04.02.14
Posted in Microsoft, Red Hat, Security, Windows at 6:27 am by Dr. Roy Schestowitz

Summary: Criticism of Red Hat’s increasing proximity to some of the very same bits of proprietary software which are accompanied by back doors (for the NSA)
THE DANGERS of Microsoft are very real, as a former foe of Microsoft, Novell, helped prove. Five years ago Red Hat consented to playing an active part in Microsoft VM hosts, despite knowing (even back then) about Microsoft’s relationship with the NSA, which meant that VMs running RHEL would be accessible (to the NSA) from the back door, Microsoft Windows.
There are many back doors in Windows and therefore in Hyper-V, which sits on top of Windows (back doors further down the stack). Microsoft tells the NSA about these back doors. To give the latest example of back doors, see this new report [2] which says: “Nearly 30 days after reports of a zero-day flaw being exploited in the wild, Microsoft will finally patch this critical vulnerability.”
Relying on Microsoft for technology means that one should also expect and accept back doors. A reader showed us this new article, claiming that “Mono [is] infecting Android,” but it’s not just Android. Even Red Hat is now making such mistakes, in addition to hiring from Microsoft for management of virtualisation. Based on [2,3], Red Hat now accommodates Microsoft .NET applications, despite them being proprietary and potential back doors. A week or so ago some speculated that Microsoft might buy Red Hat (one day) [4,5] and yesterday we found the article “Why Microsoft Will Pick Off Red Hat” (logic of investors, not technical people).
Microsoft is now knowingly abandoning hundreds of millions of Windows users, leaving them with permanent back doors [6,7], so why should Red Hat trust Microsoft .NET applications or anything that comes from Microsoft, including Hyper-V? Articles like [8-10] remind us that in GNU/Linux the main flaw is human error (not changing default passwords or not applying patches, which Red Hat is making easier to apply without any downtime [11]).
The bottom line is, Red Hat’s relationship with the NSA withstanding, it oughtn’t connect too much to Microsoft components like .NET and Hyper-V because these constitute back doors that jeopardise security of GNU/Linux users. █
Related/contextual items from the news:
-
-
-
On Wednesday, Working with Uhuru Software, Red Hat is now incorporate a rival Microsoft product – .NET – to its three-year-old OpenShift platform-as-a-service. Really? Red Hat even published a blog to explain what’s going on to those who might find the concept a bit unbelievable.
Chris Morgan, the OpenShift Partner Ecosystem Technical Director for Red Hat, wrote the blog – and even he acknowledged the incredulity of it all that something from Microsoft, which for years has been an enemy of Red Hat, Linux and Open Source, would be incorporated into OpenShift.
-
-
Today brings two new reviews. Jesse Smith reviews Linux Mint Debian Edition 201403 in today’s Distrowatch Weekly and Jamie Watson posts his latest hands-on. Steven J. Vaughan-Nichols says folks don’t care about operating systems anymore. Matt Hartley has a few suggestions for those ready to graduate from Ubuntu. All this and more in tonight’s Linux news review.
Jesse Smith tested the latest LMDE in this week’s Distrowatch Weekly. He found a few bugs but Smith says it “lives up to its description” of having “rough edges.” With all its “nasty surprises” Smith suggests folks just stick with the Ubuntu-based version of Mint. But see his full review for all the details.
-
A decade ago, Microsoft kicked off SDL, or Security Development Lifecycle, a now-widely-adopted process designed to bake security into software, and began building what has become an unmatched reputation in how a vendor writes more secure code, keeps customers informed about security issues, and backs that up with regular patches.
-
-
-
News headlines screaming that yet another Microsoft Windows vulnerability has been discovered, is in the wild or has just been patched are two a penny. Such has it ever been. News headlines declaring that a ‘major security problem’ has been found with Linux are a different kettle of fish. So when reports of an attack that could circumvent verification of X.509 security certificates, and by so doing bypass both secure sockets layer (SSL) and Transport Layer Security (TLS) website protection, people sat up and took notice. Warnings have appeared that recount how the vulnerability can impact upon Debian, Red Hat and Ubuntu distributions. Red Hat itself issued an advisory warning that “GnuTLS did not correctly handle certain errors that could occur during the verification of an X.509 certificate, causing it to incorrectly report a successful verification… An attacker could use this flaw to create a specially crafted certificate that could be accepted by GnuTLS as valid.” In all, at least 200 operating systems actually use GnuTLS when it comes to implementing SSL and TLS and the knock-on effect could mean that web applications and email alike are vulnerable to attack. And it’s all Linux’s fault. Or is it?
-
“We are seeing a lot of crypto bugs surfacing lately because these libraries are suddenly getting a lot of review thanks to Snowden’s revelations,” suggested blogger Chris Traver. “I think one has to separate the crypto bugs from others because they are occurring in a different context. “From what I have read about gnutls, though, it seems to me that this is probably the tip of the iceberg.”
-
In upstream development news, the kernel team here at Red Hat has been working on a dynamic kernel patching project called kpatch for several months. At long last, the project has reached a point where we feel it’s ready for a wider audience and are very excited to announce that we’ve released the kpatch code under GPLv2.
Permalink
 Send this to a friend
Send this to a friend
Posted in News Roundup at 5:28 am by Dr. Roy Schestowitz
Google Relationship
-
-
-
Red Hat has announced a new collaboration with Google that will enable Red Hat customers to move eligible Red Hat Enterprise Linux subscriptions to Google Compute Engine using Red Hat Cloud Access. Google joined the Red Hat Certified Cloud Provider program in November 2013.
