06.23.13
Posted in Patents at 12:30 am by Dr. Roy Schestowitz
Obama’s virtual interview from the White House (over Google+/NSA Hangout)

Summary: On opportunities of reaching President Obama or other White House staff one should calibrate the debate over patents to benefit the public, not large corporations (which want small/conventional trolls marginalised and nothing else changed)
The White House said it would look into patent trolls [1, 2, 3, 4], tackling one strand of the issues incurred by software patents. The investigation is commencing now:
Patent trolls have hit Main Street this year and anger about their demands has bubbled up to Washington.
Today, the Federal Trade Commission (FTC) is expected to announce that it will open an investigation into “patent trolls,” a derogatory term for companies that engage in no business activities aside from suing over patents. The investigation will be announced at a conference by FTC chairwoman Edith Ramirez, according to a report this morning in The New York Times. The investigation into trolls, which the FTC calls “patent assertion entities” or PAEs, will complement other anti-troll government actions this year, like President Obama’s report on patent issues and the five anti-patent-troll bills introduced so far in Congress this year.
This was also covered in British sites:
THE UNITED STATES Federal Trade Commission (FTC) will look into ridiculous but disruptive software patents and the shadowy entities that hold them.
The FTC was asked to look at patent trolls by several members of Congress. A letter signed by 19 Congress members and addressed to FTC chair Edith Ramirez said that patent trolls are useless, get in the way, slow down innovation and extract money from more deserving firms.
“As Members of Congress, we are closely following the troubling practices carried out by patent assertion entities, commonly known as patent trolls throughout the country. We are most concerned about practices that target end users who are the downstream users of technology,” the letter read.
What is needed is a reform nullifying software patents, but for the time being we need to highlight for the White House the biggest scams in existence. This should be handled as a criminal thing, using existing laws like RICO Act, it’s not merely about changing policy to marginalise classic patent trolls. They should consider Microsoft’s “natahanm” (Nathan Myhrvold), Bill Gates’ close friend, whom he financially helped to get the pyramid scheme called Intellectual Ventures started. This pyramid scheme and racketeering operation is now suing Android/Linux, with CNET correctly pointing out that it is not the first time. Josh Lowensohn says: “The controversial Bellevue, Wash.-based company that’s made headlines for accumulating a massive trove of software and design patents, sued Motorola Mobility in the U.S. District Court for the Southern District of Florida on Wednesday.”
“So it’s what we call exponential, we are at about 40,000 software patents being granted each year which is a lot considering that just about 10 years ago, it was about 10,000 patents and even in 1990, it was just 5,000 software patents a year…”
–Deborah NicholsonSoftware and design patents. That’s right. See the pattern yet? Therein lie many of the real issues. It’s about scope, too.
Meanwhile, since we’re on the subject of scope, the numbers we saw before were echoed in this new OIN interview. Deborah Nicholson says: “So it’s what we call exponential, we are at about 40,000 software patents being granted each year which is a lot considering that just about 10 years ago, it was about 10,000 patents and even in 1990, it was just 5,000 software patents a year, so it’s a very scary kind off-the-chart number.”
The OIN is not doing what’s right; it continuously says it wants to improve patent “quality” or stop “bad” software patents. Some of the OIN’s biggest backers, notably IBM, are proponents of software patents.
The latest atrocious ruling by CAFC did nothing to remove software patents; quite the contrary. And the EFF called for this ruling to be escalated to SCOTUS. The EFF has been very strange when it comes to this subject; it’s as though it’s fractured and divided within. Some members of the EFF advocate the OIN approach, whereas some want to get rid of software patents as a whole. Julie Samuels, whom we wrote about before [1, 2, 3, 4, 5, 6], has been on the side of fighting “bad” patents, not software patents, and she also targets patent trolls rather than patent scope. Gérald Sédrati-Dinet (April) wrote this message to her the other day:
…why the hell do you and EFF want to improve patent quality? we – software users and devs – just don’t need patents!
Going back to Intellectual Ventures, some suggest targeting the “bad” players (e.g. trolls) or “bad” patents, not the core issue (patents). The thing about Intellectual Ventures is, what it does qualifies as a crime; it’s racketeering. It’s not “bad”, it’s criminal. Notice the comment in this article which says:
So the FTC says it plans on cracking down on patent trolls, and IV responds by attempting to shake down several companies using patents that are blatantly bogus and should never have been granted in the first place, all originally held by other companies…
Either they aren’t following the news, or they are damn sure that the FTC would never actually come after them, because I just cannot imagine how else they could have done something so blatantly designed to draw the attention of the FTC as a perfect first case when going after patent trolling operations.
Like Acacia, there are many proxies that require immense investigation endeavours. The proxies can help impede prosecution of Intellectual Ventures.
As Troll Tracker put it the other day:
Intellectual Ventures? You really should make it a little harder to pick on you.
It has become too easy to know that this ‘firm’ is hardly different from the Mafia, but lousy pseudo-news sites like ZDNet won't tell you that. Sometimes, rogue interests in the media (e.g. Gates Foundation funding) spoil the broth and manufacture consent for despicable operations of profiteering. █
Permalink
 Send this to a friend
Send this to a friend
06.22.13
Posted in Law, Patents at 11:28 am by Dr. Roy Schestowitz
Strike three. Time to strike against the ‘legal’ system?

London strike
Summary: Silly judgment from the source of many of today’s software patents is harming what looked like progress
In the land of software patents the lawyers seem concerned that patents on software are being invalidated and one firm (patent lawyers in the US) says “The PTAB decision [invalidating software patents] was issued nine months after the PGR petition was filed and was, therefore, relatively expedient, especially compared to the district court litigation that preceded it. Versata had sued SAP in federal district court in 2007, Versata prevailed at trial, and SAP appealed to the United States Court of Appeals for the Federal Circuit in 2011. The Federal Circuit upheld the jury’s infringement verdict—and its more than $300 million damages award—with respect to the same patent just last month. Versata Software, Inc. v. SAP America, Inc., Nos. 2012-1029, -1049, slip op. at 2 (Fed. Cir. May 1, 2013).”
They try to belittle the importance of this decision. They are also missing the point that in much of the world this decision would not required the court to even get involved. Meanwhile, reveals the EFF, CAFC is up to no good again, validating software patents:
The tortured history of Ultramercial v. Hulu continues, with a new ruling from the Federal Circuit upholding one of our favorite, most absurd patents: one that claims a process for doing no more than viewing ads online before accessing copyrighted content. How could that be patentable, you might ask. To which we might answer, good question.
[...]
First, in Mayo v. Prometheus, the Supreme Court invalidated a patent covering a medical diagnostic test. There, the Court held that a method cannot be patented where it adds “nothing specific to the laws of nature other than what is well-understood, routine, conventional activity, previously engaged in by those in the field.” More recently, in AMP v. Myriad, the Supreme Court stuck with this theme, holding that Myriad could not patent genes that occur in nature and stating that “Myriad did not create anything. To be sure, it found an important and useful gene, but separating that gene from its surrounding genetic material is not an act of invention.”
This CAFC decision is very serious an event and one pundit said about it that:
Opponents of software patents suffered a setback as the Federal Circuit today said a patent for displaying content before a video should not be considered an abstract idea.
Read about CAFC in our previous posts. We really need to set up a Wiki index about CAFC pretty soon. █
Permalink
 Send this to a friend
Send this to a friend
Posted in Microsoft at 11:19 am by Dr. Roy Schestowitz
National Skype Agency

Summary: Microsoft is very much in bed with the NSA (and by extension DHS and CIA) and there is more evidence to show this now
Skype is a good pal of the NSA and they have been almost twins ever since Microsoft bought it, under mysterious financial circumstances that we covered at the time of the acquisition. We wrote about it a long time ago, naming the NSA agenda too (almost exactly one year ago).
Skype is a spy. Deal with it. I don’t use Skype myself, but the network effect makes it hard for many to quit the addiction. The network effect is what makes it so powerful a spying apparatus.
According to this report from The Guardian:
Skype, the web-based communications company, reportedly set up a secret programme to make it easier for US surveillance agencies to access customers’ information.
The programme, called Project Chess and first revealed by the New York Times on Thursday, was said to have been established before Skype was bought by Microsoft in 2011. Microsoft’s links with US security are under intense scrutiny following the Guardian’s revelation of Prism, a surveillance program run by the National Security Agency (NSA), that claimed “direct” access to its servers and those of rivals including Apple, Facebook and Google.
Project Chess was set up to explore the legal and technical issues involved in making Skype’s communications more readily available to law enforcement and security officials, according to the Times. Only a handful of executives were aware of the plan. The company did not immediately return a call for comment.
Last year Skype denied reports that it had changed its software following the Microsoft acquisition in order to allow law enforcement easier access to communications. “Nothing could be more contrary to the Skype philosophy,” Mark Gillett, vice president of Microsoft’s Skype division, said in a blog post.
According to the Prism documents, Skype had been co-operating with the NSA’s scheme since February 2011, eight months before the software giant took it over. The document gives little detail on the technical nature of that cooperation. Microsoft declined to comment.
Interesting. Now we have more facts verified. We should call out Skype like we call out Windows. It has a back door, at the server side and probably several at the client side too. Bruce Schneier, a security guru, says:
Reread that Skype denial from last July, knowing that at the time the company knew that they were giving the NSA access to customer communications. Notice how it is precisely worded to be technically accurate, yet leave the reader with the wrong conclusion. This is where we are with all the tech companies right now; we can’t trust their denials, just as we can’t trust the NSA — or the FBI — when it denies programs, capabilities, or practices.
He is being too polite. He should just say that Microsoft deceived and lied. A lot of companies choose their words very carefully these days.
Speaking of spying with microphone and camera at the edge points, Xbox spying is getting even worse and there is a Web site dedicated to the subject. It says: “Tell Microsoft: I won’t buy an XBOX ONE because I don’t want the NSA in my living room.” Check out their posts, preceded by:
Always on and listening. Infrared camera. Facial and voice recognition. Heart monitor. In your living room.
Is Microsoft’s XBOX ONE the future of the NSA’s PRISM program?
Microsoft was first to join PRISM (see the slides leaked by Snowden/Greenwald), essentially colluding with the NSA, so we should assume that the NSA can effortlessly access all this data. We know that the special relationship Microsoft has with the NSA enables even espionage in non-US counties and Stuxnet is a good example of the outcome. █
Permalink
 Send this to a friend
Send this to a friend
Posted in Marketing, Microsoft, Vista 8 at 11:05 am by Dr. Roy Schestowitz
Rigging debates
Summary: Comment AstroTurf alleged by an industry veteran who has observed and studied this phenomenon for decades
A long time ago, about half a decade into the past, Mr. Dvorak wrote about so-called “Munchkins” and we cited/quoted him on it. He saw these tactics going back to the days of OS/2 and "Barkto". Now that Reddit-planted Xbox AstroTurfing comes to light we should point out a Dvorak article from the end of 2012, around the time of the release of Vista 8 John Dvorak suspected Microsoft was “planting” comments in support of Vista 8:
While following the recent hirings and firings at Microsoft, the presence of Microsoft Munchkins is more obvious than ever to me. I cannot prove their existence, however, unless someone finally steps forward and admits everything. If you are one, please do so!
Munchkins are commenters who I believe work directly for Microsoft or for its public relations agency. They scour the comment boards and rebuke with high authority all criticisms of specific Microsoft products. The reality of these people was well-documented during the Windows versus OS/2 days and I can only suspect that the practice continues to this day.
Once in a while, one of these characters shows up on my blog with a long and seemingly thoughtful post about some Microsoft product. The piece manages to condemn everyone who is critical of something Microsoft did. When you go back into the admin section of the blog where you can look at all postings by that person, the IP address, and other details, you always find that this person has not been on the blog before, and has never posted any prior comments. I can assure that anyone who is long-winded in the comment section posts a lot of comments.
