11.28.13
Posted in Action at 8:59 am by Dr. Roy Schestowitz
Summary: New scandals involving the NSA, including COINTELPRO-like targeting by the NSA
RECENT bombshells from Snowden et al. revealed a high degree of criminality in the NSA, which infects computer networks [1]. Perhaps they can no longer accuse China of doing such things. But to what degree have governments other than the United States’ played in all this? Well, there’s allegation that Canada’s government is now part of the same institutional corruption [2]. Other US allies, even neighbours of China (where the majority of the nation is of Chinese descent), may be complicit [3]. The high degree of state surveillance [4] is being studied [5] and citizens in the United States (not to be confused with the government) want some answers [6,7,8] about the NSA’s facilities. Networks got compromised [9], essentially subverting any notion of security [10]. Now we have it confirmed that the NSA used information it had gathered for blackmail [11-14]. This is a huge deal as it makes complicit nations accomplices in the act. Back in the days of COINTELPRO, the FBI used surveillance in an attempt to drive Martin Luther King to suicide. █
Related/contextual items from the news:
-
A presentation slide provided by Edward Snowden and published by the Dutch media outlet NRC on November 23 shows that the NSA has infected more than 50,000 computer networks worldwide with malicious software designed to steal sensitive and private information.
-
The NSA used U.S. Embassy in Ottawa as command post during summits
-
-
With revelations of spyware planted on 50,000 networks, the “Five Eyes” states have been allowed to trample over their citizens’ privacy for far too long
-
The MetaPhone project asks volunteers to install an Android app that sends the researchers copies of a device’s call logs and basic data from a person’s Facebook account. The researchers say that a large collection of such data will make it possible to use data-mining techniques to discover which aspects of people’s lives—as recorded in their Facebook data—can be revealed by examining just their calling and texting logs.
-
-
-
Bluffdale agreed to sell water to the National Security Agency at a rate below its own guidelines and the Utah average in order to secure the contract and spur economic development in the town, according to records and interviews.
-
As other countries push for more control over the Internet, “you’re going to see national boundaries begin in cyberspace,” said Jason Healey, director of policy group Cyber Statecraft Initiative at the Atlantic Council, according to Bloomberg.
-
That’s not to say that the NSA has “broken” all cryptography: “the math works,” says Schneier, and while anonymizing tools like Tor are targeted by NSA, they seem to remain secure. Instead, the NSA appears to have manipulated encryption tools and tapped into data center links and fiber backbones—in essence, silently removing the hinges from their doors.
-
The US authorities have studied online sexual activity and suggested exposing porn site visits as a way to discredit people who spread radical views, the Huffington Post news site has reported.
-
-
-
The disclosures from the Snowden files keep on coming, with each revelation more disturbing than the last. The latest report reveals a plan by the National Security Agency to collected information on six people’s online activity, particularly their visits to pornographic websites, to discredit them within their community.
This is an example of “how ‘personal vulnerabilities’ can be learned through electronic surveillance, and then exploited to undermine a target’s credibility, reputation, and authority,” activist Glenn Greenwald wrote in the Huffington Post on Tuesday evening.
Permalink
 Send this to a friend
Send this to a friend
Posted in Action at 8:33 am by Dr. Roy Schestowitz
Summary: Why the paramilitaries need to be chased out of the state, for they only reduce national security and increase human toll
Paramilitaries are typically the tools of tyrants, but now even the United States has them, and they’re out of control [1]. They do illegal things [2] and the government has no power or even the will to stop them. Those who expose the paramilitaries [3-7] say that the leaders should be tried for murder [8] of thousands [9].
Recent developments in Iran [10] teach us that the paramilitaries have lied to us [11]. The paramilitaries are torturing innocent people in pursuit of the threat that makes paramilitaries seem necessary and the paramilitaries won’t let the public know the truth [12,13,14]. It is rather telling. The paramilitaries just want to recruit some spies [15], so they detain innocent people (with strong opinions) and make a farce of the legal system [16]. The paramilitaries’ power is derived from our fears and the phantom enemies which they create by provocation (assassinating many people without trial). Those paramilitaries have ties with Wall Street and they would rather we focued on phantom enemies rather than on those who steal trillions of dollars from us (robbing us blind).
