraordinary quantity of information about the company and its users. The subpoena, Google warns, is based on legal theories that could have disastrous consequences for the open Internet.
-
Openness/Sharing
-
Open Access/Content
-
Librarians have built up quite a reputation for activism in all the right ways. Whether taking a stand against DRM, expanding libraries’ catalogs to include new digital media and art, or embracing indie authors, librarians come off as much more of a hip crowd than you might expect. These stances occasionally put them at odds with some in the community that they serve, perhaps most notably with parents who have pushed for restrictions on internet access within libraries. It gets all the more unfortunate when a subsection of the citizenry sees fit to ramp up the rhetoric against an institution simply attempting to serve the greatest public good. This typically, unfortunately, devolves into the supposed accusation of librarians “defending” the right for visitors to view “pornography.”
-
Better Wi-Fi connectivity, alongside hot drinks and comfier seating, could be the key to saving Britain’s libraries
A government inquiry has called for a “complete reinvigoration” of the UK’s library network, including plans to make the facilities more welcoming by offering free Wi-Fi and hot drinks.
-
Programming
-
The goal is to let developers integrate applications more easily with its managed data analytics service.
-
Open source software theoretically ensures that the best code becomes the most widely shared and used code. But how can open source developers know how many other projects are actually making use of their handiwork? An interesting new tool called Libscore aims to provide an answer — at least for Web developers.
-
As of yesterday, there’s MIPS32R6 and MIPS64R6 support in GCC. The new MIPS R6 CPU architecture support was contributed by Imagination Technologies themselves. MIPS Release 6 features new instructions aimed for enhancing performance for JIT, JavaScript, browsers, PIC for Android, and large workload applications. The MIPS R6 architecture was announced a few months ago and the first products based on the updated MIPS ISA are their new Warrior processors.
-
Standards/Consortia
-
What a brilliant end of the year for ODF, Google have decided to add support for the file type to it’s Drive service. The new update allows users to edit and save documents on Drive and also import ODF files and edit them from Drive. Prior to this you could only import ODF files to the service but you would have to edit download and edit them locally.
-
Salford mayor Ian Stewart has already said he is ‘inclined’ towards favouring a public vote on the issue, with his council voting in favour of a motion calling for residents to have their say
-
Security
-
Hackers have gone after KeyPoint Government Solutions and its main customer, the Office of Personnel Management, is issuing a warning that nearly 50,000 people may have had their information compromised.
An OPM spokeswoman said that the agency has concluded an investigation of the breach and is notifying 48,439 people whose personally identifiable data may have been breached.
The agency is taking the action “out of an abundance of caution,” the spokeswoman said.
-
Earlier this month, a mysterious group that calls itself Guardians of Peace hacked into Sony Pictures Entertainment’s computer systems and began revealing many of the Hollywood studio’s best-kept secrets, from details about unreleased movies to embarrassing emails (notably some racist notes from Sony bigwigs about President Barack Obama’s presumed movie-watching preferences) to the personnel data of employees, including salaries and performance reviews. The Federal Bureau of Investigation now says it has evidence that North Korea was behind the attack, and Sony Pictures pulled its planned release of “The Interview,” a satire targeting that country’s dictator, after the hackers made some ridiculous threats about terrorist violence.
Your reaction to the massive hacking of such a prominent company will depend on whether you’re fluent in information-technology security. If you’re not, you’re probably wondering how in the world this could happen. If you are, you’re aware that this could happen to any company (though it is still amazing that Sony made it so easy).
-
Before I spend another night reading datasheets; would anyone be interested in an OpenHardware random number generator in an full-size SD card format? The idea being you insert the RNG into the SD slot of your laptop, leave it there, and the kernel module just slurps trusted entropy when required.
-
Malware has emerged from war-torn Syria targeting those protesting the rule of ISIS (ISIL, Islamic State, whatever the murderous humanity-hating fanatics are calling themselves these days.)
The trivial Windows spyware, analyzed by University of Toronto internet watchdog Citizen Lab, was sent out in a small number of emails aimed squarely at members of the group Raqqah is being Slaughtered Silently (RSS) – which is holed up deep in ISIS-controlled territory and campaigning against the medieval terror bastards.
-
The offer comes as the FBI formally accused Pyongyang of the attack on Friday and US President Barack Obama promised to “respond proportionally” to the online breach.
-
US President Barack Obama has declared that Sony “made a mistake” in shelving a satirical film about a plot to assassinate North Korea’s leader, and he pledged that the United States would respond “in a place and manner and time that we choose” to the hacking attack on Sony that led to the withdrawal.
-
Defence/Police/Secrecy/Aggression
-
A US drone fired two missiles at a militant hideout in northwestern Pakistan on Saturday, killing at least five Taliban fighters, two security officials said.
-
-
Drone strikes and other “targeted killings” of terrorist and insurgent leaders favoured by the US and supported by Australia can strengthen extremist groups and be counterproductive, according to a secret CIA report published by WikiLeaks.
-
The Taliban hasn’t broken a sweat replacing leaders killed by drones, according to a secret CIA report.
Controversial U.S. drone strikes may be helping rather than hindering the Taliban in Afghanistan, according to a leaked CIA document released by Wikileaks Thursday.