Google announced the public availability of the Google Compute Engine platform earlier this year. Compute Engine placed the company in direct competition with Amazon Web Services (AWS), and represented a strong step into the Infrastructure-as-a-Service space. Now, Google becomes only the second Red Hat Certified Cloud Provider to earn designation as a Red Hat Cloud Access-enabled partner.
Finance
-
“While we remain cautious around the maturing Unix-to-Linux migration cycle, the strength of the fiscal Q3 bounce back suggests that the combination of core Linux and JBoss (middleware), some contribution from RHEV (virtualization) and storage, and the halo effect of Red Hat’s aggressive move to become ‘Red Hat of OpenStack’ are sustaining mid-teens growth,” Turits wrote.
-
Red Hat reported its full-year fiscal 2014 earnings late Thursday, showing continued momentum for the Linux server operating system business leader. As Red Hat looks for future growth, the open-source OpenStack cloud platform is front and center.
-
Shares of Red Hat (RHT) today closed down $3.90, or almost 7%, at $52.23, after the company yesterday afternoon reported fiscal Q4 revenue and earnings per share that topped analysts’ expectations, but forecast this quarter, and the full year’s results below consensus.
-
Red Hat is out with a slew of news this week. As Susan covered earlier, the company reported better-than-expected quarterly results, aided by strong subscription growth for its Linux operating system, but also forecast full-year profit following below average analyst estimates. Along with that news, the company announced the Red Hat Enterprise Virtualization 3.4 Beta, which builds on the recent Red Hat Enterprise Virtualization 3.3 release, and aims to automate enterprise virtualization tasks while providing integration with OpenStack.
Virtualisation
-
The new oVirt 3.4 release improves storage, high-availability and networking features.
The open-source oVirt virtualization project debuted its 3.4 release on March 27, providing users with new features to meet the expanding needs of workload virtualization.
-
Red Hat begins beta test of RHEV 3.4, an enhanced KVM virtual machine designed to continue simplifying and automating enterprise virtualization tasks while providing an on-ramp and a seamless integration with OpenStack.
People
-
Whitehurst is an avid advocate for open source software as a catalyst for business innovation.
-
“I am to technical people what a groupie is to a rock band,” he laughs. “In other words, what’s the point of being in a rock band if you don’t have people to appreciate the music?”
-
As an OpenDaylight project board member and the technical director of Software-Defined Networking (SDN) at Red Hat, Chris Wright knows what it takes to launch a successful open source, collaborative project. He’ll share some of what he’s learned through his experience with OpenDaylight in his keynote presentation at Collaboration Summit, March 26-28 in Napa. Here he gives us a preview of the talk and shares his predictions on which industries are primed for disruption through collaborative development.
Development
-
-
If you’re a system administrator, what you really want is a stable operating system with long-term support, such as Red Hat Enterprise Linux (RHEL). If you’re a system programmer, what you really want is the latest and greatest program. What to do!
-
The next version of Red Hat’s Software Collections package includes Apache httpd and Nginx Web servers, Ruby 2.0, and NoSQL database MongoDB. They are all part of version 1.1 of Software Collections, a beta of which can now be downloaded, Red Hat said in a blog post Thursday.
-
One of Red Hat Enterprise Linux’s big selling points has been its consistency, in the operating system itself and the software packaged with it. Red Hat goes so far as to offer application certification — now with Docker support — to ensure the software running on top of RHEL behaves as expected.
-
Red Hat is out with its latest Sofware Collections package, arriving at version 1.1, and it is embracing Apache httpd and Nginx Web servers, Ruby 2.0, and NoSQL database MongoDB, among other previously unseen offerings. As Infoworld has noted: “One of Red Hat Enterprise Linux’s big selling points has been its consistency, in the operating system itself and the software packaged with it. Red Hat goes so far as to offer application certification — now with Docker support — to ensure the software running on top of RHEL behaves as expected. But what about developers who want to step outside the lines, so to speak, and run something a little more cutting-edge?”
-
Insiders have publicly bet against Red Hat’s platform-as-a-service, but I say it will stand by OpenShift without regret.
-
-
Bad Behaviour
-
Matthew Garrett, a former Red Hat employee who has gained something of a public profile, suggested that Piston had got itself into Red Hat’s bad books by competing against it for a contract – and winning.
Docker
-
Containers aren’t quite virtual machines, but with recent advances in Linux, they can do many of the same jobs as a VM while using far less memory.
-
-
-
The other is an open source tool called Docker. Docker bundles applications into self-sufficient units called “containers.” These can be easily moved from server to server, and they include everything the application needs to run. Unlike a virtual machine — which recreates the entire operating system — Docker containers are can take advantage of the host server’s operating system and other software, even though the containers are separated from each other. Basically, it’s another way of improving the efficiency of your infrastructure.
-
“Containerization has emerged as an essential solution for sys-admins and developers, as it provides a flexible way to build, scale and deploy applications, and reduces the time and expense of cloud infrastructure,” said Al Hilwa, program director, application development software at IDC. “Docker is emerging as a standard for containerization, driving innovation among developers, sys-admins, and DevOps alike.”
-
-
-
Since we first wrote about Docker last August, the open source container project has advanced in numerous ways. Not only did the company behind it officially shed its original dotCloud name and put Docker at the forefront of its focus, but it also raised $15 million in funding and announced partnerships with the likes of Rackspace, OpenStack, Red Hat and Fedora.
-
Open source developer adds container certification for Enterprise Linux apps, aims to improve workload portability and ease maintenance burden.
-
Docker is nothing more than a handy container. But for a lot of use cases, it’s opening up amazing new possibilities for making development and deployment work together more closely than ever. It’s an open source project designed to make it easy to create lightweight, portable, self-sufficient containers of an application, allowing that containerized application to run just as easily on a massively scaled cloud as it does on a developer’s laptop. For projects like OpenStack, it’s a new way of deploying applications as an alternative to (or on top of) a virtual machine, while potentially using fewer system resources in the process.
