08.20.13
Posted in Europe, Patents at 11:30 am by Dr. Roy Schestowitz
Intimidation, assassination, blackmail, torture, and sanctions
“We’re under the control of the empire of the corporations. The governments that rule our countries are governments of occupation. They don’t work for us, they don’t represent us. They pretend to, but they’re really working for the empire. And so they seek to criminalise protest whenever they can.” –Richard Stallman
Summary: The military/corporate coup in the United States (what Stallman calls a “government of occupation”) continues to damage the population and especially those speak out for public interests; The unitary patent (think US patent regime) threatens to spread in Europe even faster now that Austria bends over
THE harassment of David Miranda, who preferred to remain out of the public eye on the face of it (Wikipedia still links/strings him to the article on Glenn Greenwald), showed us that nowhere in the world can one be safe from the wrath of the CIA/NSA. Not in Brazil and certainly not in Europe, especially not in US allies like the UK. In places like Italy, which are filled with US army bases, one can even be abducted and tortured by a CIA agent, despite being innocent (famous legal case right now). Germany, which is the other European nation absolutely filled with US army bases (see a publicly-disclosed list of bases or a map, bear in mind some are unlisted), there is a similar case. This is scary. You no longer have to be Muslim to be treated like this; you can be captured under laws originally passed to combat “terrorism” and then be sent overseas to be silently killed (yes, this happened), sodomised, be forced through torture to say you’re part of Al-Qaeda (even if you’re not), and sometimes have loved ones threatened or used for blackmail (the Nazis did this). Having been stopped a lot at airports recently, I can’t help being bothered by this. Surveillance is not a selective thing anymore; everyone is under surveillance. We’re living in a mass surveillance society. In the UK, for example, there are at least two US bases (covertly run by the NSA), one in Gloucestershire, another in Yorkshire. They’re both vast. They’re a surveillance hub that assists drone strikes, among other things like global surveillance and satellite signals interception. Phone calls are being recorded indiscriminately and fibre optic cables have all of their data (very high throughput) saved indefinitely, analysed, and habitually used to profile people who are law-abiding citizens.
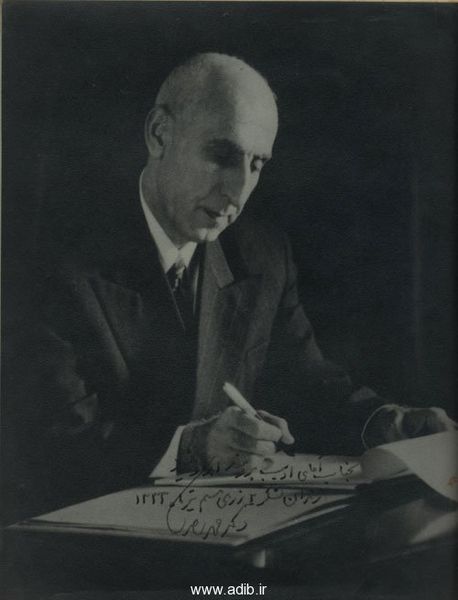
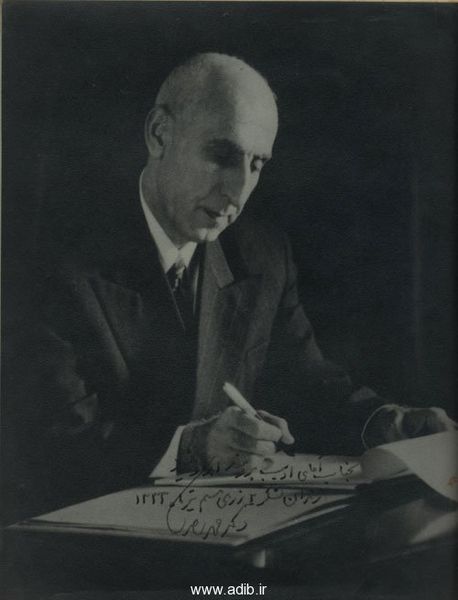
“In the UK, for example, there are at least two US bases (covertly run by the NSA), one in Gloucestershire, another in Yorkshire.”This is the symptom of a system that’s totally out of control. It’s debt-saddled, it has no stability because of class disparity that inevitably breeds unrest, and it faces high inflation rates. It’s reminiscent of Germany in the mid 1930s when many political dissenters and later ethic groups were prosecuted, some later executed. The drums of wars were widely beaten and IBM was helping the Nazis profile the population. Months ago IBM was fighting Amazon over a massive contract with the CIA, which says it wants to amass heaps of data and keep it “forever” (think of the NSA facility in Utah). The current system is frightening to those of us who speak out against people in power. It resorts to intimidation and the CIA/NSA covertly serve the interests of corporations and plutocrats, totally disregarding 99.99% of the population. This week documents are being declassified (after 60 years) to confirm what many already knew — that the CIA forcible removed (in a coup) Iran’s democratically-elected government (there have been many more actions like that since then, continuing to this date in Syria), kick-starting a cycle of oppression which serves the interests of large corporations (oil companies).