-
-
“The drone exploded during its demonstration at the Yavoriv firing ground at around 09.00 on December 18. The blast fatally wounded a volunteer from Kyiv region, which was in the area [of the explosion],” the head of the media center, Oleksandr Poroniuk, said. The causes of the incident are being established. Law enforcers and members of the military prosecutor’s office are working at the scene.
-
Pakistan suffered the worst terrorist attack of a seven-year Taliban insurgency Tuesday when militants rampaged through an army-run high school in the northern city of Peshawar, killing at least 141 people, mostly students, in what the militants described as revenge for months of airstrikes on their tribal-area strongholds by Pakistan warplanes and CIA drones.
-
Yemen’s transitional government, according to analysts and human rights groups, continues to condone extrajudicial killings of people it could arrest, detains people without due process and turns to tribal law to cover up its mistakes.
-
A federal judge vacated as moot an order that prevented government disclosure of information about the targeted drone strike that killed U.S. citizen Anwar al-Awlaki in 2011.
-
These “targeted” killings are conducted remotely in countries against which we have not declared war. Lethal drone strikes occur without warning, target for death specific individuals who are secretly selected, and are operated remotely by individuals thousands of miles away.
-
Though it was a Friday afternoon, normally a dead zone for media attention, the response was instant and stunning. As had happened five years earlier with the committee’s similarly fought-over report on torture, it became a 24/7 media event. The “revelations” from the report poured out to a stunned nation. There were the CIA’s own figures on the hundreds of children in the backlands of Pakistan and Yemen killed by drone strikes against “terrorists” and “militants.” There were the “double-tap strikes” in which drones returned after initial attacks to go after rescuers of those buried in rubble or to take out the funerals of those previously slain. There were the CIA’s own statistics on the stunning numbers of unknown villagers killed for every significant and known figure targeted and finally taken out (1,147 dead in Pakistan for 41 men specifically targeted). There were the unexpected internal Agency discussions of the imprecision of the robotic weapons always publicly hailed as “surgically precise” (and also of the weakness of much of the intelligence that led them to their targets). There was the joking and commonplace use of dehumanizing language (“bug splat” for those killed) by the teams directing the drones. There were the “signature strikes,” or the targeting of groups of young men of military age about whom nothing specifically was known, and of course there was the raging argument that ensued in the media over the “effectiveness” of it all (including various emails from CIA officials admitting that drone campaigns in Pakistan, Afghanistan, and Yemen had proven to be mechanisms not so much for destroying terrorists as for creating new ones).
-
There are lots of hypocrisies surrounding the recently released executive summary of the Senate Intelligence Committee report on the CIA’s detention and interrogation program. But they pale in comparison to the current Democratic silence about President Barack Obama’s policy of targeted drone assassinations.
-
1) CIA director John Brennan vehemently defends the agency – lauding the interrogators as “patriots” and refusing to call their methods torture;
2) President Obama backs up Brennan (his previous chief counter-terrorism adviser, his choice to head the CIA); and
3) His administration has desisted from filing charges against those responsible for the torture.
-
In other words, according to the CIA, the white South African apartheid government may have fared better against the struggle for equality and justice if it had assassinated Mandela. Governments, including the US, should murder inspirational leaders if they want to defeat insurgencies.
-
The U.S. is prepared to veto a United Nations Security Council proposal that calls for an end to Israel’s occupation of Palestinian lands in 2017.
State Department spokeswoman Jen Psaki said the resolution, offered by Jordan and pushed by Palestinian President Mahmoud Abbas, is unlikely to face an immediate vote.
-
A World War II bomb has been successfully defused in an eastern German city after some 9,700 people were evacuated from the surrounding area and a meeting of a state legislature was interrupted.
-
Former deputy prime minister John Prescott says there’s more to the UK and US “special relationship” than meets the eye
-
Saudi Arabia’s oil chief said in comments published Thursday that there are no links between the kingdom’s decision to oppose production cuts and political objectives – an apparent response to accusations last week from Shiite powerhouse Iran.
Petroleum Minister Ali Naimi was quoted by the official Saudi Press Agency as saying that there are “incorrect information and analyses … linking petroleum decisions with political objectives.”
-
A secret CIA review published recently by WikiLeaks reveals that Israel has been among the least successful countries regarding the targeted killing of opponents, Lebanese newspaper Al-Akhbar reported on Thursday. The review shows that the killings carried out by the US and its ally Israel have been the least successful among a list of eight countries; the American and Israeli authorities usually laud such assassinations.
-
A computer network that the US Central Intelligence Agency began using a decade ago to conduct the kidnap and torture of terrorist suspects has become an integral part of the system now operating drone strikes in the Middle East and Africa.
The means to send ‘above top secret’ intelligence communications around the globe without exposure empowered the CIA’s Rendition and Detention Program to snatch and interrogate suspects in the US ‘war on terror’. The same network system became the principal mechanism behind the intelligence-led “targeted killing” of suspected enemies using drone strikes today.
The technological link between the two sinister programmes, signposted in passing detail by the US Senate Select Committee on Intelligence Study of the Central Intelligence Agency’s Detention and Interrogation Program last week, further confirms that a US military network routed via the UK carried intelligence vital to the US targeted killing programme, and presents evidence that may sway officials deciding whether contractor British Telecommunications Plc should be held to account for building a part of the network used to transmit drone targeting intelligence since 2012.