-
Red Hat’s application certification program is nominally about ensuring that third-party applications and app platforms run reliably on Red Hat Enterprise Linux.
The newest candidate for certification, though, isn’t an application per se. Rather, it’s an application technology that stormed the Linux world and quickly became a major part of its landscape: containerization, which allows apps to be packaged to run almost anywhere with minimal muss or fuss.
-
-
“One of the most-requested features is private repos. Say you’re working on a project that you want to share with the world but is not yet ready for prime time. Now you can push your work-in-progress to a private repo on docker.io and invite only specific collaborators to pull from and push to it. When you’re ready, you can make your private repo public, and it’ll automatically be indexed and publicly searchable.”
Fedora
-
-
I saw on the Fedora Xfce mailing list today that it looks like xfdashboardand xfce4-whiskermenu-plugin are coming to the Fedora Xfce spin’s ISO, if not as default choices at least as things you can add to your desktop after the fact.
-
Docker is a hot topic in the Linux world at the moment and I decided to try out the new trusted build process. Long story short, you put your Dockerfile along with any additional content into your GitHub repository, link your GitHub account with Docker, and then fire off a build. The Docker index labels it as “trusted” since it was build from source files in your repository.
-
It’s been a relatively quiet week. Snapshot support in virt-manager, automatic latest-code repos with dgroc, Fedora Plasma KDE-based product proposal, and Fedora Atomic Initiative.
-
We have very positive brand. When I go to a conference and talk about Fedora, obviously there are some complaints about specific things, but overall, people are happy with us. We have a very strong user and developer community — people are using Fedora in production in the real world, sometimes in amazing and crazy ways (for large-scale web hosting, as a platform for very high-stakes rapid stock trading, as the desktop for a not-small law firm, as the basis for the most popular CS course at Harvard…).
-
Fedora 21
-
The Fedora Engineering and Steering committee convened today for talking about another round of Fedora 21 features. One week after approving a bunch of features for this Fedora Linux update due out in late 2014, there’s more features added to the list.
-
-
Last week there were a great number of interesting features approved for the Fedora 21 release due out in October~November. This week there isn’t quite as many items that were on the FESCo agenda, but there’s still some interesting work that hopes to make it into this next Fedora Linux release. The approved items at yesterday’s FESCo meeting were
-
Profiles would cover things like TLS/SSL and DTLS versioning, ciphersuite selection and ordering, certificate and key exchange parameters including minimum key length, acceptable elliptic curve (ECDH or ECDSA for example), signature hash functions, and TLS options like safe renegotiation.
Misc.
-
Red Hat (RHT) has highlighted the transition from Unix platforms to open source Red Hat Enterprise Linux (RHEL) in awarding the 2014 Red Hat Certified Professional of the Year Award. The recognition goes this year to Jorge Juarez Acevedo of Banco Azteca, who oversaw the bank’s migration from Sun Solaris, HP UX and AIX servers to RHEL.
-
Red Hat did this because it believes there are three very different ways that 70 to 80 percent people tend to use Red Hat Linux distros. Businesses that want a lot of support and device and staff certification pay for Red Hat Enterprise Linux (RHEL). Fedora is for users, often developers who use the latest and greatest Linux and open-source software and want to be ahead of the curve. CentOS is for Linux experts who can handle their own support and want a stable platform.
Permalink
 Send this to a friend
Send this to a friend
Posted in News Roundup at 5:13 am by Dr. Roy Schestowitz
Enlightenment
-
With the latest Git development work for the Elementary tool-kit and library, applications can run directly from the DRM driver interface without any display server / compositor / window manager. Applications can be created to run in DRM and by setting the ELM_ENGINE=drm option the apps will run in a standalone mode without anything else underneath.
-
Current support work is being done to enable client-side applications (as opposed to making a Wayland compositor itself – that is a future plan). Currently EFL applications that use the lower-level Ecore-Evas and higher level Elementary API’s will work and display correctly in Wayland, handle input, resizing and moving. Client-side frames are already provided. Both Shared-memory buffers AND EGL/OpenGL-ES2 buffers are supported. The Shared-memory buffers are purely CPU-rendered, meaning that they will work with or without OpenGL hardware acceleration support. They are fast and usable. The OpenGL-ES2 display is fully accelerated with all primitives being rendered by OpenGL (Hardware acceleration) and already work fully due to a long history of supporting this under X11 and other embedded EGL/OpenGL-ES2 environments.
KDE
-
April 1, 2014. Today KDE makes available the first beta of Frameworks 5. This release is part of a series of releases leading up to the final version planned for June 2014 following the previous alpha last month. This release marks the freeze of source incompatible changes and the introduction of the Frameworks 5 Porting Aids.
-
And KDE knows what happens when you alienate a group of users since the moment when the anger of some people over KDE 4 lead to the first prominent fork of KDE software, the Trinity Desktop Environment.
-
-
Today KDE released updates for its Applications and Development Platform, the fourth in a series of monthly stabilization updates to the 4.12 series. This release also includes an updated Plasma Workspaces 4.11.8. Both releases contain only bugfixes and translation updates, providing a safe and pleasant update for everyone.
-
-
Part of the KDE PIM group is meeting over this weekend in Barcelona in the spacious BlueSystems offices, hacking on all sorts of things. Me and David Edmundson took the oportunity to do some super huge changes to our KPeople library that are needed and as the library is in its dawn, it’s better to do it sooner than later. These are all internal and boring changes, but one of the changes we’ve been working on here is really cool and worth mentioning.