Techrights does not write political posts. When politicians are named it is not because of their political orientation or the party they’re affiliated with. Both major parties in the US are bought and paid for; everyone knows that. We don’t need another site to point this out. Some matters, however, are bipartisan and we deal with them separately. To us, for instance, the USPTO is relevant. The US ITC has come under increased pressure from Groklaw, which has just shut down due to surveillance (see news links at the bottom) for its role in protectionism rather than law enforcement. Lawyers offering services of protectionism say that even outside the realm of patents there is protectionism that’s facilitated by the Court of Appeals for the Federal Circuit. Those who do not think this whole legal framework is fundamentally corrupt and dysfunctional might need to do some further reading. If they don’t change their minds, then perhaps they need to read outside the echo chamber of the lawyer-writer microcosm. Patent trolls are thriving and blogs keep emerging to confront those trolls. It’s not just trolls though:
Again, we get it. And in fact, that’s one reason that the term NPE is not the same as the term Patent Troll. All patent trolls are NPE’s, but not all NPE’s are patent trolls.
RPX or OIN are NPEs and they don’t achieve much except create more cartels, dominated of course by multinational corporations, mostly US-based corporations.
Currently, this issue is limited to the United States and it mostly serves large corporations by blocking imports of competitors. We saw Microsoft doing that half a decade ago, essentially using patents aggressively, and not just for FUD.
The president of the FFII warns that US patent culture is approaching Europe, noting that:
Austria becomes the first country to ratify the Unitary Patent Court, software patents through the backcourt
Here is his source, which says:
The Agreement on establishing the Unified Patent Court (UPC) was signed in February 2013 and seeks to establish a unified patent court system across Europe to handle the enforcement of new EU Unitary Patents when they come into effect. A list of the countries who signed the agreement can be found here.
The Unified Patent Court will not have competence over national patent rights such as those granted by the UK Intellectual Property Office.
However, the Unified Patent Court will ultimately assume competence in relation to infringement and validity disputes in respect of regular (i.e. non-Unitary) European patents as currently granted by the European Patent Office.
In order for the Unified Patent Court system to become a reality it is necessary for 13 member states who signed the Agreement to take the subsequent step of ratifying the Agreement. It is also a requirement that the Agreement is ratified by the UK, France and Germany.
Austria became the first member state to ratify the Agreement by depositing its instrument of ratification in Brussels on 7 August 2013. A press release from the Austrian Foreign Ministry can be found here.
Given this disturbing trend of assimilation we might sooner or later see the grip of massive American corporations expanding to other continents. Remember which nation expanded to Austria before it decided to take over Europe and by extension the whole world? No, this isn’t Godwin’s Law creeping in, that’s just my personal opinion and I increasingly worry about — not resent — what the US is doing to the world as an irresponsible and arrogant empire/superpower. This system is not good for US citizens. It tears apart both domestic and foreign populations. It’s class warfare and extreme socoipathy.
Techrights has published well over a thousand items (mostly in daily links) about NSA surveillance, going a couple of years into the past. Binney and Drake, two brave NSA whistleblowers, opened my eyes to this massive problem, which led me to researching the CIA too. Prior to them I learned a lot from Chalmers Johnson (he died years later). Those don’t understand the severity of this problem should patiently read the articles below. Pamela Jones is not exaggerating and I admire her decision to compromise her online “baby” for the sake of principles. Techrights is going to fight the NSA; shutting down is letting the NSA get its way. █
Permalink
 Send this to a friend
Send this to a friend
Posted in GPL, Microsoft, Samsung at 10:15 am by Dr. Roy Schestowitz
The Software Freedom Conservancy did well

Summary: The fuller story behind Samsung choosing the GPL for a previously-proprietary piece of software that helps Microsoft
A few days ago we wrote about Samsung [1, 2, 3. 4] deciding to make it seem like it never violated the GPL licence, having done so before. Well, the group which years ago told us not to taunt Samsung over it claims to have just played a role. To quote:
Conservancy’s GPL Compliance Project for Linux Developers worked collaboratively with Ibrahim Haddad, the Group Leader for Open Source at Samsung Research America, and fellow community leaders, throughout the process after this code first appeared on GitHub. Conservancy’s primary goal, as always, was to assist and advise toward the best possible resolution to the matter that complied fully with the GPL. Conservancy is delighted that the correct outcome has been reached: a legitimate, full release from Samsung of all relevant source code under the terms of Linux’s license, the GPL, version 2.
LWN wrote:
The Software Freedom Conservancy has announced that it has helped Samsung to release a version of its exFAT filesystem implementation under the GPL. This filesystem had previously been unofficially released after a copy leaked out of Samsung.
This is good work, but without the leak, would it have happened? Without some public shaming, would Samsung have cared? Sometimes there’s no choice but to be brave (blowing some whistles) and potentially rude/crude. █
Permalink
 Send this to a friend
Send this to a friend
08.19.13
Posted in News Roundup at 6:59 pm by Dr. Roy Schestowitz

Contents
-
Linux is largely written today by programmers working for large companies, but, keeping in touch with its roots, the Linux Foundation is offering travel expenses to the next Linux Kernel Summit for Linux kernel hobbyist programmers.
-
As desktop Linux’s popularity grows, so, too, do concerns about viruses and malware. “Malware will come to target consumers on Linux,” said blogger Chris Travers. “When it does, we will need to address the challenges it poses. Everything from code management to repository management will need to evolve to meet such a threat, but it will. The software evolves. The culture evolves. That is life.”
-
Desktop
-
Kernel Space
-
Linus Torvalds has released a new release candidate for the Linux 3.11 and is planning to push the next release candidate with the 22nd anniversary of Linux. This release candidate, though stated a “quiet” release fixes the TLB invalidation bug that was old and “really hard to hit in practice”. There were also some other fixes in network drivers, usb sound and filesystems. At the end of the message in The Linux Kernel Mailing, he promises to something more interesting for the rc7 release as it will coincide with 22nd anniversary of Linux.