The Western states are being taken over by paramilitaries. We need to take the state back from them. In the next post we’ll show the latest NSA scandals (aside for playing a role in thousands of assassinations without trial). █
Related/contextual items from the news:
-
For a long time, the Central Intelligence Agency was in the otherwise quiet business of doing what still lingers in popular consciousness as the stuff of, well, the CIA: Intelligence gathering. Data collection, sifting, and analysis. You know, wonky spy shit.
-
“When armed drones kill unarmed, innocent civilians, there is a clear breach of international law,” Ambassador Masood Khan said while explaining Pakistan’s position on the draft approved by the General Assembly Third Committee which deals with social, humanitarian and cultural questions.
-
-
-
The Pakistan political party led by former cricketer Imran Khan has named a man it claims is the CIA’s top operative in the country and called for him and the head of the agency to face trial over a recent missile strike.
The CIA would not confirm the Islamabad station chief’s name and declined to comment on the move by the Pakistan Tehreek-e-Insaf party.
-
-
-
-
-
Here’s a recent interview I did about the recent Iran nuclear deal, adding some context and history and trying to cut through some of today’s media myths
-
It’s been hailed as a breakthrough agreement that could thaw Iran’s relationship with the West. Days of intensive discussions in Geneva resulted in concessions from Iran to reverse its nuclear programme in return for a reduction in economic sanctions imposed by the world’s powers. It’s a remarkable deal that a year ago no-one would have seen coming, least of all the writers of Homeland.
-
The ACLU filed the suit on Tuesday under the Freedom of Information Act (FOIA) demanding the Central Intelligence Agency release two reports about its post-9/11 “program of rendition, secret detention, and torture of detainees”
“This illegal program was devised and authorized by officials at the highest levels of government, and five years after it officially ended, the American public still doesn’t have the full story about some of the most devastating rights violations committed in its name,” the ACLU said in a statement.
-
This week, the American Civil Liberties Union filed the second Freedom of Information Act lawsuit intended to pry loose the Senate Permanent Select Committee on Intelligence study, as well as the CIA’s response. Judging from history, the dispute will take a long time to resolve. So far, moreover, courts often have assented when the president’s emissaries demand secrecy in the name of national security.
-
-
When prisoners began streaming into the prison on the U.S. naval base at Guantanamo Bay in January 2002, the CIA recognized it as an unprecedented opportunity to identify sources. That year, 632 detainees arrived at the island. The following year 117 arrived.
-
But he later told the court that, as the severity of the diversion became apparent, he tried to reverse this decision by telling air traffic control the men were “laughing and joking”.
Permalink
 Send this to a friend
Send this to a friend
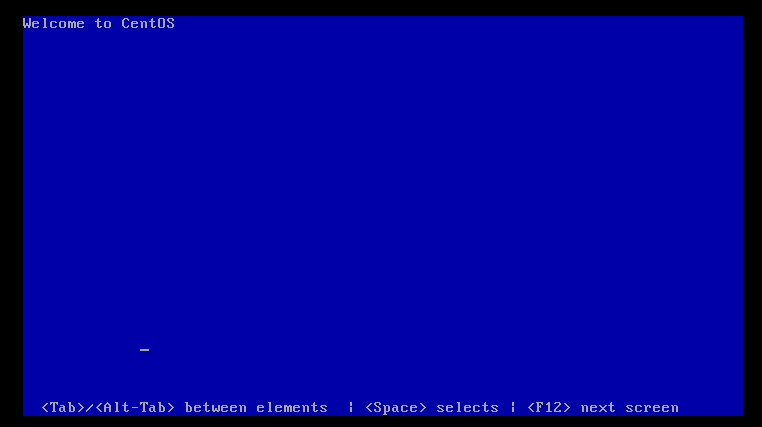
Posted in GNU/Linux, Hardware at 7:58 am by Dr. Roy Schestowitz
Rebranding and plurality
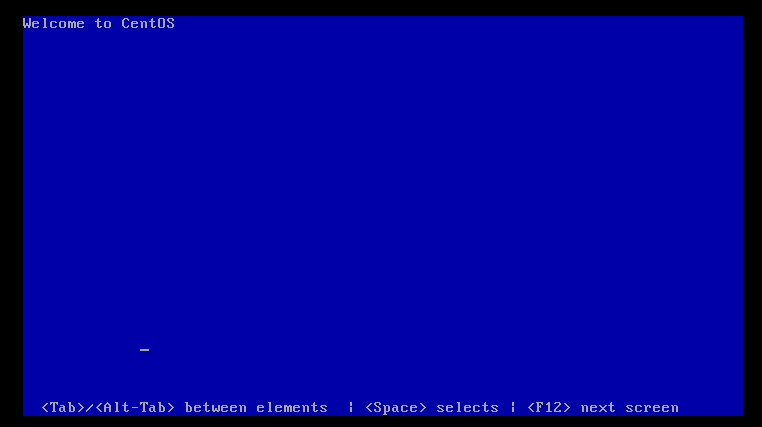
Summary: The back end of enterprises is being accommodated by more and more brands, not just in software but also hardware