-
BK: The U.S. launched its disastrous war on Iraq based largely on the false intelligence the CIA produced via torture.This intelligence was, of course, what the neocon cabal, which had a pre-9/11 interest in invading Iraq, wanted. So yes, the CIA was just doing its job, but its job wasn’t, and isn’t, to keep American citizens safe.The torture techniques detailed in the report are horrific to read about. They include beatings and waterboarding and something called “rectal rehydration.” They include sleep deprivation, hideous stress (one detainee was chained to the wall in a standing position for 17 days.) They include threats to harm or murder the detainees’ children or wife or mother. As I say, the Senate Intelligence Committee report makes clear that the information extracted by these techniques had no accuracy, belying all justification of them. But more to the point, torture and murder are utterly immoral acts, which rouse fury and hatred that come back to haunt the perpetrators: the American people.
-
Fox News has plunged itself into the centre of controversy once again for referencing the Sydney siege in an apparent justification for the CIA’s use of “enhanced interrogation”.
-
Wikileaks has released a CIA document from 2009 analyzing the positive and negative effects of strikes against high value targets.
-
Drone strikes and “targeted killings” of terror targets by the United States can be counterproductive and bolster the support of extremist groups, the CIA has admitted in a secret report released by WikiLeaks.
-
-
-
he removal of senior Taliban leaders has had little impact on the organisation, a CIA report released by Wikileaks has said.
The 2009 report analyses “high value targeting” in a number of conflicts – the assassination of senior insurgents.
It said the Taliban’s ability to replace lost leaders has hampered the effectiveness of coalition operations against its leadership.
The CIA would not comment on the leaked documents.
-
-
-
Some time in early or mid-1949 a CIA officer named Bill (his surname is blacked out in the file, which was surfaced by our friend John Kelly back in the early 1990s) asked an outside contractor for input on how to kill people. Requirements included the appearance of an accidental or purely fortuitous terminal experience suffered by the Agency’s victim.
-
President Barack Obama is naming the CIA’s second-ranking official to a top White House national security post.
Obama says Avril Haines is a “model public servant” who is respected across the government. He says that as deputy national security adviser, she will play a critical role in keeping the country save and promoting American interests around the world.
-
Transparency Reporting
-
U.S. military leaders say three top figures from the Islamic State have been killed by U.S. airstrikes, including a military chief and a deputy of Islamic State leader Abu Bakr al-Baghdadi. The news comes as the whistleblowing website WikiLeaks has published an internal CIA document which reveals the agency’s doubts about the effectiveness of such killings. The document, which is from 2009, describes both the positive and negative impacts of assassinating so-called high-value targets. It warns that such operations can “[increase] the level of insurgent support,” “[strengthen] an armed group’s bond with the population,” “[radicalize] an insurgent group’s remaining leaders.” WikiLeaks notes, “After the report was prepared, U.S. drone strike killings rose to an all-time high.”
-
The US policy exposed by Julian Assange and Edward Snowden through the dissemination of classified information gained vital importance for the entire world.
-
The charges against journalist and activist Barrett Brown, accused of threatening an FBI agent, are partially based on his quoting another person’s threat to assassinate the WikiLeaks founder, Julian Assange said.
Brown, 33, whose sentencing was delayed until January on Tuesday, faced federal charges including computer-related crimes, obstruction of justice and publicly threatening an FBI agent performing his duty. He’s now looking at up to eight years in prison for aiding hackers in breaching corporate computers, after pleading guilty in April to being an accessory.
-
Julian Assange wrote in a statement that the case of Dallas journalist Barrett Brown involves him personally and the work of WikiLeaks.
-
A study by the Central Intelligence Agency that evaluated the pros and cons of assassination programs has revealed significant insights into the agency’s thinking about targeted killings, including potential backlash. The study was published by Wikileaks on Thursday.
-
Brown has been in federal custody since his arrest more than two years ago.
-
Rolando “Roly” Sarraff Trujillo was arrested on espionage charges in Cuba in 1995.
-
Finance
-
China’s trade minister proposed more use of China’s currency in settling trade with Russia in the face of a falling rouble to ensure safe and reliable trade, Hong Kong broadcaster Phoenix TV reported on Saturday.
-
If it were not for the fact that the lives of some 45 million people are at stake, Ukrainian national politics could be laughed off as a very sick joke. Any pretenses that the October national elections would bring a semblance of genuine democracy of the sort thousands of ordinary Ukrainians demonstrated for on Maidan Square just one year ago vanished with the announcement by Victoria Nuland’s darling Prime Minister, “Yat” Yatsenyuk, of his new cabinet.
-
PR/AstroTurf/Lobbying
-
Why the phone-hacking affair has left Rupert Murdoch better off
IT MUST all seem like a distant nightmare now. After the revelations of phone-hacking at the News of the World emerged in 2011, Rupert Murdoch was hauled before Parliament, calling it “the most humble day of my life”. Executives and journalists were arrested. The scandal prompted Mr Murdoch’s News Corp to drop a cherished plan to buy out the other investors in BSkyB, a satellite broadcaster (since renamed Sky). Some predicted that the affair, which included the hacking of a murdered schoolgirl’s voicemails, could be Mr Murdoch’s and his firm’s undoing.
-
The research group whose misleading poll question was heavily touted by the media to suggest “growing public support for gun rights” has acknowledged that the question was flawed.