-
The CD and DVD era is coming to an end and developers don’t really bother to innovate when it comes to applications that deal with this media. There are quite a few apps that are capable of writing to DVDs available for the Linux platform, and K3B is one of the best.
-
The fourth beta of digiKam Software Collection 4.0 is now available for photographers interested in testing out this popular KDE software component.
-
digiKam team is proud to announce the fourth beta release of digiKam Software Collection 4.0.0.
-
-
Qt3D is the Qt component that adds 3D support to Qt Quick for easily integrating 3D functionality. Qt3D has been in development for some time and was going to be an “essential” module to Qt 5.0 before being moved to just an add-on as part of Nokia’s Qt changes prior to selling it to Digia. Qt3D offers up a lot of potential for 3D user-interfaces and applications, but hasn’t seen too much work recently — the last time we got to mention it was when talking about OpenGL taking on a greater role within Qt in late 2012.
-
The KDE Project developers have just released the first Release Candidate of Applications and Platform 4.13, and it’s all about fixes and improvements.
“KDE has released the release candidate of the 4.13 versions of Applications and Development Platform. With API, dependency and feature freezes in place, the focus is now on fixing bugs and further polishing,” said the KDE developers.
-
“The Calligra team has released version 2.8.1, the first of the bugfix releases of the Calligra Suite, and Calligra Active in the 2.8 series. This release contains a few important bug fixes to 2.8.0 and we recommend everybody to update,” reads the official announcement.
GNOME
-
-
-
Announcing her departure, Karen said: “Working as the GNOME Foundation Executive Director has been one of the highlights of my career.” She also spoke of the achievements during her time as Executive Director: “I’ve helped to recruit two new advisory board members… and we have run the last three years in the black. We’ve held some successful funding campaigns, particularly around privacy. We have a mind-blowingly fantastic Board of Directors, and the Engagement team is doing amazing work. The GNOME.Asia team is strong, and we’ve got an influx of people, more so than I’ve seen in some time.”
-
Zukitwo, a beautiful theme designed for GNOME 3.12 that makes use of the GTK2 engine Murrine and the GTK2 pixbuf engine, is now at version 2014.03.29.
The Zukitwo theme was updated shortly after the release of GNOME 3.12 and it’s probably the first theme to support the new version of GNOME. A lot of other themes will probably follow soon but, coincidentally, Zukitwo is also one of the best ones around.
-
-
Our dedication towards Wayland has pushed us to build a cleaner architecture overall. What used to be a proliferation of X-specific video and input drivers is mostly culminating in centralized, standardized code. For input, we have libinput, which we’re using from Weston, mutter, and Xorg as well. What used to be a collection of chipset-specific video plugins for doing accelerated rendering have now been replaced by glamor, a credible chipset-independent acceleration architecture. What used to be large monolithic components heavily tied to Xorg and the Xorg input and video architectures have now been split out into separate, easily-reusable libraries with separate, easily-maintainable codebases. New, experimental features can be prototyped faster than ever before.
-
-
One of the great things about Linux distributions is the customization. In contrast, an operating system like Windows 8 is rather limited. Sure, you can change some colors, wallpapers and sounds, but pretty much, it is what it is. What you see is what you get. That is probably fine for most people, however, Linux users are not most people.
-
Itching to get your hands on the latest goodies from Gnome? Look no further… If you’d like to see the project’s latest efforts, including getting the best look at the latest Gnome core apps (Music, Weather, Maps, Videos), Matthias Clasen has a special gift for you. He’s made a special live CD containing a complete Gnome 3.12 atop Fedora 20.
-
-
Review When the GNOME 3.x desktop arrived it was, frankly, unusable. It wasn’t so much the radical departure from past desktop environments, as the fact that essential things did not work properly or, more frustratingly, had been deemed unnecessary.
-
THE GNOME PROJECT has released Gnome 3.12, the latest version of the heavyweight Linux desktop environment, which adds support for better displays and faster startup times.
-
-
Earlier today GNOME 3.12 has been released, bringing major new features, several redesigned programs and three new applications: Logs, Sound Recorder and Polari.
Misc.
Permalink
 Send this to a friend
Send this to a friend
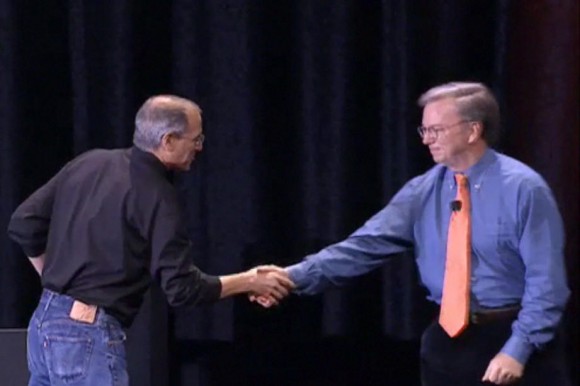
Posted in Apple, Google at 4:25 am by Dr. Roy Schestowitz
Gentlemen’s attack on workers
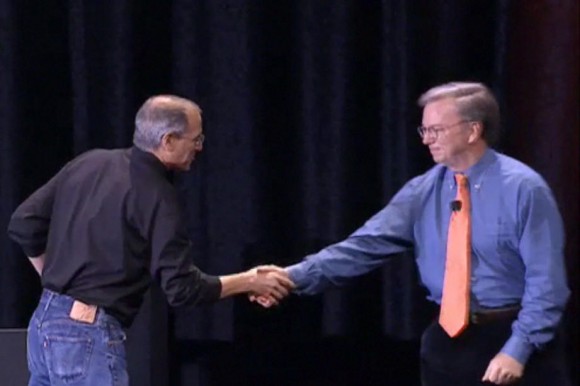
Summary: Details of correspondence between Jobs and Schmidt reveal how deep the price-fixing over workers (fixing the salaries lower) really goes
WE recently learned how Google and Apple had screwed engineers and drove their wages down by colluding. We posted some news links about it. Well, now there are unsealed documents showing us sociopaths at work.