Supercomputers are the area most prominently ruled by GNU/Linux. GNU/Linux has bragging rights in this area [1] and the press should not shy away from GNU, as it so habitually does [2]. There are companies built around this area [3] and they ensure development of faster and more potent file systems. It should not be surprising that GNU/Linux also expands to other heavy-duty datacentre tasks such as communications [4] and web servers [5].
It should be noted that something rather fascinating is happening as a result of GNU/Linux expansion in the server side. Whereas Windows mostly sustained x86 monoculture, with GNU/Linux we see expansion to Power, ARM, and many more minority architectures (some are dying breeds). Based on [6-9], big GNU/Linux distro makers now target ARM, which tends to be more energy-efficient and “ethical” than x86 (Intel is a corrupt company).
In a sense, GNU/Linux domination in the back room is contributing to the elimination of not just software monopolists but also hardware monopolists. █
Related/contextual items from the news:
-
-
-
Cray’s expert storage solutions are now available for popular x86 Linux clusters. Cray Cluster Connect (C3) offers a complete Lustre storage solution for x86 Linux. C3 brings Supercomputing-class scalability to data- and I/O-hungry Linux clusters.
-
Univention GmbH, one of Europe’s leading suppliers of Open Source products for the cost-efficient operation and efficient administration of IT infrastructures (www.univention.de), has now launched Release 3.2 of its enterprise Linux distribution Univention Corporate Server (UCS).
-
-
Boston Limited has announced a new server based on ARM processors and certified to run Ubuntu Linux 13.10, a move that could further stir up growing interest in ARM servers.
-
-
-
Permalink
 Send this to a friend
Send this to a friend
11.27.13
Posted in Free/Libre Software, OSI at 12:22 pm by Dr. Roy Schestowitz
Vulnerable terms die hard
Photo by Brian Solis
Summary: Free/libre software — unlike “Open Source” — highlights the main strength of code people are sharing among one another
WHEN it comes to freedom-respecting hardware, an explanation to the public about the benefits is relatively simple. Many refer to particular actions as “unlocking” or “jail-breaking”, so there is also familiar terminology one can use. The words “free” and “freedom” would have been very helpful in this context, but the “Open Source” movement sought to bury those words.
Nowadays it’s rather common to see articles about the subject accompanied by terms like “open-source” or “Open Hardware” (misnomers because they overlook the main benefit). Some refer to it as a matter of “control” [1]. use it as a metaphor for a process [2], a financial model [3], a business model [4], and even ecosystems [5]. There are many other new articles about it [6-10] and few actually have anything to do with source code.
By going along with a term like “open source” — a term originally coined and used by the spies (like the NSA) to mean something completely different — the “Open Source” movement made itself susceptible to brand dilution and confusion. Companies like Microsoft now call “open” some of their proprietary software products and formats. █
Related/contextual items from the news:
-
Matthew Casebeer Computer Scientist for MAYA Design, a consulting group that’s focused on simplifying devices and data. He finds that open source design benefits all who share information through their devices, not just computer scientists that work on fixing problems for large groups of users.