Last week, the Pew Research Center released the results of a survey that asked respondents whether it is more important to “control gun ownership” or to “protect the right of Americans to own guns.” The poll showed increased support for the gun rights answer and a drop in support for regulating guns. The results were reported by numerous media outlets, especially by the conservative press.
-
The Center for Media and Democracy (CMD) had joined the climate change awareness group Forecast the Facts, Credo Action, and others in asking eBay to leave what Reuters called the “controversial political group ALEC” in recent weeks. A Twitterstorm on December 17 was followed by the delivery of a petition containing nearly 100,000 petitions to eBay’s headquarters in San Jose, California on December 18. eBay’s announcement came shortly after.
-
Censorship
-
The Ukraine government has established a department that critics are calling the “Ministry of Truth” — borrowing a term from George Orwell’s classic dystopian novel 1984.
-
Thousands of people have gathered in several Spanish cities to protest against a new ‘Gag Law’ that sets hefty fines for offences such as photographing the police, peaceful disobedience and demonstrating without a permit or outside parliament buildings, banks or strategic installations. The largest protests were in Barcelona, Bilbao and Madrid; others were held in cities including Almeria, Granada and Valencia.
-
Like all cults, Facebook and Scientology have diabolical means of controlling their members. Facebook updated its Terms of Use this past month, in an attempt to clarify its privacy policies. But the pages of information and infographics just serve as a reminder that the social media company basically owns us, and has access to all our most personal information. Yet we are willing participants in this pillaging of our private lives. Being a member of Scientology is all about surrendering one’s power to self-determination. We voluntarily allow Facebook to have more power over our lives than the science fiction cult from the Planet Xenu—and here’s how.
-
-
-
The social network has shut down a page that was set up to rally behind Alexei Navalny, a critic of Vladimir Putin who is about to be sentenced to jail
-
Facebook complied with an official request to ban a page in support of Russia’s leading opposition activist, triggering a wave of censorship allegations.
-
-
-
-
HOWELL RAINES remembers a call from Ari Fleischer not long after the 9/11 attacks on the United States.
Mr. Raines, then the executive editor of The Times, says that Mr. Fleischer, President George W. Bush’s press secretary, made a startling request. He “asked for a promise that we would contact the White House in advance on any national security matter we were reporting.”
-
Privacy
-
If you’re still holding out hope for the preservation of “Internet privacy,” you may need to adjust your ideals a bit. The future of online privacy is cloudy, and policymakers and technology innovators have a weighty task on their hands – one they’re likely to fumble. This is one of the overarching findings of a recent canvassing of more than 2,500 experts by Pew Research Center’s Internet & American Life Project.
-
Judge Jeffrey White heard oral arguments by attorneys from the Electronic Frontier Foundation, which filed the suit, and the government, during a hearing in a federal district court in Oakland, California. The EFF says its suit is the first challenge in public court to the government’s upstream data program, which copies online data from the main cables connecting Internet networks around the world.
-
-
The National Security Agency is illegally searching and seizing Americans’ Internet communications, privacy advocates told a federal judge at a hearing on Friday.
-
On Friday, privacy advocates at the Electronic Frontier Foundation (EFF) are attempting a new strategy in their six-year-old lawsuit against the National Security Agency. Filed in 2008, Jewel v. NSA is a suit calling for the end of the surveillance of millions of AT&T customers’ internet traffic and emails. Despite evidence provided by an AT&T whistle-blower, the US district court, under pressure from the federal government defendants, has delayed and avoided judgment, suggesting that the case raises issues too secret for the federal courts even to rule upon and too important for national security to shut down anyway.
-
An international survey shows a growing demand for privacy and Internet access.
-
In its ongoing public relations struggle, the NSA will soon have to defend itself in court. A digital rights group, Electronic Frontier Foundation (EFF) is bringing forth a motion against the National Security Agency on Friday over the agency’s Internet data collection program.
-
The Electronic Frontier Foundation says the government’s upstream data collection violates the Fourth Amendment
-
A digital rights group in the United States plans to argue in federal court this week that the National Security Agency’s internet surveillance operations violate the US Constitution’s ban against unlawful searches and seizures.
-
Google is already beginning to lay the groundwork for another push next year to rein in government spying ahead of a crucial summer deadline to some of the National Security Agency’s surveillance authority.
-
Millions of Internet users have changed their Internet behavior and are doing more to keep their own personal data secure from possible surveillance, according to a survey from the Center for International Governance Innovation (CIGI). The survey revealed 64 percent of respondents have increased privacy worries over just one year ago, as the NSA, GCHQ, and other organized surveillance programs target Web users.
-
Nearly 700 million people worldwide have taken steps to protect their privacy from NSA surveillance, according to an international internet security survey
-
In November, a study released by the Canadian Centre for International Governance claimed that while 60% of internet users had heard of NSA whistleblower Edward Snowden, only 39% of those people had taken additional steps to protect their online privacy as a result.
-
Recent revelations about government-backed surveillance have prompted millions of people to do more to keep their data private, suggests a survey.
Many people now regularly change passwords or avoid certain websites or apps, said the Centre for International Governance Innovation (CIGI).
It also found that 64% of the 23,000 people questioned are more worried about their privacy than a year ago.
-
While the media was busy lining up to congratulate Obama for lawlessly granting amnesty to millions of illegal immigrants and cuddling up to one of the six state sponsors of terrorism in the world, Congress passed legislation that, according to one House Republican, “grants the executive branch virtually unlimited access to the communications of every American.” Republican leadership in the House inserted language into the Intelligence Authorization bill at the very last minute which includes a phrase to allow for “the acquisition, retention, and dissemination” of U.S. phone and Internet data.