-
-
Graphics Stack
-
For those curious about learning more information on Keith Packard’s work for DRI3 (DRI3000), he presented at the 2013 DebConf and the video recording is now available.
-
Now that Mir is living in the Ubuntu 13.10 archive, new Phoronix benchmarks have been conducted to look at the current performance impact of routing the graphics through XMir rather than running an X.Org Server directly on Ubuntu Linux. For this latest XMir testing, the System76 Gazelle Professional laptop with an Intel Core i7 “Haswell” CPU sporting Intel HD Graphics was benchmarked for 2D and 3D environments.
-
Applications
-
The consequences of losing data can be disastrous for any individual or organisation. The loss of a single hard disk may have huge repercussions; the loss of data with sentimental or financial value. Making file backups is an essential activity for all users, yet many users do not take adequate steps to protect their data. Whether a computer is being used in a corporate environment, or for private use, the machine’s hard disk may fail.
-
-
Instructionals/Technical
-
Games
-
Thе mod is still in development and tells the story of a lonely fisherman whose ship is stranded on a mysterious island during a violent storm.
-
-
Estranged is a critically acclaimed Half-Life 2 mod that tells the story of a lone fisherman whose ship is stranded on a mysterious island during a violent storm. The story telling is attractive and though the mod is still work in progress, its enjoyable to play with only a few bugs. The mod has an average rating of 9.1 on Desura.
-
-
Unigine Engine developers have talked about their latest round of improvements to their cross-platform visual masterpiece.
While it’s still tough to find Unigine Engine games out in the real world that are gaining ground, Unigine Corp continues to see licensees in the VR space and other commercial areas, it appears. A new Unigine Engine development log update was posted on Friday and it covers new support for mesh-based orthographically projected decals on all underlying geometry, a new field spacer node, and renderer improvements.
-
-
-
-
-
Desktop Environments/WMs
-
As I was diving back into Window Maker for this article, it occurred to me that the desktop manager I used for years with Debian is disturbingly similar to the Unity Desktop. It’s been clear since its inception that I am not a fan of Ubuntu’s new Unity interface, yet it’s odd that for years I loved Window Maker, which seems fairly similar, at least visually.
-
K Desktop Environment/KDE SC/Qt
-
In the weeks before Akademy 2013 I convinced KDE Usability Guru Björn Balazs to lend his experience to a usability workshop I wanted to organize at the conference. The goal was to teach developers how to do ‘basic usability testing at home’ by guiding users through their application and watching the process. To help developers who didn’t make it (and those who did but can use a reminder) I hereby share a description of the process and some tips and notes.
-
-
GNOME Desktop/GTK
-
The GNOME Project announced the availability for download and testing of the fifth development release towards the GNOME Chess 3.10 application for the upcoming GNOME 3.10 desktop environment.
-
The GNOME developers behind the GNOME Settings Daemon application, a daemon run by all GNOME sessions to provide live access to configuration settings and the changes done to them, announced the development version 3.9.5.
-
After the release of GLib 2.36.4, the development team behind the GLib libray software for the GNOME desktop environment, announced the availability for testing of the development version 2.37.5.
What’s new in GLib 2.37.5? Well, the development team implemented the Desktop Action specification, which means that in the case that the app is a DBusActivatable and GApplication, actions from the desktop file are automatically translated into GActions that have been already added to the app using the g_action_map_add_action() API.
-
The development team behind the famous and popular Evolution email client used in many Linux operating systems, reached unstable 3.10 Beta 1 version earlier today, August 18, 2013.
-
-
I spend quite a lot of time reading the pages at Reddit and one of the most common questions in the /r/linux4noobs subreddit is “Which distro should I use?”.
-
Screenshots
-
Gentoo Family
-
Red Hat Family
-
Fedora
-
The Korora Linux distribution is a project based on the Fedora operating system. Korora takes the latest version of Fedora and tweaks the system to make it more appealing, out of the box, to desktop users. For instance, the Fedora project doesn’t provide some multimedia codecs, Flash or VirtualBox. These packages are not included in the parent distribution and are not available through the default repositories. Korora ships with popular media codecs and enables third-party repositories such as Google’s Chrome repository, VirtualBox’s repository and the popular RPMFusion package repository. Korora also comes with a utility which makes it easy to locate third-party hardware drivers which may be useful to users. As a bonus, Korora ships with the Firefox web browser and includes several useful plugins to make surfing the web more pleasant. Korora 19 was released on the heels of Fedora 19 and shares the same base system and installer.
Korora 19 comes in two flavours, GNOME and KDE. Both of these editions are available as 32-bit and 64-bit builds. I decided to try the KDE version as I was fairly happy with the KDE spin of Fedora 19 when I tested it back in July. The download image for Korora’s KDE edition is approximately 2.2GB in size, fairly heavy in comparison with the KDE spin of Fedora. Booting from the downloaded ISO brings us to a KDE desktop with an icon in the upper-left corner of the screen that will launch the system installer. At the bottom of the screen we see the application menu and task switcher. Shortly after arriving at the desktop a welcome window appears. This window offers us quick links for accessing the project’s documentation, KDE’s user guide and Korora’s social media websites. In addition there is a button for launching the system installer.