Apple is an undisputed king of evil, but watch Google’s Schmidt acting not much better than Steve Jobs, who is laughing at the firing of staff (guess who’s fired in Hell right now). To quote some background to this: “In early March, 2007, as Google was expanding fast and furiously, one of its recruiters from the “Google.com Engineering” group made a career-ending mistake: She cold-contacted an Apple engineer by email, violating the secret and illegal non-solicitation compact that her boss, Eric Schmidt, had agreed with Apple’s Steve Jobs.
“What happened next is just one of many specific examples of how people’s lives were impacted by the Techtopus wage-theft cartel that was taken down by the Department of Justice antitrust division, and is currently being litigated in a landmark class action lawsuit.
“The Google recruiter’s email—in which she identified herself as “a Recruiter for the ‘Google.com Engineering’ team formerly known as the ‘Site Reliability Engineering’ team”— was sent out on the morning of March 7, 2007.”
Seeing how those companies have colluded and the executives never sent to prison (let alone put on trial) helps us remember that we live in a society where corporations are above the law and white-collar business crimes are so commonplace that we take them for granted (banks are a good example of it). Watch this other news report where iFixit boss Wiens is quote as saying: “They [Apple] have done everything they can to put these guys [third-party repairers] out of business.”
Also mind this new article which floats Microsoft lobbyist Florian Müller‘s old FUD, saying that “Apple wants Samsung to pony up $40 per smartphone for patents.”
At this stage, to be absolutely frank, defending Google from Apple’s aggressive litigation and Steve Jobs' thermonuclear delusions seems like an exercise in futility. Google is starting to do evil not just in patent practice and law; the company which was once hailed as the best place to work with is not an enemy of IT workers. Just ask Tim Bray (a manager in Android) why he quit Google earlier this year. █
Permalink
 Send this to a friend
Send this to a friend
Posted in Google, Patents at 4:03 am by Dr. Roy Schestowitz
Don’t do lawyers, Google

Summary: The British press names companies which are promoting software patents in the United States and Google is one of them
WE WARNED ABOUT this years ago. Rather than fight for people’s interests when it comes to patents, Google hired some of the same people who fight for themselves and against people’s interests (making themselves necessary through patent battles).
How unfortunate.
Now that SCOTUS is looking into software patents (Joe Mullin is distracting from the real issue by focusing on patent trolls, as usual, except when he takes this other angle) we have a real chance to redeem software developers from greedy business monopolists and their guardians, the lawyers. According to this report, however, Google is among those who argue for software patents. Having HP in there is not surprising given the company’s history of patent PR. It is definitely not surprising to see Microsoft and IBM there; they are the leading and biggest proponents of software patents. The report says that SCOTUS “will hear from a consortium of technology companies today that have weighed in over software patents.
“Later today, nine US Supreme Court Justices will sit for one hour of argument by representatives from companies including Google, IBM, Microsoft and HP.
“The software patent standards that the companies are seeking vary, however they are all calling for tightening patent law to protect software implementation in their field.
“Suzanna Michel, senior patent consel for Google said in a statement to Bloomberg, “The fact that we have not policed this patentability requirement and have allowed the issuance of a lot of abstract, overbroad patents for doing business on the Internet — those patents have fueled this litigation.””
Google has a “senior patent counsel” (turns out it’s a former FTC official which AOL describes as one of “the commission’s top intellectual property officials” and whose education background confirms to be a laywer) and according to this report Google is now part of the problem, making the USPTO even more developers-hostile. Having read the original article, it is a little unclear whether Google actively promotes software patents (Michel speaks about business methods), but given Google’s track record of applying for and buying software patents — a trend we severely suffer from and have criticised — Google can no longer oppose software patents with a straight face. The press now claims that Google is actively harboring such patents. It’s the first time we see this. The author, Chris Merriman, cites this report from Greg Stohr and Susan Decker.
“Well, They can’t hide,” wrote Mr. Bosson from the FFII (Sweden), “Microsoft’s Amicus Brief is quite defensive for sw-patents, using EPO-style arguments to protect them.”
He quotes Microsoft, Adobe and HP as saying: “Software makes computing technology work” (so does silicon!).
“Only by looking at the each claim as a Whole,” is also what they say. “Just like EPO makes software patents OK,” Bosson remarks.
HP and Microsoft both did some nefarious things in Europe, as we have covered here in Techrights, so let’s not be misled by news that some HP laptops may come with GNU/Linux (in the UK) [1,2]. HP is definitely not a friend of Free software based on these policies; as for Google, it seems to be drifting away in its own trajectory. █
Related/contextual items from the news:
-
While anyone living in China or India can walk into a store and buy an Ubuntu laptop off the shelves, those of us in Europe and the US find hunting down brand-name notebooks loaded with Linux a bit of a hassle.
-
The HP notebook – priced at £219.99 and available at the end of April – will be the first computer of its kind to come pre-installed with the free operating system from Linux.
Permalink
 Send this to a friend
Send this to a friend
Posted in Dell, GNU/Linux, Microsoft, Windows, Wine at 3:29 am by Dr. Roy Schestowitz
Long-sighted FUD strategy

Summary: Commentary about Microsoft’s attempts to make GNU/Linux look like it’s its own property, thanks in part to broken patent law in the United States
YEARS AGO, shortly after Novell and Microsoft revealed that they had signed a patent deal that involved Wine, we hypothetised that Microsoft was perhaps trying to keep Wine under patent threats. Amusingly enough, “Chinese People Try To Patent Wine On ARM,” according to Phoronix. One must wonder how Microsoft feels about it.