Microsoft and crime are almost synonymous, so it would not be shocking if many or most pro-Vista 8 comments were indirectly funded by the company of crimes as ‘norm’.
Thanks to the reader who showed us the article above; somehow we missed it (we are no longer watching Microsoft closely). █
Permalink
 Send this to a friend
Send this to a friend
Posted in News Roundup at 8:24 am by Dr. Roy Schestowitz

Contents
-
Kernel Space
-
Applications
-
Instructionals/Technical
-
Wine or Emulation
-
Since going into the release candidate phase two weeks ago, no new features are being introduced into the Wine trunk code-base but only bug-fixes under this code freeze. As such, Wine 1.6-rc3 isn’t too exciting unless you were impacted by one of the 30 bugs officially fixed in this release. If you’re interested in seeing the list of bugs-fixed, visit WineHQ.org.
-
Games
-
-
-
Valve has launched a new beta version for its Steam for Linux client, bringing a lot of interesting new features.
After a development version garners sufficient changes, Valve promotes it to stable. The work for the next beta starts almost immediately.
-
-
-
Caixa Mágica, an English and Portuguese distribution based on Ubuntu, for i586 and x86_64 processors, is now at version 20.
Caixa Mágica 20 (LinuxCM) brings updates for all the packages from the distribution, features new installation options (such as LVM support), has the latest hardware support integrated, and comes with global performance improvements.
-
Debian Family
-
Derivatives
-
Canonical/Ubuntu
-
Can Ubuntu smartphones and mobile devices connect with mobile carriers and telecom companies? Eager for a positive answer, Canonical has launched the Carrier Advisory Group (CAG) — which aims to shape Ubuntu for the mobile industry. The move comes a few weeks after Ubuntu Founder Mark Shuttleworth told The VAR Guy that the world needs a Google Android alternative.
-
Ubuntu for smartphones looks beautiful, but it’s going to have a tough fight on its hands to gain a foothold on a mobile market that’s completely and utterly dominated by Android and Google. To be honest, at this point in time with absolutely zero market share, even catching the likes of Blackberry and Windows Phone would be seen as an achievement.
Canonical’s hopes probably seem like a pipe dream at the moment, but that doesn’t mean it’s not going to give it a real go. To realize its ambitions to one day become the ‘third’ mobile option, Canonical has just announced the creation of what it calls a “Carrier Advisory Group,” or CAG, to help guide and shape its vision of Ubuntu for mobile phones.
-
-
Nobody could accuse Canonical of resting on its laurels. The business side of Ubuntu – the best-known desktop Linux distribution – has expanded aggressively into mobility, pushed forward with a new desktop environment, and continued to release new versions of the flagship OS over the past few years.
-
Flavours and Variants
-
Bauer-Puntu Linux, a distribution based on Xubuntu 13.04 (Raring Ringtail) that gives homage to the activist group Anonymous, is now at version 13.04.
-
-
SMART stands for Spatial Monitoring and Reporting Tool. It’s an open source solution for wildlife managers working in areas of limited and constrained resources. This software helps them collect, measure, and evaluate data overlayed on a structure of best practices, to increase the mission of the conservation community: to protect and improve the lives of endangered species around the world, maintaining biodiversity.
-
-
-
MakerBot, once the progeny and a proponent of the open source hardware/software movement is being acquired by Stratasys for about $403 million. Not bad for a company whose origins are the open-source community.
-
-
Web Browsers
-
Mozilla
-
In a mobile arena already heavily dominated by Android and iOS, can Mozilla’s young, open upstart OS really hope to succeed? Its chances are “actually surprisingly good,” opined Rob Enderle, principal analyst at the Enderle Group. “Google has done a poor job of protecting and nurturing their licensees, and they have also moved to doing their own hardware.”
There’s something eternally compelling about the ages-old story of David and Goliath, and it’s one we’ve seen play out time and time again in modern form in the tech world.
-
Mozilla’s Firefox OS clearly has an edge over other two playes Canonical and Jolla for the 3rd place in the crowded mobile space. Mozilla clearly has an edge over both Jolla and Canonical, with Canonical being the last in the race.
-
A handy Chrome feature has just been spotted in the nightly Firefox build. “Close tabs to the right” is something that’s been available on the Google Browser for some time, and it comes in really handy when you’ve been browsing and suddenly find you’ve got 10 tabs clogging things up. Close tabs to the right allows you to slash the open tabs you’ve already read, while maintaining the ones you’ve yet to get to.
-
-
Databases
-
In InfoWorld this week, I’ve reprised my views about contributor agreements. The trigger for this was seeing Oracle erroneously change the license for the MySQL man pages from GPL to something nasty. Once they were told, they fixed the error (which had been public for two months), but the fact their build system even has an option for proprietary relicensing that can be accidentally enabled is cause for thought.
-
So-called ‘contributor agreements’ give corporate sponsors of open source projects too much power
-
CMS
-
NYC Community Board offices all have filing cabinets overflowing with hundreds of paper folders containing documents related to land use in their districts—board resolutions, liquor license applications, meeting minutes, Uniform Land Use Review Procedures, sidewalk cafe applications, and more. A small fraction of these have been scanned and put online as pdfs, but they are not fully searchable.
-
BSD
-
Project Releases
-
-
Health/Nutrition
-
Although genetic engineering has been widely adopted in a few major crops—mainly soybeans, corn, cotton and canola—only two general types of engineered genes, for resistance to herbicides and for killing certain insects, have been widely commercially successful after 30 years of trying.
These have provided some benefits, such as a reduction of chemical insecticide use on some of these crops, and some relatively small yield increases. Most of the yield increases for small farmers are from cotton, a low value crop, which is unlikely to pull these farmers out of poverty.
At the same time, in the countries that have used these technologies the longest, big problems are emerging. Weeds resistant to the herbicide used on Monsanto’s crops have reached epidemic proportions in the U.S., reportedly infesting about 60 million acres and increasing rapidly. This has increased herbicide use by hundreds of millions of pounds above where it probably would have been had these crops not existed.
And now insects resistant to Bt are emerging around the world. I was at the University of Illinois recently, where I heard a respected corn entomologist bemoaning the intention of corn farmers toreturn to the use of chemical insecticides to control rootworms that have developed resistance to Monsanto’s Bt gene for controlling that important pest.
-
-
Sure, you probably know the basic ingredients in your fast food lunch — chicken or beef, lettuce and tomato, whathaveyou — after all, you’re the one who ordered it. But if you, like many consumers, care whether or not those ingredients include genetically modified organisms (GMOs), the ingredient list usually is no help. Chipotle announced that it will now mark those ingredients on its website for discerning consumers.
-
Defence/Police/Secrecy/Aggression
-
Earlier this week, an anonymous public defender sent Gothamist this photo of an NYPD warrant squad officer wearing a t-shirt with a pretty disturbing quote from Ernest Hemingway
-
June 21, 2013 “Information Clearing House – Continuing his streak of fiercely criticizing President Obama’s foreign policy and civil liberties record, pre-eminent left-wing scholar Noam Chomsky told GRITtv that this administration is “dedicated to increasing terrorism” throughout the world via its own “terrorist” drone strikes in foreign lands.
-
-
-
-
The CIA and US special operational troops and have been secretly training Syrian rebels at bases in Jordan and Turkey since November 2012. Up to 100 from all over Syria have gone through courses in the last month alone, according to US media reports.
-
The CIA and US special operations forces have been training Syrian rebels for months, since long before President Barack Obama announced plans to arm the opposition, the Los Angeles Times has reported.
-
US President Barack Obama said the United States left around 700 combat-ready troops in Jordan after a training exercise in the country.
-
The CIA and US special forces have been secretly training Syrian rebels since last year at bases in Jordan and Turkey, the Los Angeles Times reported Friday.
-
For around fifteen years, this arrangement “worked.” Those who knew about it accepted it—sometimes queasily, more often eagerly. It made them feel important, adventurous, grown up. It meant that they weren’t just playing in a student-government sandbox. Anyway, promoting liberal-democratic ideas among Third World students, opposing Communist and Soviet influence, and helping anti-apartheid student groups in South Africa did not present problems of conscience. Moreover, while the C.I.A. money was earmarked for overseas activities, it freed up funds derived from other sources to be used for the N.S.A.’s domestic purposes, which included campaigning for academic freedom, demanding the abolition of the House Un-American Activities Committee, and supporting the civil-rights movement. (For example, the N.S.A. helped found the Student Nonviolent Coordinating Committee and provided it with crucial political and financial assistance.) For these reasons, it’s too simple, and not truly correct, to dismiss the N.S.A. as nothing but a C.I.A. front. It was better than that. But it was deeply compromised. The secrecy and deception inherent in the arrangement amounted to a kind of moral corruption.
-
The election of a moderate new president in Iran, Hassan Rouhani, who has promised to enact reforms, including the release of political prisoners, comes almost exactly 60 years after a cataclysmic episode that continues to define geopolitical relations in the Middle East and profoundly influence the image of the United States in the region.
-
CIA Director John Brennan paid an unannounced visit to Moscow on Wednesday and Thursday, sources told Interfax on Friday.
Russian Foreign Intelligence Service declined to confirm or deny that Brennan had been to Moscow, but senior Kremlin aide Yury Ushakov told reporters in mid-May that “a contact with the director of CIA is being planned.”
-
In the wake of The Sopranos star James Gandolfini’s sudden death,libertarians everywhere are saying the actor was assassinated by the Central Intelligence Agency.
-
-
Cablegate
-
An Icelandic businessman linked to WikiLeaks said he has readied a private plane to take Edward Snowden, the former National Security Agency contractor who exposed secret U.S. surveillance programmes, to Iceland if the government grants him asylum.
“We have made everything ready at our end now we only have to wait for confirmation from the (Icelandic) Interior Ministry,” Olafur Vignir Sigurvinsson told Reuters. He is a director of DataCell, a company which processed payments for WikiLeaks.
-
Bradley Manning is at the defense table. Casting a long shadow over his trial, however, is the figure of someone else the government would apparently like to put on trial: Julian Assange.
On Tuesday, government prosecutors sparred with defense lawyers for Manning, the Army private first class who has admitted to leaking a massive cache of documents to the transparency organization that Assange founded. At issue was whether the judge should accept as evidence two WikiLeaks tweets and a crowdsourced document called “The Most Wanted Leaks of 2009.”
-
The Justice Department used a secret search warrant to obtain the entire contents of a Gmail account used by a former WikiLeaks volunteer in Iceland, according to court records released to the volunteer this week.
The search warrant was issued under seal on October 14, 2011 by the Alexandria, Virginia federal judge overseeing the WikiLeaks grand jury investigation there. The warrant ordered Google to turn over “the contents of all e-mails associated with the account, including stored or preserved copies of e-mails sent to and from the account, draft e-mails, deleted e-mails [...] the source and destination addresses associated with each e-mail, the date and time at which each e-mail was sent, and the size and length of each e-mail.” The warrant also ordered Google not to disclose the search to anyone.
-
Environment/Energy/Wildlife
-
The city of Houston has agreed to purchase half its electricity from renewable sources.
That will make Houston the largest municipal purchaser of renewable energy in the nation, according to the city, which cited estimates from the Environmental Protection Agency.
“Houston is already known as the energy capital of the world, but we are committed to becoming the alternative energy capital of the world as well,” Mayor Annise Parker said in a written statement Thursday.
-
Billionaire anti-Keystone XL activist Tom Steyer wants to rally legions of digital-savvy Obama supporters to persuade the President that Canadian oil sands crude poses a threat to the United States.
The wealthy Californian upped the ante Thursday in the high-stakes political showdown over Keystone XL by launching a social media campaign aimed at re-awakening the fervent hordes of mostly, young Obama supporters.