-
Debian Family
-
August, 15th 2013 was Debian’s 20th anniversary. The Debian Project is a massive community-driven open-source project devoted to a single goal: build a free Linux operating system. Debian is well-known for maintaining strictly guarded policies and principles to remain the most stable and secure Linux distribution.
-
Derivatives
-
Brian Manderville, the developer of the Descent|OS Linux operating system announced recently on his blog that the upcoming release of his distribution will no longer be based on Debian or anything else.
-
Canonical/Ubuntu
-
Canonical, the creators of Ubuntu, launched an ambitious crowd sourcing venture this past June to begin funding Ubuntu Edge, a completely new kind of smartphone. In the short time they gave themselves, Canoncacle has crowd sourced an impressive $10, 288, 472 million in funding on Indiegogo for its Ubuntu smartphone Edge.
-
Congratulations are due to Canonical for the handling of their Indiegogo campaign to raise funds for the Ubuntu Edge smartphone. The promise of a 4 GB Ram smartphone, with 128 GB of storage, dual-LTE receivers, dual booting to Android and Ubuntu, working as a desktop replacement and a mobile device certainly caught the eye of many people. As a statement of intent for Ubuntu’s mobile edition it can be regarded as a success – most of the tech watching community are now fully aware of what Canonical believes they can build.
-
Ever wish that you did not have to carry your laptop all over the place? Ever wish that your phone had more storage space, more RAM, more processor speed? What if your phone could actually do everything that your laptop could do and more?
-
Sorry Pebble – you’re not the biggest kid on the crowdsourced block anymore. But hey, at least you got made.
-
It’s the most audacious crowd-funding campaign in history: $32 million for a limited run of 40,000 high-end “super-phone” handsets.
-
There’s only two and a half days left to Canonical’s Ubuntu Edge crowd-funding campaign for building a high-end smart-phone running Ubuntu. Unfortunately, the campaign is still about twenty million dollars short of its $32M goal.
-
-
This $35 device, Chromecast, is turning out to be much more than what Google showed or told us. Not only does it turn your HDTV into external monitor for your Chrome tabs, it can also play local content such as videos, images and music via Chrome.
-
Direct Insight has launched a $200 development kit built around its Linux- and Android-ready Triton-TX6Q computer-on-module based on Freescale’s quad-core i.MX6Quad ARM Cortex-A9 system-on-chip. The kit combines the COM with a baseboard that adds an SD slot and connectors for Ethernet, dual USB, audio, serial ports, and optional capacitive touchscreens.
-
Editor’s Note: This is the fourth article in a new series by SUSE community marketing manager Brian Proffitt for Linux.com called “Reality Check” that will take a look at Linux in the real world. For more in this series see OpenStack is Not the Next Linux, 5 Linux Features You Want in Your Company and Defining the True Success of Linux.
-
Phones
-
Fresh out of five days at OSCON and all the fun events around Portland that week, a group of devoted hackers came to our Tizen Devlab and Hack to check out Tizen‘s open source, HTML5-based mobile OS, which is being brought to the world by the Linux Foundation with support from Samsung and Intel.
-
Android
-
We knew this was going to happen. All latest flagship devices have their ‘Mini’ sibling, so why should Sony’s Honami not have a ‘Mini’ version? It started with Samsung Galaxy S3 and S4 Mini, followed by HTC One Mini, then came along Motorola Droid Mini and already hinted Moto X Mini, now we have leaked information about Sony Honami Mini codenamed Ray 3.
-
-
Web Browsers
-
Mozilla
-
Mozilla continues to move rapidly ahead with its Firefox OS mobile operating system, which is arriving on phones in many markets around the world. In fact, the OS is gaining enough traction that many observers see it as eventually being competitive with iOS and Android phones, but If Firefox OS is to be a resounding success, it’s going to need a very healthy ecosystem of apps to attract users.
-
Oracle/Java/LibreOffice
-
Feng Office’s tag line is: Unleash your team’s potential. It’s an open source collaboration platform for teams and businesses that began as an academic project at UdelaR University. Interested students worked on the initial research and development, and today it remains an open source project.
-
-
FSF/FSFE/GNU/SFLC
-
Import MusicXML
Direct import of music XML.
Improved Rhythm Entry
Dotted rhythms in two keypresses
-
This feature causes runtime data structures to be built at program start up which are used for verifying the vtable pointers. The options std and preinit control the timing of when these data structures are built. In both cases the data structures are built before execution reaches ‘main’. Using std causes these data structure to be built after the shared libraries have been loaded and initialized. Using preinit causes them to be built before the shared libraries have been loaded and initialized.
-
Openness/Sharing
-
Open Hardware
-
Furniture is probably the last thing on the mind of most open source proponents but now it doesn’t have to be. OpenDesk is a free, open source line of furniture that you can make yourself or order unassembled from a maker with a CNC machine. Not only is the furniture cheap – free if you have the wood and hardware – it’s actually cool-looking.
-
Programming
-
Standards/Consortia
-
Last year, we established our definition of an open standard for software interoperability, data and document formats, and the Open Standards Principles that explain our rationale for putting them into government IT.
Now we are working on identifying the specific open standards that will most benefit users of government technology and services. That process depends on suggestions and recommendations from experts on the field — many of whom are outside of government. We need your help.
-
-
Defence/Police/Secrecy/Aggression
-
Things are getting really messy in Yemen at the moment. With soldiers being murdered in their sleep and embassies closing en masse in fear of an imminent wave of attacks and multiple drone strikes, the country seems to be the latest sandbox full of blood in our war on terror.