-
Six years ago, Maggie Vail and Jesse von Doom launched CASH Music, a nonprofit with the express goal of building open-source tools to help musicians reach their audience—and make a living. Vail originally cut her teeth at the Kill Rock Stars label, while von Doom’s background was in web development. Both wanted to streamline the musician-to-audience experience. And so they made the CASH (which stands for Coalition of Artists and Stakeholders) platform open-source, allowing artists and labels to build networks in their own unique and flexible ways.
-
Open-source capitalism is the same exact thing that made early America a successful nation to begin with.
-
Proof that open source can pay arrived today in the guise of Cambridge bioinformatics company, Eagle Genomics, who closed a £1 million funding round that it said would allow it to further develop its core platform technology and scale up operations including a doubling of staff.
Having started in human health and expanded into the areas of crop science and personal hygiene, the company also plans to move further into non-traditional areas for bioinformatics such as consumer goods, food safety and animal health.
-
The Open Source Beehives Project aims to lower the barriers to backyard beekeeping with simple, low-cost hive designs. With bees dying by the millions, they need to spread the buzz.
-
-
When your last smartphone started to get a little long in the tooth, you probably just bought a new one. Maybe you kept the old one around as a backup. Maybe you recycled it. But, chances are, whatever you did, you didn’t physically upgrade the thing. You didn’t toss in more memory or a new processor or any aftermarket parts.
-
-
If like me you would prefer to be dining something else rather than mowing the lawn, you might be interested in this awesome open source Arduino mower which brings a little more fun back to moving your yard and has been under development for some time.
-
Permalink
 Send this to a friend
Send this to a friend
Posted in News Roundup at 11:48 am by Dr. Roy Schestowitz
-
Python, the programming language, is an open source, volunteer-driven project. Historically viewed as a scripting language (think: slow), the Python of today has developed into a robust and responsive language for the enterprise and other open initiatives around the world—with a Foundation to boot that reinvests money into the community and works to attract newcomers.
-
There is no doubt that the Oak Ridge Leadership Computing Facility’s (OLCF’s) Titan, the nation’s most powerful supercomputer, gets its kick from its 18,688 GPU accelerators. On Titan, GPUs operate in tandem with CPUs to simulate groundbreaking scientific research at breakneck speeds. Now, the OLCF is working with Mentor Graphics, a leading electronic design automation company, to bring accelerated computing to a broader audience.
-
The API originally came as a limited developer preview, which was only open to Glass-owners, Google said, because “to develop great experiences and effectively test them, you need to have Glass”.
-
For the fourth year in a row, Google has organized its Code-in contest for pre-university students to contribute to open source projects.
-
Most devs end up using a huge amount of open-source code in their projects, so giving back to these projects only makes sense.
-
-
-
-
I leave out .NET on my own philosophical grounds where I believe you should not be tied to an operating system, particularly one of a monopolist. If you can get past that objection then I would add it to the list since a lot of civic governments IT departments are currently Windows shops. Look I understand you know and love {insert favorite tech here} but if your goal is to really help civic governments, then make life easy for them, not for you.
I put PHP first because it is everywhere and easy for people to pick up and use. There are a bazillion books on it, there are tutorials all over the web, there are plenty of hosting providers, and it is easy to find people who know it outside of the tech hubs in the US. Java is next because most Computer Science departments teach their students Java, it is stable, there are tutorials for it all over the web, it is used by large enterprises and small shops so it may be in the government IT shop already, and there are libraries for almost anything you want to do. Finally, I put Python in the list because it meets the needs of those who like dynamic languages, it is mature and stable, it is the programming language to extend quite a few desktop applications, it is relatively easy to read and learn, plus there are tons of books and tutorials, and it also has a lot of libraries to carry out almost any function you want.
-
Last year Intel proposed a tool to auto-convert C++ code into C++11 compliant code. The last time I wrote about this automatic code migrator it was called the C++11 Migrator and was still making steady progress, but that was months ago. Today we have an update on this useful utility now known as the C++ Modernizer and can auto-convert large amounts of code.
-
Coders are the new rock stars! And next week, 25-30 November, is Europe Code Week. Today a guest blog from Alja Isaković, one of my young advisors from Slovenia – plus my video message welcoming all those taking part.
“I have this great business idea, but no technical skills to build it.” This is exactly what I kept hearing all over again when reading hundreds of applications from women, age 14 to 64, who signed up for Rails Girls in Ljubljana and were eager to learn more about how the internet works. Can you imagine what would happen if we gave even a small percentage of those ideas a chance to see the light of the day?