-
The impacts of 2013′s severe drought are apparent across the nation in forests, on farms and on once snowy peaks. Meanwhile, the oil and gas industry is demanding unprecedented amounts of water for hydraulic fracturing, better known as fracking.
-
Finance
-
Financial adviser Chauncey Mayfield allegedly stole $3.1 million from the pension funds of Detroit police officers and firefighters so he could buy shopping centers in California, according to the Securities and Exchange Commission.
Did he do it? Who knows? Mayfield and several of his associates settled the case last week without admitting or denying guilt. All they had to do to make the SEC go away was agree to give the money back.
-
U.S. District Judge Sim Lake of the Southern District of Texas announced at a hearing in Houston today that Skilling will serve 14 years. His original conviction called for him to serve 24 years in connection with the collapse of the once high-flying energy trading firm. Under the agreement with federal prosecutors, Skilling could be released as early as 2017.
-
Robert Kuttner’s title refers, first, to the “medieval institution” that was the fate of improvident souls in England who could not repay their debts, including Daniel Defoe. In 1692, Defoe was committed to King’s Bench Prison in London, where he began to agitate for a change in the legal system. Forcing debtors to rot, Defoe not disinterestedly pointed out, was injurious to both parties, since “after a debtor was confined in prison both he and the creditor lost through his prolonged distress.” Society responded, eventually, with bankruptcy laws, but it is very much Kuttner’s point in “Debtors’ Prison” that we — America and Europe in the age of the financial crisis — have yet to absorb the principal lesson of Defoe’s “bitter experience.”
-
Privacy
-
Amidst the havoc surrounding the earth-shattering revelations being made about the massive catch-all surveillance being conducted by the US government against virtually everybody with an Internet connection, a set of relatively unremarkable letters arrived in our GMail inboxes on Tuesday evening, containing a series of attachments.
These attachments were scanned court orders, sealed and later unsealed, issued to Google by the United States District Court for the eastern district of Virginia. These orders demanded that Google hand over to the United States (yes, they were that specific), various information relating to accounts we hold with Google, including whom we communicated with, when, from where, and for how long.
The court orders were almost certainly related to the Grand Jury investigation of the unauthorized public disclosure of information showing considerable misconduct, including a number of probable cases of war crimes, by US military forces in Iraq and Afghanistan during their wars in these countries, a list of people being held without trial or legal recourse in Guantanamo Bay, and a trove of diplomatic cables detailing the ways the US government have conducted themselves – both good and bad – over many years.
-
Project Tempora – the evolution of a secret programme to capture vast amounts of web and phone data
-
Exclusive: British spy agency collects and stores vast quantities of global email messages, Facebook posts, internet histories and calls, and shares them with NSA, latest documents from Edward Snowden reveal
-
There’s been plenty of commentary concerning the latest NSA leak concerning its FISA court-approved “rules” for when it can keep data, and when it needs to delete it. As many of you pointed out in the comments to that piece — and many others are now exploring — the rules seem to clearly say that if your data is encrypted, the NSA can keep it. Specifically, the minimization procedures say that the NSA has to destroy the communication it receives once it’s determined as domestic unless they can demonstrate a few facts about it.
-
-
Edward J. Snowden, the former National Security Agency contractor whose leak of agency documents has set off a national debate over the proper limits of government surveillance, has been charged with violating the Espionage Act and stealing government property for disclosing classified information to The Guardian and The Washington Post, the Justice Department said on Friday.
-
Last week, President Obama claimed in an interview that the National Security Agency could not listen to Americans’ phone calls or read their emails. But newly revealed secret government documents—the latest in the series of high-profile leaks about classified surveillance—outline how the NSA can sweep up and store Americans’ communications.
The documents, published by the Guardian late Thursday, are signed by Attorney General Eric Holder and stamped with the date July 29, 2009. They were submitted to the secret Foreign Intelligence Surveillance Court and outline the so-called “minimization procedures” the NSA is supposed to follow to limit any “incidental” spying it does on the communications of Americans or permanent U.S. residents. The disclosure sheds light on highly significant surveillance procedures the government has until now managed to keep beyond public scrutiny.
-
Wired’s kicked off a new animated webcomedy starring John Hodgman as a crusty old NSA agent and Nicole Winters as his young protege. It’s pretty promising stuff!
-
Yesterday, the Guardian released two previously-classified documents describing the internal “minimization” and “targeting” procedures used by the NSA to conduct surveillance under Section 702. These procedures are approved by the Foreign Intelligence Surveillance Court (FISC) on an annual basis and are supposed to serve as the bulwark between the NSA’s vast surveillance capabilities and the private communications of Americans. As we noted earlier today, the procedures, themselves, aren’t reassuring: far too much discretion is retained by NSA analysts, the procedures frequently resolve doubt in favor of collection, and information is obtained that could otherwise never be obtained without a warrant.
-
-
-
-
The British spy agency GCHQ has secretly tapped more than 200 fiber-optic cables carrying phone and internet traffic and has been sharing data with the U.S. National Security Agency, according to a news report.
-
According to a post on Facebook’s security blog, a bug in the company’s friend recommendation system exposed the contact information of some six million users to others. The bug has been present for about a year, but the company only found out about it in the last 24 hours. The affected users will be notified by email. The company says there’s no evidence the bug was exploited maliciously.
-
To Daniel Ellsberg, the well-known whistleblower and lifelong advocate for freedom who leaked the “Pentagon Papers” 40 years ago, “there has not been in American history a more important leak than Edward Snowden’s release of NSA material.”
-
-
Russ Tice, a former intelligence analyst who in 2005 blew the whistle on what he alleged was massive unconstitutional domestic spying across multiple agencies, claimed Wednesday that the NSA had ordered wiretaps on phones connected to then-Senate candidate Barack Obama in 2004.
Speaking on “The Boiling Frogs Show,” Tice claimed the intelligence community had ordered surveillance on a wide range of groups and individuals, including high-ranking military officials, lawmakers and diplomats.
-
Nick Pickles, director of Big Brother Watch, said: “This appears to be dangerously close to, if not exactly, the centralised database of all our internet communications, including some content, that successive Governments have ruled out and Parliament has never legislated for.
“Britain has a clear legal process in place to govern the interception of the content of communications and blanket interception is not a part of that system. If GCHQ have been intercepting huge numbers of innocent people’s communications as part of a massive sweeping exercise then I struggle to see how that squares with a process that requires a warrant for each individual intercept. This question must be urgently be addressed in Parliament.
“The fact GCHQ staff have been discussing how light the UK’s oversight regime is compared to the US highlights why we need a wholesale review of surveillance law, including the fact that there is absolutely no judicial process within the current system and the people making these decisions are able to hide in the shadows rather than face public scrutiny.”
-
Mobile company EE has been quite open in explaining the sale of data analytics based on their customers data in partnership with Ipsos MORI. But we are concerned that they think the storm is over and can return to business as usual. We may need your support to make them listen.
EE has already met with ORG to explain how their data services work, how they aggregate data and what general legal framework they operate. For this, we commend EE on their openness and hope that it continues.
-
Communications Security Establishment Canada (CSEC), the NSA’s Canadian counterpart and longstanding partner, has been scrutinizing the metadata of Canadians’ electronic communications since at least 2005.
Moreover, the NSA routinely provides Canada’s security agencies with intelligence on Canadians and CSEC reciprocates by providing U.S. intelligence officials with information about people living in the U.S. This arrangement allows both agencies to circumvent legal bans on warrantless surveillance of their own citizenry’s communications.
It was “common” for NSA “to pass on information about Canadians,” Wayne Easter, Canada’s Solicitor-General in 2002-3, told the Toronto Star this week. As Solicitor-General, Easter was responsible for overseeing the operations of the Canadian Security Intelligence Service (CSIS) and the Royal Canadian Mounted Police (RCMP).
-
Information commissioner’s office says it will launch contempt of court proceedings if data is not deleted within 35 days
-
The Guardian published a new batch of secret leaked FISA court and NSA documents yesterday, which detail the particulars of how government has been accessing Americans’ emails without a warrant, in violation of the Constitution. The documents lay bare fundamental problems with the ineffectual attempts to place meaningful limitations on the NSA’s massive surveillance program.
Essentially, the new documents, dated July 2009 and approved in August 2010, detail how the NSA deals with the huge streams of information it receives during the collection program that gathers the content of email and telephone calls, allowing it to keep vast quantities of content it could never get with a warrant. They may not be the current procedures – more on that in another blog post shortly.
-
The world is still reeling from the series of revelations about NSA and FBI surveillance. Over the past two weeks the emerging details paint a picture of pervasive, crossborder spying programs of unprecedented reach and scope: the U.S. has now admitted using domestic networks to spy on Internet users both domestically and worldwide. The people now know that foreign intelligence can spy on their communications if they travel through U.S. networks or are stored in U.S. servers.
-
A million people marched in London to stop Blair going to war.
-
Terrorism analysts and specialist journalists say claims of thwarted terror plots from phone and data mining do not stand up.
-
• Where did Facebook chief security officer Max Kelly go after he left the social network in 2010? To the NSA, according to the New York Times, which says it’s the first to report that tidbit. Also previously unreported, says the NYT, is that Internet-call provider Skype developed a program to make it easier to cooperate with law enforcement and the government.
-
Civil Rights
-
Yes, informing the American public of misdeeds by the US government is considered “aiding the enemies of the United States.” The reality, of course, is what they’re saying is that they really mean “the current government” when they refer to “the United States,” and “the enemies” are the American public.
-
-
Even before a former U.S. intelligence contractor exposed the secret collection of Americans’ phone records, the Obama administration was pressing a government-wide crackdown on security threats that requires federal employees to keep closer tabs on their co-workers and exhorts managers to punish those who fail to report their suspicions.
President Barack Obama’s unprecedented initiative, known as the Insider Threat Program, is sweeping in its reach. It has received scant public attention even though it extends beyond the U.S. national security bureaucracies to most federal departments and agencies nationwide, including the Peace Corps, the Social Security Administration and the Education and Agriculture departments. It emphasizes leaks of classified material, but catchall definitions of “insider threat” give agencies latitude to pursue and penalize a range of other conduct.
-
-
In 2013 alone, one could count at least 5 suspicious deaths of people who are outspoken against government tyranny…
-
An undercover police officer posing for years as an environmental activist co-wrote a libellous leaflet that was highly critical of McDonald’s, and which led to the longest civil trial in English history, costing the fast-food chain millions of pounds in fees.
The true identity of one of the authors of the “McLibel leaflet” is Bob Lambert, a police officer who used the alias Bob Robinson in his five years infiltrating the London Greenpeace group, is revealed in a new book about undercover policing of protest, published next week.
-
-
Intellectual Monopolies
-
Copyrights
-
I first placed music online in 1996, a WAV file recorded through a microphone to promote the sale of an album I had under license on my indie BeanBag label featuring Georgie Fame and Van Morrison. I cheered for other music industry executives like Larry Rosen of GRP Records when he launched Music Boulevard online around 1997. I licensed songs by Jesse Colin Young (founder of The Youngbloods) to music publishing expert Bob Kohn’s eMusic.com for a cash advance against future royalties that had us partying like it was 1999.
But by the year 2000, any hope of that engagement between legal music and the Internet leading to a new future was pretty much dashed by an online startup corporation named Napster that provided free music downloads. Though a Federal court would find Napster guilty in 2001 of providing illegal copying similar to a counterfeiting operation, the business model known as “DMCA ‘Safe Harbor’ corporations” was launched.
Permalink
 Send this to a friend
Send this to a friend
06.21.13
Posted in News Roundup at 11:24 am by Dr. Roy Schestowitz

Contents
-
Cumulus Linux, which bills itself as “the first true, full-featured Linux operating system for datacenter networking,” has emerged from stealth mode. Backed by several VMware (VMW) veterans, Cumulus sounds like a next-generation software-defined networking (SDN) player. And the company has $15 million in venture funding from Andreessen Horowitz, Battery Ventures and others.