Not that this warz one is all that new. Al Qaeda in the Arabian Peninsula (AQAP) have had a presence in the area for years, their membership rose from around 300 in 2009 up to an estimated 1,000 today. In an attempt to combat this rise in manpower, the US has escalated its infamous drone program, allegedly targeting high-ranking AQAP members. Although, according to reports, they’ve yet to actually kill any of them.
Is this hit-and-hope policy really the best way to fight al Qaeda in Yemen? Or are these drone strikes, which have a habit of killing civilians, exactly the PR ammo al Qaeda need to lure new recruits in a country that is already as politically stable as a gang of jihadists on a bouncy castle?
-
An escalation of drone strikes in Yemen highlights the fact that the US public is still in the dark about this use of lethal force
-
Today, on the 60th anniversary of the coup against Iran’s Mohammed Mossadegh, Foreign Policy Magazine (FPM) reported that the National Security Archive website — an independent non-governmental research institute and library located at The George Washington University in Washington DC — has published a document in which the CIA openly acknowledges its involvement in the overthrow of the man who was elected as Iran’s prime minister.
-
Lady was among 23 Americans sentenced at an Italian trial in
2009, the first time U.S. nationals had been convicted over the
programme, operated by the administration of former U.S.
President George W. Bush during the so-called war on terror.
-
Mossadeq was a democratically elected prime minister of Iran from 1951 to 1953, when his government was overthrown through the coup. His successor, said to have been chosen by Britain’s MI6 and the CIA, was Fazlollah Zahedi, an Iranian general. General Zahedi had resigned as minister of interior in 1951 because of the criticism he received in handling a demonstration, according to the CIA history.
-
Former Interior Minister and former leader of APML Mian Zahid Sarfaraz has claimed that Osama bin Laden was not killed during 2nd May, 2011 Abbottabad action by the US Seals and he was arrested in injured condition.
-
Transparency Reporting
-
People say reckless things on Twitter, as Grunwald’s defenders pointed out and as some of his more extreme critics, who posted that they couldn’t wait to write a similar defense regarding the drone strike that hit him and other gruesome things, demonstrated. If dumbness were the only issue we’d be done. But this one deserves being talked about a bit more, less because Grunwald still seems a bit oblivious as to what was wrong with what he said (though there’s that) than because it encapsulated something hazardous about the current moment, for journalists, for anyone who cares about civil liberties, and for the political culture more generally. And there’s the issue of the lack of civility on Twitter—but we already knew that one.
-
The group, which has been assisting ex-NSA contractor Edward Snowden after he leaked top-secret documents to the media, posted links for about 400 gigabytes of files on their Facebook page Saturday, and asked their fans to download and mirror them elsewhere.
-
PR/AstroTurf/Lobbying
-
The Wall Street Journal’s latest defense of the American Legislative Exchange Council (ALEC), penned by WSJ Editorial Board Member Stephen Moore, fails to disclose Moore’s deep ties to ALEC.
-
Privacy
-
-
Two of congressional Republicans’ most outspoken members on the National Security Agency’s surveillance programs on Sunday highlighted the sharp divide within the party on the issue.
-
-
Holy crap. They perform 20 million surveillance queries per month? On the bright side, if you assume that their internal auditing really does catch every “incident,” it means they have a violation rate of about 0.001 percent. On the less bright side, they perform 20 million surveillance queries per month.
That’s genuinely hard to fathom. Is some of that automated? Or is that truly 600,000-plus human queries each and every day? The mind boggles.
-
-
EFF filed an amicus brief in an important case known as Du v. Cisco, where Chinese human rights activists have sued the US tech giant Cisco in Maryland federal court. The case alleges that Cisco knowingly customized, marketed, sold, and provided continued support and service for technologies used by the Chinese government to facilitate human rights abuses.
The case arises in part from the publication several years ago of a presentation in which Cisco confirms that the Golden Shield is helpful to the Chinese government to “Combat Falun Gong Evil Religion and Other Hostilities.” This shocking statement indicated not only that Cisco knew of the Chinese government’s strategy of repression of dissident groups, but that it was marketing and customizing its Golden Shield technologies to meet those goals. Shortly after this case was filed in August 2011, China detained the lead plaintiff, Du Daobin, and interrogated him about his involvement in the case. EFF called on Cisco to intervene to help protect the plaintiffs.
-
An attorney best known for his prodding environmental regulators over their email usage has turned to a new potential ally in the war against climate science: the National Security Agency.
While the NSA has been getting flack in recent months after reports on its secret surveillence programs, Chris Horner, a senior fellow at the Competitive Enterprise Institute, doesn’t seem to mind. In fact, he’s so pleased with the practice that he’s using it to further his pursuit of emails and other documents from former Environmental Protection Agency head Lisa Jackson. Horner first revealed in June what many conservatives decried as a “secret email account” that Jackson utilized in her time at the EPA.
-
A conservative gadfly who has made a crusade of uncovering embarrassing emails at the Environmental Protection Agency wants to tap a new potential evidence trove: the National Security Agency’s electronic snooping program.
-
-
Seems like everything gets hacked these days. Baby monitors. White House employees’ personal email. Toilets.