For those who think that Microsoft has finished extorting companies, look no further than this Dell deal where “[t]he companies did not provide specific information on which products the agreement will apply to” (or how much — if anything at all — gets paid).
We long ago called for a boycott of Dell, immediately after Microsoft pretty much took this dying company under its wing. Appropriately enough, Muktware is now contradicting its own report (which we criticised) in the comments, insisting that maybe a few pennies are paid to Microsoft by Dell (or nothing at all) and that this is more of a publicity stunt, trying to make Chrome OS and Android seem expensive and dangerous. At the time we also wrote about Verizon joining OIN and other factions of the Linux world, demonstrating that unlike Dell, many companies are now taking a stand for GNU/Linux, not against it (as Dell did). █
Permalink
 Send this to a friend
Send this to a friend
Posted in GNU/Linux, Ubuntu at 3:09 am by Dr. Roy Schestowitz
Summary: Canonical did the right thing by removing a controversial behaviour which was facilitating remote user profiling by Amazon, demonstrating yet again that users’ feedback counts
Our coverage regarding Ubuntu's departure from Amazon search in Dash (by default, in future versions) was followed by a lot of articles in general news sites [1] and a lot of blogs or GNU/Linux-oriented news sites which say “it seems that the online search paradigm in Unity is about to end.” Actually, this is pretty much confirmed now. Back in the days when Ubuntu had Mono (we lobbied hard to remove it, by default) and Ubuntu was about to have a Yahoo (Microsoft) search bar we found that Canonical does listen to its users; it’s just that when it takes action accordingly (corrective action) it never admits that it is due to users’ pressure. The bottom line though, Canonical listens. Just before Christmas of 2012 I contacted Stallman and asked him to address the issue of Amazon spyware, whereupon he wrote an article and started to tackle this issue (in his public talks too). He called it “malware”, but I advised him to call it “spyware” instead. 16 months later Canonical took action and a lot of people are exceedingly happy about it. Pressure from users acted as a moral compass, or a regulator. This is the power of Free software. We no longer rely on derivatives of Ubuntu (none of which had this behaviour) to give Canonical a run for the money.
I can happily install Ubuntu again. The weak attempts [2] to describe the end of Windows XP support as a “Bad for Linux and Open Source” [3] don’t quite correspond to what I am seeing. At this moment, after setting up Puppet to mass-remove Amazon from search in Dash (upon request), I know of a company (client at work) that is right now moving hundreds of desktops from Windows XP to Ubuntu (due to XP EOL). Let’s hope this is one example of many. Let’s also hope that Canonical keeps taking users’ needs seriously. It is apparent that even large companies did not like Amazon search in Dash; it’s not just to do with a bunch of opinionated Free software proponents. █
Related/contextual items from the news:
-
-
Christopher Tozzi wrote, “The sad reality is that everybody needs to run a Windows app now and then” in an article about the increasing difficulty of virtualizing that other OS on a GNU/Linux system. He’s right about the RAM/CPU/storage burdens of that other OS increasing but he’s wrong that this is bad for GNU/Linux and FLOSS.
-
Permalink
 Send this to a friend
Send this to a friend
04.01.14
Posted in News Roundup at 9:09 am by Dr. Roy Schestowitz
GCHQ
-
-
The NSA and GCHQ hacked into the systems of three German satellite communication providers, according to the latest leaks from the files of Edward Snowden, fugitive ex-NSA sysadmin.
-
-
Huawei
-
-
China’s Huawei Technologies Co Ltd “maintained calm” and operated “business as usual” after media reports saying the U.S. accessed servers at the telecom giant’s Shenzhen headquarters, acting Chief Executive Eric Xu said on Monday.
-
American cloud companies stand to lose billions of dollars in business because of Edward Snowden’s NSA revelations, and non-U.S. companies are already preparing to pick up the slack.
Snowden and Greenwald
-
Although the title of his talk was framed as a question, “Edward Snowden: Patriot or Villain?” — there really is no doubt that Ray McGovern, a former CIA analyst turned political activist, considers Snowden a patriot.
-
-
Staged ‘Leaks’ (Washington Post)
-
Reeling from the leak of classified data, NSA officials have anticipated future leaks by sometimes announcing them to the media preemptively, a minimization tactic according to one of the journalists still holding the intel agency’s documents.
-
A couple weeks ago, we learned from leaked documents that the NSA has the capability to record an entire country’s calls, texts, and email in real time. That’s a hell of a capability, and those documents revealed that it was being used in one country. Now, thanks to a retired NSA leader, we know which country that is: Iraq.
-
The entire article is a weak (and grossly transparent) attempt to recast General Keith Alexander’s legacy — and thus it seems that Inglis, Alexander and the NSA have no problem at all revealing the details of its capabilities in Iraq when the entire purpose in doing so is an attempt to show how good Alexander was for the NSA. Rest assured, however, had the same bit of information come out from one of the reporters with access to the Snowden documents, the NSA and all its defenders would be screaming as loud as possible about how the publication of such information would cost lives and create immense damage to American interests while aiding our enemies. Yet, apparently, it’s all fine and dandy to reveal such information… when it’s part of the effort to canonize the NSA retired leader.
-
The former head of the NSA, General Keith Alexander, has claimed numerous times that Edward Snowden’s leaks about the NSA’s vast spying programs on innocent American citizens and overseas allies has put the U.S. at serious risk.
‘Reform’
-
One of the expected concessions to civil society is the promise to leave records at the telephone companies, so that the government would allegedly be able to obtain them only in an emergency situation. But in the cold light of the day, records will still be kept. So, what could the ‘metadata’ –information on personal phone calls, claimed to contain no names or content – reveal to the NSA or just to the people who have access to them?