Cumulus Linux emerged from stealth mode and become generally available on Wednesday. The company behind its development, Cumulus Networks, says the OS will do for networking what Linux has already achieved in other areas.
-
-
-
-
Cumulus Networks, a Silicon Valley startup with a Linux operating system for data center networking and Silicon Valley superstar pedigree, came out of stealth Wednesday.
-
-
-
Server
-
The ‘surprise’ win for the machine also known as Tianhe-2 marks China’s first return to top spot since 2010.
-
Linux’s many strengths are undeniable in numerous aspects of computing today, but if there’s one area in which its domination tends to continue virtually unchallenged, it’s supercomputing.
-
Audiocasts/Shows
-
Kernel Space
-
-
-
-
-
Graphics Stack
-
NVIDIA is bringing their 319.xx proprietary graphics driver from Linux x86 to ARM.
Up to now NVIDIA has just supported their proprietary Linux graphics driver for GeForce, Quadro, and Tesla hardware on Intel x86 and x86-64 architectures (and formerly for Itanium), but now ARM support is coming.
-
Applications
-
Instructionals/Technical
-
-
-
-
-
-
-
-
-
I am taking a graphic design course and one of the assignements received was to remake the logo of a well known soft drink (for the purpose of this tutorial I replaced that logo with something else, as this is not the place for unpaid advertising, especially for products I don’t use nor endorse). Is a trivial task with Inkscape, so I decided to enrich it with some water drops, as at the final exam I can show my skills and get a higher grade. For the exam I can’t provide a SVG, will have to import/convert it in a proprietary format (such is life…), but Inkscape is my tool of choice so I m sharing the process here.
-
Games
-
Linux is a solid and secure operating system that’s suitable for gaming, but at this time Windows remains the lead platform for PC games. This may be about to change. Last year, Valve Software brought their game distribution system Steam to Linux, along with several of their popular game titles like Left 4 Dead and Half-Life.
-
Bookmark and Share
Planetary Annihilation one of the most successful games to hit it on Kickstarter has within the last week pushed out their Linux version!
Planetary Annihilation is a Real Time Strategy game from Uber Entertainment which includes some of the staff that made Total Annihilation and Supreme Commander two games that have a big place in my heart! I do love RTS games so this is a big, big win for me!
-
Desktop Environments/WMs
-
K Desktop Environment/KDE SC/Qt
-
-
digiKam team is proud to announce the second beta release of digiKam Software Collection 3.3.0. This version currently under development, including a new core implementation to manage faces, especially face recognition feature which have never been completed with previous release. Face detection feature still always here and work as expected.
-
I’ve been looking into how easy it is to confirm that a binary package corresponds to a source package. It turns out that it is not easy at all. So I’ve written down my findings in this blog entry.
-
-
Rekonq now provides several popular features found in Mozilla Firefox and Google Chrome. This web browser may be up for consideration as your new favorite.
-
We saw last week the release of the first beta of KDE Plasma Workspace and applications 4.11
From my side, that’s a very important milestone, because it’s pretty much the coronation of what we intended the 4.x series of the workspace to be. It was a long ride, but I think this future release will be pretty stable and “defined” in its own identity.
-
-
Prolific KDE developer Pawan Yadav has updated the PotenzaRemix theme bringing it to version 1.7. The theme, as he explains, is a mix of Potenza and Awoken (action icon) with his custom icons.
If you are already running the previous version of this theme and want to update, he suggests deleting the previous theme from the usr/share/icon folder.
-
-
Linux is considered by most to be a big scary place for new users to break into, but the truth is that’s Linux distributions provide a great community for many technology enthusiasts to come together and share their ideas and of course their desktops.
So if you’re sick of looking at that familiar blue Widows desktop and you’re looking to learn something new, or if you just want something that’s more secure than Windows/Mac, then take a look at some of the best beginner Linux distro’s below.
-
New Releases
-
-
antiX is a lightweight Linux distribution aimed at old systems with not-so-good configurations. It is based on the “testing” branch of Debian. Unlike several other distros based on the “testing” repository of Debian, like Linux Mint Debian Edition, Parsix and PureOS, antiX specifically targets computers that people usually plan to throw away in dustbins. According to its developers, antiX should run on most computers, ranging from 64MB old PII 266 systems with pre-configured 128MB swap to the latest powerful boxes. It’s easy to install, and comes as live CD that users can test-drive before installing on their PCs.
-
-
-
PCLinuxOS/Mageia/Mandrake/Mandriva Family
-
The developers at the OpenMandriva Association have released the first development version of OpenMandriva Lx 2013, the first release to take place under the governance of the new association. OpenMandriva Lx Alpha includes version 3.8.12 of the Linux kernel, a desktop based on KDE 4.10.4, and current versions of LibreOffice (4.0.3.3) and Firefox (version 21). The distribution, which in the past had been merged with the ROSA Linux code base, also includes a number of tools from the Russian ROSA Laboratory developers including version 1.6 of the ROSA Media Player (ROMP).
-
Red Hat Family
-
The leading Open Source company, and the sponsor of Fedora Linux, Red Hat has posted the total revenue of $363 million for the first quarter of 2013. It’s an increase of 15% in U.S. dollars from the year ago quarter. Subscription revenue for the quarter was $316 million, up 16% in U.S.
-
-
-
Linux software developer Red Hat Inc. was among the stocks seeing notable activity in after-hours trading following the company’s quarterly results.
-
Red Hat Inc., the company behind the Linux open-source operating system, said Wednesday that net income in its fiscal first-quarter grew 8 percent as subscription revenue increased.
-
First quarter revenue of $363 million, up 15% year-over-year
-
U.S. stock-index futures pointed to a lower opening on the Wall Street as investors weighed comments by Fed Chairman Ben Bernanke and the Federal Open Market Committee’s (FOMC) post-meeting policy statement.
-
-
Debian Family
-
Derivatives
-
Canonical/Ubuntu
-
-
-
How important is Mark Shuttleworth’s to Canonical, Ubuntu, Linux and open source? Officially, Shuttleworth’s role at the company behind Ubuntu, which he founded in 2004, has been limited to product strategy and design since he stepped down as CEO in December 2009. Still, his presence looms much larger in the Ubuntu community.
-
-
Like many Canonical-led projects, Mir is under GPLv3 – a strong copyleft license. There’s a couple of aspects of GPLv3 that are intended to protect users from being unable to make use of the rights that the license grants them. The first is that if GPLv3 code is shipped as part of a user product, it must be possible for the user to replace that GPLv3 code. That’s a problem if your device is intended to be locked down enough that it can only run vendor code. The second is that it grants an explicit patent license to downstream recipients, permitting them to make use of those patents in derivative works.
-
Several high-profile telecom carriers have signalled their interest in supporting Ubuntu Touch – Canonical’s mobile platform
-
The debate that has sparked around Mir and its use with the other flavors of Ubuntu has also raised another interesting question regarding the Legacy support.
-
Jono Bacon, the Ubuntu Community Manager, has recently been working to finalize a fair and transparent plan for how the money raised from the community, upstreams, and flavors sliders can be used to benefit the most valuable projects and efforts within the Ubuntu and flavors community. Jono prepared a plan and reviewed it with the Community Council who were happy with the programme he proposed.
-
-
The Cubieboard is a tiny computer that’s about the size and shape of a Raspberry Pi, but which features more memory, built-in storage, and a few other goodies that the Raspberry Pi lacks.
-
Linux.com interviewed Wolfgang Denk, founder of Denx and the creator of the U-Boot bootloader. The embedded Linux pioneer spoke on a range of issues including the future of U-Boot, the importance of Yocto Project code and how it has changed Denx’s own ELDK distribution, and the growth of ARM and real-time Linux in embedded computing.
-
Phones
-
Electronics manufacturer Foxconn Technology Group is putting yet more effort behind Mozilla’s Firefox OS, and plans to hire up to 3,000 people in Taiwan with expertise in HTML5 and cloud computing.
On Thursday, Foxconn said it was looking to hire between 2,000 and 3,000 people in order to bolster its research into software. It’s looking for software engineers with skills in HTML5 operating systems, HTML5 apps, and cloud computing, the company said.
-
Ballnux
-
Samsung’s Galaxy series is a range of mobile computers that all run on Google’s Android mobile operating system. One branch of the series is not smartphones, though, but rather Samsung’s stab at point-and-shoot style cameras. The company has apparently decided that the camera business suits it, and subsequently introduced the logical next step in image capturing: the Galaxy NX Digital Single-Lens Reflex camera (or simply DSLR).
-
The device is designed for customers on a budget, and features a 1GHz Qualcomm Snapdragon S1 processor and 4GB of onboard storage.
-
Samsung unveiled a quad-core, 20-megapixel Galaxy NX camera with 4G LTE and a 4.8-inch display, billed as being the first Android-based, connected interchangeable-lens camera, following up on last week’s announcement of its Android-powered 16-megapixel, 10x-zoom Galaxy S4 Zoom. Also today, Samsung unveiled the Ativ Q, a dual-boot 13.3-inch convertible tablet that runs Android and Windows 8 on an Intel “Haswell” Core processor.
-
Android
-
Apple and Microsoft have been doing this for years, so it’s not a new concept. But Google is trying to make sure it keeps riding on the success wave till as long as possible. Android is already the leading mobile operating systems in most parts of the world, ahead of Apple’s proprietary iOS that powers its iPhones and iPads, especially in the Asia region. Yet Google doesn’t want to leave a stone unturned. Google has partnered with Spice Global, an Indian conglomerate headquartered in Singapore, to open an Android Nation store in the capital city of New Delhi.
-
So a few people have sent me this review of the OUYA console, and asked if things were really that bad. I’ve been tweeting about receiving the final retail version of the console, and I was surprised to see a review get up so quickly. The retail kits were only sent to the press today. So I read the review and just as I thought, that’s old hardware being reviewed.
-
Sub-notebooks/Tablets
-
Smaller variations are going to account for over half of overall tablets this year, analysts say.
-
-
-
The Minister of Finance and the Economy, Nicolas Marceau, has announced that LINAGORA, a French company specializing in open source software development, will open a facility in Montréal.
-
Web Browsers
-
SaaS/Big Data
-
The U.S. has spent hundreds of billions of dollars fighting terrorists. Ironically, however, the best technology available to fight terror likely isn’t a line item on the National Security Agency’s (NSA) $8 to $10 billion budget. More probably it’s Hadoop, which is open source and 100% free.
-
Oracle/Java/LibreOffice
-
The Document Foundation has announced the release of LibreOffice 4.0.4, the last version of the open source office suite before it moves on to the 4.1.x branch of releases, which is currently scheduled to arrive at the end of July. For this release, the developers of LibreOffice have closed 98 bug reports that also include a few improvements and some enhanced translations.
-
MariaDB founder Ulf Michael “Monty” Widenius says that Oracle has failed to make a success of MySQL because the company doesn’t understand open source. “It’s not in their blood,” Widenius, one of the three co-founders of MySQL, told iTWire in an interview.
-
Healthcare
-
The advancements in medicine over the last 50 years are remarkable. Diseases once thought of as terminal are now curable. Chronic conditions today can be treated far more effectively than just a decade ago, making a huge impact on a patient’s quality of life.
-
Business
-
“There is a trend where a company starts with open source and builds out to follow the commercial model. Certainly all of our large customers want a company behind the platform, so they opt for that notion. A lot of smaller companies start in the open source world and then gradually move towards the commercial as they get bigger or get more dependent on those solutions.”
-
More than half of UK private and public sector organisations will spend at least 20% of their IT budget on open source applications and software within the next five years, this is the claim arising from an Open for Business study, conducted by IT service provider Reconnix,
A total of 61% of respondents intend to invest 20% or more into open source.