-
Deputy NSA Director John Inglis recently told Congress that analysts “try to be judicious” in analyzing telephone metadata so as not to waste their name studying phone records from “the pizza delivery man.” But there are other groups of American citizens whose telephone records likely interest the intelligence community far more than takeout restaurants: attorneys who represent Guantanamo detainees. Journalists. Whistleblowers. Human rights researchers.
-
Europe’s privacy watchdogs are demanding details on the extent of U.S. surveillance efforts in the wake of NSA leaker Edward Snowden’s revelations about the PRISM spying program.
The National Security Agency’s PRISM operation compels major Internet firms to hand over detailed contents of communications such as emails, video chats and more.
-
Arguing that congressional hearings and new safeguards recently announced by President Barack Obama might not be enough to ensure privacy rights, Sen. Rand Paul (R-Ky.) called for the Supreme Court to review the constitutionality of the National Security Agency’s surveillance programs.
-
There was a showing of the new documentary, Terms and Conditions May Apply late last week in Washington DC, and Rep. Dennis Kucinich stopped by and made some very pointed remarks while discussing the NSA’s surveillance activities. The (well-timed) documentary, of course, looks at how companies and the government use and abuse everyone’s digital data. Kucinich’s remarks are well worth listening to, as he suggests that Congress should abolish the NSA, while also saying that Ed Snowden deserves a ticker-tape parade.
-
-
Sick of government spying, corporate monitoring, and overpriced ISPs? There’s a cure for that.
-
Amash Seeks New Vote on Ending Surveillance
-
Civil Rights
-
The partner of journalist Glenn Greenwald, who revealed mass surveillance by US and British security agencies, has been detained under the Terrorism Act, the Guardian reports. He was reportedly stopped at Heathrow Airport but has since been released.
-
David Miranda, partner of Guardian interviewer of whistleblower Edward Snowden, questioned under Terrorism Act
-
The detention of my partner, David Miranda, by UK authorities will have the opposite effect of the one intended
-
In an outrageous and unacceptable attack on press freedom, Guardian journalist Glenn Greenwald’s partner, David Miranda, was detained for almost nine hours at Heathrow airport in London earlier today under section 7 of the UK’s pernicious Terrorism Act. Miranda was returning to his home in Brazil after a week-long visit with documentarian Laura Poitras. Miranda, whose flights were paid for by the Guardian, was reportedly bringing important documents back to Greenwald on USB thumbdrives.
[...]
It is unclear what the UK government was trying to accomplish by detaining Miranda. Likely, it was meant as some form of intimidation. But surely, it will backfire. Investigating acts of journalism under “terrorism” laws and detaining family members of reporters are hallmarks of authoritarian regimes.
[...]
Take, for example, this report from Human Rights Watch from a year ago: “The Iranian government has been intimidating and detaining relatives and friends of foreign-based Persian-language journalists to obtain information or silence them.”
And until UK government takes swift action to rectify this injustice, other journalists — and their loved ones — should be on alert. Not only was Miranda detained, but Greenwald’s journalistic work-product was seized. As Andrew Sullivan wrote, “So any journalist passing through London’s Heathrow has now been warned: do not take any documents with you. Britain is now a police state when it comes to journalists, just like Russia is.”
[...]
Ironically, this incident comes the same day as a long profile in New York Times Magazine of Poitras, who has shamefully been the subject of similar harassment at the border by the US for years, solely because she produces journalism that the United States government apparently does not like. It’s unknown whether the US had any involvement in the detention of Miranda but questions should be asked as to what they knew and when.
-
The stranger responded with instructions for creating an even more secure system to protect their exchanges. Promising sensitive information, the stranger told Poitras to select long pass phrases that could withstand a brute-force attack by networked computers. “Assume that your adversary is capable of a trillion guesses per second,” the stranger wrote.
-
On a few occasions, I stood outside in a protest of Arab registration in America where a still unknown number of men went into DHS offices, and never came home. We all watched the surveillance and intimidation of Muslim and Arab communities in America, the UK and Europe and said to those governments, it’s ok, because those communities have extremists.
Now the extra-judicial harassment of journalists has begun. And a bunch of folks are saying “How could this happen?”
-
Senior MP to seek explanation from police after detention of Glenn Greenwald’s partner, David Miranda, at Heathrow airport
-
Nick Pickles, director of privacy and civil liberties campaign group Big Brother Watch, said: “This is a direct attack on freedom of the press and a chilling reminder that our anti-terror laws are in desperate need of reform. Whoever took the decision to have David Miranda arrested and detained should be named and held publicly accountable for this flagrant abuse of anti-terrorism laws.
-
Today’s detention of David Miranda, the partner of The Guardian’s Glenn Greenwald who interviewed whistleblower Edward Snowden, is a direct attack on freedom of the press and a chilling reminder that our anti-terror laws are in desperate need of reform. Whoever took the decision to have Miranda arrested and detained should be named and held publicly accountable for this flagrant abuse of anti-terrorism laws.
The law Miranda was detained under provides powers to deal with those suspected of involvement with acts of terrorism, not a license to interrogate those with knowledge of the activity of journalists. If a foreign government detained the partner of a British journalist we would rightly be up in arms.
-
The British government has received international condemnation after the partner of Guardian journalist Glenn Greenwald was questioned for nine hours over Edward Snowden’s NSA and GCHQ leaks.
Brazilian national David Miranda, who was in Heathrow airport en route to Rio de Janeiro, was held under the 2000 Terrorism Act – although Greenwald claims the interrogation had nothing to do with terrorism.