-
Last week, the government quietly released a new cache of court filings and orders from late 2006 and early 2007 that together reveal a watershed moment in the government’s effort to secretly expand its authority to conduct surveillance on American soil—without ever asking Congress or the public. Instead, the government once again asked the Foreign Intelligence Surveillance Court (FISC) to belatedly bless certain aspects of the President’s Surveillance Program, which was initiated by President Bush without judicial or legislative approval in 2001.
-
Disclosures from the vast trove of NSA documents obtained by Edward Snowden were first published in The Guardian exactly 560 days ago, and it’s worth asking ourselves whether we have gained anything from the revelations since then. The answer to that question increasingly seems clear: no.
-
-
The trio responsible for breaking last year’s NSA spying scandal have been honored for defending human rights. Prominent Germans praised the work of Edward Snowden, journalist Glenn Greenwald and filmmaker Laura Poitras.
-
The government argued by way of contrast that allowing Snowden onto German soil would hamper international relationships, notably with the United States. It would also corner the government in Berlin: extradite Snowden, or face the unpleasant transatlantic music.
-
-
A panel investigating the CIA’s search of a computer network used by Senate staff will not recommend disciplining the agency officials involved in the incident, according to the New York Times.
The review panel is looking into the search by agency officials of staffers from the Senate intelligence committee who were investigating the CIA’s use of torture in interrogations of detainees after the 9/11 attacks on the US.
The Times, citing current and former government officials, said the panel was likely to fault the CIA for missteps. But the newspaper said the decision not to recommend anyone for disciplinary action was likely to anger members of the intelligence committee, who have accused the agency of interfering with its investigation of agency wrongdoing.
-
A bill filed today in Missouri would not only support efforts to turn off NSA’s water in Utah….
-
-
For global insurance firms, cyberattacks have become the most threatening of all emerging risks, according to a survey conducted recently by Guy Carpenter & Co., the risk and reinsurance specialists. Over the past two years, hackers have infiltrated major airlines, energy companies and defense firms, among many other businesses.
-
-
-
German researchers have discovered security flaws that could let hackers, spies and criminals listen to private phone calls and intercept text messages on a potentially massive scale – even when cellular networks are using the most advanced encryption now available.
-
Civil Rights
-
Matt DeHart faces a very depressing and lonely Christmas in jail this year for reasons that are at best down to an extreme bureaucratic SNAFU, and at worst (and more likely) down to collusion between the Canadian and American authorities to stop the whistleblower talking to the press.
-
People who knew Lacy don’t think he committed suicide. Others are unsure what to believe. But many here say the possibility that Lacy, a popular high school senior who moved easily between black and white social circles, was the victim of a racially motivated killing demands more investigation.
-
While most journalists report official government statements, and cite only approving voices, there are a few who quote dissenters. We should pay attention to these few, considering the long list of government lies attributing evil deeds to designated foes. Learning from experience is the beginning of strength.
-
Conservatives who usually hail individual liberties are leading the televised defense of the U.S. government’s torture of terror suspects, including many who were completely innocent. But some conservatives are troubled by this knee-jerk defense of the Bush administration, as Independent Institute’s Ivan Eland explains.
-
Americans like to think of themselves as the ultimate “good guys” and anyone who gets in their way as a “bad guy.” Under this theory of U.S. “exceptionalism,” whatever “we” do must be moral or at least morally defensible, from sponsoring coups around the world to torture, as William Blum describes.
-
American exceptionalism has always maintained a moral imperative. The conduct of the world’s foremost liberal democracy is guaranteed by a fierce commitment to liberty and the security of individual rights.
-
The world has often seemed on fire of late. There has been a horrific massacre in a Pakistani school. A cyber-hacking apparently organised by North Korea, which might come to look very familiar in years to come. The Sydney siege. The barbarians of Isis unbowed. Ebola continuing to spool out. Russia’s economy tumbling.
So it’s well to note a milestone of huge positive significance when it occurs. The United States’ detente with Cuba, announced all of a sudden by the presidents of both countries late last week, was such a moment.
-
Pyongyang warns of ‘serious’ consequences if Washington rejects a probe that it believes will prove North Korea had nothing to do with the cyberattack. An unidentified Foreign Ministry spokesman said North Korea knows how to prove it’s not responsible for the hacking, so the U.S. must accept its proposal for the joint investigation.
-
As the world awaited the US Senate report on the CIA’s detention and interrogation programme under the George W Bush administration, there was very little introspection in Europe. As if European countries had nothing to do with what went on in the hunt for al-Qaida in the years after 9/11. In fact, many of America’s European allies were deeply involved in the CIA programme. And they have managed to stay very quiet about it. Could this change now?
-
Residents of the Chagos Islands who were kicked out of their homes in the 1960s by the British government to make way for a US military base fear they may never return home, despite politicians’ promises, RT’s Polly Boiko reports.
“You have to go back where you belong. That’s me, as a Chagossian,” says Bernard Nourrice, a former resident of Diego Garcia, one of the Chagos Islands, now a closed US military base.
Diego Garcia has recently made headlines after the CIA torture report revealed the US used the so-called “black sites” based in other countries for detention. Though the report did not mention the names of the locations, it’s been alleged Diego Garcia could be one such site.