The majority (48%) expect to invest between 20% – 40%.
A smaller 10% of firms believe that their open source spend could account for as much as 60% of their total budget.
-
Semi-Open Source
-
FSF/FSFE/GNU/SFLC
-
The next-generation VP9 and HEVC codecs are the latest incremental refinements of a basic codec design that dates back 25 years to h.261. This conservative, linear development strategy evolving a proven design has yielded reliable improvement with relatively low risk, but the law of diminishing returns is setting in. Recent performance increases are coming at exponentially increasing computational cost.
-
Licensing
-
-
Oracle accidentally changed the licence of MySQL manual pages from the previous GPLv2 licence to a non-free licence. The change was revealed by Colin Charles, MariaDB evangelist, in a post on the MariaDB Foundation’s blog. But as the news spread, a bug report in Oracle’s issue tracker revealed that what had been found was actually a problem in the build system.
-
Openness/Sharing
-
Programming
-
If, despite the upcoming release of the web framework Ruby on Rails 4.0, users are not interested in giving up version 2.3, they can look to a German company for support. In future, Makandra will provide security updates for Ruby 2.3.x. As announced a few months ago, the Rails developers will officially no longer provide support for that version once Ruby on Rails 4.0 is launched; only Ruby 3.2.x and later versions will continue to receive updates.
-
Employing the open source R programming language for statistical analysis can reduce the pain of dealing with large and complex data sets. That’s why R is becoming more popular, as it automates the analysis process, saving a substantial amount of time, according to Open Universities’ digital analytics manager, Johann de Boer.
Speaking at the Google Analytics User Conference in Sydney, de Boer demonstrated how he could do a full analysis, fetching and cleaning up data, merging data sets together, processing the data and visualising the results, using the R language in minutes.
-
-
Hastings, a reporter for Rolling Stone and BuzzFeed who died in a car crash in L.A. yesterday at the age of 33, didn’t see it as his job to maintain “good media/military relations,” or to decide what is “necessary to report.” To the contrary–he told CounterSpin (1/27/12) that one of his golden rules for reporting was, “What does everybody know who’s on the inside, but no one’s willing to say or write.”
Hastings never forgot that journalists’ loyalties are supposed to be with the public and not to the government officials whose actions they cover–and that approach distinguished him not only from Burns but from most of his colleagues.
-
Google has admitted that the headscratching questions it once used to quiz job applicants (How many piano tuners are there in the entire world? Why are manhole covers round?) were utterly useless as a predictor of who will be a good employee.
-
Science
-
Physicists at The University of Texas at Austin have built a tabletop particle accelerator that can generate energies and speeds previously reached only by major facilities that are hundreds of meters long and cost hundreds of millions of dollars to build.
-
Hardware
-
Health/Nutrition
-
The surprise defeat of the farm bill in the House on Thursday underscored the ideological divide between the more conservative, antispending Republican lawmakers and their leadership, who failed to garner sufficient votes from their caucus as well as from Democrats.
[...]
The failure was a stinging defeat for Speaker John A. Boehner of Ohio, who continues to have trouble marshaling the Republican support he needs to pass major legislation. Without the solid backing of his party, Mr. Boehner has to rely on some Democratic support, which deserted him Thursday.
-
Security
-
Recent email found by blogger Brandon Dixon indicates that the latest spear-phishing campaigns from the group behind NetTraveler are using the PRISM controversy to lure victims into reading the booby-trapped email. The mail, which tells the tale of the disclosure of PRISM and other NSA programmes, offers a 2.5MB file – “Monitored List1.doc” – and implies that this contains a list of those monitored by the NSA. The file, of course, actually contains malware that exploits an older vulnerability CVE-2012-0158 to infect the computer.
-
Defence/Police/Secrecy/Aggression
-
-
In perfect Bush-like fashion, President Obama has invented a bogus pretense for military intervention in yet another Middle East country. The president’s claim that the Syrian government has used chemical weapons — and thus crossed Obama’s imaginary “red line” — will likely fool very few Americans, who already distrust their president after the massive NSA spying scandal.
-
We’re still waiting for the FBI to finish its internal investigation into exactly what happened in an Orlando apartment last month, when an FBI agent shot and killed Ibragim Todashev, a Chechan man who knew Boston bombing suspect Tamerlan Tsarnaev. Since the shooting, unnamed officials have painted a number of different pictures of the scene in the room in the moments before the agent opened fire. Among them, that Todashev was unarmed, that he was brandishing a knife, and that he was carrying a pipe or maybe a broomstick.
-
Iraq is being buffeted by both sides in the civil war raging across its border in Syria and Baghdad’s official policy of neutrality is at risk as the conflict spirals into a region-wide proxy war, its foreign minister said.
-
During the weeks before he was killed in a car crash in Los Angeles, reporter Michael Hastings was researching a story about a privacy lawsuit brought by Florida socialite Jill Kelley against the Department of Defense and the FBI.
Hastings, 33, was scheduled to meet with a representative of Kelley next week in Los Angeles to discuss the case, according to a person close to Kelley. Hastings wrote for Rolling Stone and the website BuzzFeed.
Kelley alleges that military officials and the FBI leaked her name to the media to discredit her after she reported receiving a stream of emails that were traced to Paula Broadwell, a biographer of former CIA director David H. Petraeus, according to a lawsuit filed in Federal District Court in Washington, D.C., on June 3.
-
Some Bradley Manning supporters have put together a very compelling campaign, called I Am Bradley Manning, asking the government to drop the “aiding the enemy” charge against Bradley Manning and noting the chilling effects it has on whistleblowers. The key part of the campaign is a five minute video of various well-known people talking about Bradley Manning and asking what would you do if you were in his shoes, and saw that your government was lying to the public, and doing things that you believed went against the very values and principles you were supposed to be fighting for.
-
No word on whether these companies would delay a patch if asked nicely — or if there’s any way the government can require them to. Anyone feel safer because of this?
-
It was a central fuel tank explosion that sent TWA Flight 800 plummeting into the Atlantic Ocean in a 1996 crash that remains one of the country’s most devastating airline accidents.
-
Corporations are trying to use the PATRIOT Act in ways that have nothing to do with Osama Bin Laden because the PATRIOT Act gives transnational corporations the power to snuff out the activism of all those who oppose them.
Terrorism, as it is commonly considered, is the use of violence against civilians to achieve any number of political ends: the destruction of the federal government, the overturning of Roe V. Wade, the restoration of a Caliphate. If you try to kill people – or succeed in killing people for a political purpose – you’re a terrorist. If you blow up the Alfred P. Murrow Federal Building and kill 168 civilians, like Timothy McVeigh, you’ve committed an act of terrorism.
Seems pretty self-explanatory – right? Not according to TransCanada Corp., the Canadian owned energy conglomerate that is the backer of the Keystone XL pipeline extension. A new set of documents obtained by the group Bold Nebraska shows that this foreign corporation is encouraging American law enforcement agencies to treat anti-pipeline protestors like terrorists. Yes, terrorists.
The documents, which Bold Nebraska got a hold of through a FOIA request, were part of a briefing given to Nebraska law enforcement agents about the “emerging threat” of groups like Tar Sands Blockade and Rainforest Action.
-
It’s dangerous business when private contractors recruit top government employees and then effectively lease them back to the government.
-
That was President John F. Kennedy speaking to the 1963 graduating class of American University —announcing that the human race was ready to move beyond war. This was the speech in which he revealed that talks on a Nuclear Test-Ban Treaty with the Soviet Union had begun, and that the U.S. was unilaterally suspending atmospheric nuclear testing.
-
Today we’re publishing—for the first time—the FBI’s drone licenses and supporting records for the last several years. Unfortunately, to say that the FBI has been less than forthcoming with these records would be a gross understatement.
Just yesterday, Wired broke the story that the FBI has been using drones to surveil Americans. Wired noted that, during an FBI oversight hearing before the Senate Judiciary Committee, FBI Director Robert Mueller let slip that the FBI flies surveillance drones on American soil. Mueller tried to reassure the senators that FBI’s drone program “is very narrowly focused on particularized cases and particularized leads.” However, there’s no way to check the Director on these statements, given the Bureau’s extreme lack of transparency about its program.
-
When a journalist dies, how can you tell if they’ve had a career that’s upheld the proudest journalistic traditions of challenging the powerful and fearlessly exposing the truth?
The New York Times will attempt to piss on that career in the journalist’s obituary.
-
In the 24 hours since the tragic death of journalist and author Michael Hastings was first reported on Tuesday, those who knew him, worked with him, and covered his work have offered numerous remembrances of the man best known for his Polk Award-winning Rolling Stone piece, “The Runaway General.”
That article, which presented a dim view of the U.S. strategy in the Afghanistan war and exposed a military command structure working to actively undermine its civilian leadership, also contained several accounts of less-than-professional behavior and comments by Gen. Stanley McChrystal, the International Security Assistance Force commander, the disclosure of which led to McChrystal tendering his resignation in June 2010.
But it’s an obituary in The New York Times that has sounded a discordant note amid the rest of the encomiums. And now Hastings’ widow, Elise Jordan, is firing back at Times brass.
-
Bill O’Reilly probably lost it during his sow O’Reilly Factor on Wednesday when he wondered why far-left loons who opposed drones and Gitmo detention are ‘so crazy.’
Well, it appears it’s the other way round since O’Reilly did a really pathetic impression of a German reporter who quite rightly questioned Obama’s drone warfare policy in Berlin that day.
-
Cablegate
-
RT’s promos for Julian Assange’s ‘The World Tomorrow’ and Spanish-language ‘La lista de Erick’ have received two gold PromaxBDA awards for Promotion, Marketing and Design as part of an international competition held in the US.
-
Speaking on the one-year anniversary of his flight to the Ecuadorian Embassy in London, WikiLeaks founder Julian Assange said that his group has a “common cause” with Edward Snowden and is in touch with the NSA leaker’s lawyers to help him seek asylum in Iceland.
A year ago, Assange took to the embassy to avoid being extradited from the United Kingdom to Sweden, where he is wanted for questioning on allegations of sexual assault. Sounding fatigued from a confinement during which he has reportedly suffered from a chronic lung condition, Assange nevertheless let loose a provocative series of rhetorical questions about Snowden and The Guardian’s Glenn Greenwald, who broke the NSA story, on Wednesday.
-
Wikileaks founder Julian Assange said on Wednesday that his antisecrecy group has been in touch with National Security Agency leaker Edward Snowden’s legal team in a bid to help him secure asylum in Iceland.
“I feel a great deal of personal sympathy with Mr Snowden,” Assange told reporters on a conference call. He joined the call from the Ecuadoran embassy in London, where he has lived since entering the diplomatic mission and seeking asylum exactly one year ago.
-
-
WikiLeaks said it needs a reply from Iceland on whether former U.S. national security contractor Edward Snowden will be granted asylum before it transports him to the Nordic island.
-
In the hours leading up to his death in a fiery car crash, a ‘paranoid’ Michael Hastings told WikiLeaks he was being investigated by the FBI, according to the whistleblowing website.
-
-
-
WikiLeaks founder Julian Assange said Wednesday his organization is helping Edward Snowden seek asylum in Iceland. Assange also hinted that he might publish Snowden’s next revelations.
-
-
-
Environment/Energy/Wildlife
-
A massive mine proposal could wipe out half of the world’s remaining wild population
-
Finance
-
The common defense of the unpaid internship is that, even if the role doesn’t exactly pay, it will pay off eventually in the form of a job. Turns out, the data suggests that defense is wrong, at least when it comes to college students.
For three years, the National Association of Colleges and Employers has asked graduating seniors if they’ve received a job offer and if they’ve ever had either a paid or unpaid internship. And for three years, it’s reached the same conclusion: Unpaid internships don’t seem to give college kids much of a leg up when it comes time to look for employment.