-
The partner of Glenn Greenwald, the journalist who published classified information on U.S. government surveillance, was detained for 9 hours in London’s Heathrow Airport. On Sunday morning, David Miranda was detained for the maximum allowable time under British Law; his property was confiscated and has yet to be returned, according to Greenwald.
-
The domestic partner of the journalist who broke a series of stories revealing mass surveillance programs by the U.S. National Security Agency was held for almost nine hours Sunday by British authorities at London’s Heathrow airport on his way home to Rio de Janeiro.
-
London: British police have detained the live-in partner of a Guardian journalist responsible for leaking reports on US surveillance programme for nine hours under terror laws, prompting Indian-origin lawmaker Keith Vaz to seek an explanation from Scotland Yard on the issue.
[...]
“It is an extraordinary twist to a very complicated story,” Vaz told BBC today. “I will write to the police to ask for the justification of the use of terrorism legislation they may have a perfectly reasonable explanation.”
Greenwald has written a series of stories revealing mass surveillance programmes by the US National Security Agency.
-
-
-
On August 12 the California Senate Appropriations Committee sent to the floor a bill making it more difficult for residents of the Golden State to be indefinitely detained under provisions of the National Defense Authorization Act (NDAA).
-
Internet/Net Neutrality
-
This week Facebook’s ban-bot went berserk; Github went down; and all Google services collapsed for a few minutes, taking 40% of the Internet with them. Just another week on the Internet, then. We love our centralized services, until they let us down.
Permalink
 Send this to a friend
Send this to a friend
Posted in Database, Microsoft, Oracle at 8:03 am by Dr. Roy Schestowitz
Proprietary software giants love to spy
Summary: Proprietary software from the dominant database players (which recently got together) is expected to further violate privacy
After a recent interview with Larry Ellison it is no longer secret or just mere speculation that he is an NSA proponent (Oracle’s founders and the business have a renowned CIA-assisted/subsidised past), but what’s noteworthy is Microsoft’s view, which based on the company’s relationship with the NSA is more than happy and even eager to strengthen the NSA. How would China feel if it knew all those facts*? It is already investigating some US companies like IBM over privacy intrusions and it should know that HP has back doors in its storage servers (caught red handed).
Oracle recently got closer to Microsoft, which helped devour Java and add NSA surveillance to it (on the ‘cloud’). It is being noted by IDG that:
The new Microsoft-Oracle partnership benefits both companies, as Oracle gets access to Azure and Microsoft can finally license Java. Will the deal have any effect on either company’s enterprise customers?
Anyone who runs a program or a GNU/Linux distribution on Microsoft’s ‘cloud’ should expect NSA surveillance. But it’s not like this would bother Larry Ellison. More and more people will, over time, realise that the PATRIOT Act made it risky to host with US companies (or US-made software) anywhere, respective of the datacentre’s location (the Internet is global). █
___
* Having just spent 2 hours at a Chinese superstore, it seems evident that we in the West increasingly come to depend on China for everything, rather than the other way around. The US and UK governments are openly worried right now about dependence on Chinese hardware which could facilitate back doors.
Permalink
 Send this to a friend
Send this to a friend
Posted in TechBytes Video at 3:24 am by Dr. Roy Schestowitz

Direct download as Ogg (00:00:50, 2.8 MB)
Summary: Dr. Richard Stallman, the Free Software Foundation’s founder, explains how the press in the US is controlled
Made entirely using Free/libre software, heavily compressed for performance on the Web at quality’s expense
Permalink
 Send this to a friend
Send this to a friend
08.17.13
Posted in FUD, Google, Microsoft at 6:56 pm by Dr. Roy Schestowitz
The rotting empire resorts to separate desperate measures

Summary: A glimpse at Microsoft’s latest ugly moves against Google, which is a Microsoft Nemesis in the generation of Linux/Android and services
Microsoft seems to have censored Free software which runs on Windows, reveals strong evidence. Microsoft goes further by trying to do that at Google. OpenOffice could be vanished due to a bogus DMCA notice from Microsoft. As put by Swapnil Bhartiya: “Most of the time most open source players including the Apache Foundation provides the software via torrents as it’s a better technology than direct download and these torrents are then shared across the torrent sites. These are legitimate torrents. But NSA friendly Microsoft goes ahead and terminates these links not only from its own Bing, but also from Google and other search engines.
“I think there should be some penalty for sending wrong DMCA notices to discourage the abuse of the already flawed system.”
That’s a tool Microsoft habitually abuses, as we showed before. And as part of the resurrected "Scroogled" campaign Microsoft will try to accuse Google of what Microsoft is doing.
As the above author put it:
If you are a long-term GNULinux user you would love to see Microsoft in this position. IT world and competition has suffered quite a lot under Microsoft’s abusive monopoly which killed many competitors in the bud, before iOS and Android happened.
While Microsoft’s legal team may not miss any opportunity to brag about signing bogus patent deals with Android players over undisclosed (and thus can be assumed bogus) patents, it has no respect for the work of others.
Microsoft’s Windows Phone has a very very tiny market share, and thus it’s not a viable platform for Google or any other player to create any app for Windows Phones. Looking at the popularity of YouTube, Microsoft who never bothered to create any of its apps for GNULinux, went ahead and create its own YouTube app. For the obvious reasons the app did not meet Google’s terms and conditions as it offered a download option (and removed ads) to cut the revenues of hardworking content creators who publish their content on YouTube to monetize from the ads.