-
A proposal that would require telecom companies to store phone records and make them easily accessible to the U.S. government may not be an insurmountable IT challenge, analysts say. But should that proposal become law, the way companies choose to implement the needed technology raises a number of questions about how that data will be transmitted and secured, and what steps telecoms will take to protect customer privacy.
-
A few plans are now on the table. There is the USA Freedom Act (Leahy-Sensenbrenner bill), the House Intelligence Committee Bill and the President’s own proposal. The latter has yet to find legislative form. President Obama’s proposal involves allowing phone companies to retain their databases of records in standardised, interoperable format. The focus on storage will shift from government agencies to telephony companies. The NSA would, in obtaining access, have to seek an order from the Foreign Intelligence Surveillance Court. In turn, the FISC would have to be satisfied that the records pertained to a person connected with a terrorist organisation.
-
Ron Wyden, the senator who is a leading voice in attempts to rein in the National Security Agency, has urged President Barack Obama to order an immediate halt to the bulk collection of domestic telephone metadata records.
-
Gen. Keith Alexander, the head of the US high-profile National Security Agency, stepped down from his post Friday, amid turmoil at the besieged spy agency.
-
Some other proposals to eliminate bulk data collection, but still offer the same sort of data on potential terrorists and their phone calls have now surfaced. One of the plans is offered by the House Permanent Select Committee on Intelligence (HPSCI) and backed by Obama. It would require a new authority to be created that would duplicate the core capability of the NSA program without having to collect bulk data.
-
Senate intelligence committee Chairman Dianne Feinstein said she supports requiring court approval for all searches of U.S. telephone records, setting the stage for a legislative fight over how to rein in the powers of the National Security Agency.
Satire
Response From Business
-
The good news for lawyers worried about maintaining their duty of confidentiality is that there are tools and safeguards to help them. In a session entitled “N.S.A.y What? Firm and Client Data Security & Encryption in the Age of Monitoring” held at ABA Techshow on Friday, Sensei Enterprises vice president John Simek and Oracle Corporation’s Chris Ries provided tips on gadgets and best practices for lawyers to use if they wish to avoid the NSA’s massive net.
-
-
A survey of 1,000 business leaders from around the world has found that many are questioning their reliance on “cloud computing” in favour of more secure forms of data storage as the whistleblower’s revelations continue to reverberate.
Toward Real NSA Reform
-
This month, the Utah State Records Committee ruled that the City of Bluffdale must release water records pertaining to the massive NSA data center located there.
-
-
Indeed, we have gone a long way down the road of violating American’s basic civil rights, as most recently revealed by whistleblower Edward Snowden who exposed the National Security Agency’s massive spy program, which Judge Richard J. Leon ruled Dec. 16, 2013, a violation of the Fourth Amendment to the U.S. Constitution and “almost-Orwellian.” This egregious violation of the privacy rights of American citizens has prompted Freedom Watch to file for class action certification in its epic lawsuit against the NSA, the first of its kind, in order to open it up to all the Americans whose constitutional rights have been defiled. The new class action suit expands the allegations of constitutional violations to include the NSA’s collection of Internet metadata, social media and its spying on overseas phone calls under its so-called PRISM program.
RSA
-
-
Security industry pioneer RSA adopted not just one but two encryption tools developed by the U.S. National Security Agency, greatly increasing the spy agency’s ability to eavesdrop on some Internet communications, according to a team of academic researchers.
Privacy
-
TO keep an eye on his child via his smartphone, Marc Gilbert installed Internet-connected video baby monitors in his home in Houston. One evening, Gilbert heard a stranger’s voice bellowing obscenities from the monitor. He disconnected the device after realizing that it had been hacked.
PRISM
-
Bruce Schneier: “At SXSW earlier this month, CEO Eric Schmidt tried to reassure the audience by saying that he was ‘pretty sure that information within Google is now safe from any government’s prying eyes.’ A more accurate statement might be, ‘Your data is safe from governments, except for the ways we don’t know about and the ways we cannot tell you about. And, of course, we still have complete access to it all, and can sell it at will to whomever we want.’”
-
Back Doors
-
Technology that remotely makes a stolen smartphone useless could save American consumers up to US$2.6 billion per year if it is implemented widely and leads to a reduction in theft of phones, according to a new report.
Torture
-
-
CIA got DOJ to authorize “water dousing”
-
-
For years, the CIA has been feuding with the Senate Intelligence Committee over its report on Bush-era “enhanced interrogation techniques,” and now we know why. While the 6,300-page report remains classified, on Monday U.S. officials described its contents in detail to the Washington Post. The report concludes that the CIA routinely misled members of Congress and the public by suggesting detainees gave up key information due to the use of those brutal techniques, when they had actually talked before the interrogation. “The CIA described [its program] repeatedly both to the Department of Justice and eventually to Congress as getting unique, otherwise unobtainable intelligence that helped disrupt terrorist plots and save thousands of lives,” said one U.S. official. “Was that actually true? The answer is no.”
-
Sources have told the Associated Press (watch out for another round of phone record-snatching, guys!) that the Senate Intelligence Committee report at the center of a fight between the committee and the CIA confirms what many observers knew or suspected: Waterboarding and harsh interrogation techniques did not provide any useful information to catch Osama bin Laden. In every case where the CIA used torture and claimed it helped, there were other explanations as to where they got the information.
-
Intelligence committee finds methods such as waterboarding did not produce any crucial evidence in hunt for al-Qaida leader, aides say
-
-
-
A report by the Senate Intelligence Committee concludes that the CIA misled the government and the public about aspects of its brutal interrogation program for years – concealing details about the severity of its methods, overstating the significance of plots and prisoners, and taking credit for critical pieces of intelligence that detainees had in fact surrendered before they were subjected to harsh techniques.