-
America’s reputation for cognitive dissonance is being tested by the Senate report documenting the U.S. government’s torture of detainees and the fact that nothing is happening to those responsible. Ex-CIA analyst Ray McGovern says the nation must choose between crossing the Delaware or the Rubicon.
-
When you are in a radical movement, it’s wise to assume that the person arguing for the most extreme action is an agent provocateur. The question for opponents of fracking is on whose behalf are the agents provocateurs provoking.
Nato and the Romanian and Lithuanian governments have alleged that Russia is urging on opponents of the new technology. Not because Putin gives a damn about global warming, but because he wants Europe to remain dependent on Russian gas. They have no conclusive proof. But the prominence the Kremlin’s apparatchik journalists on RT, the state-funded television channel, give to fracking protests suggests Russian agents may be seeking to manipulate the green movement.
-
On Tuesday the sentencing of Barrett Brown, a US journalist, was delayed for a second time and postponed until January 22 of next year. At the hearing the prosecution dramatically presented 500 pages of new evidence, seemingly unrelated to the charges to which Brown was awaiting sentencing. The only explanation for this is that it was a clumsy attempt by the prosecution to provide the judge with a basis for awarding a maximum sentence at the January hearing. But the behaviour of the prosecution at the hearing revealed several important ambiguities that can only be described as (unintended) prosecutional sabotage. (See also video at end.)
-
More than 70 years after South Carolina sent a 14-year-old black boy to the electric chair in the killings of two white girls in a segregated mill town, a judge threw out the conviction, saying the state committed a great injustice.
George Stinney was arrested, convicted of murder in a one-day trial and executed in 1944 – all in the span of about three months and without an appeal. The speed in which the state meted out justice against the youngest person executed in the United States in the 20th century was shocking and extremely unfair, Circuit Judge Carmen Mullen wrote in her ruling Wednesday.
-
Police are killing unarmed teens, and demanding apologies from critics. Here’s the only way they will ever change
-
Footage has emerged of a plain-clothed New York police officer punching a teenage boy repeatedly in the back as he was being handcuffed by four other police on Monday.
Witnesses claim the suspect was just 12. The NYPD says he is actually 16 years old and has a history of arrests.
The case has been referred to the Internal Affairs Bureau for investigation and the NYPD is saying very little about the details of the arrest.
Scene caused outrage on the streets of the Lower East Side of Manhattan on Monday afternoon. The NYPD has come under increasing scrutiny for its use of force in the wake of the Eric Garner case.
-
If you thought nothing could top Cleveland police union chief Jeff Follmer’s brazen defense of police authority – “the nation needs to realize, when we tell you to do something, do it” – you need to read this story about New York Patrolmen’s Benevolent Association head Patrick Lynch’s meltdown in the wake of criticism over the NYPD’s killing of Eric Garner in Staten Island.
-
It seems like there are so many police-behaving-badly stories that have come out recently, it’s no longer all that noteworthy. Mind you, I don’t know that the policing situation is generally actually getting worse, as it might seem, or if there is just simply a greater willingness to shine a spotlight in some very uncomfortable places within our own society. That said, what does remain interesting is watching how police around the country react to this spotlight. Watching the unfortunate reactions to athletes showing support for protesters, for instance, would be hysterical if it weren’t so sad. Those stories appear to indicate that some within law enforcement appear to think that protecting some members of the population is a task with which they can be selective.
-
A 27-year-old woman is accused of slapping a 72-year-old woman who denied her friend request on Facebook.
The Tampa Bay Times reports Rachel Anne Hayes became angry on Wednesday when the woman said the Facebook name she uses is inappropriate.
-
Ex-cops who claim VIP paedophile investigations were axed in a cover-up are to hand a dossier to Britain’s most senior police officer.
They have agreed to compile formal statements on what they knew of operations being shut down.
The file will be presented to Met Commissioner Sir Bernard Hogan-Howe.
-
Chief Inspector Jukka Salminen says that the Finnish Police use guns very infrequently on a comparative scale. Last year in Finland, the police fired their weapons in an official capacity a total of six times.
-
Parts of the massive Mall of America were temporarily closed Saturday following a demonstration against racial profiling and police brutality at one of the nation’s largest shopping centers. A large crowd gathered in the Bloomington, Minnesota, mall rotunda just before 2 p.m. local time and staged a “die-in,” despite warnings from mall officials that the protest was not permitted and could lead to arrests.
-
“Join us at the Mall of America in solidarity with #BlackLivesMatter,” read a Facebook invitation to protest a year of police brutality this afternoon at the massive Bloomington, Minn., shopping center that bills itself as “the place for fun in your life.”
-
The group Black Lives Matter Minneapolis had more than 3,000 people confirm on Facebook that they would attend. Official crowd estimates weren’t immediately available, but pictures posted to social media by local news organizations showed the rotunda was full. Organizer Mica Grimm estimated about 3,000 people participated.
-
Tamir Rice and Eric Garner aren’t anomalies. Cops aren’t properly trained and now routinely use maximum force
-
The NYPD should know better. In August, it handed a $125,000 settlement to a man it arrested for recording officers performing a stop-and-frisk. A month earlier, the ACLU sued the NYPD in federal court to prevent the NYPD from arresting the people recording them. It’s even clearly stated in the NYPD policy manual that “bystanders are allowed to film [officers] as long as they’re not interfering with the officers’ duties and/or police operations.”