-
Americans were no less greedy, ignorant, selfish and violent then than they are today, and no more generous, fair-minded and idealistic.
-
Global markets have fallen sharply after the Federal Reserve signalled it may begin to scale back its stimulus of the US economy later this year.
On Wall Street, the Dow Jones dropped 354 points, or 2.3%, to close at 14,758, while the S&P 500 had its worst day since November 2011, shedding 2.5%.
-
The economic crisis has caused the United Kingdom to drift apart, creating ever-widening rifts between rich and poor, native and immigrant, English and Scot. With the anti-Europe UKIP party on the rise, Great Britain stands at a crossroads.
-
Competition from China and other low-wage rivals, coupled with fallout from the 2007-09 financial crisis, has put American wages under such unprecedented strain that they have shifted into reverse — not merely stagnating, but falling.
“Water finds its equilibrium, its own level,” said Jeff Joerres, chief executive of Milwaukee-based global staffing giant ManpowerGroup Inc., who refers to this accelerating leveling of wages as “global labor arbitrage.”
Read more: http://www.post-gazette.com/stories/business/news/us-wages-fall-amid-overseas-pressure-692123/#ixzz2WpuIFBiI
-
At one time, it seems decades ago now, the general thinking in the USA was that President Barack Obama would jolt the American political system into actually doing something beneficial for its citizens rather than spying on them, building F-35 aircraft, upgrading nuclear weapons, spending trillions of dollars (US) on national security, cutting unemployment benefits/food stamps, fomenting war with Iran, Syria, China and Russia; and dragging out the war in Afghanistan.
-
Of all the public entities that have fallen victim to the big bank-induced economic downturn, cities have the most compelling stories of being burned. If “all politics is local,” this is even more true for economics, at least where people’s ordinary lives are concerned. City budgets contain the life blood of communities. School districts, contracts with utility companies, waste services, and street repairs all filter locally. City social services are often the first line of response for people in need. City councils also fund soup kitchens, domestic violence shelters, and animal shelters.
-
Privacy
-
The libertarian senator picked up on the dip in support for the POTUS among younger Americans
[...]
Rand Paul is claiming that the youth of America have his back in his battle against Big Brother, reports Politico.
-
The NSA warrantless spying program is only a part of a “vast” American secrecy regime that has developed and expanded since 9/11, former NSA senior official and a whistleblower Thomas Drake has told RT.
Thomas Drake, who worked for the American National Security Agency (NSA) from 2001 to 2008, says he was at the place “from the very beginning” of the development of the mass surveillance program, PRISM, that grants the government access to Internet users’ emails, search results, video chats and other data.
-
Recent revelations of the National Security Agency’s (NSA) data mining capabilities have come to the forefront recently, making “big data” a new subject of interest and concern for many people.
So what better time than now to launch a data analytics tool based on the very technology that the NSA uses to perform its real-time analysis of massive amounts of data being pulled in from sources like the PRISM program?
-
Last week, in Your Computer Is Watching You: AOL Rolls Out Emotion Tracking, I described how YouEye and other firms could use the webcam built into your computer to measure your emotional reactions to videos. There’s nothing nefarious about this program – the participants in the video testing explicitly opt-in to be part of the process. But, with the recent revelations about NSA vacuuming up phone and computer data, one wonders what might be possible with clever engineers and an unlimited budget…
-
After the PRISM leak, you probably want to know exactly what the NSA has on file about you. And here’s some good news amid all the are-we-living-in-a-surveillance-state hand-wringing: Civil rights advocate Jonathan Corbett put together a website called My NSA Records that wants to help you understand what your records looks like.
-
Edward Snowden, the 29-year-old fugitive who revealed the NSA’s PRISM system, has told the technology companies involved in surveillance to stand up for users’ rights and demand a change in the current law.
“If for example Facebook, Google, Microsoft, and Apple refused to provide this cooperation with the Intelligence Community, what do you think the government would do? Shut them down?” he said, during a question and answer session hosted by The Guardian
-
Booz Allen, whose top personnel served in key positions at the NSA and vice versa after the inconvenient collapse of the Cold War, has been attempting to substitute terrorist for communist as the enemy of choice. A difficult switch indeed for the military-industrial complex about which Dwight Eisenhower, the general-turned-president, had so eloquently warned us.
-
Muslim and Arab Americans have been targets of intrusive monitoring programs even when they ‘have nothing to hide’
-
Answering the questions about him being a potential Chinese spy, Snowden said that by calling him a traitor, the US government has destroyed any possibility of a fair trial.
-
-
So, making the assumption that the NSA can eavesdrop on our Internet traffic already, does it really need access to Apple and Google’s server farms? After all, there’s nothing irreproducible about their systems—the rise of cloud computing technologies in recent years means that these companies’ servers are virtual constructs in any case, running on fungible hardware. With enough storage space and computing power, it is certainly technically possible to imagine shadow servers, emulating the relevant functions of a number of companies’ online services, and synchronized with data from Internet backbone taps at telcos. It might not be a perfect copy of what’s on the real servers, but such a system would still allow extensive historical searches in many cases. With such a system, “direct access” versus “intercepting traffic in transit” becomes a distinction without a difference.
-
-
“I’m neither traitor nor hero. I’m an American.” – Edward Snowden
[...]
There are weeks that change the course of human history. There are weeks when people must choose sides. There are weeks that expose the real American traitors. There is no middle ground in this debate. You are either on the side of freedom, liberty, truth, transparency and the U.S. Constitution or you are on the side of mindless obedience, oppression, deception, corruption and tyranny. A courageous young Millennial named Edward Snowden has risked his life and his future to expose the illegal, surreptitious surveillance programs being conducted by the United States government in clear violation of the 4th Amendment to the U.S. Constitution. The NSA, with the full knowledge of Barack Obama and Congress, has been covertly collecting phone and internet records on millions of Americans with the full cooperation of Verizon and other mega media/data corporations. Our owners have been using the U.S. Constitution to wipe their asses. The 4th Amendment to the U.S. Constitution is so unambiguous that any intelligent politician, bright journalist or fifth grader in Miss Sabatini’s history class could interpret its meaning and intention. Our founding fathers believed in truth, clarity and simplicity. The traitorous sociopaths in control of our government today believe in obfuscation, ambiguity and complexity.
-
Michael Dowling, a Denver-based attorney who acted as Zazi’s defence counsel, said the full picture remained unclear as Zazi pleaded guilty before all details of the investigation were made public. But the lawyer said he was sceptical that mass data sweeps could explain what led law enforcement to Zazi.
“The government says that it does not monitor content of these communications in its data collection. So I find it hard to believe that this would have uncovered Zazi’s contacts with a known terrorist in Pakistan,” Dowling said.
Further scepticism has been expressed by David Davis, a former British foreign office minister who described the citing of the Zazi case as an example of the merits of data-mining as “misleading” and “an illusion”. Davis pointed out that Operation Pathway was prematurely aborted in April 2009 after Bob Quick, then the UK’s most senior counter-terrorism police officer, was pictured walking into Downing Street with top secret documents containing details of the operation in full view of cameras.
-
One of the most articulate commentators to come to the defense of the NSA is Thomas Friedman. His recent column in the New York Times epitomizes what bothers me most about this whole affair—the readiness of people who claim to be defenders of an open society to make excuses for people and policies that undermine it.
Friedman argues that although what the NSA is doing is distasteful, we should put up with it because it might stop some future terrorist attack, which in turn, would prompt even more intrusive violations of our freedoms.
-
Russia will not ignore the actions of the US authorities who had admitted leaks of personal data of Russian citizens to which the US security services had access, the Foreign Ministry’s plenipotentiary for human rights, Konstantin Dolgov, said at a special meeting initiated by the Upper House of the Russian parliament.
-
-
Obama and other NSA defenders insist there are robust limitations on surveillance but the documents show otherwise
-
Glenn Greenwald, the Guardian journalist who broke the NSA surveillance story earlier this month, joins us one day after both President Obama and whistleblower Edward Snowden gave extensive interviews on the surveillance programs Snowden exposed and Obama is now forced to defend. Speaking to PBS, Obama distinguished his surveillance efforts from those of the Bush administration and reaffirmed his insistence that no Americans’ phone calls or emails are being directly monitored without court orders. Greenwald calls Obama’s statements “outright false” for omitting the warrantless spying on phone calls between Americans and callers outside the United States. “It is true that the NSA can’t deliberately target U.S. citizens for [warrantless] surveillance, but it is also the case they are frequently engaged in surveillance of exactly that kind of invasive technique involving U.S. persons,” Greenwald says. After moderating Snowden’s online Q&A with Guardian readers, Greenwald says of the whistleblower: “I think what you see here is a person who was very disturbed by this massive surveillance apparatus built in the U.S. that spies not only on American citizens, but the world, with very little checks, very little oversight. He’s making clear his intention was to inform citizens even at the expense of his own liberty or even life.”
-
The former intelligence contractor who leaked documents on US surveillance programmes has defended himself in an online chat, the Guardian reports.
-
National Security Agency discloses in secret Capitol Hill briefing that thousands of analysts can listen to domestic phone calls. That authorization appears to extend to e-mail and text messages too.
-
“You have to assume everything is being collected,” said Bruce Schneier, who has been studying and writing about cryptography and computer security for two decades.
-
The other two types of collection, which operate on a much smaller scale, are aimed at content. One of them intercepts telephone calls and routes the spoken words to a system called NUCLEON.
-
What are secret courts? Why do we need them? To protect Britain’s special relationship with the United States, we are officially told; to protect the credibility and integrity of our intelligence services. Never mind that for decades we have handled security-sensitive cases by clearing the court whenever necessary, and allowing our secret servants to withhold their names and testify from behind screens, real or virtual: now, all of a sudden, the credibility and integrity of our intelligence services are at stake, and need urgent and draconian protection.
-
…massive operation to secretly keep track of everyone’s phone calls on a daily basis…
-
-
Polls conducted in the days since Glenn Greenwald and The Guardian pulled back the curtain on the NSA’s surveillance program have found that a majority of Americans are fine with said program so long as it targets suspected terrorists, but are less fine with being targeted themselves; and that they’re skeptical of the claim that leaking information about the NSA’s spying program will jeopardize the government’s ability to keep America safe.
-
In a landmark ruling, Sweden’s data protection authority (the Swedish Data Inspection Board) this week issued a decision that prohibits the nation’s public sector bodies from using the cloud service Google Apps.
-
It’s a step closer to protecting your electronic privacy… in Texas.
-
WikiLeaks activists in Iceland are discussing with government officials there the possibility of asylum for Edward J. Snowden, the former National Security Agency contractor who disclosed hundreds of classified documents on N.S.A. surveillance, Julian Assange, the founder of the antisecrecy group, said Wednesday.
-
An alternative search engine DuckDuckGo has enjoyed a record surge in traffic as NSA scandals spark fears and frighten away Internet users from the more popular Google or Yahoo!.
Over the previous week DuckDuckGo, a private search engine, which claims not to collect users’ searches or create any personal user profile, has increased its traffic by 26 per cent and passed 3.1 million of direct queries.
-
To make matters worse, DuckDuckGo are not audited by any external body, so we only have their word that they are not an NSA honeypot setup to monitor people that deliberately avoid Google on privacy grounds (exactly the type of people the NSA are interested in) and we only have their word that their privacy policy is upheld – frankly Gabriel, that is not good enough.