-
The CIA repeatedly misled the US government over the severity and effectiveness of its interrogation methods, the Washington Post reports.
A long-awaited US Senate report said that the CIA used secret “black sites” to interrogate prisoners using techniques not previously acknowledged.
These included dunking suspects in icy water and smashing a prisoner’s head against a wall.
Drones
-
The Defence Ministry refused on Monday to share details of CIA chief’s visit to Pakistan with the Senate Foreign Affairs Committee.
The committee had asked for details of the visit of CIA Director John Brennan to Pakistan in the last week of February for meetings with Army Chief Gen Raheel Sharif and ISI Director General Lt Gen Zaheerul Islam.
-
-
There are many other arenas where we could explore the tension between proclaimed individual values and the contradiction of policies which emanate from the White House. The one I wish to focus on is the use of drones – unmanned aerial vehicles – now becoming the go-to strategy for fighting “the war on terror”, even as that name has now fallen out of favor.
-
-
-
Drone missiles may have prompted outcry from international human rights groups and controversy in the media, but unmanned air vehicles could be on the verge of being upstaged by a new weapon on the block: Lethal Autonomous Robotics (LARs). This emerging breed of technology will be able to select a target, aim and fire with no intervention from human beings beyond programming and deployment. War could be about to get a lot cheaper, a lot less bloody… and a lot more frequent.
-
The drone assassination campaigns are one device by which state policy knowingly endangers security. The same is true of murderous special-forces operations. And of the invasion of Iraq, which sharply increased terror in the West, confirming the predictions of British and American intelligence.
-
Armed drones, more than any other weapons system, need international regulation because their very nature makes it easier to stealthily wage war. Since the use of drones can cancel out the need for boots on the ground, they can be used to target countries even when the attacker has not declared war on them. Pakistan, along with Yemen, has most suffered from this new kind of war that drones facilitate and so it is no surprise that we have consistently taken the lead at international forums to have the drone war declared illegal and the use of the weapon be strictly regulated by the UN.
-
What would you do if you witnessed someone killing innocent people? Would you be brave enough to do something to make them stop? We all hope we would be that brave. But if that “someone” is our government and the weapons are missiles and unmanned aerial drones, it seems that our answer is different.
-
The political and economic foundation of the United States is built on the corpses of legal lynching, or “lynch law”. Without the genocide and enslavement of Black and indigenous peoples, the US capitalist class could not have amassed its profits, wealth, or power. Following the passage of the 13th Amendment that supposedly ended Black chattel slavery at the close of the Civil War, the US capitalist class moved quickly to reorganize the capitalist economy so newly “freed” Blacks would remain enslaved. Convict-leasing, sharecropping, and legalized segregation ensured Black exploitation and white power. These brutal forms of exploitation were kept intact by white terrorism in the form of lynching.
Civil Rights
-
-
People are angry over Albuquerque police’s involvement in 37 shootings, 23 of them fatal, since 2010. Critics say that is far too many for a department serving a city of about 555,000.
-
Robert H. Richards IV does not work. He doesn’t have to. The great-grandson of Irénée du Pont, the chemical magnate who provided much of the financial backing to a failed effort to defeat Franklin Delano Roosevelt during the 1930s, Richards lives off a trust fund in a 5,800 square foot mansion he bought for $1.8 million. When he is not staying in his mansion, he might be found in his beach home “in the exclusive North Shores neighborhood near Rehoboth Beach.”
-
After a demonstration in Madrid on Saturday night, seven photographers were assaulted, beaten and injured by police as they tried to cover an arrest.
War
-
-
Academy Award-winning documentary filmmaker Errol Morris joins us to talk about his new film, “The Unknown Known,” based on 33 hours of interviews with former Defense Secretary Donald Rumsfeld. The title refers to an infamous press briefing in 2002 when Rumsfeld faced questions from reporters about the lack of evidence of Iraqi weapons of mass destruction. “The Unknown Known” is Morris’ 10th documentary feature. He won a Best Documentary Oscar for his film “The Fog of War: Eleven Lessons from the Life of Robert S. McNamara.” His other films include “Standard Operating Procedure,” about alleged U.S. torture of terror suspects in Abu Ghraib prison, and “The Thin Blue Line,” about the wrongful conviction of Randall Adams for the murder of a Dallas policeman. The release of “The Unknown Known” comes in a month marking 11 years since the U.S. invaded Iraq, leaving an estimated half a million Iraqis dead, along with at least 4,400 American troops.
-
The Journal leaves out one other parallel with Vietnam: war crimes. The Pakistan army is responsible for disappearances, unlawful detention, extrajudicial killing, bombardment of villages, and mass displacement of Pakistan’s tribal peoples..
-
A Facebook meme argues that Americans are pretty two-faced when it comes to Russia’s recent annexation of Crimea.
The meme says, “22 Countries Invaded by the U.S. in 20 Years. Russia Does It and Everyone Loses Their Mind,” illustrating its point with a photograph of Heath Ledger’s Joker character from Batman movie The Dark Knight.
A reader asked us to check this claim, so we did. Fortunately, the post that accompanied the meme listed the nations that had been “invaded,” along with the years of the purported invasion.
Intervention
-
-
Guess which country held its ‘first free election in decades’ and which held a ‘bogus’ and ‘illegal’ referendum under military occupation.
Permalink
 Send this to a friend
Send this to a friend
« Previous Page — « Previous entries « Previous Page · Next Page » Next entries » — Next Page »





























 Content is available under CC-BY-SA
Content is available under CC-BY-SA