-
A human rights group in Berlin, Germany, has filed a criminal complaint against the architects of the George W. Bush administration’s torture program. The European Center for Constitutional and Human Rights has accused former Bush administration officials, including CIA Director George Tenet and Defense Secretary Donald Rumsfeld, of war crimes, and called for an immediate investigation by a German prosecutor. The move follows the release of a Senate report on CIA torture which includes the case of a German citizen, Khalid El-Masri, who was captured by CIA agents in 2004 due to mistaken identity and tortured at a secret prison in Afghanistan. So far, no one involved in the CIA torture program has been charged with a crime — except the whistleblower John Kiriakou, who exposed it. We speak to Michael Ratner, president emeritus of the Center for Constitutional Rights and chairman of the European Center for Constitutional and Human Rights, and longtime defense attorney Martin Garbus.
-
-
-
-
President Obama is unlikely to go against the will of Congress and unilaterally shutter the prison in Guantánamo Bay, Cuba, lawmakers from both parties predict.
“I don’t know that he can,” Sen. Tim Kaine (D-Va.) said. “I know that there are enough congressional restrictions on the books that limit his options.”
-
A CIA prisoner whose treatment set the torture template in the agency’s notorious Salt Pit jail outside Kabul, and another known as a “ghost prisoner” – held in such secrecy that for years even his name was classified information – have disappeared into Afghanistan’s prison system, where they are once more at risk of torture.
-
When reports about abuse at the Abu Ghraib prison first came out more than a decade ago, Michael Peppard started researching every account of mistreatment and torture he could find. He soon noticed a pattern missed by most journalists: American interrogators were using the religious faith of Muslim detainees as a weapon to abuse them.
-
The debate over the CIA interrogation program pits critics who insist illegal torture took place against defenders who say the treatment of prisoners was legal. These defenders cite guidance that the spy agency got from the Bush Administration. Former CIA Director Michael Hayden phrased it this way: “It needs be said that on multiple occasions all of the techniques were determined lawful by the Department of Justice and judged appropriate for the circumstances.”
-
John Yoo, the former Justice Department lawyer who authored a series of notorious memos cited by the Bush administration to justify the torture of terrorism detainees, acknowledged on Sunday that the CIA may have broken the law.
-
-
-
Thousands of images depicting U.S. soldiers abusing prisoners in Iraq and Afghanistan may be released this week following the Senate’s ‘torture report’.
-
The logic that torture is a “stain” on U.S. history is the heart of the problem, since it blocks an honest reading of whatever “values” Washington actually stands for.
-
Released in 1975 and 1976, the Church Commission report revealed that the CIA had been secretly trying to assassinate foreign leaders, including Fidel Castro, for years. It’s a murky chapter in American history that’s worth looking back at this week, as America prepares for an epochal shift in its relationship with the Cuban leader and Cuba itself.
-
-
The First Minister has backed calls for a judicial inquiry into the possibility of Scottish and British involvement in the torture or rendition of terror suspects.
The UK Government is facing pressure for a judge-led inquiry after new revelations in a US Senate report on CIA interrogation.
-
-
-
-
Thailand’s prime minister says his government had no knowledge of a secret location inside the country where the CIA is said to have waterboarded top al-Qaida operatives in 2002.
Prime Minister Prayut Chan-ocha was responding to the so-called “torture report” released by the Senate Intelligence Committee earlier this month that detailed the treatment of terrorism suspects at secret locations — black sites– around the world.
-
The controversy over the CIA torture report has moved on to calls for the UK government to be open about its own involvement. The arguments have also been widened to include other elements of CIA activities, especially in Iraq.
-
-
The CIA tortured al-Qaeda suspects because it wanted evidence that Saddam Hussein was linked to 9/11 in order to justify the invasion of Iraq in 2003. The agency was under intense pressure from the White House and senior figures in the Bush administration to extract confessions confirming co-operation between the Iraqi leader and al-Qaeda, although no significant evidence was ever found.
-
The horrific stories of CIA-sponsored torture that aren’t in the Senate report.
-
The fear that the US has lost its moral compass is vastly exaggerated, for the simple reason that the US – at least in the Arab World – never possessed this moral legitimacy in the first place.
-
Torture methods employed by the CIA under the guise of its “enhanced interrogation techniques” program can be traced back — through personnel and decades of research — to human experiments designed to induce the subjugation of prisoners through use of isolation, sleep and sensory deprivation, psychoactive drugs and other means, according to details contained in the Senate Select Committee on Intelligence report, a summary of which was released last week.
-
“Being an accomplice to torture is a war crime,” says MFÍK Chair Þórhildur Sunna Sævarsdóttir
-
In July 2004, despite growing internal concerns about the CIA’s brutal interrogation methods, senior members of George W. Bush’s national security team gave the agency permission to employ the harsh tactics against an al-Qaida facilitator whom the agency suspected was linked to a plot to disrupt the upcoming presidential election.
-
In March 2004, a Boeing 737, registration number N313P, lifted off from Baghdad International Airport with two prisoners on board – captured by the SAS after a shoot-out in the city.
-
Romania allowed the CIA to use a number of sites on its territory, a former head of the country’s intelligence confessed. He added that Bucharest’s bid to join NATO at the time prevented it from asking the US about the purposes of the sites.