Microsoft had agreed to remove the app and the two companies were supposedly working together on the problem (nice to see Microsoft getting the same treatment it’s been giving to Linux for decades).
Microsoft is now excluding Android from apps and also accusing Google of being sloppy on privacy (look who’s talking). The Microsoft-esque PR from Consumer Watchdog seems to have been more bogus than we realised. As Lauren Weinstein’s blog shows, there might be fabrication. Google never said what it’s claimed to have said. As Weinstein put it:
“There was (I like believe) a time when supposedly reputable news-oriented organizations made the effort to try independently verify “news” — at least to the extent of verifying easily available materials — before writing about or republishing items likely to inflame passions and falsely damage reputations.”
[...]
We’ve just been treated to another vivid example of this, courtesy (initially) of reliably Google-hating “Consumer Watchdog” and Putin’s propaganda channel “Russia Today (RT).”
This sorry sequence began when Consumer Watchdog breathlessly proclaimed that Google had been caught in a legal brief proclaiming that “Gmail users have no expectation of privacy.” RT picked up the story, and sites that we normally would consider to be reasonably reputable started echoing it without further investigation, playing on the current climate of government surveillance furor (and in many cases, related hyperbolic and unjustified paranoia).
[...]
I don’t really expect any better from Consumer Watchdog or Putin’s RT. But it seems reasonable to at least hope for more sense from mainstream news and other websites who portray themselves as accurate sources of information.
This JoinDiaspora discussion about it has AJ saying: “it is kind of sad, that not a single investigative reporter took the time to verify this quote
“the reason i say that is because the actual quote is sufficiently absurd, there was no need to change it :)”
Will Hill replies:
Gates gets the press he pays for. Here’s a recent example of analyst and press manipulation. You can get a small glimpse of how big the microsoft controlled press is by reading their training manuals carefully.
the financial analysts particularly carry a lot of weight. We may think that, you know, Christine Comerford and Jesse Burst and other people who write in the Windows magazines are important, but the most important analysts are the guys who work for, like, Goldman Sachs and Lehman Brothers and the other financial analysts. … everybody reads PC Week, but the VPs and above, those guys are reading the Goldman Sacks analyst reports. They’re the guys, you know, really making the decisions
There are two kinds of developer conferences. There’s those that are controlled by the platform vendors, such as our PDC. We control everything that goes on there; nobody says nothing that we don’t approve beforehand … At independent conferences, subvert them. Find the people who choose who goes on the agenda and … Just suck up to them so hard your face collapses. I mean, those people…those people are so valuable to you, it’s beyond belief, because they control who goes on that session or not.
There’s lot’s of independent programming journals. You want to infiltrate those. Again, there’s two categories. There’s those that are controlled by vendors; like MSJ; we control that. And there’s those that are independent. The ones that we control, you use. … The ones that third parties control, like the WinTech Journal, you want to infiltrate. You want to get yourself onto the advisory committee that picks out which authors are published and which ones aren’t, or which topics are covered and over these special issues, things like that Just be so helpful that they can’t do without you, and then make sure that things go your way. …that was actually my first claim to fame before I started doing presentations and forming users groups and so forth, was that I was really good on the Internet. And the main thing I did was that I was very formal and polite.
and so on and so forth. Those jerks never quit.
Microsoft, in the mean time, is also using antitrust against Google. Here is a response to this dirty trick:
Microsoft and Nokia protest “price predation” and play at being prey.
[...]
Practically, however, predatory pricing turns out to be controversial and difficult to establish. This is particularly true for predatory pricing claims against free software. An alleged predator is highly unlikely to recoup “losses” caused by free distribution, since free software’s four freedoms allow competitors liberal entry into the market. Moreover, free software licenses (including GPLv2 and Apache v2) arm these competitors with the power to redistribute royalty-free, making any alleged effort at monopoly pricing unsustainable.
[...]
Of course, Microsoft’s complaint is a bit hypocritical, since the Department of Justice and 20 states accused them of predatory pricing when they distributed Internet Explorer without charge. Recall their response at the time: That a market participant – Netscape – had already set the price for browser technology at zero. Does that sound familiar?
And by their accusations, Nokia displays ignorance about its own history with free and open source software. Speaking about Google at a recent legal conference, Nokia’s head of competition law wondered aloud: “If you make a multi-billion-dollar investment as Google has done in the Android operating system, why would you just give it away?” Presumably Google sought the same benefits as Nokia when Nokia open-sourced its own mobile operating system – Symbian.
The outcome of FairSearch’s request for a Commission investigation is not yet known. What is known is that the benefits of free software – high quality, high value, customizable, low lock-in technologies cooperatively developed, tested, distributed, and improved by an efficient global-scale community marshaled using the latest collaborative Internet tools – ring true with consumers. And these benefits, along with the disruptive business model that brings them to fruition, should identify free software distributors not as price predators, but as embodiments of “maverick firms,” a species of competitor that authorities in both the US and the EU seek to protect, not punish.
Hopefully the Commission will view free software the way consumers do and reject FairSearch’s complaint.
FairSearch is just a Microsoft proxy, one of many. We have already analysed the roots of “FairSearch” and “Consumer Watchdog” (deceiving names) before. █
Permalink
 Send this to a friend
Send this to a friend




















 Content is available under CC-BY-SA
Content is available under CC-BY-SA