For the above reasons, I once again turn my old friends at Ixquick. If you are looking for a private search engine, you cannot do better than Ixquick and Startpage at this time – they have been audited and certified by Europrise, they are not based in the US and therefore not under the jurisdiction of FISC and I know them personally and know that they stand by their word. They haven’t paid me to say this, so no, this isn’t some profit making scheme by me, but the facts are as they stand – it is literally impossible to trust that your data is private and secure if you use a company that has any legal ties to the United States. That means Cloud, Email, Blogs, ECommerce, Hosting, Image Galleries, Microblogs, Voice over IP, Instant Messaging, Social Networking – yes absolutely -everything- which makes up our digital society. If you still don’t quite understand what that means, GMail, Hotmail, Skype, Facebook, Twitter, Dropbox, Crashplan, Blogger, Google Search, Bing, Yahoo Mail etc. are all inherently insecure as a direct result of the Foreign Intelligence Surveillance Act, the PATRIOT Act, the National Security Agency and PRISM – and that is before we even start to discuss CALEA and whether or not your broadband router has a built in back door…
-
Fisa court submissions show broad scope of procedures governing NSA’s surveillance of Americans’ communication
-
-
“National security” agencies and major tech sectors have teamed up to make Big Brother a reality. “Of the estimated $80 billion the government will spend on intelligence this year, most is spent on private contractors,” the New York Times noted. The synergy is great for war-crazed snoops in Washington and profit-crazed moguls in Silicon Valley, but poisonous for civil liberties and democracy.
-
The US PRISM internet surveillance case highlights the urgent need to pass legislation to protect EU citizens’ personal data, most MEPs agreed in Wednesday’s Civil Liberties Committee debate with Justice Commissioner Viviane Reding. MEPs also called for safeguards for personal data transferred outside the EU.
-
USA Today has published an extraordinary interview with three former NSA employees who praise Edward Snowden’s leaks, corroborate some of his claims, and warn about unlawful government acts.
-
When it comes to surveillance rules, some US people are more equal than others.
-
There are still people warning us of sleepwalking into a Stasi or “1984” society. They missed the boat by a long shot: we are already far, far past the point of Stasi or “1984”. The apparatus that governments have built to trace, track, and record citizens is the stuff of nightmares.
-
So now the penny drops, and we all know why GCHQ has long refused to allow government departments to store information classified at “Restricted” or above in US cloud computing services. But what about the private sector? Well, Edward Snowden’s revelations are now causing something of a crisis in the IT industry as its international customers start thinking through the implications. In the past week I’ve heard of big firms reconsidering plans to spend hundreds of millions on services that would have been hosted in the US, as they start to realise that US agencies might snoop on their data and use it to tip off their competitors. US service firms now fear this will harm their growth, and it’s not just Microsoft and Google; many other companies such as Amazon, Salesforce and Rackspace could lose out.
-
President Obama, the former college lecturer on constitutional law, got a lecture on privacy rights Wednesday from German Chancellor Angela Merkel and faced tough questions from the German press about his perceived failure to be less warlike after winning the Nobel Peace Prize.
Mrs. Merkel raised the subject of National Security Agency surveillance of the Internet in a private meeting with Mr. Obama in Berlin, where she emphasized the need for “proportionality.”
-
Russ Tice, a former intelligence analyst and Bush-era NSA whistleblower, claimed Wednesday that the intelligence community has ordered surveillance on a wide range of groups and individuals, including high-ranking military officials, lawmakers and diplomats.
He also made another stunning allegation. He says the NSA had ordered wiretaps on phones connected to then-Senate candidate Barack Obama back in 2004.
“They went after–and I know this because I had my hands literally on the paperwork for these sort of things–they went after high-ranking military officers; they went after members of Congress, both Senate and the House, especially on the intelligence committees and on the armed services committees and some of the–and judicial,” Tice told Peter B. Collins on Boiling Frog Post News.
-
If you use privacy tools, according to the apparent logic of the National Security Agency, it doesn’t much matter if you’re a foreigner or an American: Your communications are subject to an extra dose of surveillance.
Since 29-year-old systems administrator Edward Snowden began leaking secret documentation of the NSA’s broad surveillance programs, the agency has reassured Americans that it doesn’t indiscriminately collect their data without a warrant, and that what it does collect is deleted after five years. But according to a document signed by U.S. Attorney General Eric Holder and published Thursday by the Guardian, it seems the NSA is allowed to make ambiguous exceptions for a laundry list of data it gathers from Internet and phone companies. One of those exceptions applies specifically to encrypted information, allowing it to gather the data regardless of its U.S. or foreign origin and to hold it for as long as it takes to crack the data’s privacy protections.
-
Contradicting a statement by ex-vice president Dick Cheney on Sunday that warrantless domestic surveillance might have prevented 9/11, 2007 court records indicate that the Bush-Cheney administration began such surveillance at least 7 months prior to 9/11.
The Bush administration bypassed the law requiring such actions to be authorized by FISA court warrants, the body set up in the Seventies to oversee Executive Branch spying powers after abuses by Richard Nixon. Former QWest CEO John Nacchios said that at a meeting with the NSA on February 27, 2001, he and other QWest officials declined to participate. AT&T, Verizon and Bellsouth all agreed to shunt customer communications records to an NSA database.
-
For defense contractors, the government officials who write them mega checks, and the hawks in the media who cheer them on, the name of the game is threat inflation. And no one has been better at it than the folks at Booz Allen Hamilton, the inventors of the new boondoggle called cyber warfare.
-
Two US congressmen introduced a bill on Thursday compelling the Obama administration to declassify the secret legal justifications for the wide-ranging surveillance programs run by the National Security Agency.
The disclosure bill, a complement to one pushed in the Senate last week, is the latest in a series of legislative attempts to rein in the NSA’s collection and analysis of Americans’ phone records and, potentially, Internet usage.
-
-
-
Avoid Prism and the NSA with the Electronic Frontier Foundation’s guide to maintaining your privacy – comprised of free and open source software
-
-
-
The French data protection authority, CNIL, has today announced that Data Protection Authorities from France, Germany, Italy, the Netherlands, Spain and the United Kingdom have respectively launched enforcement actions against Google.
-
The Apple co-founder Steve Wozniak has backed NSA whistleblower Edward Snowden and admitted he feels “a little bit guilty” that new technologies had introduced new ways for governments to monitor people.
“I felt about Edward Snowden the same way I felt about Daniel Ellsberg, who changed my life, who taught me a lot,” he said.
Speaking to Piers Morgan on CNN he said he was not the kind of person to “just take sides in the world – ‘I’m always against anything government, any three letter agency,’ or ‘I’m for them’.”
-
Thursday 6 June, the day the PRISM story broke, was a good day to be a cryptographer. The sudden prospect of mass, unwarranted surveillance delivered an electric shock to thousands who were now looking for ways to protect their privacy online. At Cryptocat, we saw nearly 5,000 new individuals starting to use our free encrypted chat software. Other privacy and encryption services saw a rise of as much as 3,000 per cent in new users. – See more at: http://newint.org/blog/2013/06/21/prism-surveillance-nsa-software/#sthash.bP6q2IQe.dpuf
-
Music veteran also says MP3s ‘sound like shit’ and journalists are ‘very problematic’ in first appearance since liver transplant
-
-
-
The independent senator Nick Xenophon is pressing for answers about whether Australian parliamentarians are being watched by intelligence agencies in the wake of revelations in the Guardian about the US Prism programme.
-
The founder of the world’s biggest marketing services company, Sir Martin Sorrell, has said he believes revelations about the National Security Agency’s Prism internet surveillance programme are a “game changer” that will spark a fundamental rethink of web privacy by web users.
-
-
Leaked documents have revealed how the United States’ National Security Agency (NSA) is able to gather and use information on US citizens.
-
-
The Guardian released new details about the National Security Agency’s spying practices, which reveals how analysts can store vast sums of data without a warrant. Specifically, if the NSA “inadvertently” stumbles upon anything related to a potential crime, it can store the data for later investigations.
Quite reasonably, the Supreme Court has declared that law enforcement can charge citizens with a crime if it’s being conducted in “plain sight“–e.g. if cops see pot sitting in the passenger seat of a car during a traffic stop. That is, the presumption of innocence doesn’t apply to if police inadvertent witness a crime. Unfortunately, the scope of the presumption of innocence gets tinier as the government’s eyes get bigger.
-
The National Security Agency may keep Americans’ emails and phone calls if they’re “believed to contain significant foreign intelligence,” secret papers show.
The world’s largest spy agency may also keep U.S. citizens and legal residents’ domestic communications if NSA analysts believe the communications could suggest evidence of a crime, the documents published Friday by British newspaper The Guardian and The Washington Post indicated.
-
Two secret documents describing the procedures the National Security Agency (NSA) is required to follow when spying on foreign terror suspects reveal the provisions that allow the agency to collect, retain and use information on U.S residents without a warrant, The Guardian newspaper reported today.
-
The National Defense Authorization Act recently approved by the House would build on powers currently available to government to allow unrestricted access to all personal data collected “during combat operations from countries, organizations, or individuals, now or once hostile to the United States,” political analyst Stephen Benavides reports at Truthout.
The data are known officially as “captured records” and include any kind of personal file belonging to parties deemed to be in conflict with the United States. Of course, the war on terror’s expanding battlefield means those records do not have to be collected outside of the United States.
-
Passed in 1978, the Foreign Intelligence Surveillance Act (FISA) set the groundwork for surveillance, collection, and analysis of intelligence gathered from foreign powers and agents of foreign powers, up to and including any individual residing within the U.S., who were suspected of involvement in potential terrorist activity. On October 26, 2001, a little over a month after 9/11, President George W. Bush signed the USA Patriot Act into law. Two provisions, Sec. 206, permitting government to obtain secret court orders allowing roving wiretaps without requiring identification of the person, organization, or facility to be surveyed, and Sec. 215 authorizing government to access and obtain “any tangible thing” relevant to a terrorist investigation, transformed foreign intelligence into domestic intelligence.
-
-
Civil Rights
-
-
-
The streets of central Rio de Janeiro and dozens of other cities echoed with percussion grenades and swirled with teargas last night as ranks of riot police scattered the biggest demonstrations Brazil has seen for more than two decades.
As a minority of protesters threw rocks, torched cars and pulled down lamp-posts, the police fired volleys of pepper spray and rubber bullets into the crowd and up onto overpasses where car drivers and bus passengers were stuck in traffic jams. At least 40 people were injured in the city and many more elsewhere.
A vast crowd – estimated by the authorities at 300,000 and more than a million by participants – filled Rio’s streets, one of a wave of huge nationwide marches against corruption, police brutality, poor public services and excess spending on the World Cup.
-
Protests have popped up across the globe in recent years, but government response has varied. Rousseff’s approach contrasted with the adversarial position of Turkey’s Erdogan, for example.
-
For decades, California’s political leaders have tried every imaginable approach to dealing with its overcrowded prisons – sending inmates out of state, fighting the federal courts all the way to the U.S. Supreme Court, promising more prison beds and insisting that it has done plenty to cut inmate populations and improve health care.
-
Calls for the doctors who force-feed hunger-striking prisoners at Guantánamo Bay to refuse to perform the practice on ethical grounds have got nowhere, a spokesman for the prison said on Thursday.
-
Internet/Net Neutrality
-
In a user forum on Verizon’s website, a couple users claim their Netflix instant streaming quality has been on the decline. Some claim to continue to experience problems even after contacting Verizon’s customer service agents and working with them to resolve it.
-
Intellectual Monopolies
-
The House of Commons may have adjourned for the summer, but just hours before breaking, the government filed its response to the Standing Committee on Industry, Science and Technology’s report on the Intellectual Property Regime in Canada. That may sound dry, but the document provides a clear indication of what the government has planned for the coming years on IP reform.
So what’s in store? Leaving aside an assortment of promised studies on international best practices, improving patent quality, and improving research and development, the government response includes five notable plans (or non-plans).