-
A top official from Romania has for the first time confirmed that the CIA had “at least” one prison in the country.
Ioan Talpes, the former head of the country’s intelligence service said the CIA had “centres” in Romania, including a transit camp or compound, where prisoners were kept before being moved to other locations. He is the first Romanian official to confirm the information in the CIA torture report last week, which stated the existence of at least one “black site” in which prisoners were held and probably tortured.
-
Abu Zubaydah has now been held incommunicado for 12 years without trial. This is gross injustice
-
The British parliament’s intelligence and security committee (ISC) has started to question intelligence agencies over whether they requested redactions in the explosive US Senate report on CIA torture.
The ISC has already been investigating broader allegations of UK agencies’ involvement in torture or mistreatment.
-
-
-
-
-
-
Internet/Net Neutrality
-
The Associated Whistleblowing Press released portions of draft text proposed by the United States for the Trade in Services Agreement (TISA) this week, revealing some alarming provisions that indicate how tech companies have been involved in influencing a secret international deal. The language of the leaked treaty shows provisions that could impact privacy online, and net neutrality—with no public consultation or opportunities for open debate. What is dispiriting is some of the language of these Internet regulations almost certainly comes from tech companies, who have joined the many other lobbyists fighting for their special interests behind closed doors.
-
DRM
-
Cautioning the tech-savvy people about the universal snooping propaganda of the technology giants, president of Free Software Foundation Richard Stallman spoke about the unholy nexus of the states with the corporates, in the city.
Stallman, a reputed cyberspace activist and a champion of the free software movement, lashed out at the malpractices of technology giants like Apple and Microsoft, who, according to him, take the users hostage using ‘digital handcuffs’.
Advocating freedom of computing and the Internet, he said that the apparent technology providers often exercise ‘Orwellian Justice’, which peeps into the privacy of users. “Amazon’s Kindle, the e-reader application, is infamous for remotely erasing the purchased copies of the book ‘1984’,” said Stallman.
-
Intellectual Monopolies
-
The TTIP negotiations are in trouble. After 18 months of talks, the EU and US have precious little to show for all their jetting to and fro across the Atlantic. And external factors such as the imminent Presidential race in the US means that time is running out to get the deal signed and sealed. Against that background, there are signs of a (rather feeble) attempt to put “rocket boosters” under the negotiations, as David Cameron likes to phrase it – although he forgets that rocket boosters can also explode on take-off, destroying their cargo completely.
-
Of course, this is just one legal opinion, and doubtless the European Commission would beg to differ. But it does indicate that the very ambition of CETA — and therefore also TAFTA/TTIP, which is very similar in this respect — may be its downfall. By seeking to move “behind the borders”, tackling “non-tariff barriers” that are actually regulations protecting health, safety, the environment, etc., these agreements may interfere with too many core functions of how a democracy works, and be struck down by the courts as a result.
-
Copyrights
-
As you may have heard, the Pirate Bay was raided and is down as I write this post. The closure of the Pirate Bay has generated a lot of discussions online, and many people have been looking for alternative torrenting sites. Fortunately, there was an interesting thread on Reddit about that very topic and one redditor was kind enough to post a list of alternative torrent sites:
-
To get the same results in a post-SOPA world, MPAA has hired some of the nation’s most well-connected lawyers. The project is spearheaded by Thomas Perrelli, a Jenner & Block partner and former Obama Administration lawyer. Perrelli has given attorneys general (AGs) across the country their talking points, suggesting realistic “asks” prior to key meetings with Google. Frustrated with a lack of results, Perrelli and top MPAA lawyers then authorized an “expanded Goliath strategy” in which they would push the AGs to move beyond mere letter writing. Instead, they would seek full-bore investigations against Google.
-
Say what you will about the copyright industry, but it certainly doesn’t give up. No matter how many times a bad idea is fought off, sooner or later, it comes back again. The best example of this is probably WIPO’s Broadcasting Treaty, which Techdirt has been covereing for a decade: in 2004, 2005, 2008, 2011 and 2013.
Permalink
 Send this to a friend
Send this to a friend

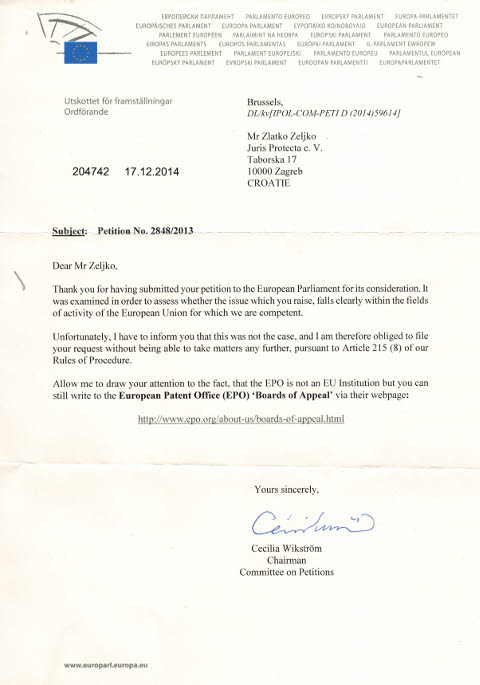
















 Content is available under CC-BY-SA
Content is available under CC-BY-SA