-
Gambas is an open-source development environment based on a Basic interpreter and with support for object extensions. It’s been compared to Visual Basic, but Gambas supports Linux and is GPLv2 software.
Permalink
 Send this to a friend
Send this to a friend
Posted in Free/Libre Software at 11:44 am by Dr. Roy Schestowitz
Summary: Espionage, warrantless interception, and other illegal activities highlight the need for freedom-respecting software (with ethics built in)
THE CRIMINAL, villainous operations of the NSA just keep getting worse. More so-called ‘allies’ turn out to have been stabbed in the back. Based on [1,2], we in the UK are under NSA surveillance in a wholesale fashion (no discrimination) and the NSA goes after civil disobedience by means of shaming, e.g. espionage and blackmail [3]. It’s like COINTELPRO all over again, but this time it’s international and it targets many groups.
US politicians are growingly uncomfortable about it [4] and so are European politicians [5]. Those who were complicit are getting negative publicity [6,7] as there is clear abuse of the law (using anti-terror pretext for corporate purposes [8]) at huge but secret expense to the public [9].
Those who publish the facts receive an award [10], those who repeat propaganda get educated [11], and FOSS developers are working on solutions right about now [12,13,14].
The NSA has helped show why Free software is essential; without it, there is no trust and there is a lot of complicity/collusion. Secrecy is often an indication of misconduct. We need to fight secrecy. █
Related/contextual items from the news:
-
Verizon, BT, Vodafone, Level 3 ‘let NSA hook into Google, Yahoo! fiber’ • The Register
-
-
The National Security Agency has been gathering records of online sexual activity and evidence of visits to pornographic websites as part of a proposed plan to harm the reputations of those whom the agency believes are radicalizing others through incendiary speeches, according to a top-secret NSA document. The document, provided by NSA whistleblower Edward Snowden, identifies six targets, all Muslims, as “exemplars” of how “personal vulnerabilities” can be learned through electronic surveillance, and then exploited to undermine a target’s credibility, reputation and authority.
The NSA document, dated Oct. 3, 2012, repeatedly refers to the power of charges of hypocrisy to undermine such a messenger. “A previous SIGINT” — or signals intelligence, the interception of communications — “assessment report on radicalization indicated that radicalizers appear to be particularly vulnerable in the area of authority when their private and public behaviors are not consistent,” the document argues.
-
“They who would give up essential liberty, to purchase a little temporary safety, deserve neither liberty nor safety.”
-
-
-
An interview on the German mainstream TV channel ARD. The programme is called FAKT Magazin:
-
-
A cryptic comment in a police report is raising questions about whether the United States’ National Security Agency spied on internet tycoon and New Zealand resident Kim Dotcom.
-
Documents released by the U.S. National Security Agency in the last couple of months, following successful Freedom of Information Act (FOIA) requests as part of a new crowdsourcing project called SpyLighter, reveal the agency purchased products from Packet Forensics and VUPEN Security in 2010 and 2012. The two companies are well known for selling Internet surveillance technology and software exploits to governments and businesses world-wide.
-
-
That’s worth keeping in mind any time someone writes off the NSA as not being an issue for them because they’ve “done nothing wrong.” Driving home that point is an excellent short “Op-Doc” in the NY Times by filmmaker Brian Knappenberger, which has brief interviews with a bunch of great people (many of whom you’ll hopefully recognize) explaining in very clear terms why you should absolutely care about the NSA. There are many reasons discussed, but a simple one, highlighted by David Sirota, goes back to that quote above. You can claim that you’ve done nothing wrong all you want. However, if someone really powerful decides they want to railroad you, you’d be surprised at how much it can be made to look like you’ve “done wrong.” And when the NSA (or the FBI) can readily access all sorts of data about your life, their ability to build such a story increases tremendously.
-
The NSA had cracked Internet encryption.
The NSA was listening in to everything.
European customers were especially concerned, he says.
Fortunately, many of the headlines had been unnecessarily alarmist.