-
Copyrights
-
Following a trial spanning two weeks, the Stockholm District Court has just handed down its sentence in the Gottfrid Svartholm hacking case. The 28-year-old was found guilty of hacking into Logica, a company carrying out work for local tax authorities, and sentenced to two years in jail. Another man, said to be his accomplice, was sentenced to probation.
-
The co-founder of file-sharing website The Pirate Bay has been sentenced to two years in prison for hacking into the computers of a firm that administers data for Swedish authorities, and for making illegal online money transfers.
Permalink
 Send this to a friend
Send this to a friend
Posted in Microsoft at 4:55 am by Dr. Roy Schestowitz
FSFE now runs this campaign against Xbox One:
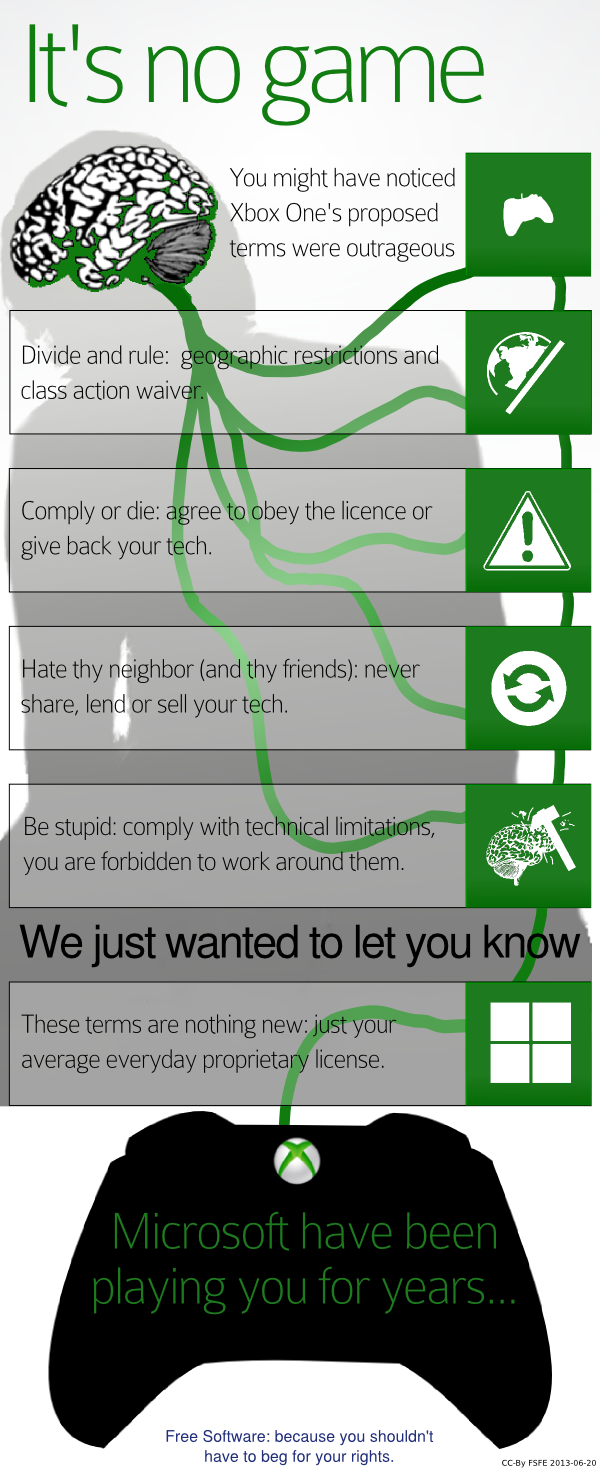
Summary: Microsoft to use peripheral devices and VOIP to carry out audio-visual surveillance in people’s own homes
MICROSOFT HAS an ongoing PR campaign trying to paint itself as a champion of privacy, never mind if NSA leaks reveal Microsoft to be the company that kickstarted PRISM (it is listed as first). To make matters worse, the other PR campaign, which entered the realm of the illegal [1, 2] as Microsoft hired agents to do AstroTurfing, is promoting the Orwellian Xbox One, a device designed to spy on the users in notorious ways, with a camera in the living room too (patents suggest it will be used for spying and other patents say the same about Microsoft wearable devices). The spying features in Xbox One are so malicious that massive backlash pressured Microsoft to backtrack, or as Masnick’s site put it, Microsoft capitulates.
What about Skype, which is probably one of Microsoft’s worst bits of spyware (Microsoft made it worse after it had bought it)? Well, the latest NSA leaks and the leaker too show us that Microsoft is lying. To quote RT:
Microsoft may have misled millions of Skype users around the world by making claims last year that have since been contradicted by intelligence leaked by former NSA contractor Edward Snowden.
National Security Agency documents leaked by Snowden to the Guardian and Washington Post last week have grabbed the attention of Americans concerned over the NSA’s blanketing surveillance of communications involving United States citizens. The NSA is regularly retaining the phone records for millions of Verizon customers, the documents revealed, and a separate program called PRISM allegedly lets federal investigators access Internet use information for customers of the biggest online services. One of those documents, a slideshow examining how the NSA has access to conversations conducted over nine major Internet services, may have caught Silicon Valley giant Microsoft in a lie.
Ryan Gallagher of Slate noted this week that one of the slides cited by the Washington Post was labeled a “User’s Guide for PRISM Skype Collection,” suggesting that the NSA has in place a method for eavesdropping on conversations conducted over the popular Web client acquired in 2011 by Microsoft.
According to the slide, NSA agents can listen in or watch Skype chats “when one end of the call is a conventional telephone and for any combination of ‘audio, video, chat, and file transfers’ when Skype users connect by computer alone.”
Thank you for this clarification. So Microsoft is, indeed, worse than its child Facebook, which also promotes Skype by the way (Microsoft owns part of Facebook).
No company is worse on security than Microsoft. For crying out loud, Microsoft tells the NSA how to hijack people’s — let alone businesses and governments — PCs (with hard drives and everything). █
Permalink
 Send this to a friend
Send this to a friend
Posted in Finance, Microsoft at 4:38 am by Dr. Roy Schestowitz

Summary: Intellectual Ventures moves into the public arena in attacking Linux/Android
The pyramid scheme and racketeering operation known as Intellectual Ventures should really be dealt with as though it’s a criminal operation, but in the age of corporate power and war on dissent do not expect Obama to do anything. He is too busy talking about small trolls [1, 2, 3] and we sure hope he’ll crack down on this massive one that came from Bill Gates and Microsoft. Groklaw reveals that this trolls is now going directly — not indirectly as before — after the leading Linux-based operating system. We saw that coming. To quote:
This one is brought by Intellectual Ventures against Motorola in Florida. Here’s the complaint [PDF]. They are already suing Motorola in Delaware. Why not just add them to the Delaware case, if it needs shoring up? Maybe because this way, they get two tries at the golden ring on this merry-go-round, and if Google tries to consolidate the cases, they have to pay lawyers for that extra work, and if the effort fails, they have to pay two teams of lawyers to go to two different states to protect Motorola. Lawyers do know how to be annoying if they want to be. If the goal is to sue someone, like Google, let’s just say, until they scream Uncle and pay up, they might just do so. Not that Google ever does. It has a fabulous record of success in patent defense, and they have done it repeatedly even without counterclaims, so in that sense, part of the benefit expected from using a troll to go after Google is probably lost.
This is probably a case we’ll hear a lot more about. Troll Tracker, a site whose author I occasionally speak to, did some work to expose this troll and its author now says: “This is why the idea of a place to track troll activity is a good one. There’s lots of information to track, but one of the first things is demand letter information. Let’s build a picture of what these guys look like before they show themselves to the public via an actual lawsuit. Yeah, I know. They hide behind shell companies. Well, guess what? I happen to know a few folks with mad data mining skillz who can prove up the data behind the scenes. Cross reference locations, patents asserted, law firms used to send the shakedown letter, etc. and use a little heat mapping and investigative skills to triangulate who these people are and who they’re going after and how to best mitigate against the threat. It will take time, and it will take patent demand letter data.”
It would be valuable to have the list of ~2,000 shell companies of Intellectual Ventures.
Meanwhile, over in Germany, the patents debate gets heated, with software patents facing the possibility of complete ban. FSFE plays a commendable role in this and it means that Europe as a whole may stay resistant to patent trolls, for now. Remember that the patent trolls’s weapon of choice is software patents; it has been shown statistically. █
Update: Guess where Intellectual Ventures’ patents came from. They came from Microsoft Nokia, says this report. It’s all becoming rather obvious now. We also learn from this news that Nokia might soon officially become part of Microsoft. Well, it’s already in Microsoft’s hands, just like Yahoo, and when it comes to acquisition by Microsoft, we heard it before (Microsoft had considered doing that in the past. iophk, however, calls it “pump -n- dump”.
Permalink
 Send this to a friend
Send this to a friend
« Previous Page — « Previous entries « Previous Page · Next Page » Next entries » — Next Page »




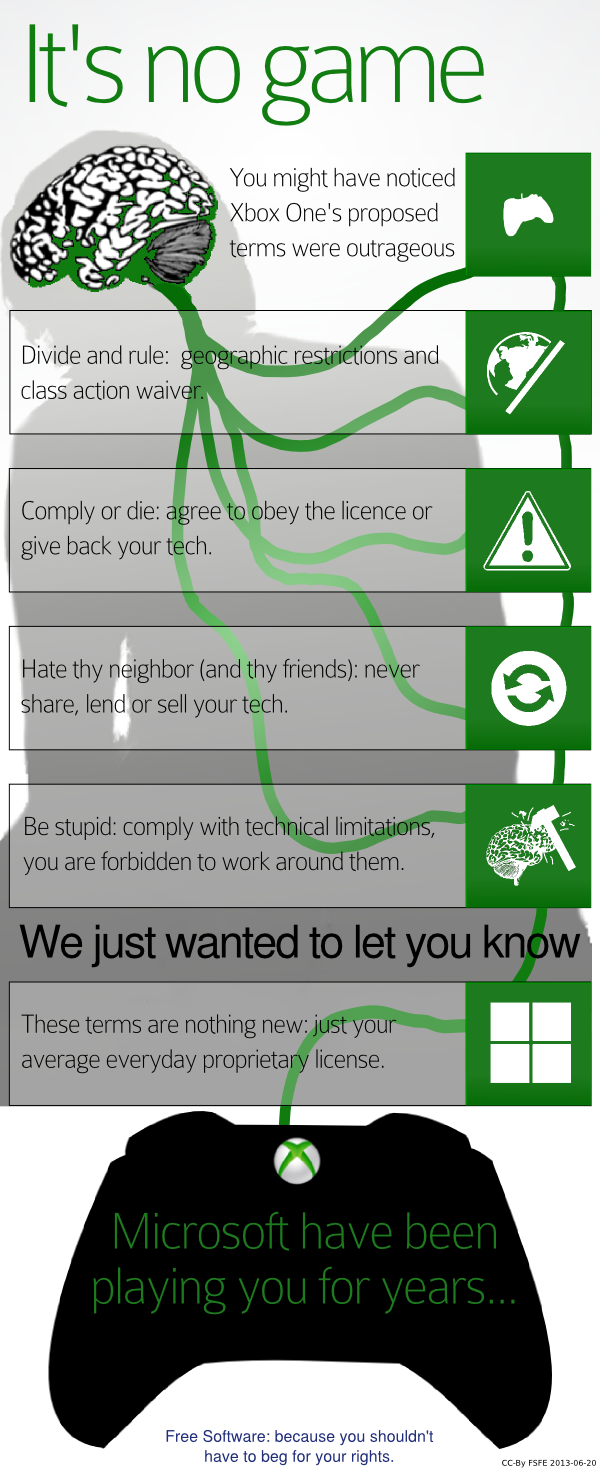

















 Content is available under CC-BY-SA
Content is available under CC-BY-SA