“The earlier types of encryption, with 64 bits or less, the NSA has figured out how to brute force decrypt at least some of that traffic,” he says. “But the more modern, strong encryption, with 128 or 256 encryption units, they can’t decrypt that. And it bothers them no end.”
-
But could the push back against the NSA’s comprehensive surveillance with new privacy-enhancing technology be jeopardised by community reluctance for large-scale collaboration?
-
Four Brisbane security researchers are fighting back against government surveillance by building a router based on open source components designed to make security and privacy verifiable and more accessible to users.
The Open Router Project (ORP-1) router would be built on open source hardware and software to allow users to check that the unit was free of vulnerabilities and backdoors.
Permalink
 Send this to a friend
Send this to a friend
Posted in Free/Libre Software, Security at 11:19 am by Dr. Roy Schestowitz
Without source code of all levels/layers of the software trust just cannot be established

Summary: Proprietary software can never be secure and back doors inside of it can be assumed (unless proven otherwise), based on some of the latest NSA leaks
THE NSA is a criminal operation, so we expect it to work with other criminal operations. Microsoft and the NSA collude to make the world a less secure place, enabling espionage with Windows (Stuxnet for example) and providing video/audio surveillance in people’s own homes without any warrants. Microsoft is about lawlessness is the same way the NSA is. The law of “rule” supersedes the rule of law.
Some say that the Windows-centric Stuxnet is the “world’s first true cyber-weapon”, but that is not true. History aside, to put it as IDG put it: “Stuxnet’s creators recognized they had built the world’s first true cyber-weapon and were more interested in pushing the envelope of this new type of digital warfare than causing large-scale destruction within targeted Iranian nuclear facilities, a study shows.
“In an analysis released last week, Ralph Langner, head of The Langner Group and a renowned expert in industrial control systems (ICS), also refuted arguments that only a nation-state had the resources to launch a Stuxnet-like attack. Assailants with less ambition could take the lessons learned and apply them to civilian critical infrastructure, he said.”
This was an example of overreach and violation of the law, enabled of course by Microsoft and Windows. GNU/Linux does not sell its users down the river the way Windows does.
Sadly, firms like White Source make a comeback with their FUD and they single out FOSS for security issues (here is the press release). This is not acceptable because they totally ignore the much bigger threats, as above (where security issues are there by design).
The White House is at war against FOSS geeks and other phantom enemies [1,2], where the logic is something along the lines of, if we don’t control it (we as in the government), then it’s a threat to national security. While it seems clear that a brute force attack is the Achilles Heel of FOSS [3,4,5] and Google keeps improving security of FOSS projects like Android [6,7,8,9.10] and others [11,12], the logic followed by the likes of White Source and White House is that if something proprietary keeps its flaws (or back doors) secret, then it’s secure and we should not pay attention to real security. Again, this is simply not acceptable.
The head of the Linux Foundation recently said that FOSS is safer, and Linux is more secure than any other OS [13]. Mikko Hypponen seems to agree with him [14] and despite some new known flaws in Red Hat software [15,16] (transparency makes weaknesses visible) we should remember that lack of knowledge about something does not mean it’s not there. Just because we cannot easily see back doors in proprietary software doesn’t mean they’re not there (some groups of people know they’re there and they exploit them silently). If Europe is serious about cyber security [17], then it should dump all proprietary software (back doors-friendly software) as soon as possible. Given everything we now know about the NSA, ignorance and uncertainty are no longer an excuse. A Dutch source has just revealed that the NSA cracked 50,000 computer networks. The evidence is overwhelming. Stuxnet is peanuts next to that. █
Related/contextual items from the news:
-
Depending on when one asked, Antisec was generally between 8-10 people, with a solid core of about six. Not all of them were comfortable with talking to me, and certain ones were designated to communicate with press. I was never entirely sure who was in or out at any particular time — it was a fluid group. I never knew all the nicks. I talked repeatedly with five of them, including Sabu.
-
This article argues that online gambling is a strategic national threat because terrorists could use it to launder money.
-
-
GitHub is experiencing an increase in user account hijackings that’s being fueled by a rash of automated login attempts from as many as 40,000 unique Internet addresses.
-
-
-
-
-
-
Google has extended its Patch Reward Program to include a raft of new platforms and technologies including its own Android system as it looks to improve the securiry of open source software.
The firm announced an overhaul to its security patch policies last month, offering white hats up to $3,133 for fixes.
-
Step up to 2048-bit keys optimizes balance between protection of company services and maintaining performance
-
Pinkie Pie returned in 2013 for the desktop Pwn2Own event operated by Hewlett-Packard’s Zero Day Initiative (ZDI), taking aim once again at Google. This time, it was Google’s Chrome browser running on Chrome OS. Pinkie Pie’s effort landed him another $40,000 in award money for the discovery and reporting of what turned out to be a trio of flaws, including one buried deep within the Linux kernel. Chrome OS is a Linux-based operating system that Google uses on its Chromebook notebooks.
But wait. There is still more.
Just this week in Japan at HP’s Mobile Pwn2Own event, the legend of Pinkie Pie grew as the My Little Pony-loving security researcher once again demonstrated previously unknown zero-day flaws in Google’s Chrome. Pinkie Pie was able to pwn Chrome on both a Nexus 4 as well as a Samsung Galaxy S 4 smartphone. This time, Pinkie Pie pocketed $50,000 for his efforts.
-
-
Open source software can be one answer to combating the global surveillance of innocent citizens, said security expert Mikko Hypponen in his keynote last week at LinuxCon and CloudOpen Europe in Edinburgh.
-
Attackers are actively exploiting a known vulnerability to compromise JBoss Java EE application servers that expose the HTTP Invoker service to the Internet in an insecure manner.
-
-
The European Cyber Security Directive, which proposes that European businesses have a legal obligation to ensure they have suitable IT security mechanisms in place, is soon to be enforced in the UK.
Permalink
 Send this to a friend
Send this to a friend
Posted in GNU/Linux, Kernel at 10:45 am by Dr. Roy Schestowitz

Summary: NVIDIA’s drivers still cannot be trusted and NVIDIA’s assurance of performance improvements isn’t enough
NVIDIA, the world’s most proprietary GPU maker (which artificially cripples Linux drivers), is trying to appeal to gamers on GNU/Linux [1], perhaps with some performance gains [2] but hardly with any source code. NVIDIA, which already left back doors in Linux some years ago (severe flaw in the driver), should try harder than that. Freedreno [3] recognises the value of source code, Mesa 10.0 is coming [4] with an open door to public participation [5], and even Intel, the company behind restricted boot through UEFI, is giving source code to buyers of physical hardware [6]. There is nothing detrminetal when it comes to releasing source code to accompany hardware one sells (hardware which requires placing binaries in one’s computer with ‘root’ privileges). NVIDIA should wake up already and become respectful to software freedom, or at least those who want reassurance that NVIDIA’s blobs are not just Linux back doors. We already know that the NSA wanted back doors in Linux and it was eager to even bribe companies to help achieve this. NVIDIA is an American company.
Those who chastised Richard Stallman for rejecting proprietary components in his computers have hopefully changed their views after the NSA leaks/scandals. █
Related/contextual items from the news:
-
-
-
The Freedreno open-source graphics driver project that’s a clean-room reverse-engineered implementation of the Qualcomm Adreno graphics core on the company’s ARM SoCs keeps reaching new milestones. While the driver is mostly just worked on by Rob Clark and without any support from Qualcomm, it’s quickly becoming the flagship open-source ARM graphics driver for the Linux desktop.
-
-
If you really want to contribute to Mesa you should at least have some C\C++ experience, if you don’t buy yourself a book and go for it. Knowledge of OpenGL would also obviously be useful The OpenGL SuperBible is generally the most recommended book on OpenGL.
-
Intel’s open-source Linux graphics driver for supporting Broadwell is continuing to move along ahead of the availability of the new Intel processors in a few months time.
While Intel only open-sourced the Broadwell graphics driver changes earlier this month and began pushing the code forward into the Linux kernel, Mesa, libdrm, and xf86-video-intel drivers, the support is moving along nicely.
Permalink
 Send this to a friend
Send this to a friend
« Previous Page — « Previous entries « Previous Page · Next Page » Next entries » — Next Page »



















 Content is available under CC-BY-SA
Content is available under CC-BY-SA